Search results for "cyber criminals"
-

 3.7KMalware
3.7KMalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
A “multi-faceted campaign” has been observed abusing legitimate services like GitHub and FileZilla to deliver an array of stealer malware and banking...
-

 1.6KData Security
1.6KData SecurityBinance’s 4.3 Billion-Dollar Blunder: How cyber criminals launder money via Binance?
Cyber criminals have utilized cryptocurrency exchanges like Binance for money laundering due to the pseudonymous nature of digital currencies. Here’s a general...
-
 2.9KMalware
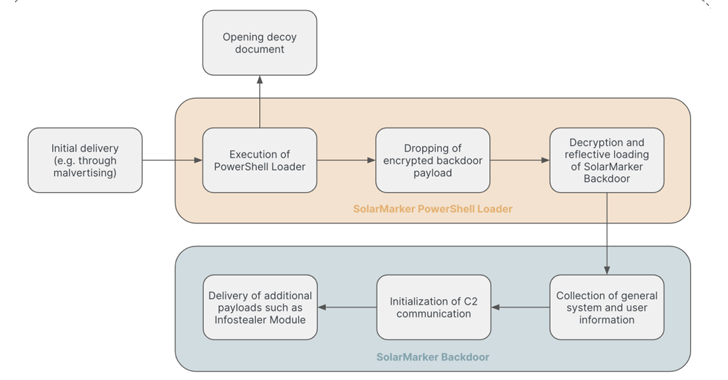
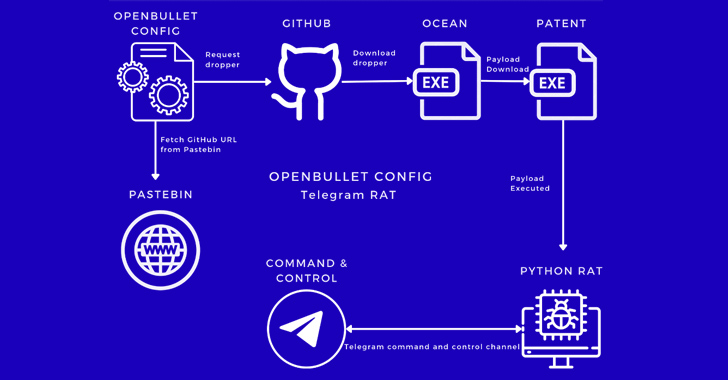
2.9KMalwareNew Malware Campaign Targets Inexperienced Cyber Criminals with OpenBullet Configs
A new malware campaign has been observed making use of malicious OpenBullet configuration files to target inexperienced cyber criminals with the goal...
-
 2.0KMalware
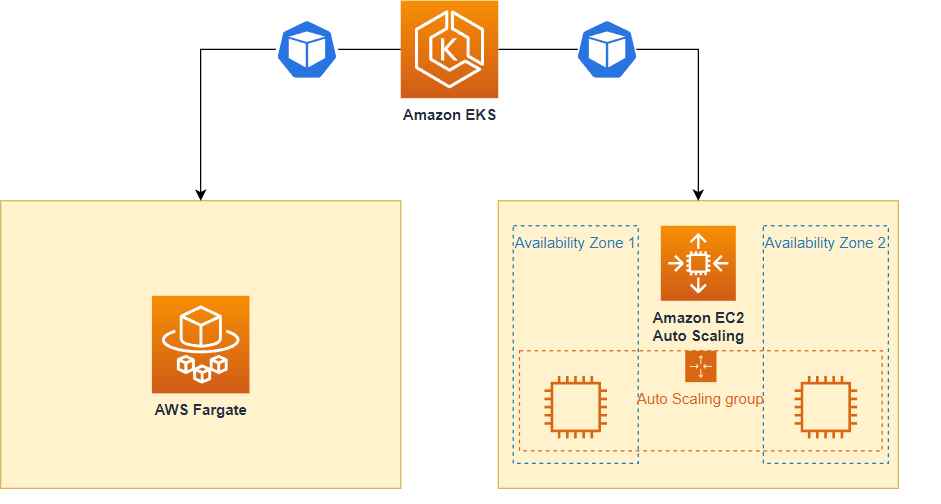
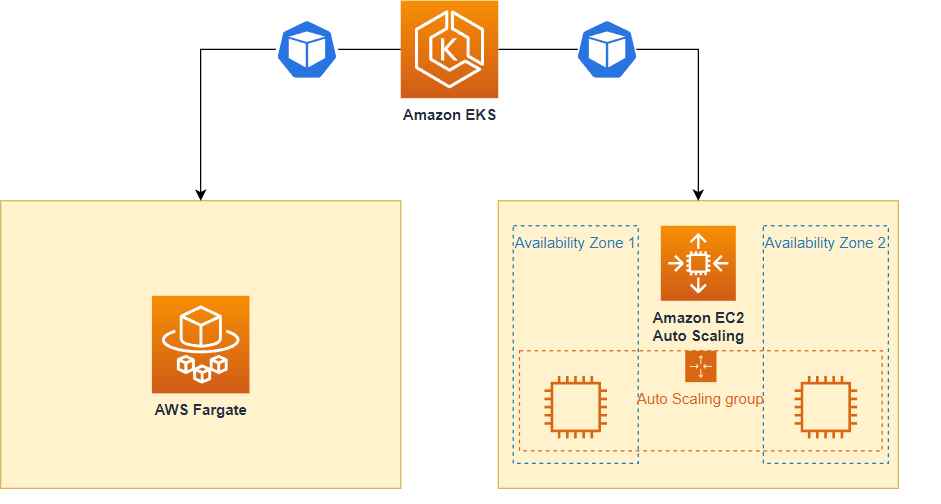
2.0KMalwareHow cyber criminals are hacking into AWS Fargate, EKS & evading cloudtrail logs detection
Sysdig, a company that specializes in cybersecurity intelligence, uncovered a sophisticated hacking operation known as Scarleteel in February. Since then, Scarleteel has...
-
 2.4KMalware
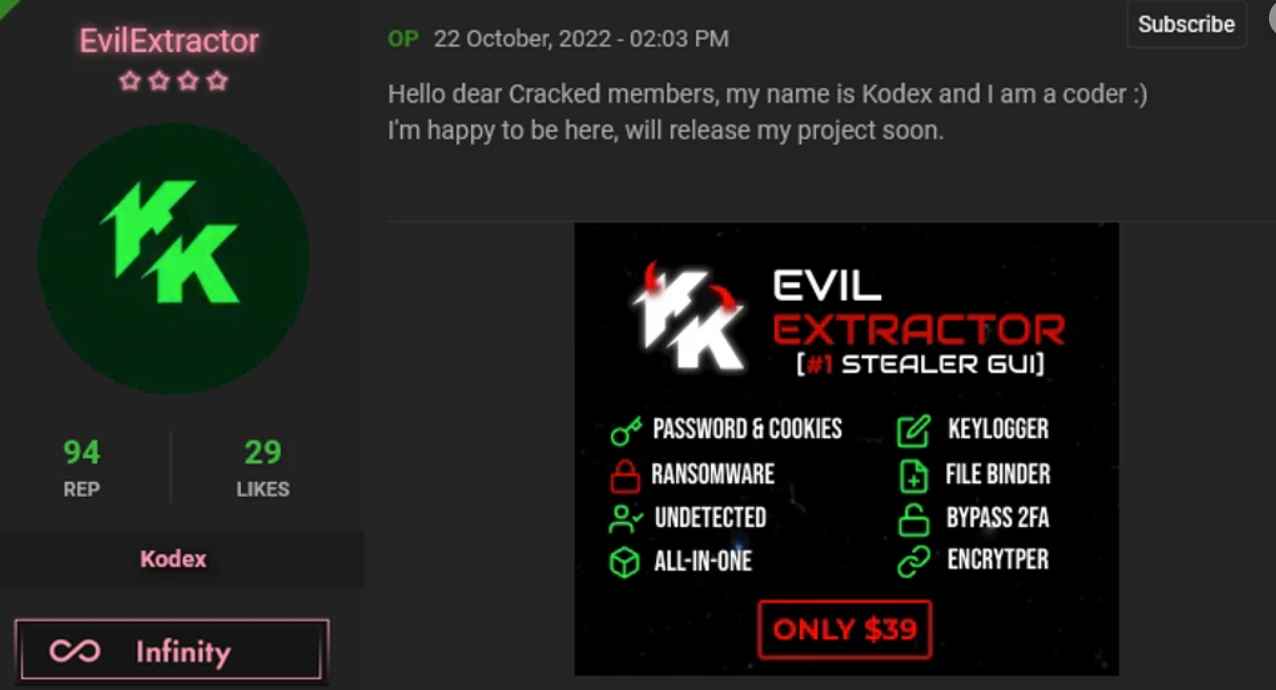
2.4KMalwareNew famous all in one malware and hacking tool among cyber criminals: EvilExtractor
EvilExtractor is an attack tool that is meant to target Windows operating systems to extract data and files from endpoint devices. EvilExtractor...
-

 942Data Security
942Data Security3 different ways cyber criminals are using ChatGPT to conduct new cyber attacks
At the end of November 2022, OpenAI announced the introduction of ChatGPT, the new interface for its Large Language Model (LLM), which...
-

 2.8KMalware
2.8KMalwareResearchers Warn of Cyber Criminals Using Go-based Aurora Stealer Malware
A nascent Go-based malware known as Aurora Stealer is being increasingly deployed as part of multiple campaigns designed to steal sensitive information...
-

 3.2KIncidents
3.2KIncidentsOne of the world’s largest telescopes becomes target of cyber criminals affecting the observatory operations
Following a hack, one of the biggest and most sophisticated telescopes in the world had to halt operations. A attack on its...
-

 1.1KData Security
1.1KData SecurityGang of 31 cyber criminals arrested for stealing cars via hacking software
In a coordinated operation on October 10 throughout the three nations, 31 people were detained. A total of 22 addresses were raided,...
-
 3.0KMalware
3.0KMalwareCyber Criminals Using Quantum Builder Sold on Dark Web to Deliver Agent Tesla Malware
A recently discovered malware builder called Quantum Builder is being used to deliver the Agent Tesla remote access trojan (RAT). “This campaign...
-
 492Malware
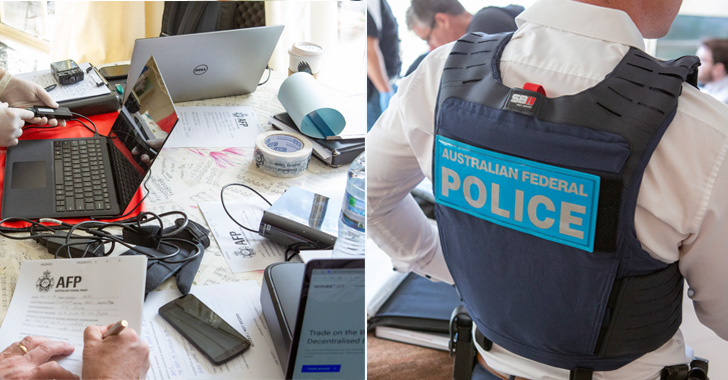
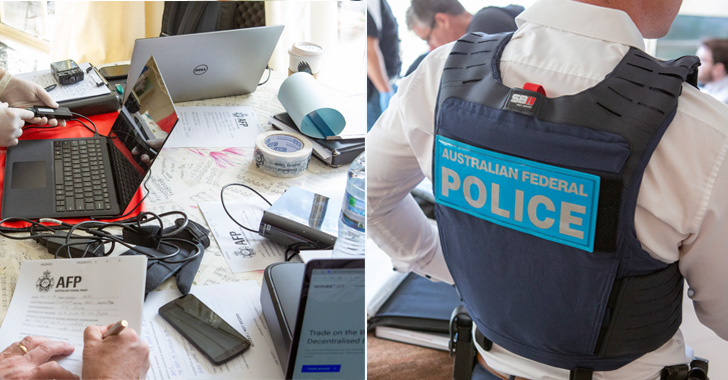
492MalwareAustralian Hacker Charged with Creating, Selling Spyware to Cyber Criminals
A 24-year-old Australian national has been charged for his purported role in the creation and sale of spyware for use by domestic...
-

 1.4KMalware
1.4KMalwareMalicious IIS Extensions Gaining Popularity Among Cyber Criminals for Persistent Access
Threat actors are increasingly abusing Internet Information Services (IIS) extensions to backdoor servers as a means of establishing a “durable persistence mechanism.”...
-
 4.5KData Security
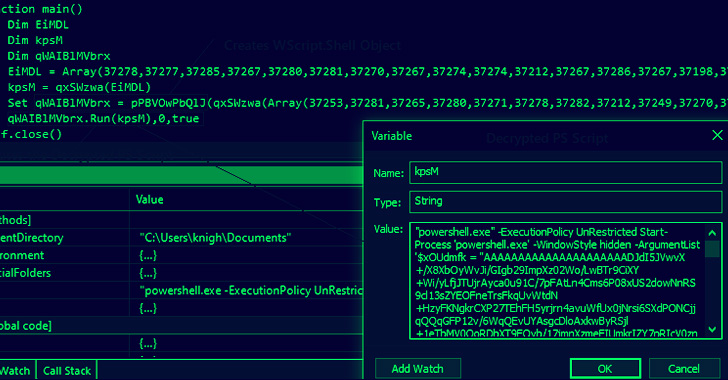
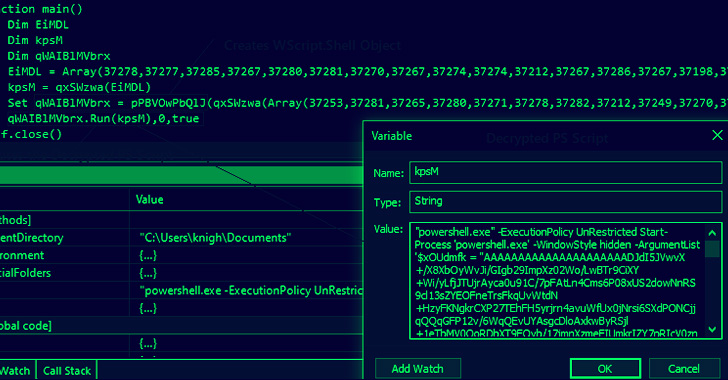
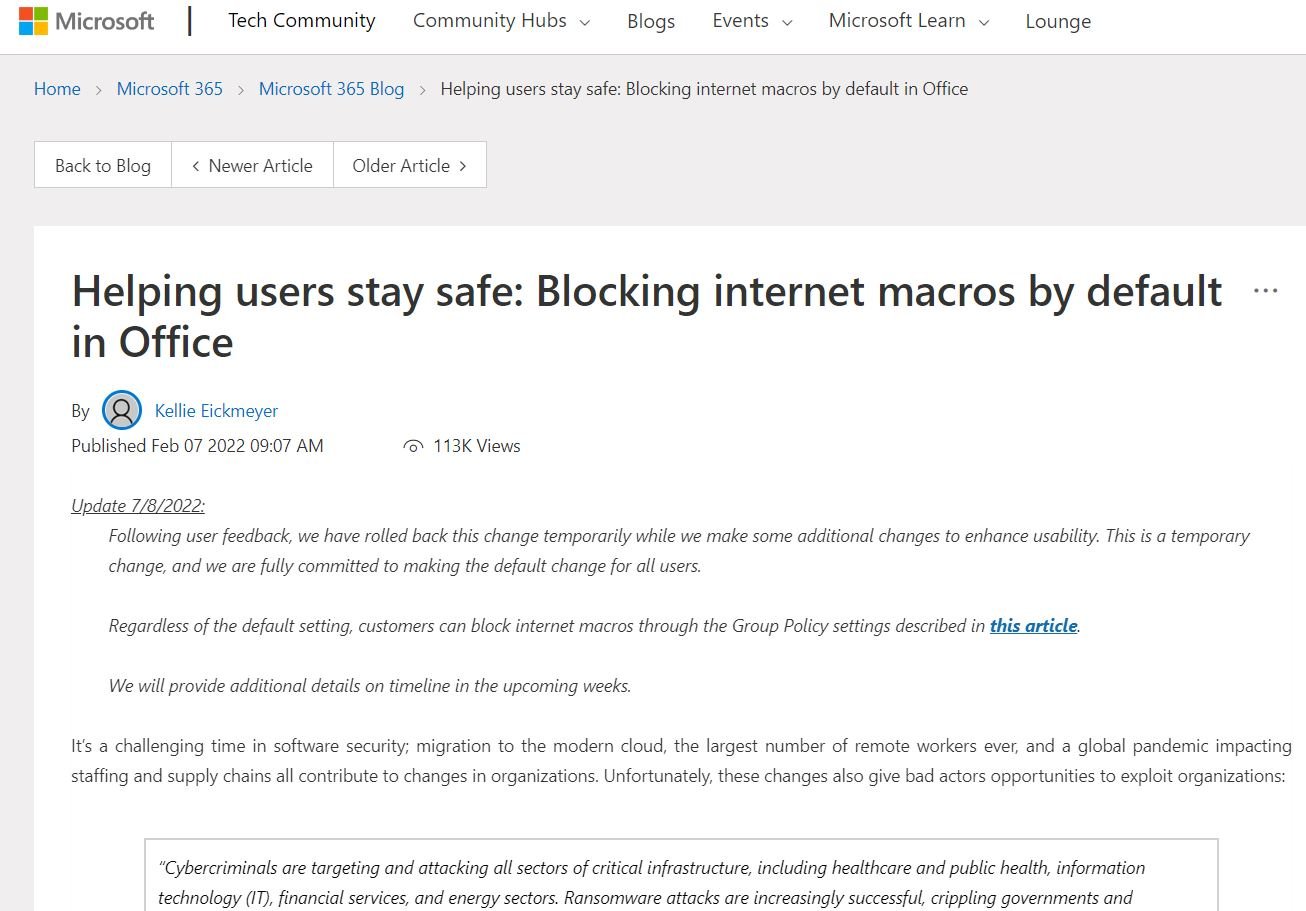
4.5KData SecurityMICROSOFT MAKES THINGS HARDER FOR CYBER CRIMINALS BY DISABLING MACROS AGAIN BY DEFAULT IN OFFICE PRODUCTS
One of the attack methods that hackers can use is a simple Word document that they send in the mail. They use...
-

 2.7KData Security
2.7KData SecurityMICROSOFT MAKES THINGS EASIER FOR CYBER CRIMINALS BY ENABLING AGAIN MACROS BY DEFAULT IN OFFICE PRODUCTS
Microsoft has surprised key parts of the security community with its decision to quietly reverse course and allow untrusted macros to open...
-

 3.7KData Security
3.7KData Security24,649,096,027 (24.65 billion) account usernames and passwords have been leaked by cyber criminals till now in 2022
Credential abuse is something that happens only to CEOs or very rich people or employees of fortune 500 companies right? Nope. It’s...
-

 1.7KIncidents
1.7KIncidentsHow misspelling of one word saved a man his $6 millions from cyber criminals
A businessman nearly lost $6 million to hackers, but one word saved his fortune from falling into accounts of hackers and disappearing...
-
 4.2KMalware
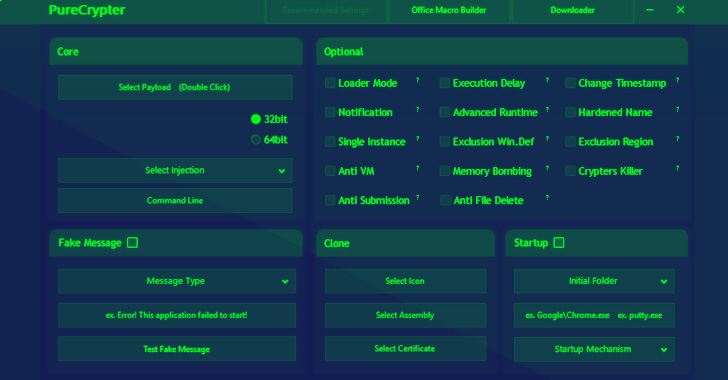
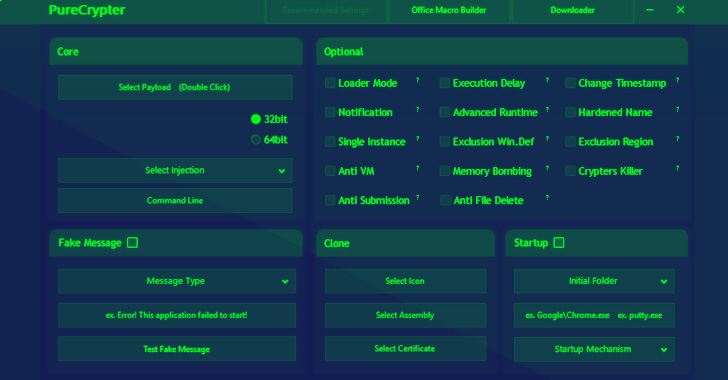
4.2KMalwareResearchers Detail PureCrypter Loader Cyber Criminals Using to Distribute Malware
Cybersecurity researchers have detailed the workings of a fully-featured malware loader dubbed PureCrypter that’s being purchased by cyber criminals to deliver remote...
-

 5.1KData Security
5.1KData SecurityMicrosoft makes things harder for cyber criminals by disabling macros by default in Office products
Microsoft has developed multiple protection mechanisms against some popular hacking variants, including the malicious use of macros. Sometimes, threat actors send Office...
-

 3.1KIncidents
3.1KIncidentsNew way to steal NFT via Discord used by cyber criminals
At the end of 2021, the Non-Fungible Token (NFT) projects Monkey Kingdom and Fractal were targeted by the same hacking variant, in...
-

 3.2KIncidents
3.2KIncidentsCyber criminals who helped people cheat and pass CISCO Certifications, CompTIA Certifications, EC- Council certifications arrested. New modus operandi discovered
Authorities in India arrested three individuals accused of participating in a fraudulent operation in order to cheat on the presentation of an...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesNew vulnerability in MacOS allows cyber criminals to hack Macbook Pros via rootkits
In a security report, Microsoft detailed the finding of a critical vulnerability in macOS whose successful exploitation would allow threat actors to...