Search results for "cyber criminals"
-

 125Data Security
125Data SecurityCyber-Criminals Throw Molotov Cocktails at Dr.Web Antivirus Headquarters After Being Exposed
Cyber-crime syndicate tried to intimidate antivirus vendor. In some cases, cyber-security work can turn really dangerous, and even deadly, if you manage to...
-
 92Cyber Crime
92Cyber CrimeRansomware: Should you pay the cybercriminals?
If your files are encrypted by ransomware, should you pay the ransom? We examine the options...
-

 112Cyber Crime
112Cyber CrimeFour Mortal Kombat moves cybercriminals use to attack your security
Some of the tricks employed by the characters in the Mortal Kombat series aren't a million miles away from those deployed by...
-
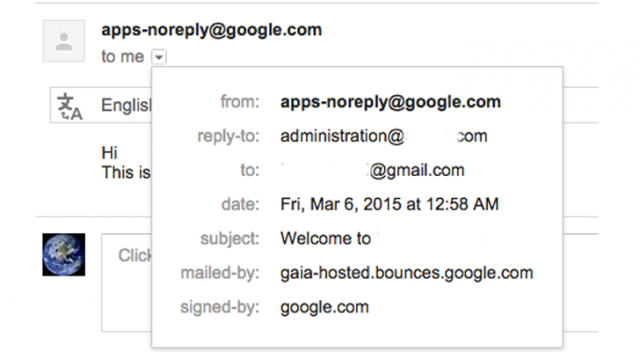
 302Data Security
302Data SecurityCybercriminals Abusing Vulnerability in Google Apps to Send Phishing Emails
It has been found that hackers can now easily abuse any website’s domain name based email addresses through the Google Apps for...
-

 99Cyber Crime
99Cyber CrimeAdvertising fraud: a quarter of digital ads stolen by cybercriminals’ bots
Nearly a quarter of digital advert impressions are faked, according to a new study. This advertising fraud is set to cost advertisers...
-

 280Malware
280MalwareBotnets: remote controls for cybercriminals
As promised in our post about the European Cyber Security Month during October, we are publishing about Botnets and Exploits this week....
-

 94Cyber Crime
94Cyber CrimeThink cybercriminals are “evil geniuses”? Wrong – and these idiots show why
Many cybercriminals are not exactly Bond villain material - in fact, some are criminals with a level of weapons-grade stupidity that Bond...
-

 100Cyber Crime
100Cyber CrimeCyber defense: businesses need to “spy on” cybercriminals to survive
The key to a good cyber defense strategy is to improve knowledge of current threats, and risks to businesses, according to law...
-
 128Malware
128Malware“You have cancer” phishing attack shows how low cybercriminals will go
A “particularly unpleasant” phishing email purporting to be the results of a blood count report showing that the recipient may have cancer...
-

 164Scams
164ScamsHow cybercriminals ‘market’ email attacks – and why LinkedIn lures are today’s prize phish
Cybercriminals ‘manage’ phishing emails using techniques similar to those used by marketing agencies, including the use of ‘test audiences’ to see how...
-

 95Cyber Crime
95Cyber CrimeBorrowing tricks from cybercriminals can ‘scare’ web users into safe browsing, Cambridge researchers claim
Computer users often feel bombarded by warnings about malware - particularly in internet browsers, which often repeatedly warn about risky sites -...
-

 94Cyber Crime
94Cyber CrimeBitcoin heist nets cybercriminals $1 million after huge DDoS “smokescreen”
A large-scale “heist” targeting Bitcoin site BIPS led to the theft of $1 million in Bitcoin - the second such major attack...
-

 88Cyber Crime
88Cyber CrimeRogue’s gallery? New app aims to “out” cybercriminals who prey on online daters
A new app, Truly.am, aims to put a stop to a fast-growing area of online fraud - online dating scams - by...
-

 133Malware
133MalwareStop, thief! Five new tricks used by cybercriminals – and how to stay safe
From legitimate companies delivering software with a “side-order” of malware, to PC attacks that persuade you to infect your own phone, here...
-

 139Cyber Crime
139Cyber CrimeCybercriminals trying new tactics, security body warns – and attacks could have “large impact”
Cybercriminals are switching tactics, a leading security body has warned - and the combination of anonymisation technologies, mobile devices, and social media...
-

 505How To
505How ToA scam‑spotters guide: Ten things your bank will NEVER do – but cybercriminals will
These days cybercriminals will use phone calls, SMS messages, emails, fake apps - and even couriers - in an effort to get...
-

 88Cyber Crime
88Cyber CrimeCybercriminals use DDoS attacks as “smokescreens” for major cyber thefts
Millions of dollars have been lost to an "ominous" new hi-tech tactic used by cybercriminals - where a low-powered DDoS attack is...
-

 94Cyber Crime
94Cyber CrimeCybercriminals “saving up” wave of Windows XP attacks for when Microsoft stops support
Cybercriminals will unleash a wave of “zero-day” vulnerabilities to attack Windows XP machines after April 8, 2014, a security expert has claimed.
-

 92Cyber Crime
92Cyber CrimeCybercriminals turn to Perfect Money after Liberty Reserve takedown
Cybercriminals are turning to a new digital currency, Perfect Money, in the wake of the closure of the notorious Liberty Reserve, which...
-

 361Cyber Crime
361Cyber CrimeHacked signal‑boosters let cybercriminals “listen in” on cellphones
A $250 signal-boosting device for cellphone users can be hacked, two researchers claim - offering total access to phone calls, internet use...
-

 391Cyber Crime
391Cyber CrimeCybercriminals use photo‑sharing to snare victims in auction scams, FBI warns
Cybercriminals are using online car auctions and photo-sharing services to dupe victims into downloading malware, the FBI has warned. Once infected, the...






