Search results for "cyber criminals"
-

 2.1KMalware
2.1KMalwareCybercriminals Developing BugDrop Malware to Bypass Android Security Features
In a sign that malicious actors continue to find ways to work around Google Play Store security protections, researchers have spotted a...
-

 2.7KCyber Crime
2.7KCyber Crime5 ways cybercriminals steal credit card details
Here are some of the most common ways hackers can get hold of other people’s credit card data – and how you can...
-

 1.9KIncidents
1.9KIncidentsCybercriminals hack Fortress Protocol, steal its funds and launder them through Tornado Cash
Fortress Protocol, an algorithmic marketplace platform and decentralized finance (DeFi) lending protocol, suffered the loss of all its funds following a massive...
-

 2.1KMalware
2.1KMalwareCybercriminals Using New Malware Loader ‘Bumblebee’ in the Wild
Cybercriminal actors previously observed delivering BazaLoader and IcedID as part of their malware campaigns are said to have transitioned to a new...
-

 2.9KMalware
2.9KMalwareHaskers Gang Gives Away ZingoStealer Malware to Other Cybercriminals for Free
A crimeware-related threat actor known as Haskers Gang has released an information-stealing malware called ZingoStealer for free on, allowing other criminal groups...
-

 4.3KData Security
4.3KData Security4 Ways Cybercriminals Exploit Remote Teams
Working from home (WFH) is not a piece of cake especially when cybercriminals exploited every possible vulnerability to break into your workstation....
-

 2.1KData Security
2.1KData SecurityCybercriminals are using Spider-Man: No Way Home film to steal banking credentials
Last Friday, the highly anticipated film Spider-Man: No Way Home was released, and fans are desperate to find tickets, sold out since...
-

 410Vulnerabilities
410VulnerabilitiesCybercriminals are exploiting Owowa IIS module to take control of exposed servers
A report by the security firm Kaspersky details the detection of a hacking group using an Internet Information Services (IIS) web server...
-
 4.9KHow To
4.9KHow ToHow Artificial intelligence (AI) Stops Cybercriminals
Newer AI algorithms are extremely good at analyzing data traffic, access, and transfer, as well as detecting outliers or anomalies in data...
-

 5.2KIncidents
5.2KIncidentsComputer manufacturer Acer suffers massive cyberattack; cybercriminals threaten to leak sensitive data
Through a statement, Taiwanese firm Acer confirmed that its aftermarket systems in India were compromised by what they described as an “isolated...
-

 3.9KMalware
3.9KMalwareCybercriminals are signing malware in new way to prevent detection: new research via Google team
The experts of Google Threat Analysis Group, specialized in the investigation of state hacking campaigns, electronic fraud and disinformation, report the detection...
-

 3.0KIncidents
3.0KIncidentsHow 106 cybercriminals working for Italian and Spanish mafia were hacked by EUROPOL
An investigation coordinated by Europol led to the dismantling of a complex cybercriminal network linked to the Italian mafia, which operated dozens...
-
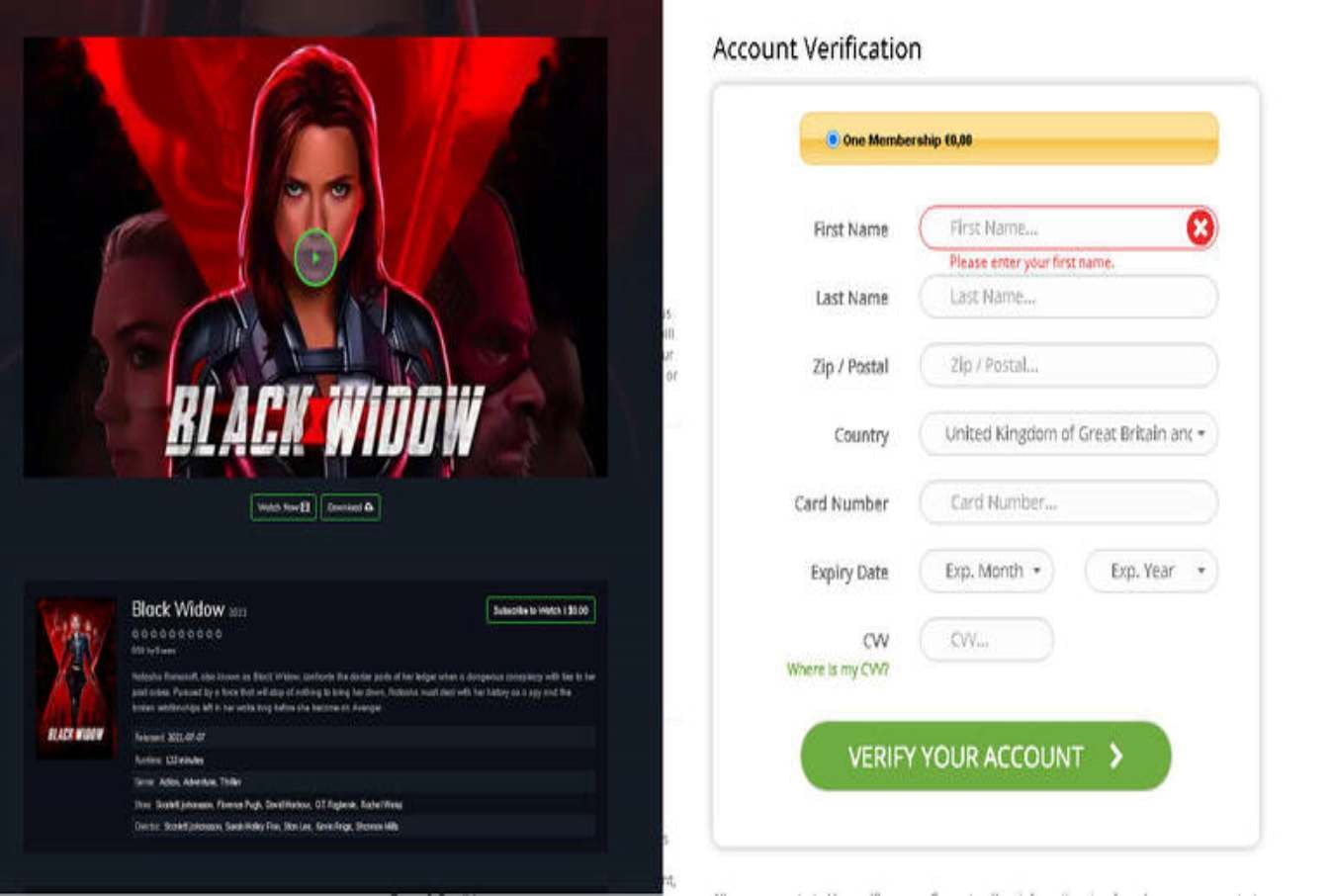
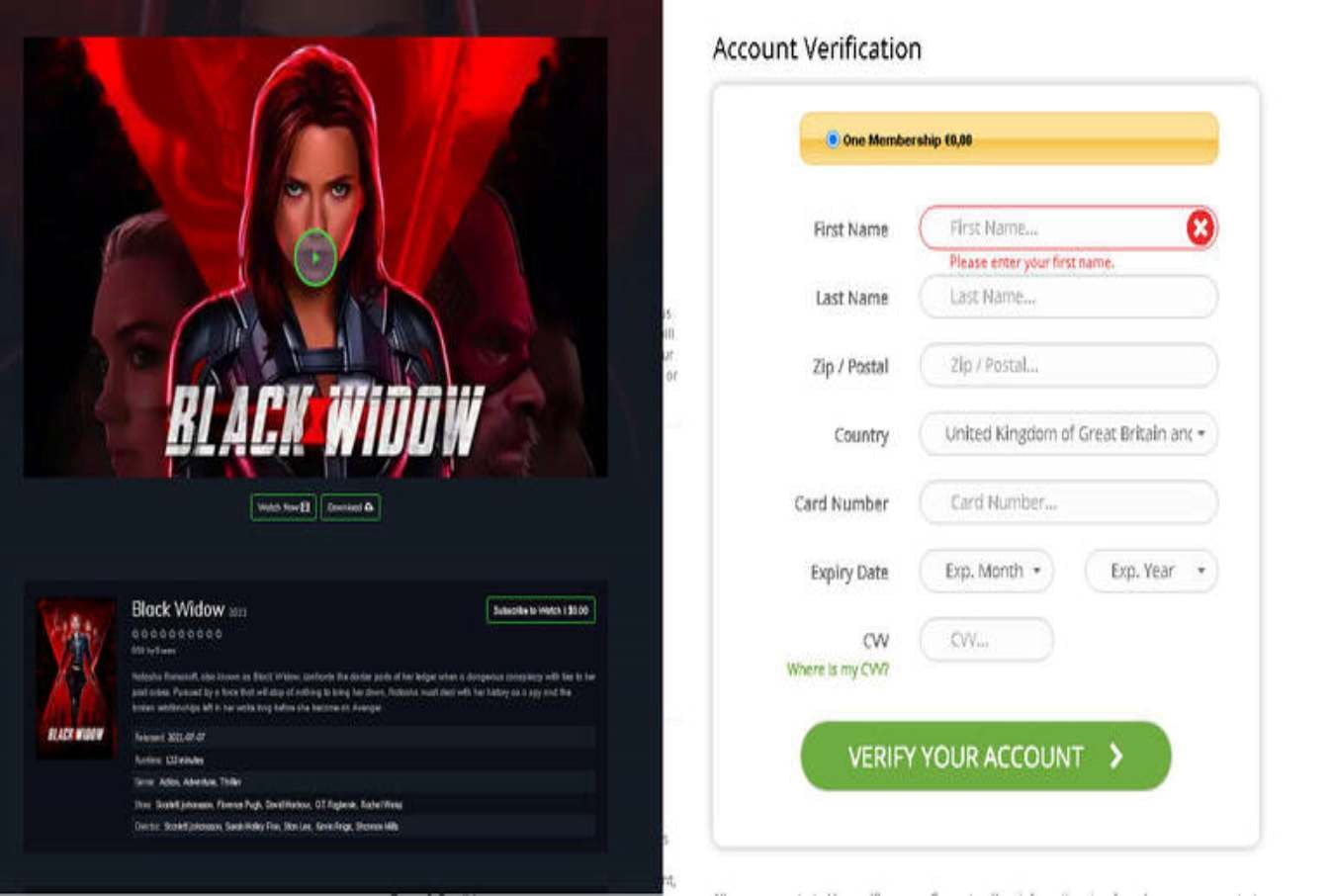 5.3KCyber Crime
5.3KCyber CrimeCybercriminals using Marvel’s Black Widow movie to spread malware
Apart from malware, offers to watch the online premiere of the Black Widow movie are being used to steal payment card data....
-
 5.2KMalware
5.2KMalwareCybercriminals Abusing Internet-Sharing Services to Monetize Malware Campaigns
Threat actors are capitalizing on the growing popularity of proxyware platforms like Honeygain and Nanowire to monetize their own malware campaigns, once...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesCybercriminals are scanning servers for the Microsoft Exchange ProxyShell RCE vulnerabilities after technical details presented at the Black Hat
Researchers report the detection of multiple attempts to exploit ProxyShell, a set of remote code execution flaws in Microsoft Exchange disclosed during...
-

 3.7KData Security
3.7KData SecurityChinese cybercriminals attack electric companies, water treatment plants and more critical infrastructure
A China-based group of threat actors is deploying an attack campaign against critical infrastructure in South Asia to compromise industrial control systems...
-

 5.3KMalware
5.3KMalwarePrometheus: the hacking platform that helps cybercriminals to attack as many users as possible
A new cybercriminal operation identified as Prometheus is helping multiple hacking groups distribute malware across various compromised websites. Researchers point out that...
-

 3.6KMalware
3.6KMalware16 Cybercriminals Behind Mekotio and Grandoreiro Banking Trojan Arrested in Spain
Spanish law enforcement agencies on Wednesday arrested 16 individuals belonging to a criminal network in connection with operating two banking trojans as...
-

 4.2KCyber Crime
4.2KCyber CrimeGlobal police shut down VPN service favored by cybercriminals
A global operation takes down the infrastructure of DoubleVPN and seizes data about its customers
-

 5.2KIncidents
5.2KIncidentsBrazilian cybercriminals created fake Uber, DoorDash and other digital platforms accounts to earn thousands of dollars
A recent report by the Federal Bureau of Investigation (FBI) points to a Brazilian group operating a plan to defraud customers of...
-

 1.2KMalware
1.2KMalwareColonial Pipeline Paid Nearly $5 Million in Ransom to Cybercriminals
Colonial Pipeline on Thursday restored operations to its entire pipeline system nearly a week following a ransomware infection targeting its IT systems,...






