Search results for "cyber criminals"
-
 1.7KMalware
1.7KMalwareVietnamese Cybercriminals Targeting Facebook Business Accounts with Malvertising
Malicious actors associated with the Vietnamese cybercrime ecosystem are leveraging advertising-as-a-vector on social media platforms such as Meta-owned Facebook to distribute malware....
-
 827Cyber Attack
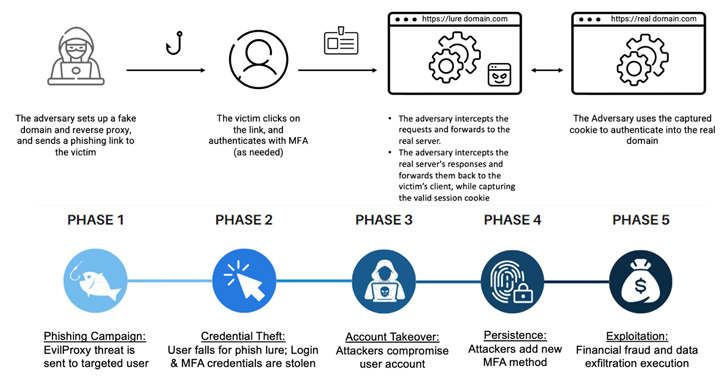
827Cyber AttackCybercriminals Increasingly Using EvilProxy Phishing Kit to Target Executives
Threat actors are increasingly using a phishing-as-a-service (PhaaS) toolkit dubbed EvilProxy to pull off account takeover attacks aimed at high-ranking executives at...
-

 5.0KMalware
5.0KMalwareIranian Company Cloudzy Accused of Aiding Cybercriminals and Nation-State Hackers
Services offered by an obscure Iranian company known as Cloudzy are being leveraged by multiple threat actors, including cybercrime groups and nation-state...
-

 3.7KMalware
3.7KMalwareCybercriminals Renting WikiLoader to Target Italian Organizations with Banking Trojan
Organizations in Italy are the target of a new phishing campaign that leverages a new strain of malware called WikiLoader with an...
-
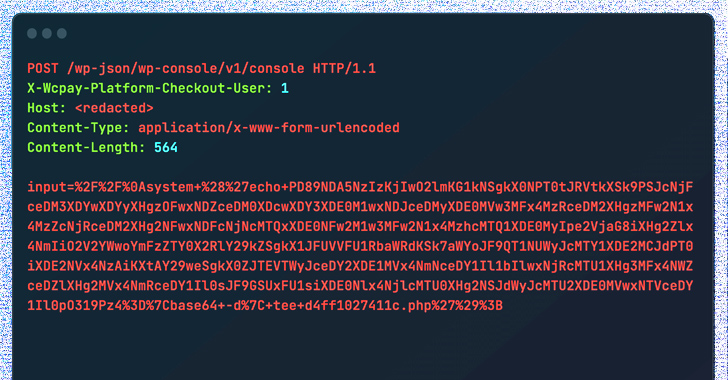
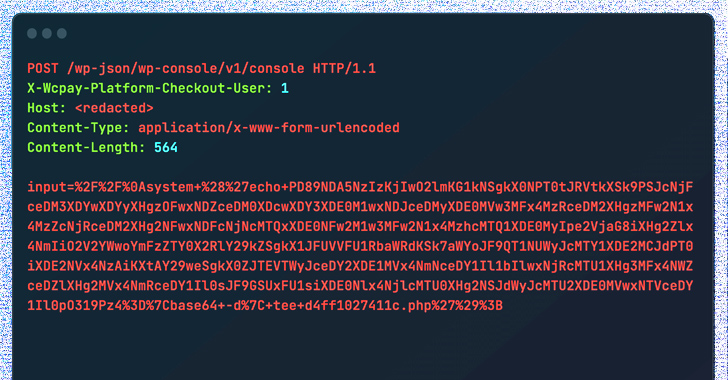 375Vulnerabilities
375VulnerabilitiesCybercriminals Exploiting WooCommerce Payments Plugin Flaw to Hijack Websites
Threat actors are actively exploiting a recently disclosed critical security flaw in the WooCommerce Payments WordPress plugin as part of a massive...
-
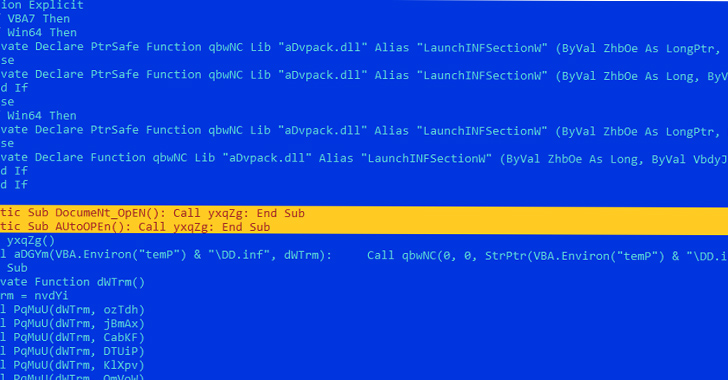
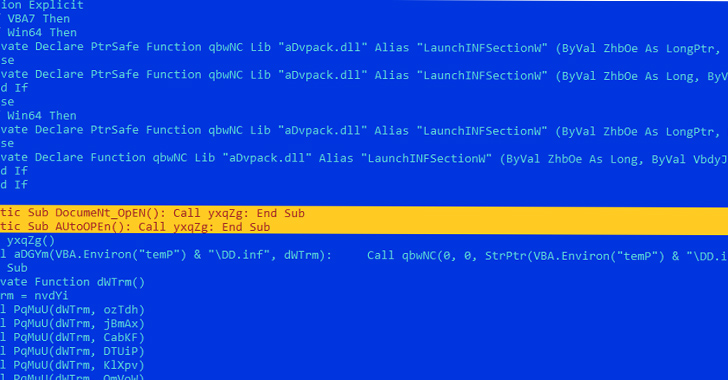 4.5KMalware
4.5KMalwareCybercriminals Exploit Microsoft Word Vulnerabilities to Deploy LokiBot Malware
Microsoft Word documents exploiting known remote code execution flaws are being used as phishing lures to drop malware called LokiBot on compromised...
-

 4.7KMalware
4.7KMalwareCybercriminals Using Powerful BatCloak Engine to Make Malware Fully Undetectable
A fully undetectable (FUD) malware obfuscation engine named BatCloak is being used to deploy various malware strains since September 2022, while persistently...
-
 1.7KMalware
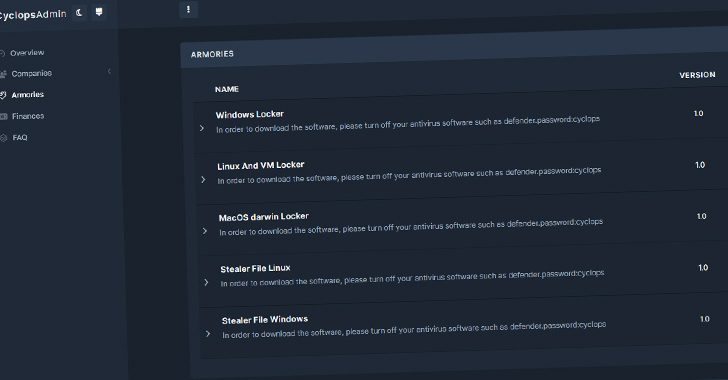
1.7KMalwareCyclops Ransomware Gang Offers Go-Based Info Stealer to Cybercriminals
Threat actors associated with the Cyclops ransomware have been observed offering an information stealer malware that’s designed to capture sensitive data from...
-
 974Malware
974MalwareAceCryptor: Cybercriminals’ Powerful Weapon, Detected in 240K+ Attacks
A crypter (alternatively spelled cryptor) malware dubbed AceCryptor has been used to pack numerous strains of malware since 2016. Slovak cybersecurity firm...
-

 2.7KData Security
2.7KData SecurityReconShark: New undetectable reconnaissance tool used by cybercriminals for hacking
Kimsuky is an advanced persistent threat (APT) organization that originates in North Korea and has a lengthy history of launching targeted attacks...
-

 1.4KMalware
1.4KMalwareCybercriminals Turn to Android Loaders on Dark Web to Evade Google Play Security
Malicious loader programs capable of trojanizing Android applications are being traded on the criminal underground for up to $20,000 as a way...
-

 916Malware
916MalwareCybercriminals Targeting Law Firms with GootLoader and FakeUpdates Malware
Six different law firms were targeted in January and February 2023 as part of two disparate threat campaigns distributing GootLoader and FakeUpdates...
-

 1.7KData Security
1.7KData SecurityCybercriminals hack FBI computer networks
The Federal Bureau of Investigation (FBI) is now investigating a cyber breach that occurred on its computer network and affected a computer...
-
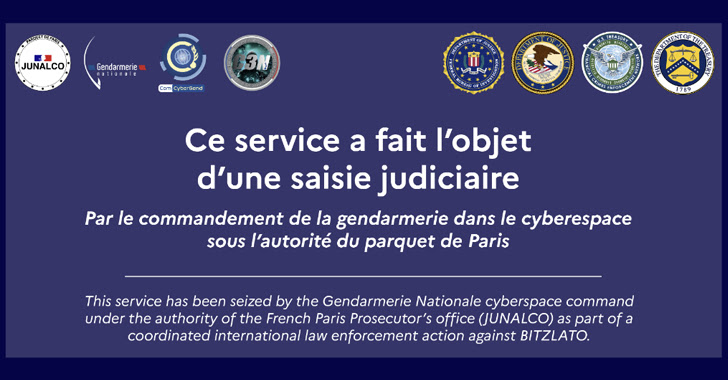
 735Malware
735MalwareBitzlato Crypto Exchange Founder Arrested for Aiding Cybercriminals
The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of Anatoly Legkodymov (aka Gandalf and Tolik), the cofounder of Hong...
-
 1.9KMalware
1.9KMalwareCybercriminals Using Polyglot Files in Malware Distribution to Fly Under the Radar
Remote access trojans such as StrRAT and Ratty are being distributed as a combination of polyglot and malicious Java archive (JAR) files,...
-

 4.1KIncidents
4.1KIncidentsData on 270,000 patients was stolen from the medical hospital in Louisiana by ransomware cybercriminals
During the month of October, cybercriminals broke into the computer system of a health care system in Louisiana, gaining access to the...
-

 1.1KData Security
1.1KData SecurityWhat should you do if your WhatsApp number is leaked by cybercriminals in the recent WhatsApp hack
A gang of hackers has been responsible for the hacking of WhatsApp in recent days, which resulted in the disclosure of a...
-
 4.8KMalware
4.8KMalwareRaspberry Robin Operators Selling Cybercriminals Access to Thousands of Endpoints
The Raspberry Robin worm is becoming an access-as-a-service malware for deploying other payloads, including IcedID, Bumblebee, TrueBot (aka Silence), and Clop ransomware....
-

 5.1KMalware
5.1KMalwareCybercriminals Used Two PoS Malware to Steal Details of Over 167,000 Credit Cards
Two point-of-sale (PoS) malware variants have been put to use by a threat actor to steal information related to more than 167,000...
-
 1.5KMalware
1.5KMalwareEternity Group Hackers Offering New LilithBot Malware-as-a-Service to Cybercriminals
The threat actor behind the malware-as-a-service (MaaS) known as Eternity Group has been linked to new piece of malware called LilithBot. “It...
-

 1.4KData Security
1.4KData SecurityPhishing alert: Giving your condolences for Queen Elizabeth II can leave your data in the hands of cybercriminals
Cybercriminals are taking advantage of the death of Queen Elizabeth II to launch phishing attacks, specifically these scammers directing users to malicious...






