Data Security
-

 2.5K
2.5KBrazilian marketplace integrator Hariexpress exposed 1.75 billion records
At the time of publishing this article, the data was still exposed and growing as there has been no response from Hariexpress....
-
 411
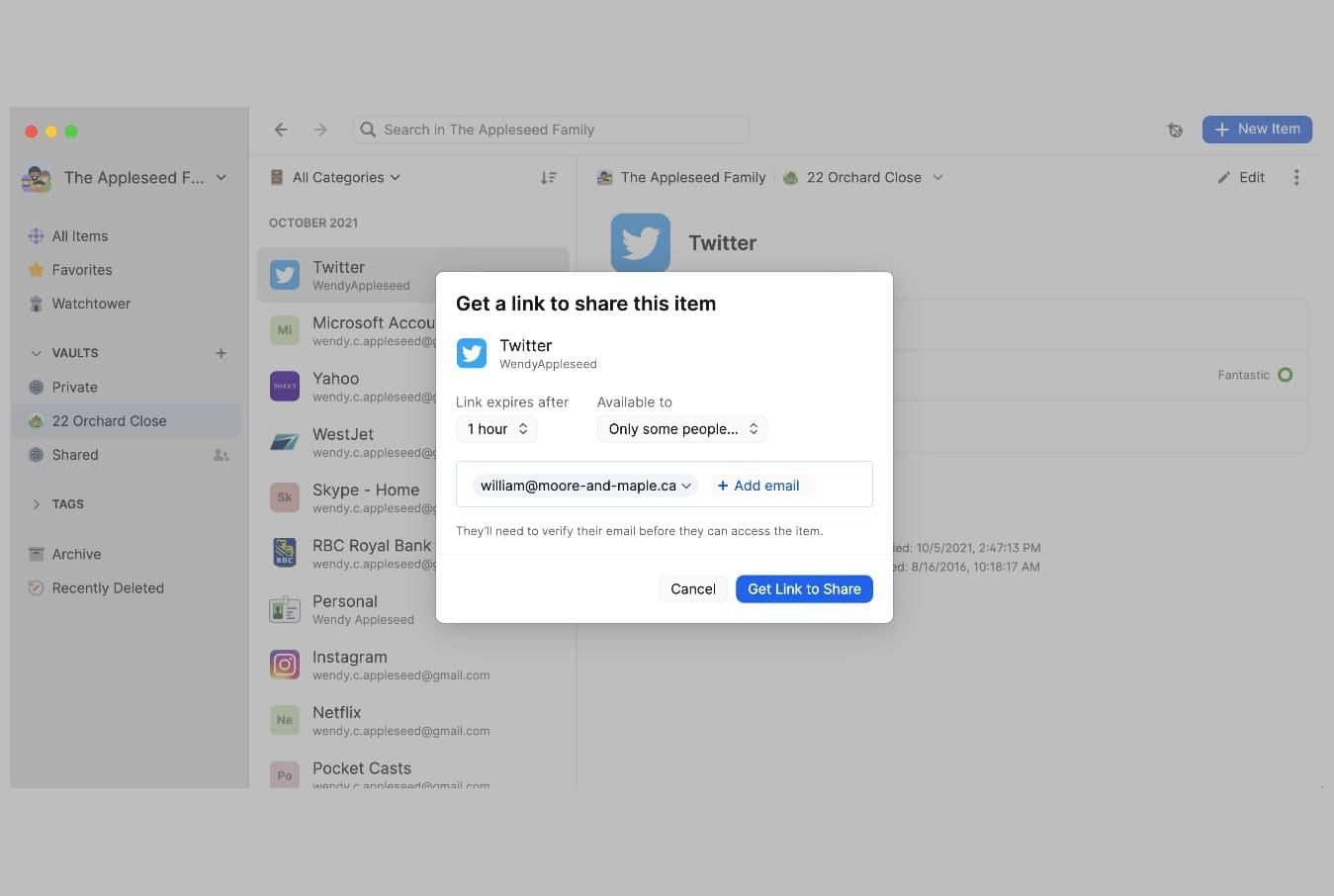
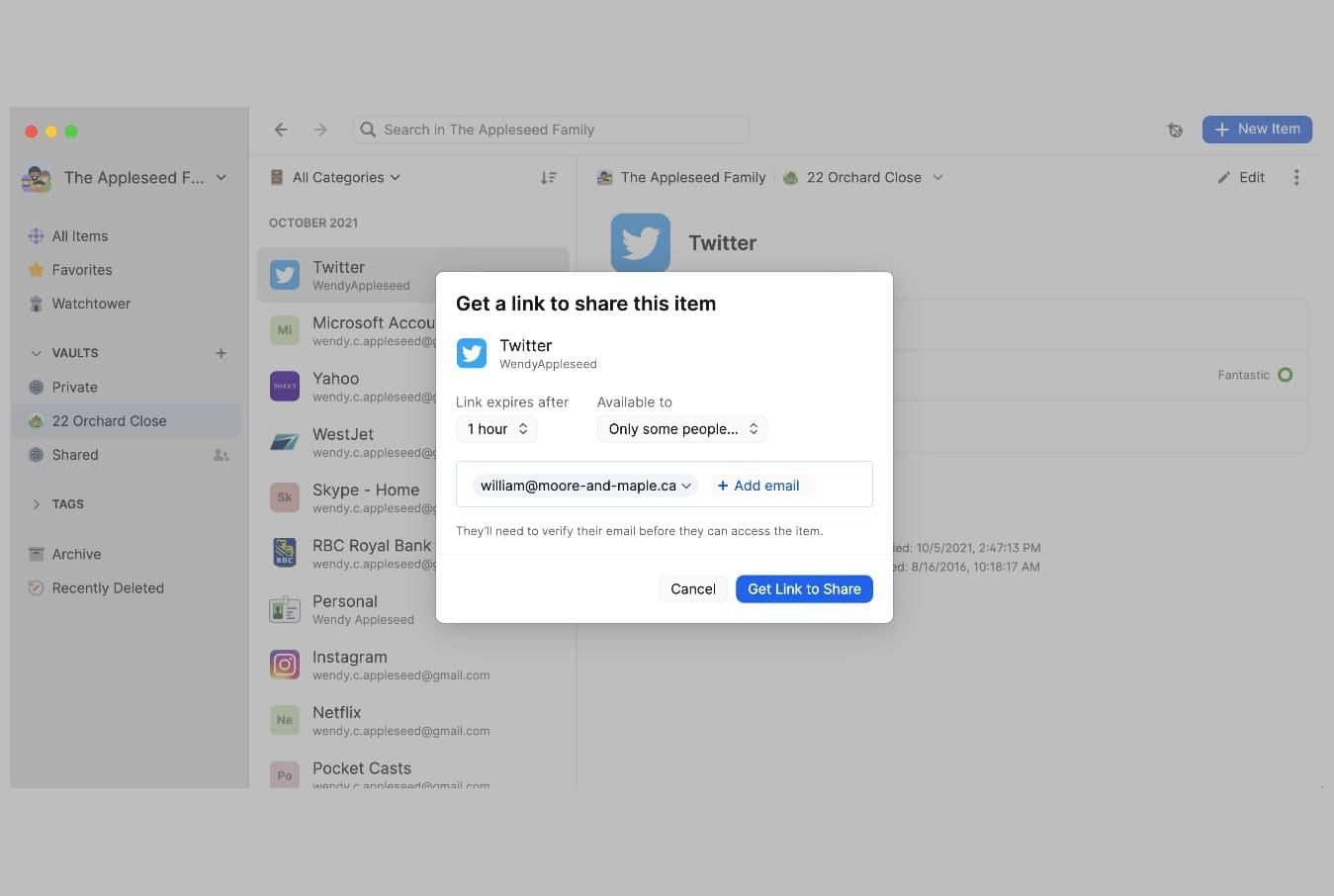
411Psst! tool by 1Password lets users share passwords using a link
1Password password manager has introduced a new tool called Password Secure Sharing Tool or Psst! that lets users share their passwords or...
-

 486
486OpenSea vulnerability allowed crypto stealing with malicious NFTs
Researchers investigated the issue in OpenSea after an increase in complaints about receiving and opening free airdropped NFTs to steal user funds....
-

 4.1K
4.1KStaggering growth of cybercrime and how data science helps improve online security
Did you know if you were to compare the money generated by cybercrime with the GDP of world nations, it would come...
-

 2.0K
2.0KIndia, Mexico, Nigeria, Singapore, South Africa and 25 other nations form a taskforce with United States to stop Ransomware payment
In an unprecedented event, officials and legislators from 25 countries, including the United States, Mexico, Canada, India, the European Union, Singapore, South...
-

 531
531How DocuSign phishing technique can be used to bypass your spam controls
Avanan cybersecurity specialists report the detection of a new phishing method in which threat actors look for susceptible targets among low-ranking employees...
-

 3.5K
3.5KHow to protect your Facebook account from hackers with new security feature “Facebook Protect”
To every single Public Relationships crisis it goes through, Facebook tries to respond with improvements to its service, especially in terms of...
-

 2.5K
2.5KNew technique for hacking NFT crypto wallets through OpenSea and MetaMask using NFT artwork
Cybersecurity specialists report the detection of a new attack method on non-fungible token (NFT) sale platforms and cryptocurrency wallets such as OpenSea...
-

 4.9K
4.9KMalKamak, the Iranian hacking group targeting telecommunications and aerospace companies
Cybersecurity specialists report the detection of a new Iranian hacking group that has been employing a never seen before variant of remote...
-

 3.4K
3.4KNew research: How to steal data from air-gapped devices using Ethernet cable as antenna without Internet
A research published by Ben Gurion University in Israel points to the discovery of a new mechanism for stealthily extracting data from...
-

 3.3K
3.3KTA544 threat actors hit Italian firms with Ursnif banking trojan
The IT security researchers at Proofpoint have discovered a new malware campaign in which threat actors from a group called TA544 are...
-
 1.1K
1.1KTelegram Bots Stealing One-Time Passwords
So far two Telegram bots called SMSRanger and BloodOTPbot have been found taking part in this malicious campaign. Intel 471 researchers report...
-
 3.6K
3.6KNSA, CISA Release Guidelines to Secure VPNs
State-backed hackers have been constantly exploiting vulnerabilities in VPNs to breach critical cyberinfrastructure in the United States, agencies have warned. The National...
-

 1.4K
1.4KGriftHorse Android malware hit 10 million devices in 70 countries
GriftHorse malware uses malicious apps to subscribe victims to premium services that cost them $42 (£30 –€36) per month. The IT security...
-

 1.5K
1.5KApple AirTags can be used as trojan for credential hacking
According to security researcher Bobby Raunch, the attack exploits the way Lost Mode of AirTags is set up. Although Apple’s Bluetooth-enabled item...
-
 1.8K
1.8KHackers exploit 2FA flaw to steal crypto from 6,000 Coinbase users
Coinbase is working to reimburse the customers for the funds they have lost and help them regain control of their accounts. Coinbase...
-
 928
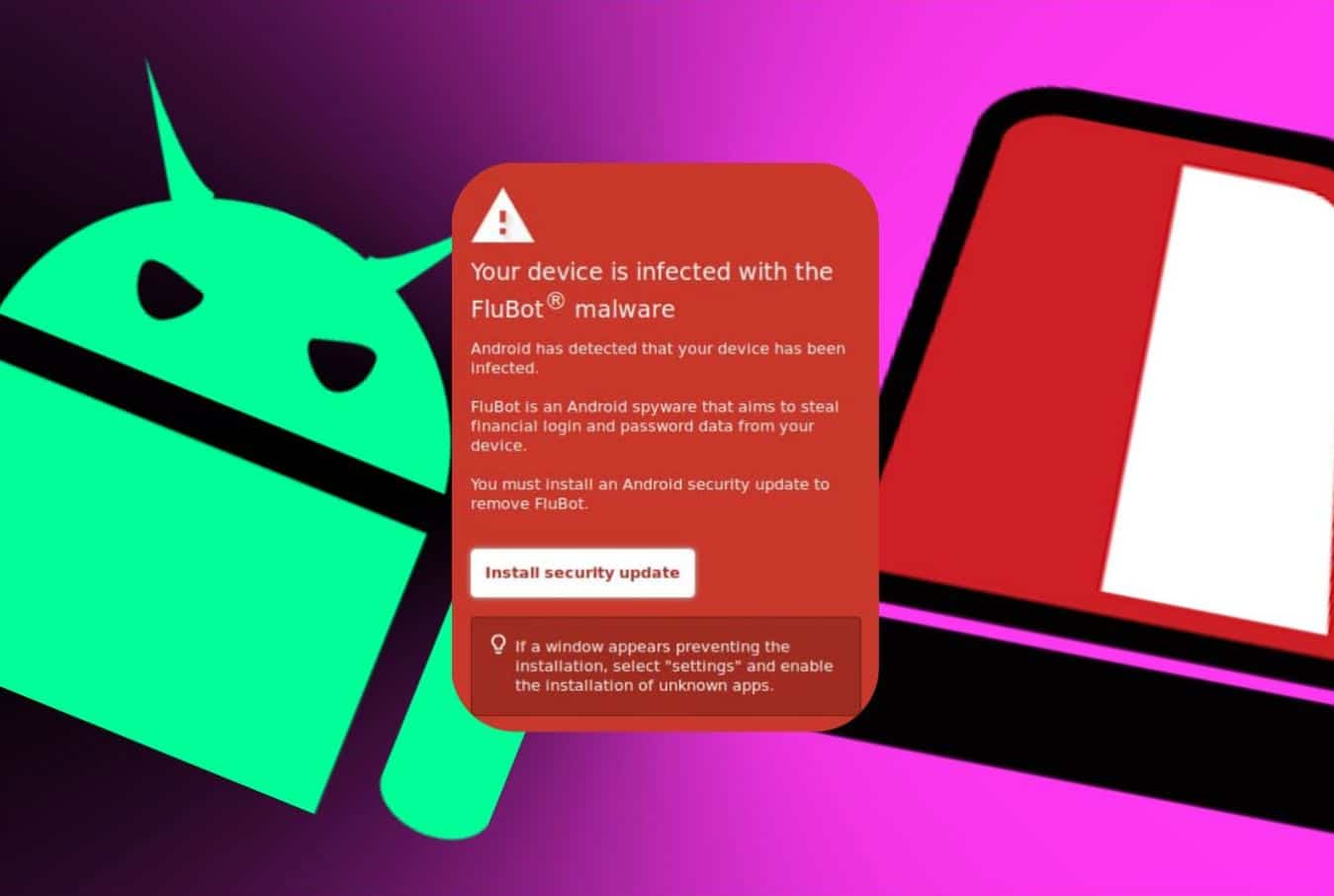
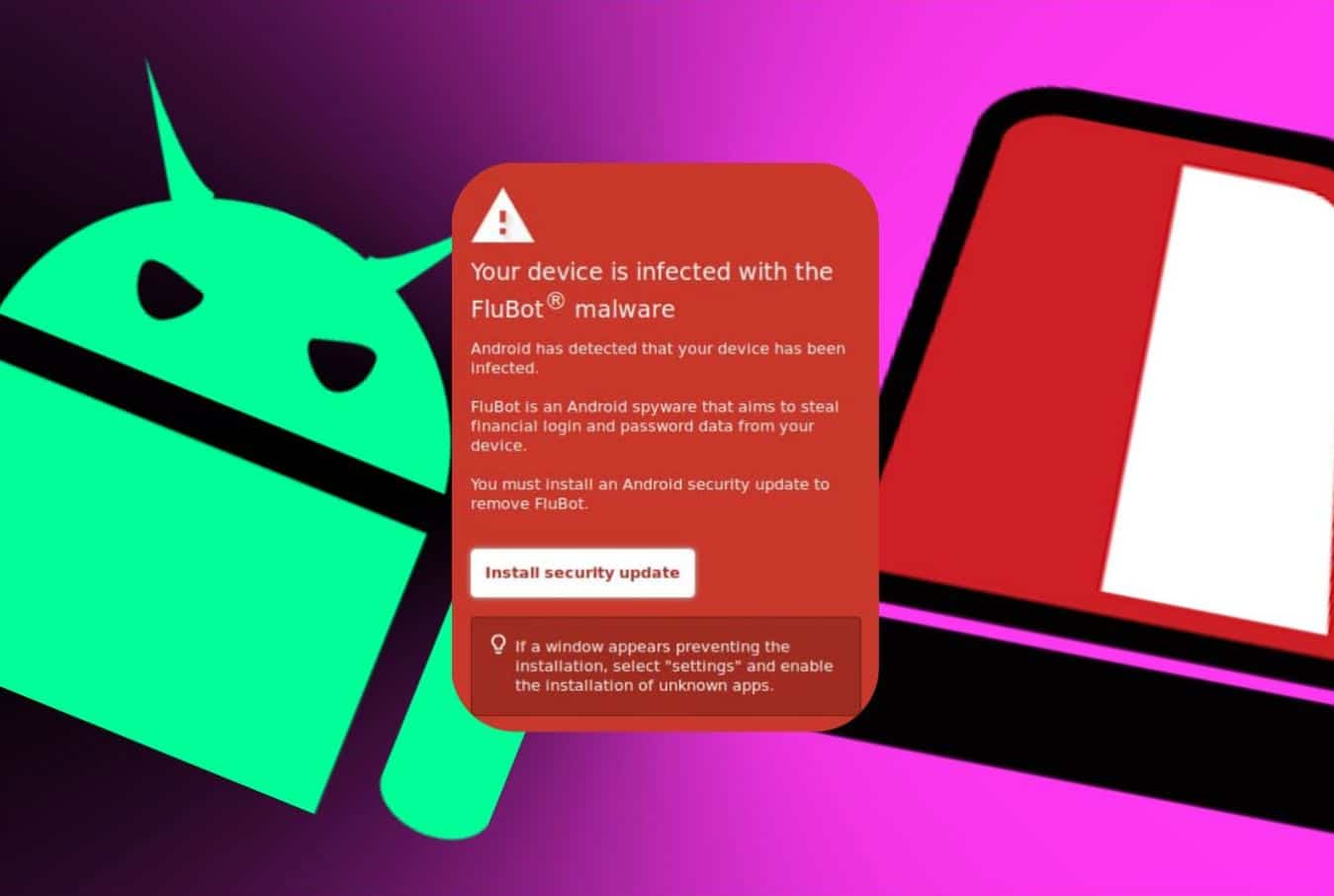
928Android flubot malware installs itself by faking security update
The security update is obviously phony but looks authentic that can deceive users into installing Flubot malware on their devices. New Zealand’s...
-

 5.0K
5.0KCybersecurity risk assessment: Does Your Company Need It?
Cyber security risk assessments are a framework for detecting, analyzing, and prioritizing operational risk – Let’s dig deeper into why your company...
-

 3.9K
3.9KNew secure payment feature in upcoming versions of Google Chrome
As part of the latest beta version of Chrome 95, Google announced the inclusion of a feature for secure payment, basing its...
-
 2.4K
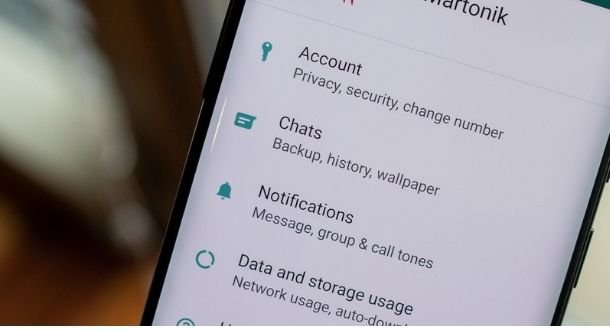
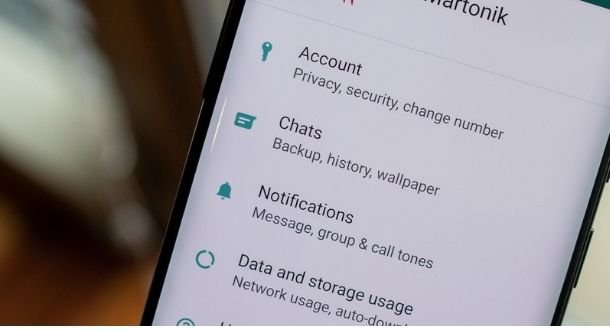
2.4KClicking this WhatsApp backup notification can allow hackers to spy on your conversations
Cybersecurity specialists report the detection of a massive phishing campaign in which threat actors pose as WhatsApp employees in order to trick...
-
 4.6K
4.6KDangers of DNS poisoning and how to prevent it
The cyberworld is constantly evolving, and with evolution comes new methods of committing crimes. DNS poisoning is one such threat that might...






