Data Security
-
 5.2K
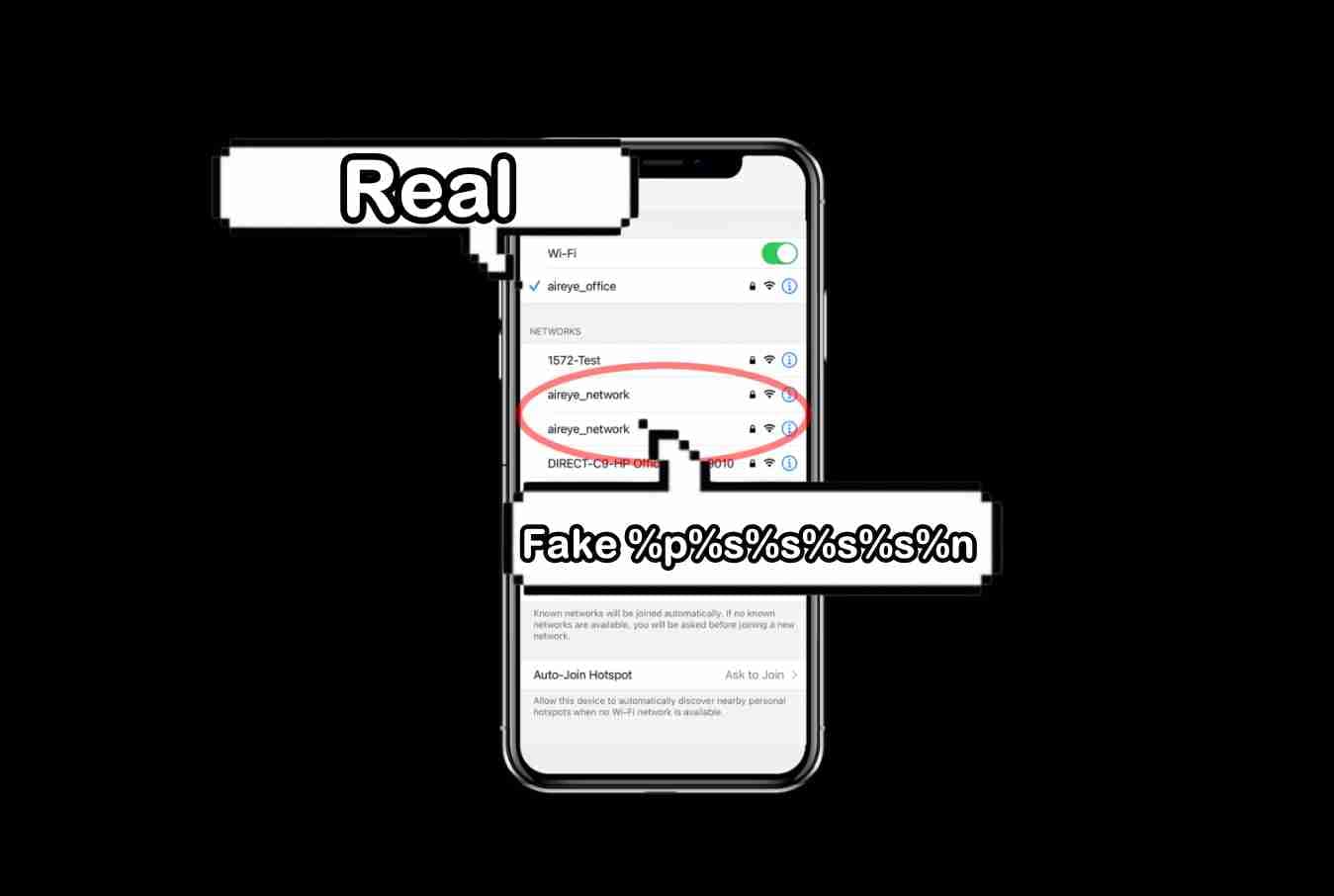
5.2KSSID Stripping flaw lets hackers mimic real wireless access points
SSID Stripping has emerged as a significant threat because it impacts almost all software platforms, including MS Windows, macOS, Apple iOS, Ubuntu,...
-
 1.4K
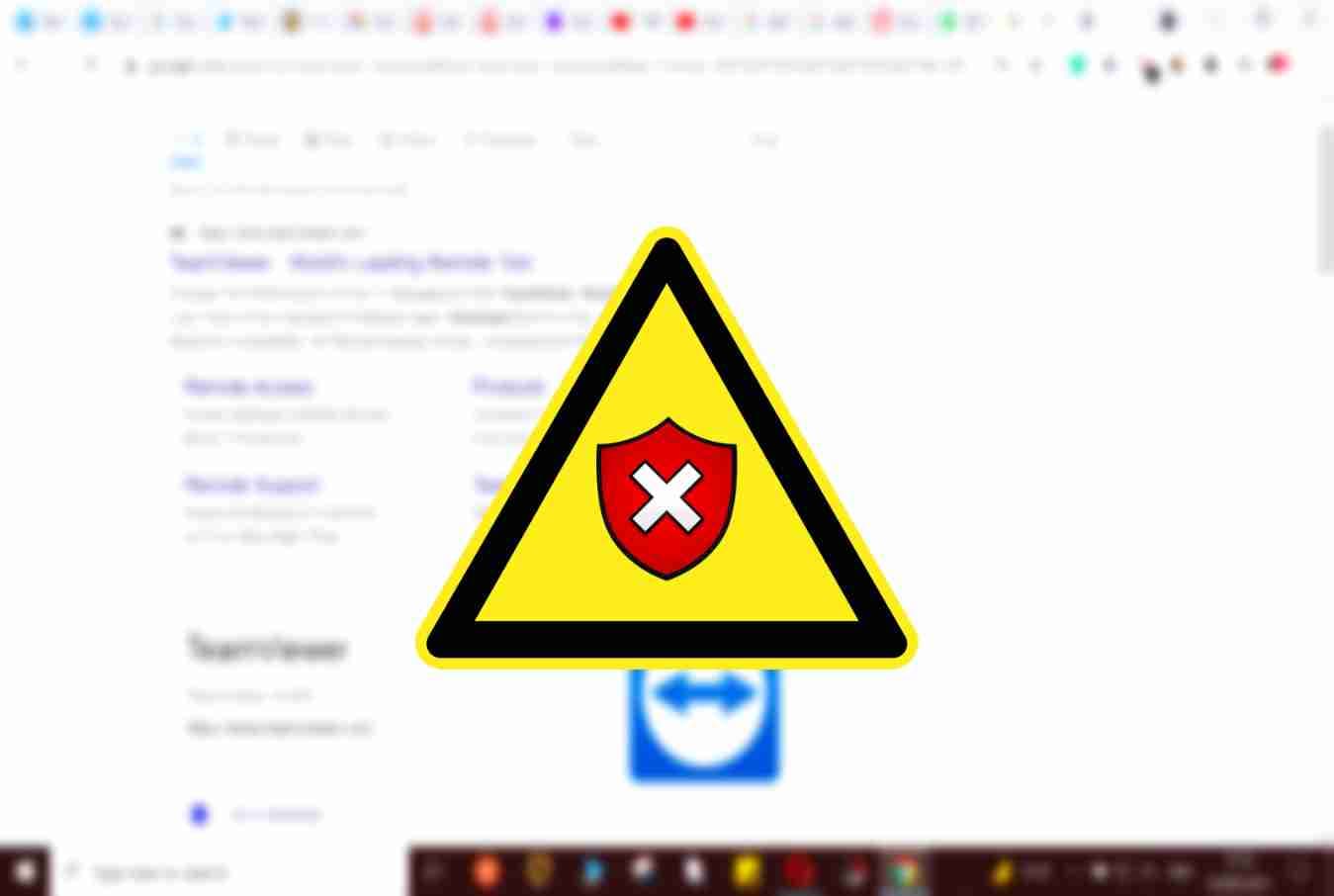
1.4KFake TeamViewer download ads distributing new ZLoader variant
The infection chain starts when the victim clicks on an ad from Google on the search results page. SentinelLabs researchers have identified a...
-

 5.0K
5.0KUniversal decryptor key for Sodinokibi, REvil ransomware released
Romania-based cybersecurity firm Bitdefender has released the much-awaited universal decryptor for REvil ransomware victims in collaboration with an undisclosed but trusted law...
-
 4.0K
4.0KDownload Kali Linux 2021.3 with Kali NetHunter on smartwatch, new tools
Kali Linux 2021.3, comes with a range of new pentest tools, improved virtualization support, and a brand-new OpenSSL configuration to enhance the...
-
 1.2K
1.2KMirai botnet exploiting Azure OMIGOD vulnerabilities
The infamous Mirai botnet lets threat actors use compromised devices to carry out large-scale and crippling DDoS attacks. Critical Microsoft Azure vulnerabilities...
-
 4.7K
4.7KNew version of Jupyter infostealer delivered through MSI installer
Originally, Jupyter infostealer is known for stealing data from popular browsers like Chrome and Firefox. In 2020, Hackread reported about Jupyter, a trojan...
-

 4.7K
4.7KNew Google Chrome update has a dangerous idle detection feature that will track system usage in detail
Despite the disagreement of companies such as Apple and Mozilla, Google security teams released the Chrome 94 update for Android devices and...
-

 665
665New malware can infect Windows and Linux devices; 70 different VirusTotal antvirus can’t detect it
The Windows Subsystem for Linux (WSL) is a companion feature released by Microsoft in 2016 to run a Linux image in a...
-

 2.5K
2.5KSensitive Walgreens customer data leaked, including COVID-19 test results
Recent security reports indicate that the results of COVID-19 tests conducted by the pharmaceutical company Walgreens could be exposed to threat actors....
-

 1.4K
1.4KUnjustified: Former NSA employees who created Pegasus-like tools for UAE will pay $1.6 million to avoid jail time
In a controversial decision, the U.S. Department of Justice (DOJ) announced that it reached an agreement with three former US intelligence agents,...
-

 1.2K
1.2KRead deleted WhatsApp messages without any additional application for iPhone and Android. Never seen before trick
WhatsApp has lots of little-known functions, although an Internet search is enough to master these techniques. An example is a function to...
-

 1.8K
1.8KREvil ransomware gang is back after disappearing amid Kaseya attack
The official .Onion website of REvil ransomware gang is back online while its chat platform and clearnet site is still offline. The...
-
 4.6K
4.6KMalware droppers for hire targeting users on fake pirated software sites
Some fake piracy websites have also been found distributing Crypto Bot and Raccoon Stealer malware in cracked software. Sophos Labs’ security researchers...
-

 2.3K
2.3KHackers dump login credentials of Fortinet VPN users in plain-text
Fortinet VPN users are urged to reset their passwords as the company has acknowledged the data to be legitimate. Popular network security...
-

 630
630Microsoft warns of Azure vulnerability which exposed users to data theft
Currently, there is no evidence that this particular Azure vulnerability was exploited to gain unauthorized access to customer data. In its newest blog...
-

 825
825What are endpoint security threats, and how can they enter your device?
Endpoint security threats are usually targeted towards corporate organizations but can often use private individuals to get inside these companies – Let’s...
-
 4.5K
4.5KYandex hit by largest DDoS attack involving 200,000 hacked devices
Yandex, a Russia-based technology and search engine giant, has confirmed that its servers were targeted with cyber history’s largest DDoS attack last...
-

 4.4K
4.4KExperts concerned over emergence of new Android banking trojan S.O.V.A.
S.O.V.A. Android banking trojan is actively being advertised on Russian hacker and cybercrime forums. In early August 2021, ThreatFabric’s team of researchers...
-

 1.4K
1.4KHow this job offer WhatsApp message allowed spying thousands of user accounts easily
Since its mass adoption as an instant messaging platform, WhatsApp has been a tool widely used by cybercriminal groups to deploy some...
-

 4.3K
4.3KSecurity risks to your mobile app and how to avoid them
Mobile devices, while convenient tools for communication and engagement, also come with their fair share of security risks — particularly when it...
-
 3.4K
3.4K$120 charging cable O.MG remotely steals data from Apple devices
Originally, O.MG Cable was introduced in 2019. In 2019, at DEFCON, an IT security researcher going by the online handle of MG...






