Hacked
-

 218
218Dozens Of Popular iPhone Apps Caught Selling Your Location Data: Here’s What To Do
A group of researchers from the security firm GuardianApp has found that dozens of popular iPhone applications are selling the location data of...
-

 183
183Tesla Launches Bounty Program; Allows Good Faith Hackers To Inspect Firmware
Tesla announced on Twitter that they are launching a bug bounty program and are allowing “good faith” researchers to probe into its...
-

 254
254North Korean Hacker Charged Over WannaCry Attack And Sony Hacking
The U.S. has charged and sanctioned a North Korean hacker who is accused of being responsible for the infamous WannaCry Cyberattacks of...
-

 171
171Shahid Kapoor’s Instagram & Twitter Accounts Hacked; Kriti Sanon Also Targeted
All the major tech giants appear to be doing everything in their power to improve the user security and privacy; Google just...
-
 221
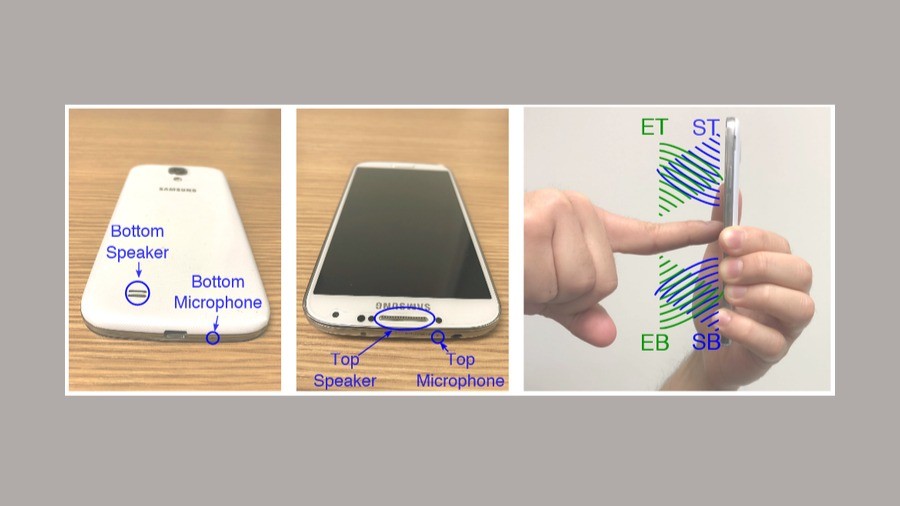
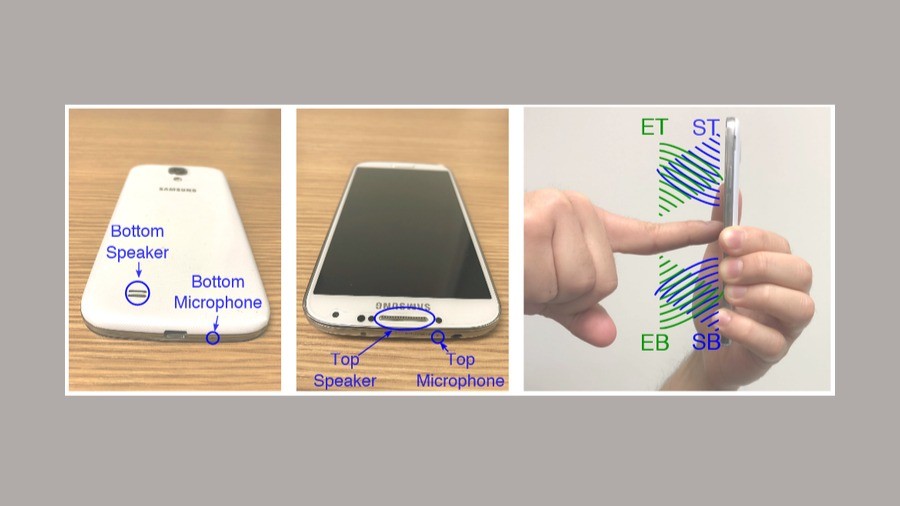
221Your Android Lock Screen Pattern Can Be Hacked With Phone’s Speaker & Microphone
Researchers from the universities in Sweden and the UK have stumbled on a new technique using which your smartphone’s speaker and microphone...
-
 210
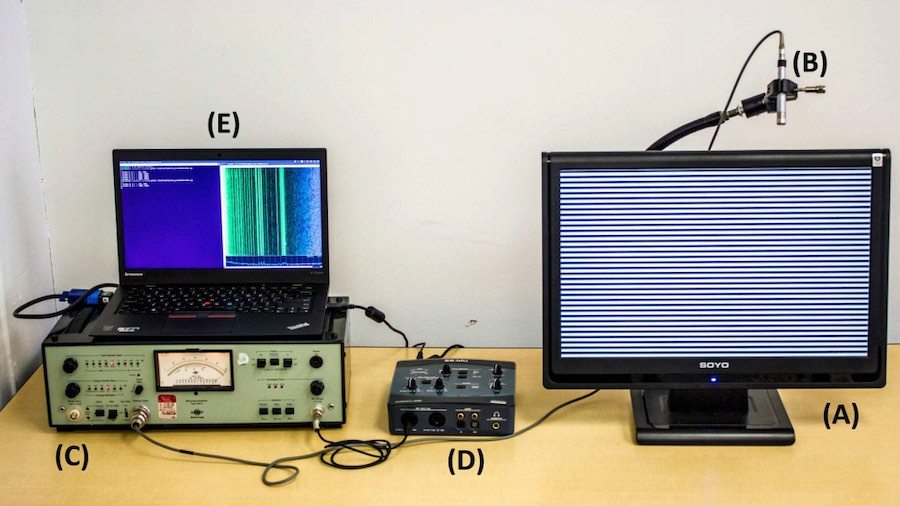
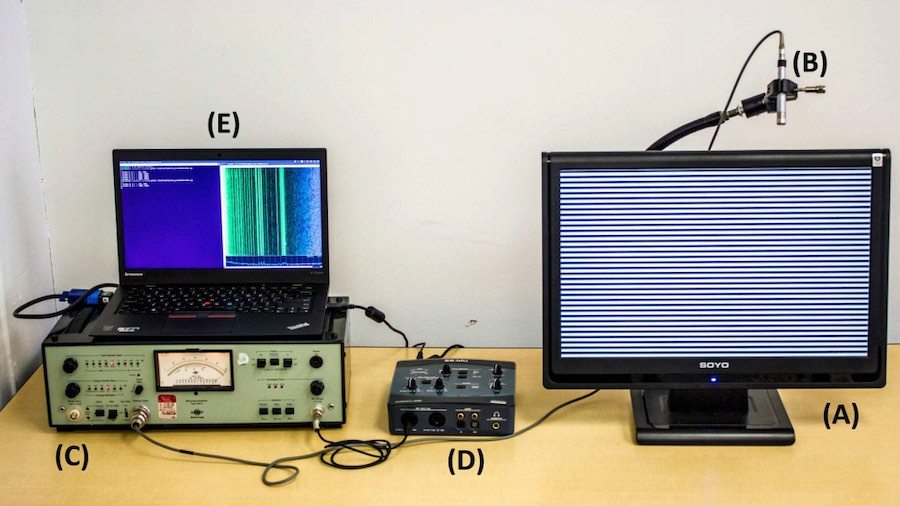
210How Hackers Can Spy On You By “Listening” To LCD Screens
You might have come across the term side-channel attacks while reading news articles on Spectre and Meltdown. These exploits were possible due to...
-
 187
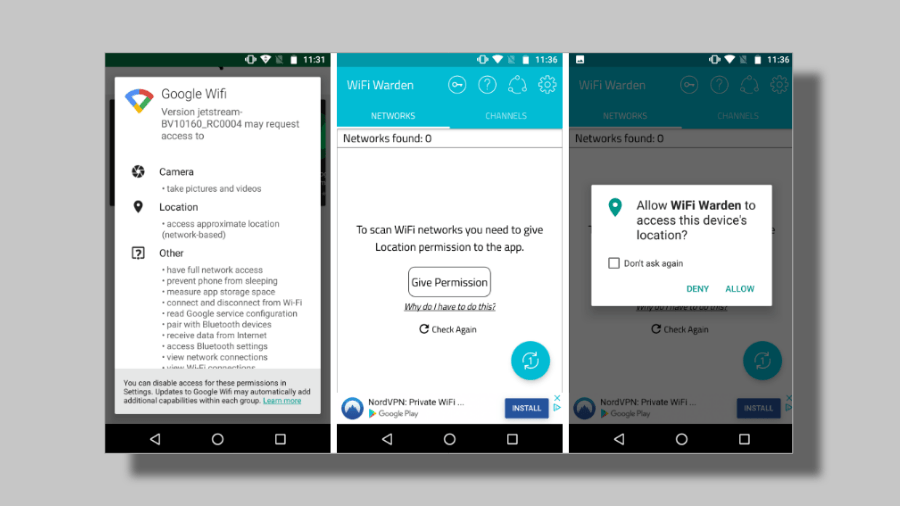
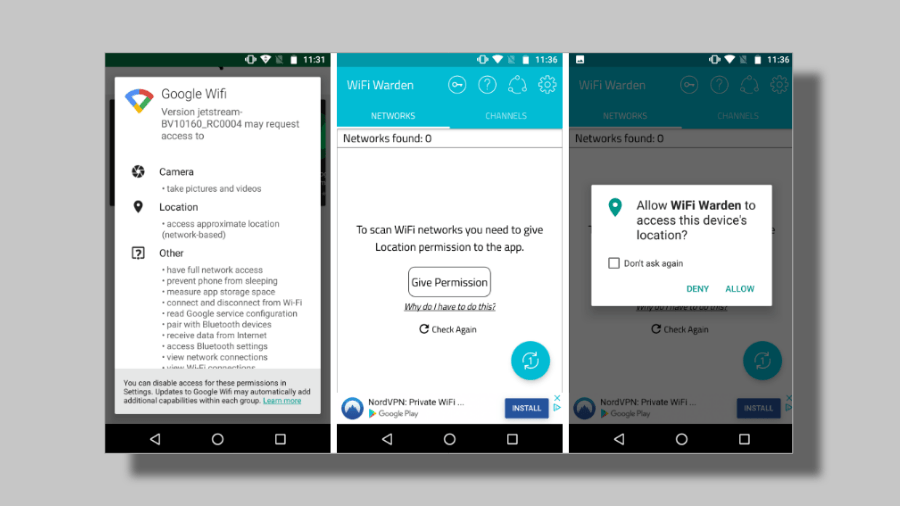
187Android 9 Pie Safe From The WiFi Bug That Leaks Sensitive Data
Researchers have discovered a vulnerability in all Android versions except Android 9, which could allow attackers to capture WiFi broadcast data and even...
-

 215
215Firefox Browser Will Soon Block All Web Trackers By Default
There’s no denying the fact that data collection on the web is one of the fundamental ways how our Internet actually works....
-
 428
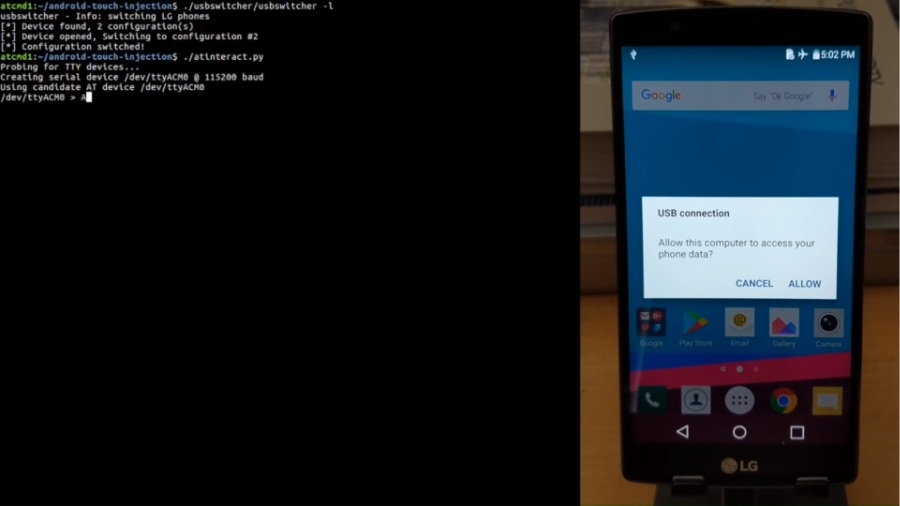
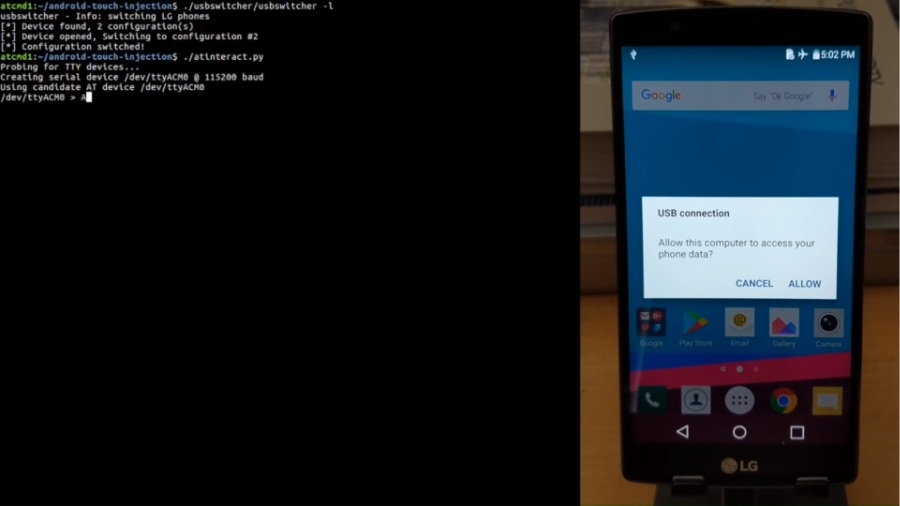
428How These Android Smartphone Can Be Hacked With Simple AT commands
According to a research, millions of Android devices from 11 OEMs are vulnerable to attacks from simple AT commands. These AT commands or...
-

 225
225Windows Task Scheduler Zero-Day Exposed; No Patch Available
A zero-day flaw has been revealed by a Twitter user SandboxEscaper, for the Windows Task Scheduler in 64-bit Windows 10 and Windows Server 2016...
-

 159
159Your Smart Electricity Meters Can Track Every Activity, Court Ruling Warns
Nowadays, smart devices have taken the wicked roads, contrary to the original plan of helping the citizens of the world. A few...
-

 197
197Google Found A Serious Security Flaw In Fortnite Installer For Android
Epic Games’ decision to make its popular game Fortnite available on Android through its own website instead of Google Play Store seems...
-

 236
236Android Spyware ‘Triout’ Records Phone Calls, Steal Pictures & Texts
Researchers at Bitdefender have identified a new powerful Android spyware named ‘Triout.’ It can secretly record phone calls, collect pictures, videos, text...
-

 287
287USBHarpoon: How “Innocent” USB Cables Can Be Manipulated To Inject Malware
A researcher from SYON Security has managed to build a modified USB charging cable that will enable hackers to transfer malware on...
-

 257
257A 16-Year-Old Hacked Apple Servers And Stored Data In Folder Named ‘hacky hack hack’
Apple’s tall claims of keeping your data secured were challenged by an Australian teenager when he repeatedly hacked Apple servers and downloaded...
-

 272
272Audio & Video Tags Exploited For Collecting Sensitive Data in Google Chrome: Update Now
Ron Masas, a security researcher, working with Imperva, has recently flagged a vulnerability in Google Chrome that leveraged audio and video tags...
-
 180
180Add-on Recommended By Mozilla Caught Logging Users’ Browsing History
According to the reports by Mike Kuketz, an independent security blogger from Germany and uBlock Origin, an add-on named “Web Security” has been...
-

 329
329Spectre-like “Foreshadow” Flaw In Intel CPUs Can Leak Your Secrets
When the Spectre and Meltdown security flaws in Intel chips were disclosed earlier this year, security researchers called it a loophole so...
-
 306
306Google Is Tracking You Non-stop Even If You Tell It Not To: Report
While using your Android or iOS device, if you choose the option to pause the location sharing, what are your expectations? While...
-

 362
36225 Smartphone Models Found Shipping With Severe Firmware Flaws: Defcon 2018
This year’s Defcon witnessed many interesting events, including the hacking of voting machines by 11-year-olds and macOS’s vulnerabilities to grant permissions to...
-

 334
334Defcon 2018: Hacker Exploits Vulnerabilities In macOS With “Invisible Clicks”
At Defcon 2018, ex-NSA staffer and a popular Mac hacker Patrick Wardle presented his research work which involved bypassing the layers of...






