Hacked
-
 785
78511-Year-Old Changes Election Results On Florida’s Website: DefCon 2018
Defcon 2018, one of the most popular hacking conferences, is going on in Las Vegas. The conference, every year, sees famous hackers...
-

 266
266Black Hat 2018: A Pacemaker Hack That Can Stop The Heart
Hackers from all over the world flocked to the Black Hat 2018 security conference that was held in Las Vegas this week....
-
 340
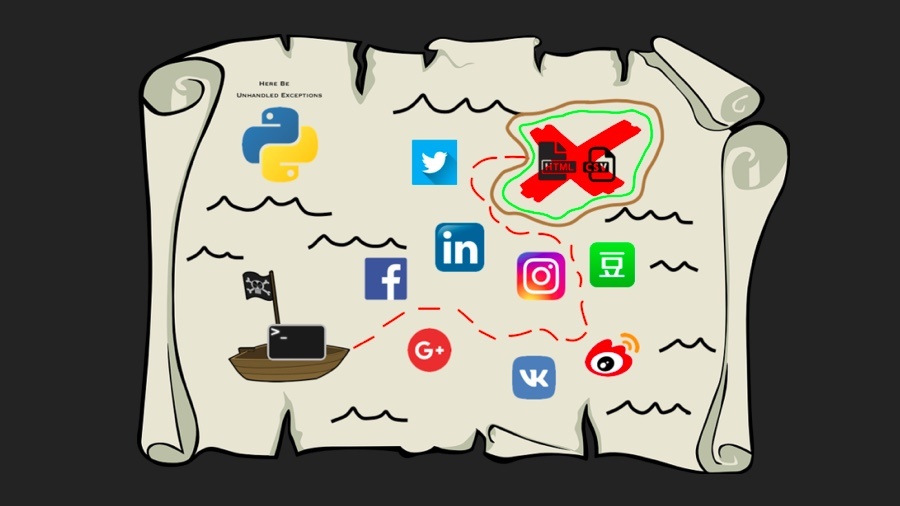
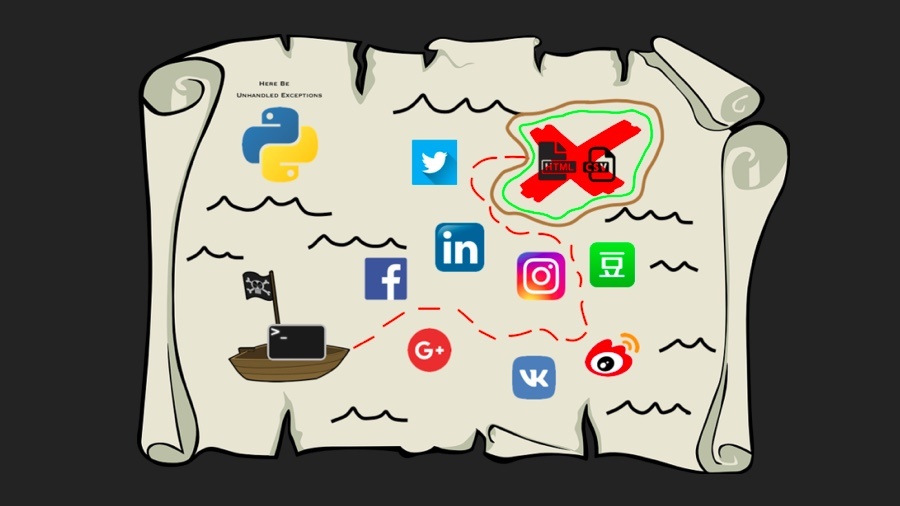
340Social Mapper: This Open Source Tool Lets “Good” Hackers Track People On Social Media
There are tons of automated tools and services that any shady hacker can employ to grab the public data on Facebook, Twitter,...
-

 264
264Windows Lock Screen Bypassed Using Cortana Vulnerability; Already Patched
In another interesting research work presented at Black Hat USA 2018, a group of researchers from Kzen Networks and Isreal Institute of...
-

 223
223Black Hat 2018: Satellite Communication Systems Hackable; Threat For Aviation Industry
Black Hat USA 2018 which commenced on August 4 has seen some of the famous researchers putting out their research works. While...
-

 230
230WhatsApp Vulnerability Lets Attackers Alter Your Messages And Spread Fake News
A new vulnerability has surfaced in WhatsApp’s encryption method that allows attackers to alter messages and user identities in group chats. This...
-

 247
247DeepLocker: Here’s How AI Could ‘Help’ Malware To Attack Stealthily
By this time, we have realized how artificial intelligence is a boon and a bane at the same time. Computers have become...
-

 277
277Snapchat’s Source Code Leaked Online, Archived on Github
Hackers leave no chance of obtaining the source codes of popular apps as they aren’t public. However, in a recent incident, someone...
-

 215
215This Tool Stops Your Data From Passing Through Surveillance-Happy Countries
Many of us already know that the internet traffic passes through different countries before reaching its destination. But did you know that...
-

 336
336CCleaner Facing Backlash For User Data Collection And Active Monitoring
Ever since Avast acquired Piriform’s CCleaner, users have been complaining of the software going downhill as they often encounter annoying ads and...
-

 237
237Reddit Hacked: Here’s How To Know If You Were Compromised
The popular news aggregator website Reddit has revealed that it suffered a data breach between June 14 and 18. While Reddit calls the...
-
 281
28111 Million Android, iOS, Chrome, And Firefox Users Infected By Spyware: Delete These Apps Now
It seems that efforts being made by Google and Mozilla to safeguard their Chrome and Firefox extension store aren’t turning out to...
-
 267
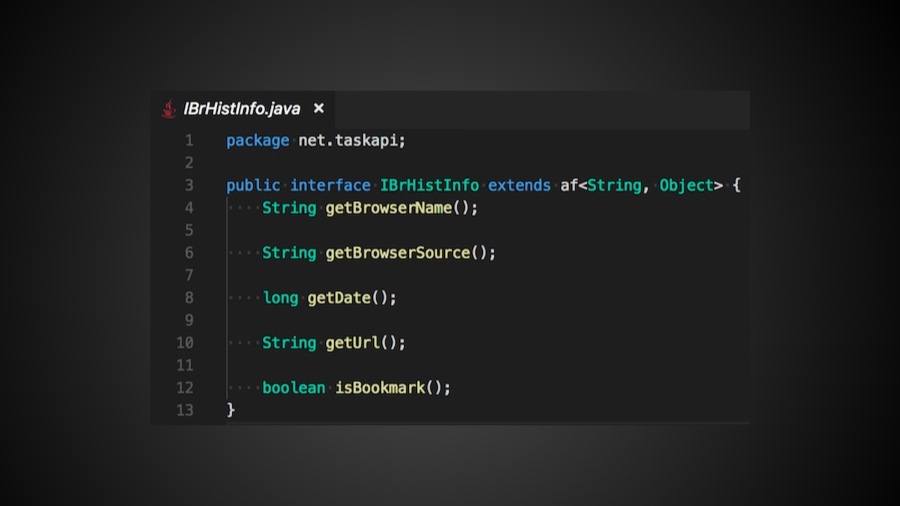
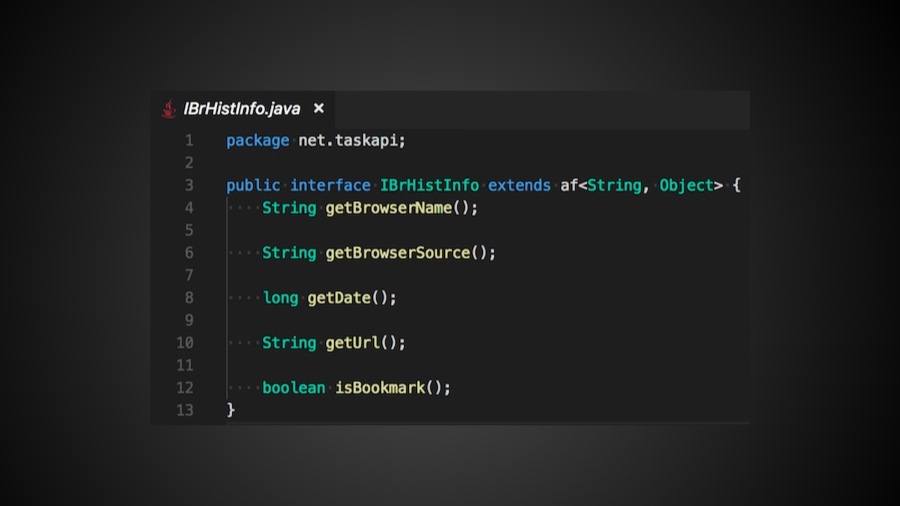
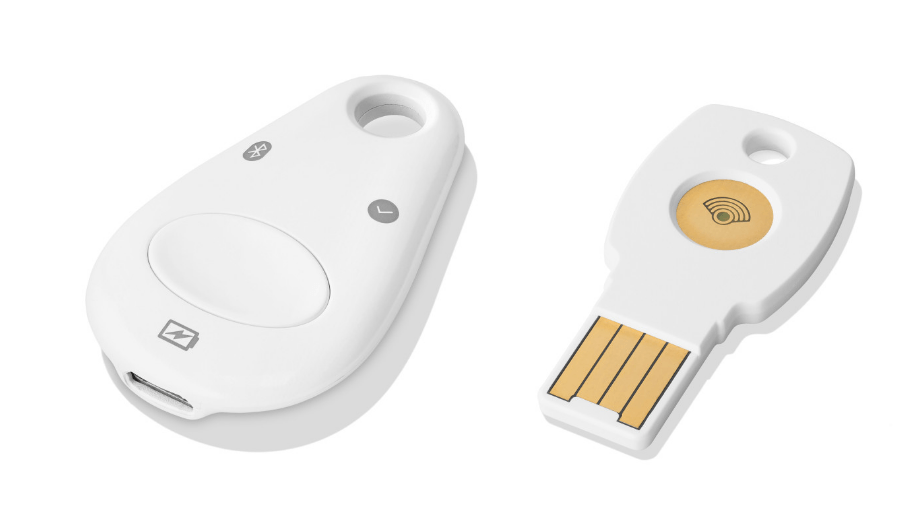
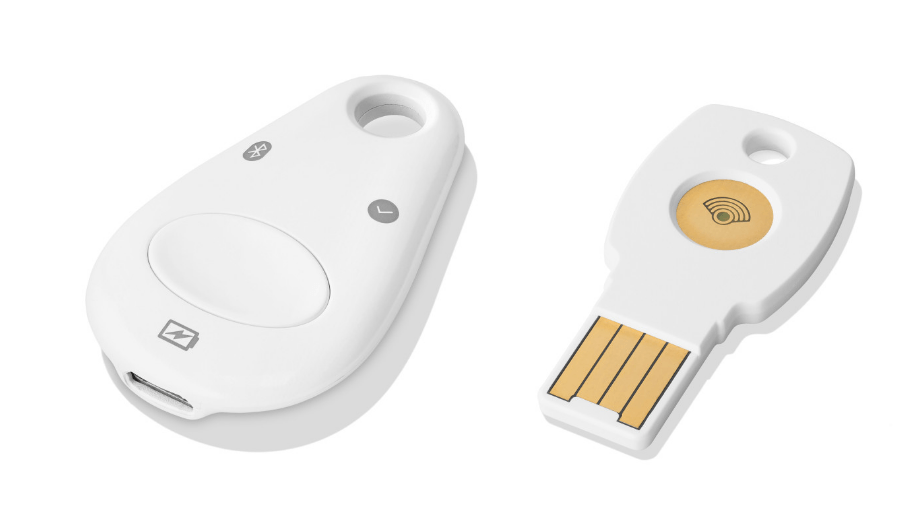
267Google Launches ‘Titan Security Key’ To Boost Your Online Security
Google has launched the public version of the security key used to protect its 85,000 employees from phishing and other cyber attacks...
-

 228
228Hacking Unattended Laptop In Under 5 minutes: Researcher Shows How
We all are aware of the cyberhacking and phishing that takes place in the digital world. And safeguarding us from petty hacks is...
-
 258
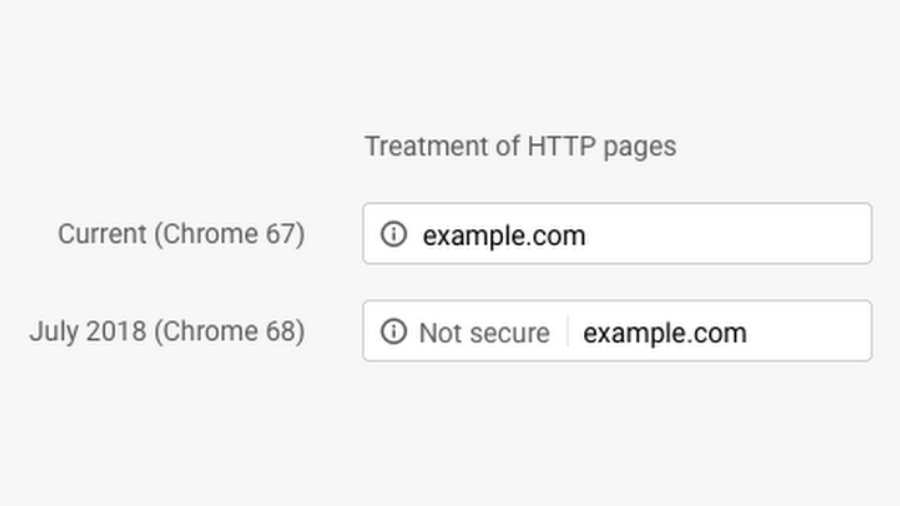
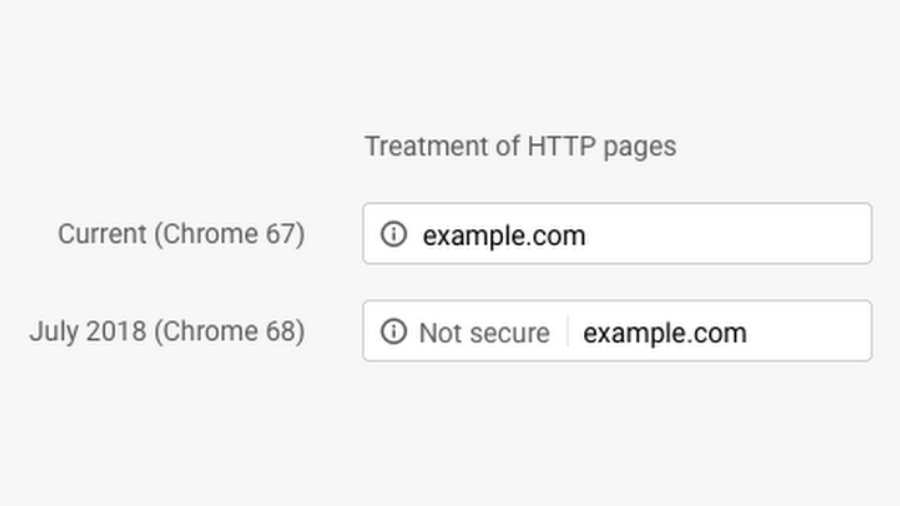
258Here’s Why Chrome Is Now Showing Millions of Websites As “Not Secure”
Google is taking the privacy quite seriously, and the new Chrome security update will undoubtedly put a significant toll on all your...
-

 285
285Intel Patches New ME Flaws That Could Let Hackers Run Arbitrary Code: Check For Patches
Another day, another security fix released by Intel. In a blog post, Positive Technologies has detailed four different vulnerabilities found in the...
-

 242
242Amazon, Reddit And Others Fail To Warn Us About Dumb Passwords
Believe it or not, there is still a large number of people who use passwords such as “password,” “password123”, “[dog’s name]1” and others...
-
 224
224Here’s How Hackers Are Using Google’s Servers To Host Malware For Free
In the past, the security researchers have come across cases where notorious hackers were able to use EXIF data of images to...
-
 251
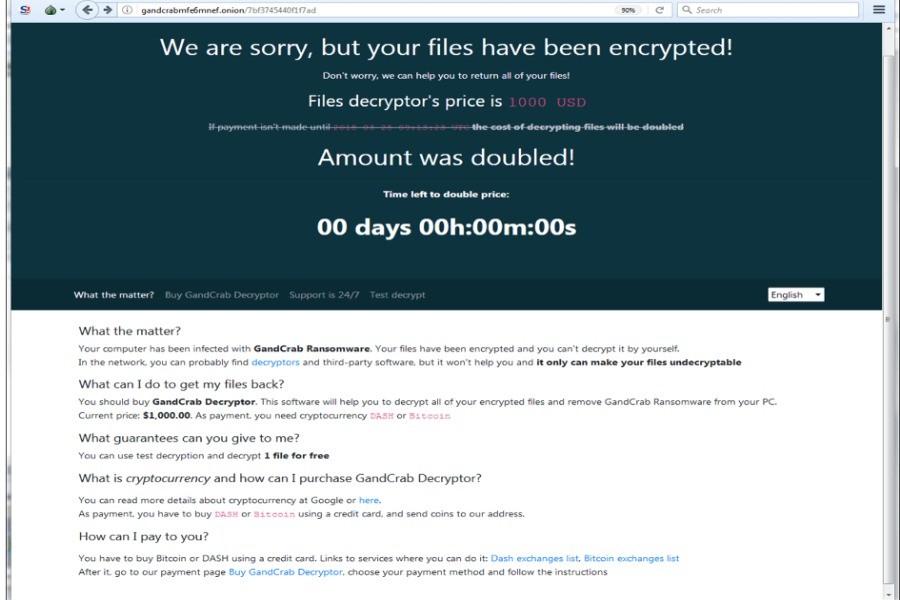
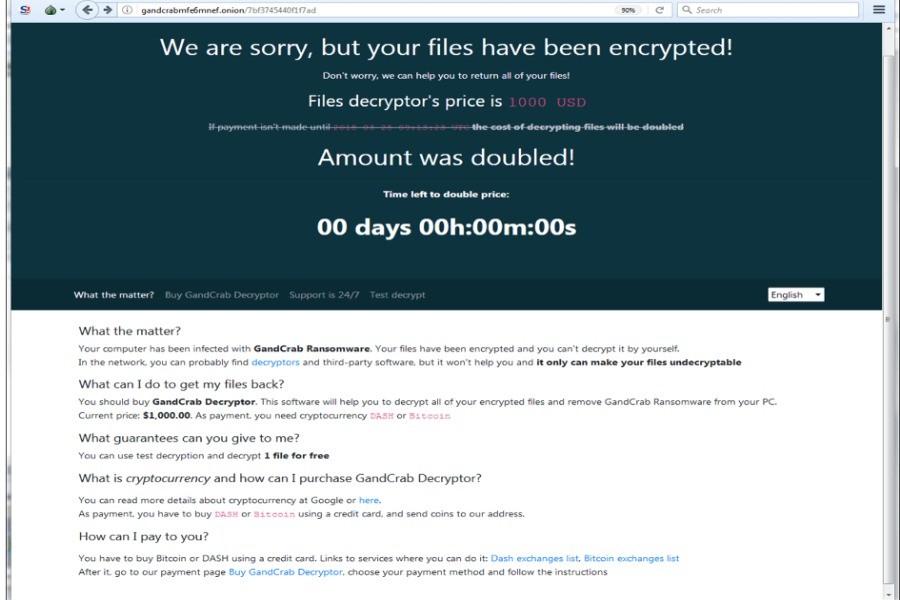
251Rewritten GandCrab Ransomware Targets SMB Vulnerabilities To Attack Faster
GandCrab ransomware, which has created a hullabaloo in the cybersecurity industry by constantly evolving, has yet again caused a commotion. The latest...
-

 258
258Malware Attack On Arch Linux AUR Repository; Three Packages Infected So Far
Arch Linux software repository named Arch User Repository (AUR) has been infected by malware. As many as three Arch Linux packages available...
-
 210
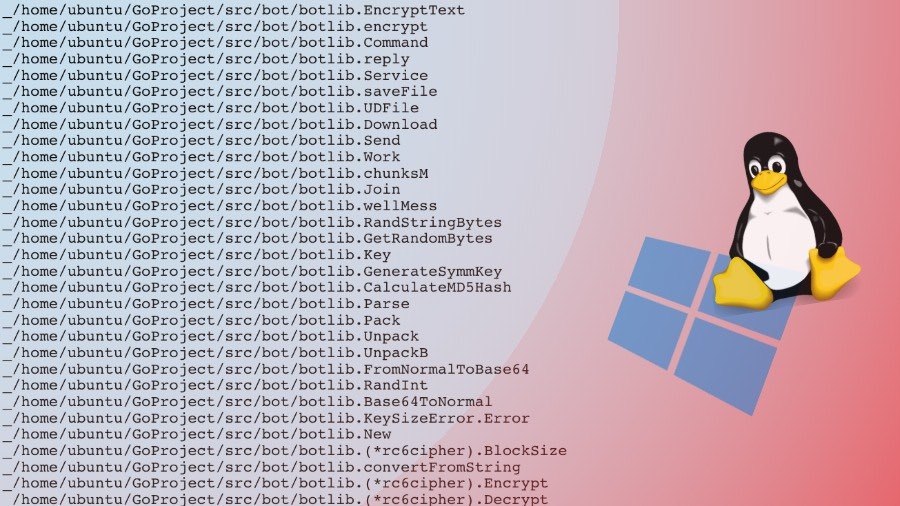
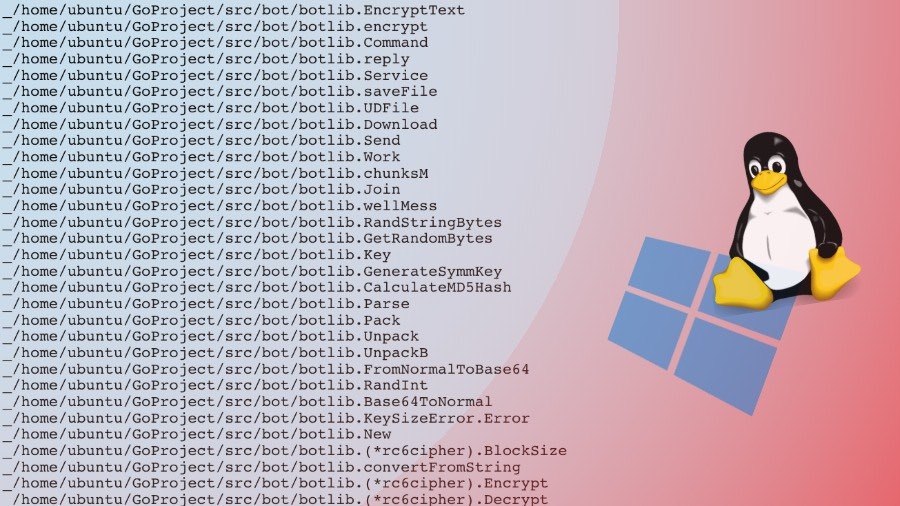
210WellMess: This Go-based Malware Attacks Both Linux And Windows Machines
There’s no doubt that Linux and Mac are more secure operating system choices as opposed to Microsoft Windows. But this doesn’t mean...






