Hacked
-

 236
236iOS 11.4.1 Launched With A New Feature To Stop Cops From Cracking Your iPhone
After receiving complaints regarding abnormal battery discharge across different models of iPhone, Apple has released iOS 11.4.1 which brings minor bug fixes...
-

 235
235Amazon Is Selling Facial “Rekognition” Tech To Government And You Should Be Worried
Amazon is selling its facial recognition technology called Rekognition to the American law enforcement agencies — this news has been making rounds in...
-

 213
213Rakhni Trojan Becomes Smart: Now Infecting With Either Ransomware Or Cryptomining
Rakhni Trojan which was first discovered in 2013 has evolved over the course of five years. As an addition to its already...
-

 263
263Keyboard Attack “Thermanator” Steals Your Passwords Using Body Heat
Remember the movie “Mission Impossible” where the protagonist, Tom Cruise bypassed a security system using body heat signatures left on the keyboard? Well,...
-

 270
270The Pirate Bay AGAIN Caught Mining Cryptocurrency Using Your CPU Power
Last year, when The Pirate Bay was first caught mining cryptocurrency without notifying the users, it created lost of havoc in the pirate...
-
 188
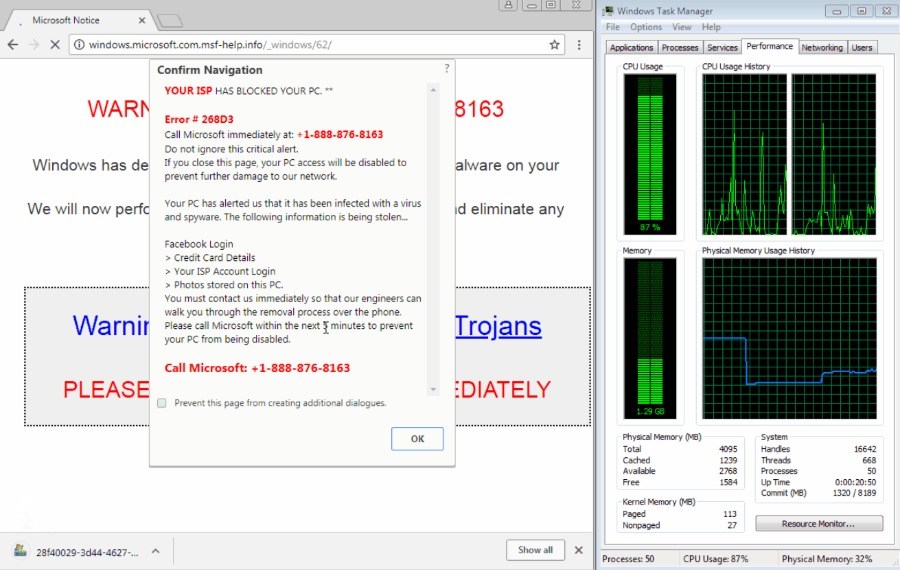
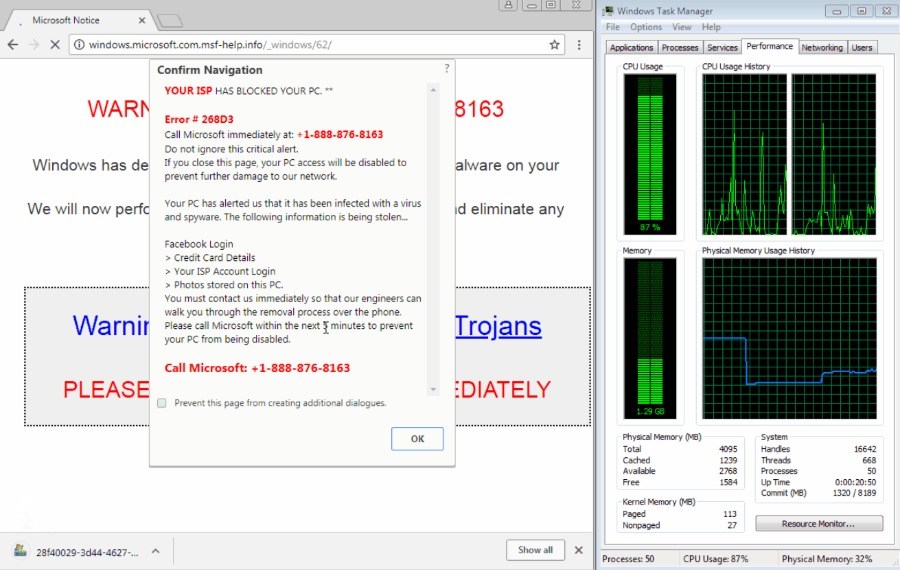
188Google Chrome’s “Download Bomb” Attack Is Back, Also Affects Firefox, Opera, Brave
Earlier this year, a bug in Google Chrome was a rejoice for tech support scammers who could freeze people’s browser using the...
-
 286
286Google Slammed For Giving Gmail Access To Third Party Developers (Humans)
There are many third-party apps that require access to your Gmail account. For instance, the ones that help you plan trips or...
-

 245
245NSA Deletes Hundreds Of Millions Of Call Records It Wasn’t ‘Authorized’ To Access
On May 23rd, The American intelligence agency NSA started the process of deleting the call records it has obtained from US telecom companies since 2015....
-
 181
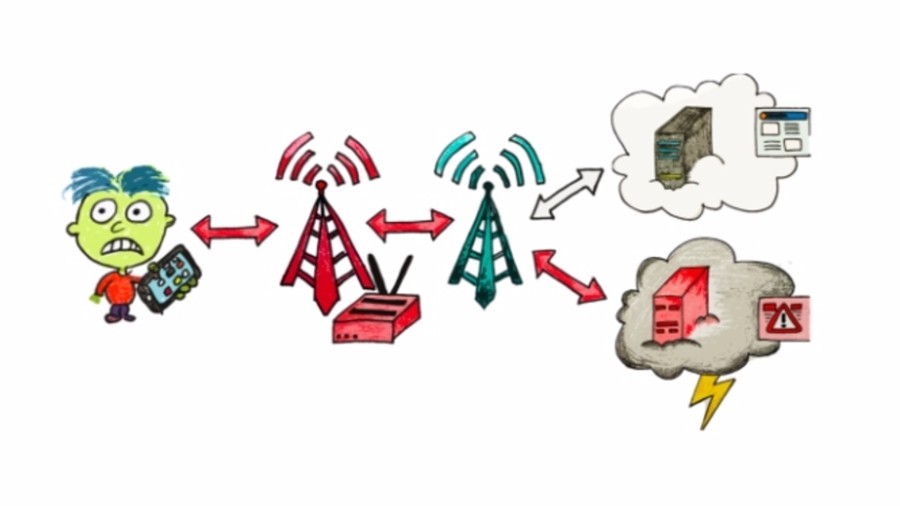
181LTE (4G) Flaw Allows Attackers To Redirect Browsers And Spy On You
The Long Term Evolution (LTE) standard for mobile communication, also known as 4G was designed to overcome security flaws of its predecessor standards...
-
 287
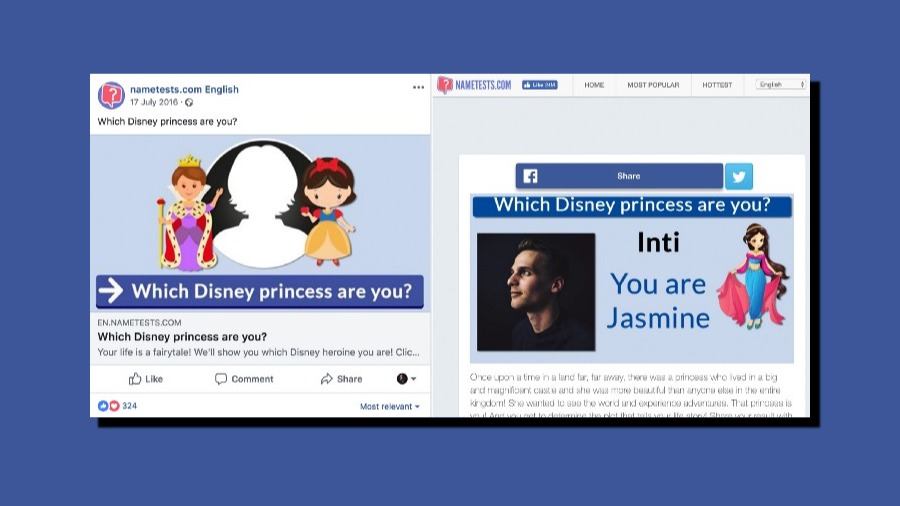
287“NameTests” Facebook Quiz Exposed Personal Data Of 120 Million Users For Years
When Facebook-Cambridge Analytica scandal started blazing up headlines, many Facebook critics and security experts called it just a beginning. That prophecy is...
-

 228
228Even Batteries Can Be Used To Steal Data From Your Smartphone
A new research has proved that the battery in your cell phone could be turned into a secret surveillance device which can potentially...
-

 214
21435+ Darknet Vendors Selling Illicit Goods “Busted” By US Authorities
In addition to making you anonymous, the Tor network also gives access to the world of Darknet where activities like selling of...
-
 267
267WPA3: Wi-Fi Receives Its Biggest Security Upgrade After 14 Years
Last year, when security researchers tore apart WPA2’s security with KRACK exploit, questions were raised regarding its ability to protect billions of WiFi-compatible...
-

 356
356NSA Spying Centers Hidden Inside AT&T Buildings In 8 US Cities
The Intercept, the publication known for its groundbreaking reports, has come up with another revealing piece (via TechCrunch) about the National Security Agency....
-

 369
369iPhone Brute Force Hack: Researcher Finds How To Bypass iPhone’s Passcode Limit
Over the past years, Apple has been playing cat and mouse with the security researchers and hackers who keep trying to develop...
-

 179
179Beware! Fake Fortnite APKs Having Malware Making Rounds on Internet
Fortnite is the talk of the town. The popularity of the video game has crossed all boundaries, and the game is attracting...
-

 249
2496-Year-Old Malware Injects Ads, Takes Screenshots On Windows 10
A sneaky and persistent malware has surfaced which spams Windows 10 PCs with ads and takes screenshots to eventually send it to...
-

 267
267MysteryBot Android Malware Combines Keylogger, Ransomware, And Banking Trojan
A new malware that targets banking apps has hit Android devices. Names MysteryBot, the malware packs a banking trojan, keylogger, and ransomware,...
-

 188
188Hackers May Have Already Defeated Apple’s USB Restricted Mode For iPhone
It seems that the cat and mouse chase between Apple and people who want to get access to iPhone is never going...
-

 250
250Cortana Flaw Lets Hackers Access Data, Reset Password On Locked Windows 10 PCs
Security researchers have found a critical flaw in Windows 10 where Cortana can be manipulated into executing Powershell commands on locked devices. Attackers can...
-

 221
221ADB Exploit Leaves Thousands Of Android Devices Exposed To Attackers
A network worm has surfaced on Android devices that exploits Android Debug Bridge (ADB) feature of the mobile OS – a feature that...






