Hackers Repository
-
 233
233Overview of Social Engineering
“In the context of information security, refers to psychological manipulation of people into performing actions or divulging confidential information.” A type of...
-
 259
259Reset Windows Password with Kali
Sometimes we forget our password, or even we want to reset the password of the windows OS of our friends, officemate or...
-

 371
371Google Dorks – Google Hacking
Google search engine find answer to our question which is helpful in our daily lives, search about our school assignments, reports, presentation and...
-

 315
315Windows 10 – Most Important Features you need to know
With Windows 10, Microsoft is making a strong step towards its goal of One Microsoft by looking forward to connect all the...
-
 167
167Building your own Web Crawler
Web crawler is a program that browses the Internet (World Wide Web) in a predetermined, configurable and automated manner and performs given...
-

 256
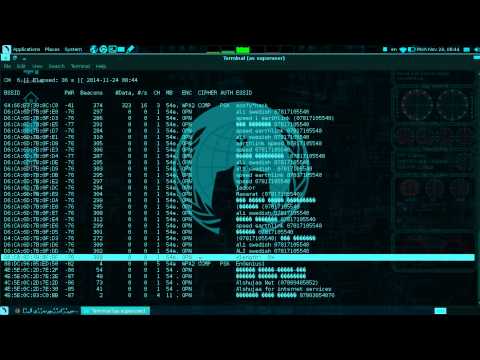
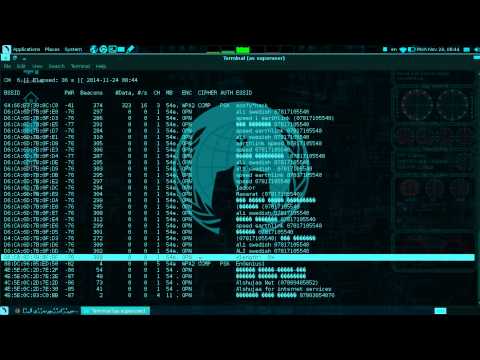
256Hacking WiFi – Selecting the best strategy
Not every hack will work under every circumstance, so choosing the right strategy is more likely to lead to success and less...
-

 254
254Ollydbg – Cracking software like a pro
If you’ve ever wondered how software pirates can take software and crack it time and time again, even with security in place,...
-

 233
233RunAsDate – Cracking Trial Software
It infuses the predefined date and time to the objective programming in this way preventing it from expiry. Demo variant programming basically...
-

 261
261Flooding a Facebook User
This guide will show you how to flood a persons facebook wall, comments, and messages. What is flooding? Basically spamming the same...
-
 328
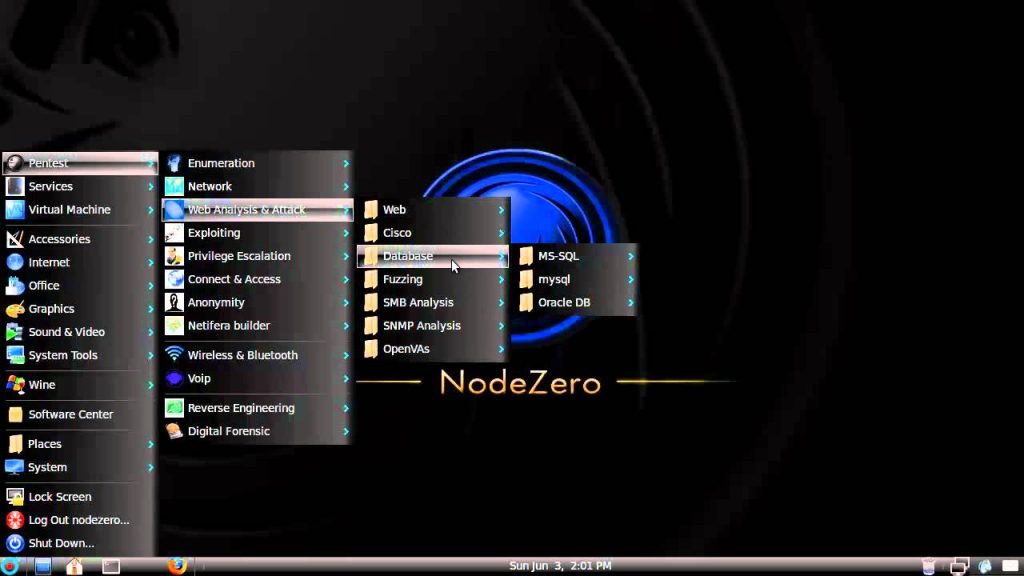
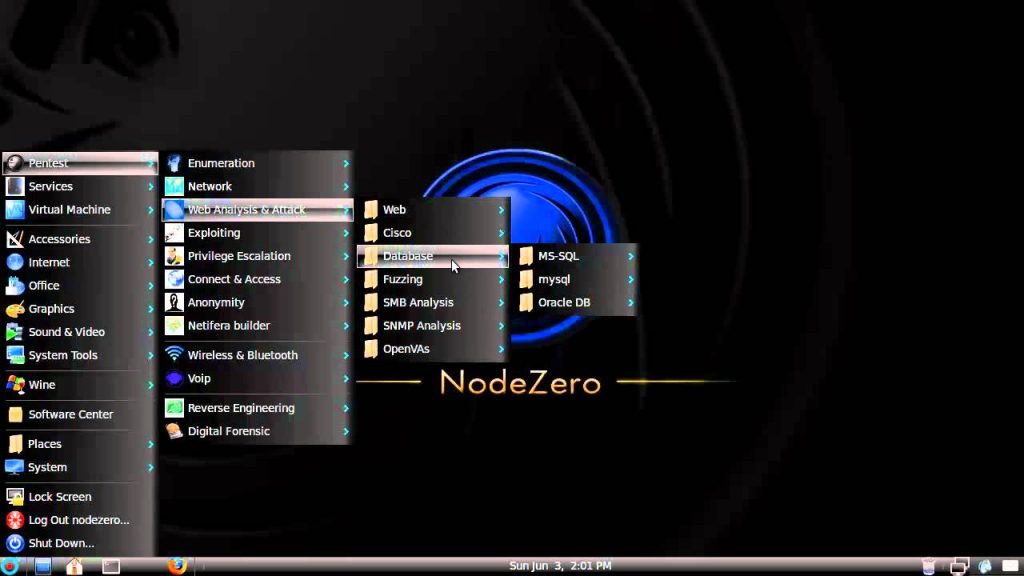
328NodeZero – Lurking in the shadows of Pentesting
Us penetration testers have of course all heard of BackTrack it’s the most popular penetration testing distro out there but Node Zero...
-

 219
219Hacknet , a real Hacking game.
Developed by Team Fractal Alligator, an Australian one-man studio, Hacknet is “an immersive, terminal-based hacking simulator for PC.” Here’s the official...
-
 472
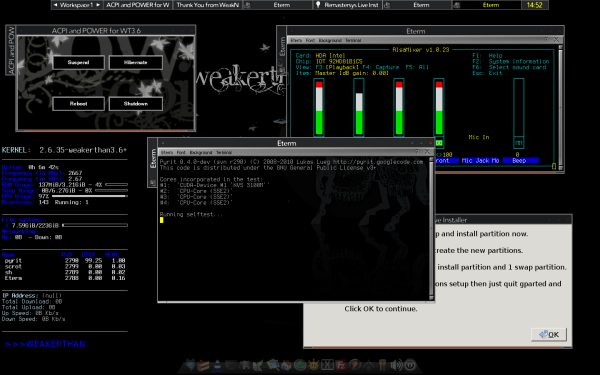
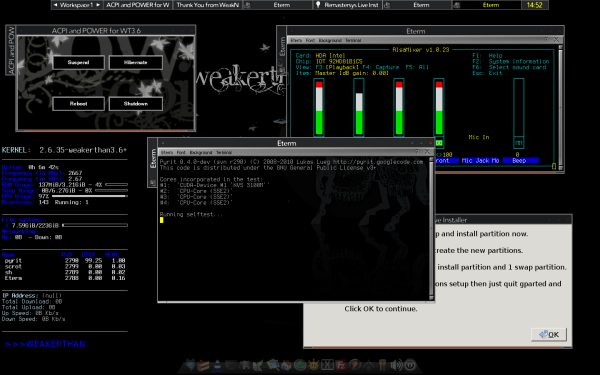
472WEAKERTH4N – Another Hacking OS
Most of the hackers would have heard about Backtrack. Weakerthan is another Linux based pentesting distro which is really good.. I think Weakerthan is second...
-
Removing a PDF password
Now a days, we all save our data in a Word file or a PDF file. Some have basic information and some...
-

 229
229A Guide to become an Ethical Hacker
A person who hacks into a computer network in order to test or evaluate its security, rather than with malicious or criminal...
-

 206
206Download Torrents with IDM
There may be many reasons to download torrent files using IDM. It may be that you get good speed using IDM, no...
-
 231
231Review of Parrot OS
Parrot Security OS is a security oriented operating system designed for Pentesting, Computer Forensic, Reverse engineering, Hacking, Cloud pentesting, privacy/anonymity and cryptography....
-
 128
128Hacker Series – Enough to motivate you?
With the amount of hackers expanding in the modern world, so does TV shows start to react. Time to get your ‘mode’...
-
 203
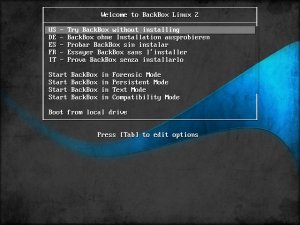
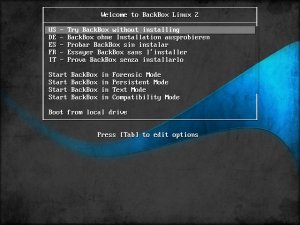
203Backbox – Turning heads in the pentesting scene
A relative newcomer to the forensic and penetration testing live CD scene, Italian project BackBox is already turning heads as it hits...
-

 216
216Turning your Android into a hacking device
Now days, smartphones and tablets are the most popular gadgets. The reason behind this is that people utilize tablets for most of...
-

 304
304Review of Kali Linux – The Successor of backtrack
Kali Linux is a penetration testing and security auditing Linux distribution. After its release in March 2013, Kali Linux has quickly become...
-
Linux…. Where did it come from?
Linux was originally developed as a free operating system for personal computers based on the Intel x86 architecture, but has since been...






