Hackers Repository
-

 292
292Pentest Box – Hacking on a Windows platform
Pentest Box is a portable penetration testing distribution for Windows environments,it provides all security tools as a software package, eliminating requirement of...
-
 147
147Get 2000 Backlinks for Free
If you own a website then you would know how important backlinks are. So we have a nice tool that gives you...
-

 152
152Anonymous Opened Virtual School to Teach Hacking
The hacktivist group Anonymous have launched a virtual school in a dark web hidden service that allows you to share your experiences...
-

 223
223How to Hack ISP for free Internet [Bypass login page]
This trick works only on networks which uses a username and password to connect. This is known as PPPoE, this will not work...
-

 221
221The Hacker that Hacked Facebook shows us how
“As a pentester, I love server-side vulnerabilities more than client-side ones. Why? Because it’s way much cooler to take over the server...
-

 425
425The Vigilante Hacker that hacked Hacking Team
The hacker who hacked the Hacking Team explains how he did it and includes tips to avoid being busted The hacker responsible...
-

 162
162How to Bypass URL shortener links
Sometimes we need to download very important data from the Internet but those links are attached with adfly and other ads network...
-

 378
378Extension Spoofer
A filename extension is very important in the Windows operating system and it appears at the end of the file name. Not...
-

 337
337Hacking Wifi within 10 Minutes
Any non-technical person who knows how to operate the computer can hack/crack WiFi within or less than 10 minutes. PS. Screenshots are...
-

 84
84Addmefast BOT – 2016
AddMeFast is a network that will help you grow your social presence by exchanging likes for Facebook / Youtube / Twitter etc....
-
 160
160MorphVOX PRO Cracked – Anonymous voice changer
If you want to make sure that your true identity remains a secret even if you want to talk over the Internet,...
-
 207
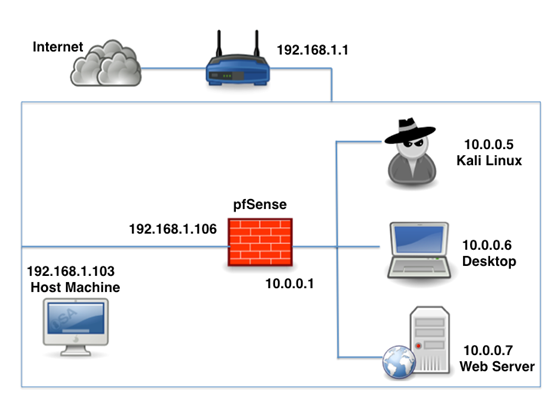
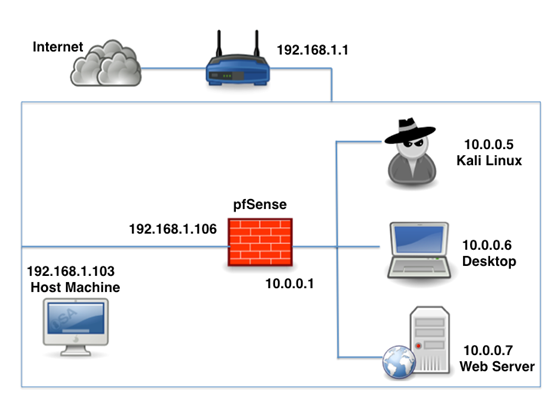
207Building your own Pentest Lab
Following is the network we are going to setup in this article. Host machine = (192.168.1.103) which is connected to a wireless...
-
 239
239120 Hacking Books to Download
Hackers education is very important. Most hackers attend college or reached that level by self-taught. There’s a saying: ” Hacking Is Not...
-
 200
20011 Tips to protect yourself against Ransomware
Ransomware can be very scary – the encrypted files can essentially be considered damaged beyond repair. But if you have properly prepared...
-

 450
450Faceniff – Hacking Facebook from your Android Device
Faceniff is probably the most easiest way to gain access to someone’s Facebook account and also works for twitter, YouTube, amazon, and...
-

 322
322How to send a spoofed SMS
SMS Spoofing occurs when a sender manipulates address information. Often it is done in order to impersonate a user that has roamed...
-

 299
299Anatomy of a Crypto-Ransomware attack
Ransomware is a type of malware that forces its victims to pay the ransom through certain online payment methods in order to...
-

 3.5K
3.5KHacking Facebook using Kali-Linux
Here we will discuss how to hack Facebook, as well as to develop understanding of how fake web pages are created, so...
-
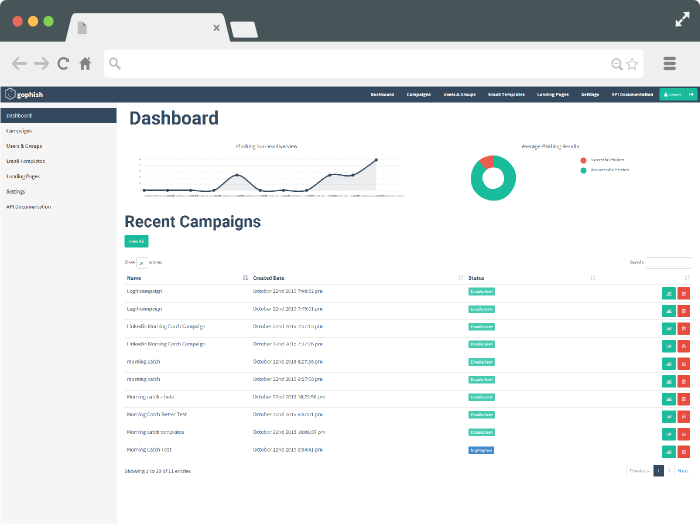
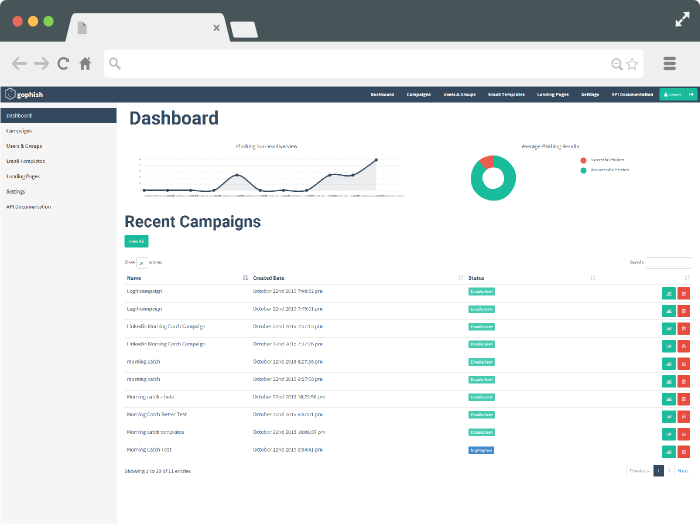 168
168Gophish – Open Source Phishing Toolkit
Gophish is an open-source Phishing tool designed for penetration testers. It is user-friendly and easy to setup and execute phishing engagements and...
-
 182
182Creating your own Run Commands
The Run command on Microsoft Windows Operating System allows you to directly open an application or document with just a single command...
-
 196
196Windows 8.1 – Alienware OS released
Alienware OS released. The first version in this series, the Alpha, will run Windows 8.1. The operating system and ability to play...






