Hackers Repository
-
 231
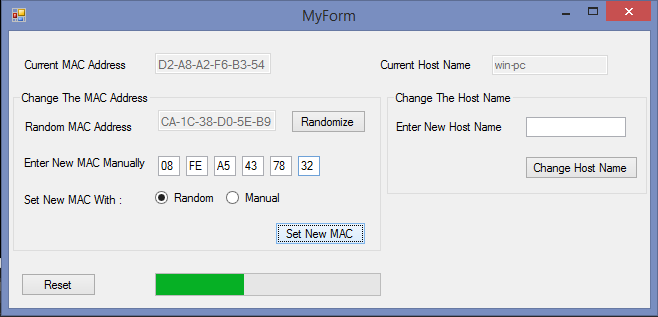
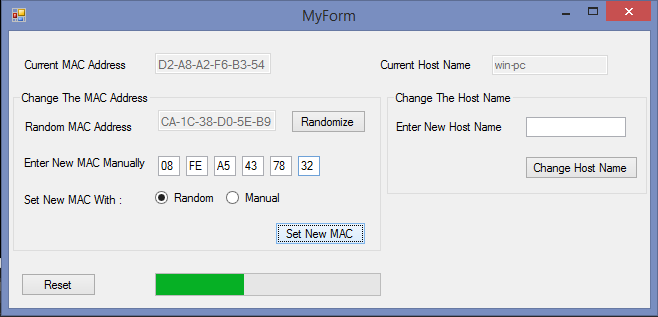
231WinMACSpoofer – Windows Tool For Spoofing The Mac Address and Hostname
Windows application for spoofing the MAC address and host name. Usage The program must be run in “administrator mode” for the functions...
-

 234
234Gone-Phishing – Mac keychain and password stealer
A phishing app that is written in applescript. It is small and works on macs, whose users often don’t worry about malware on...
-
 169
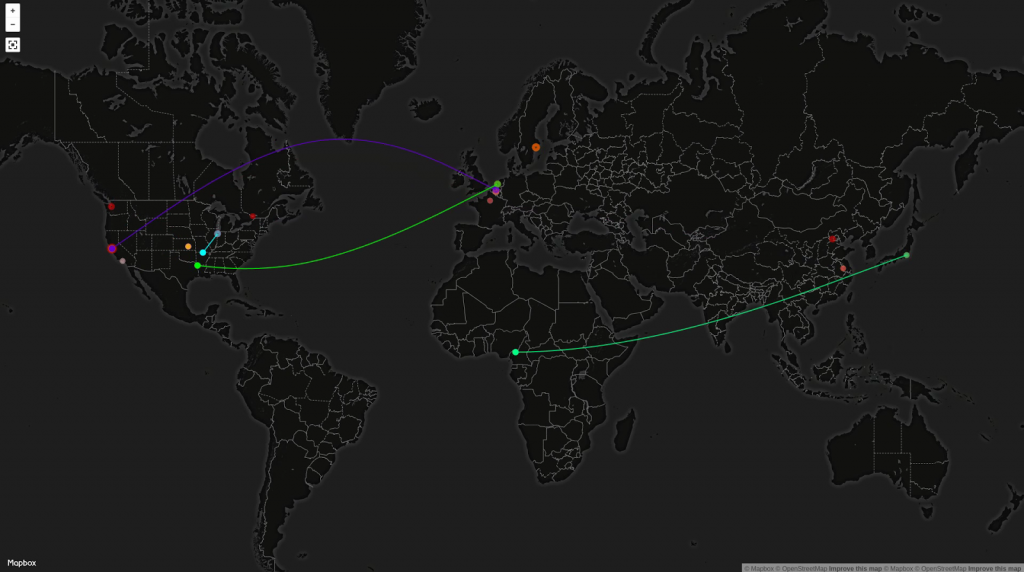
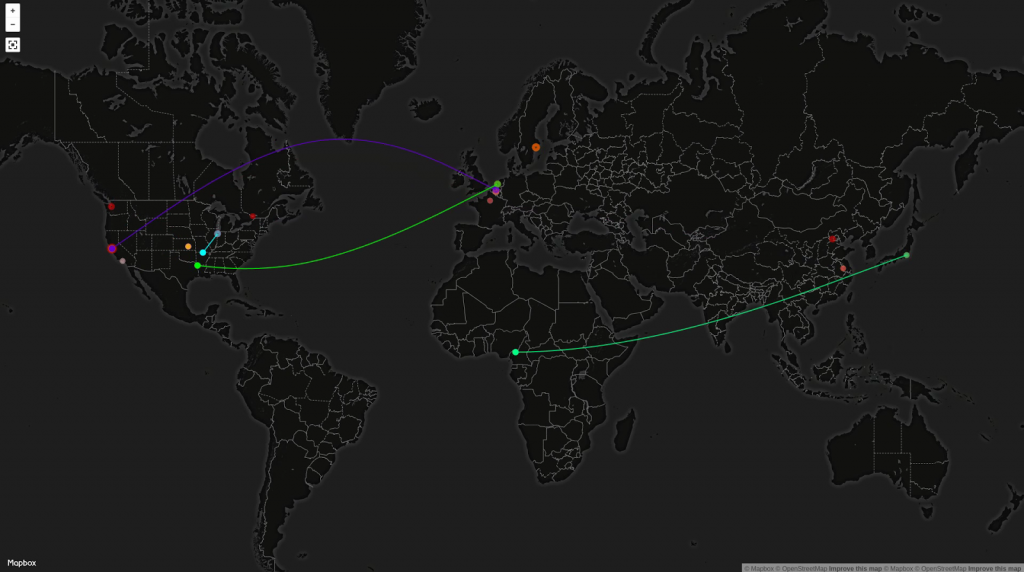
169Geoip-attack-map – Cyber Security GeoIP Attack Map Visualization
This geoip attack map visualizer was developed to display network attacks on your organization in real time. The data server follows...
-
 2.0K
2.0K100 working deep web, onion and dark web links
The Dark Web, Deep Web or Darknet is a term that refers specifically to a collection of websites that are publicly visible,...
-

 114
114Radium Keylogger – Python keylogger with multiple features
Keylogging is the malicious action of spying on the keyboard input of a target user. This is done in secret by malware...
-
 145
145Configure Network Share via Samba CLI
Here we will learn how to create a network share via Samba using the command line interface in a easy, simple detailed...
-

 237
237Hack any Mobile APP – Reverse engineering and Analysis Framework.
MARA is a Mobile Application Reverse engineering and Analysis Framework. It is a tool that puts together commonly used mobile application reverse...
-
 219
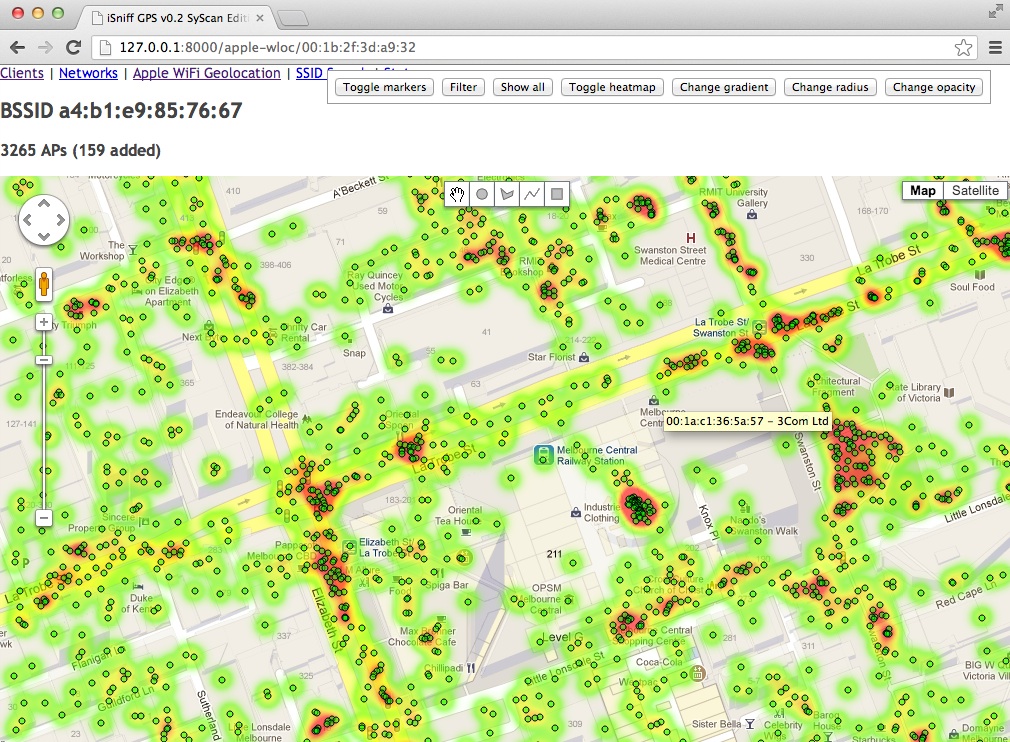
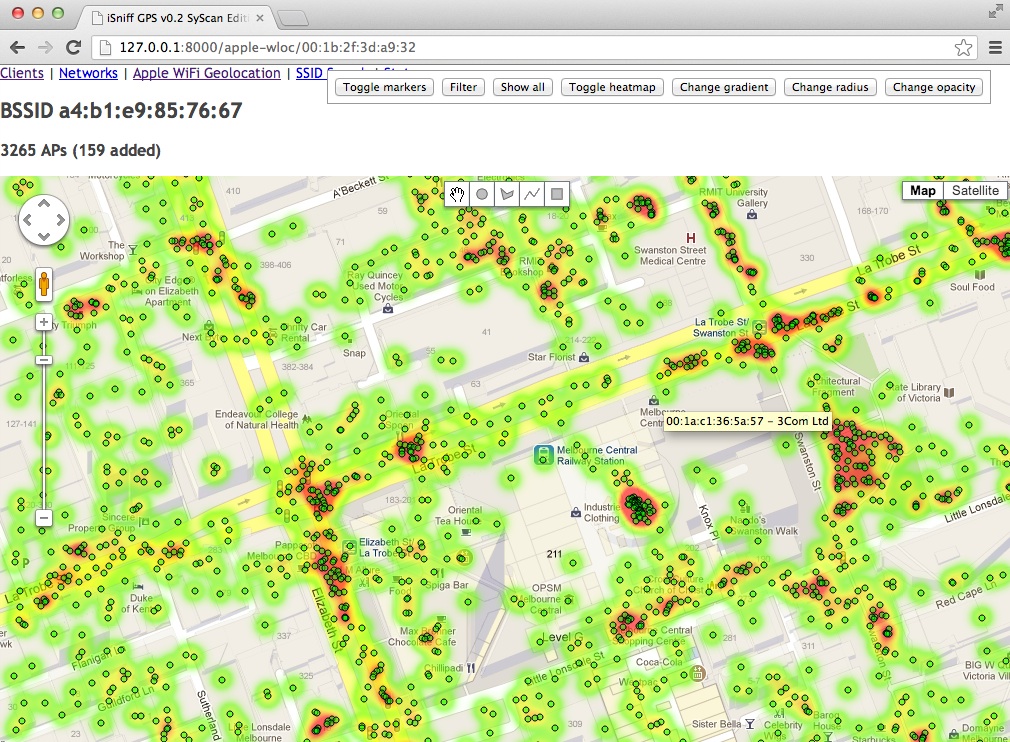
219iSniff GPS – Determine where a device and its owner have been
iSniff GPS passively sniffs for SSID probes, ARPs and MDNS (Bonjour) packets broadcast by nearby iPhones, iPads and other wireless devices. The...
-
 248
248ir-rescue – A Windows Batch Script To Comprehensively Collect Host Forensic Data
ir-rescue is a lightweight Windows Batch script that collects a myriad of forensic data from 32-bit and 64-bit Windows systems while respecting...
-
 220
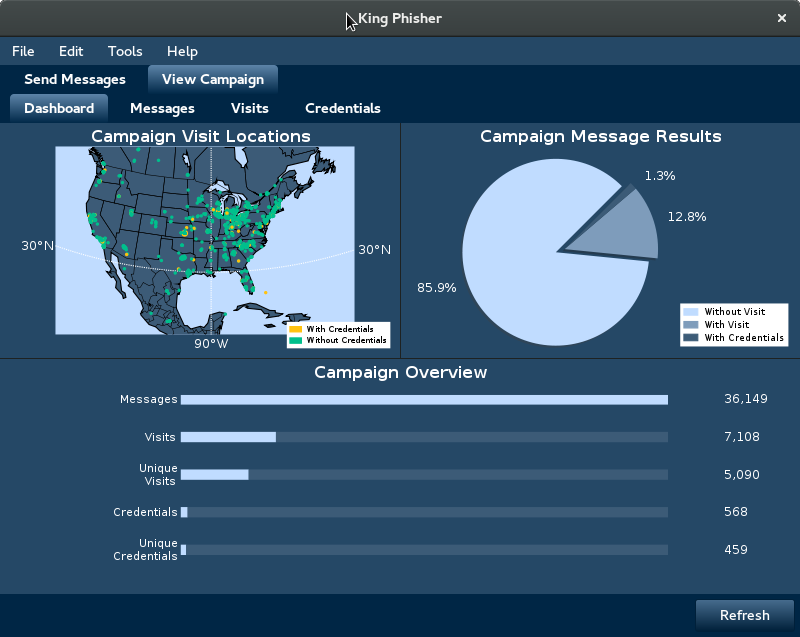
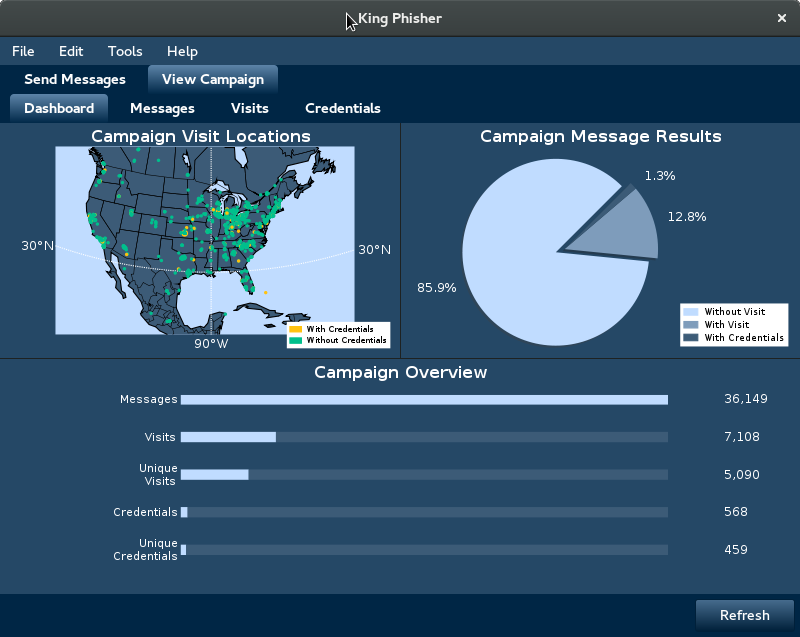
220King Phisher 1.5.2 – Phishing Campaign Toolkit
King Phisher is a tool for testing and promoting user awareness by simulating real world phishing attacks. It features an easy to...
-

 147
147DracOS – Lightweight and Powerful Penetration Testing OS
Dracos Linux ( www.dracos-linux.org ) is the Linux operating system from Indonesian , open source is built based on the Linux...
-
 276
276Malicious Outlook Rules
Anyone familiar enough with Outlook will know it has a “Rules and Alerts” section that allows the user to automate certain actions based on message...
-

 190
190Droid Hunter – Android Application Vulnerability Analysis And Android Pentest Tool
.---. .----------- / __ / ------ / / ( )/ ----- ╔╦╗╦═╗╔═╗╦╔╦╗ ╦ ╦╦ ╦╔╗╔╔╦╗╔═╗╦═╗ ////// ' / ` --- ║║╠╦╝║ ║║...
-

 170
170CodinGame: Get Better At Programming While Playing Games
CodinGame: The new way to improve your programming skills while having fun and getting noticed. Here players can test their new ideas...
-
 235
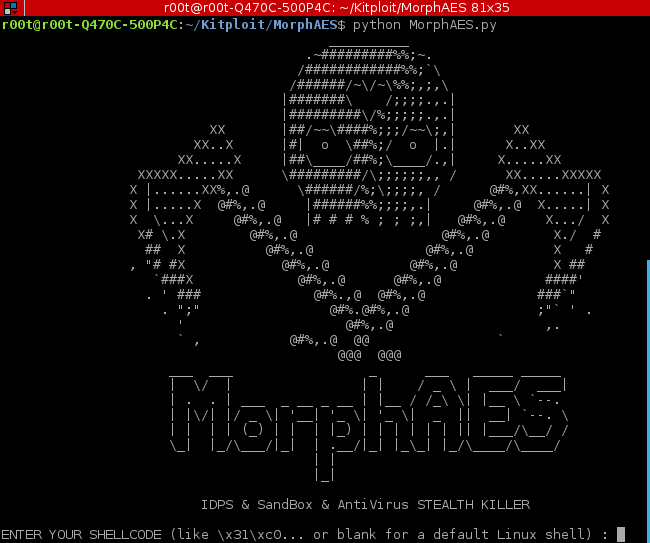
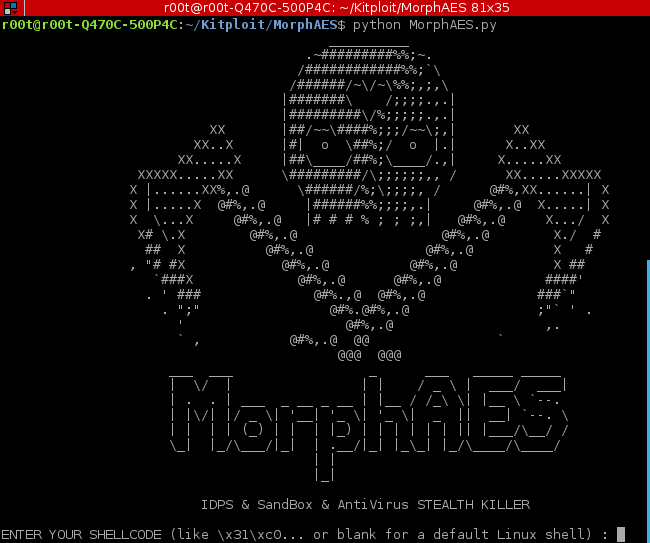
235MorphAES – IDPS, SandBox & AntiVirus STEALTH KILLER
MorphAES is the world’s first polymorphic shellcode/malware engine, with metamorphic properties and capability to bypass sandboxes, which makes it undetectable for an...
-
 100
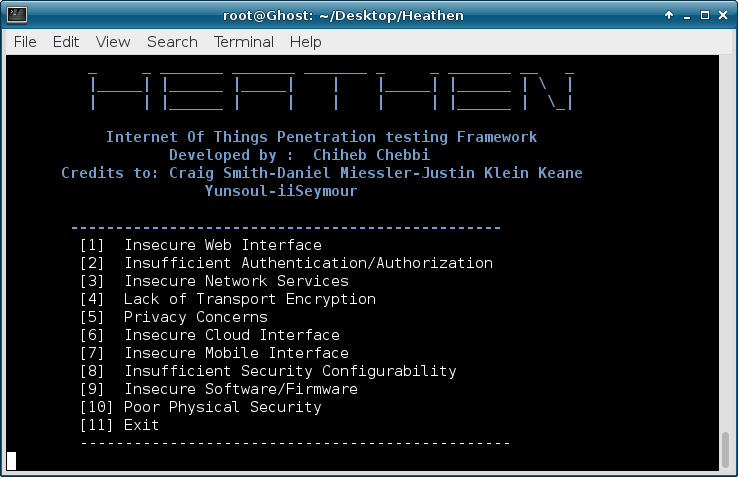
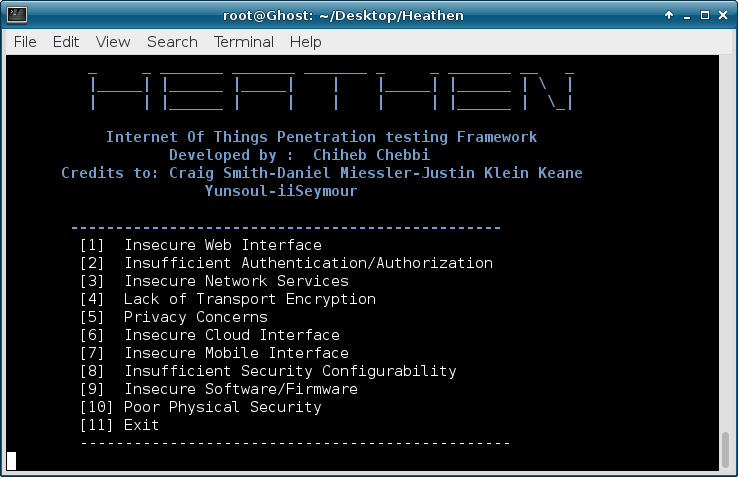
100Heathen – IoT Pentesting Framework
Heathen Internet of Things Penetration Testing Framework developed as a research project, which automatically help developers and manufacturers build more secure products in...
-
 246
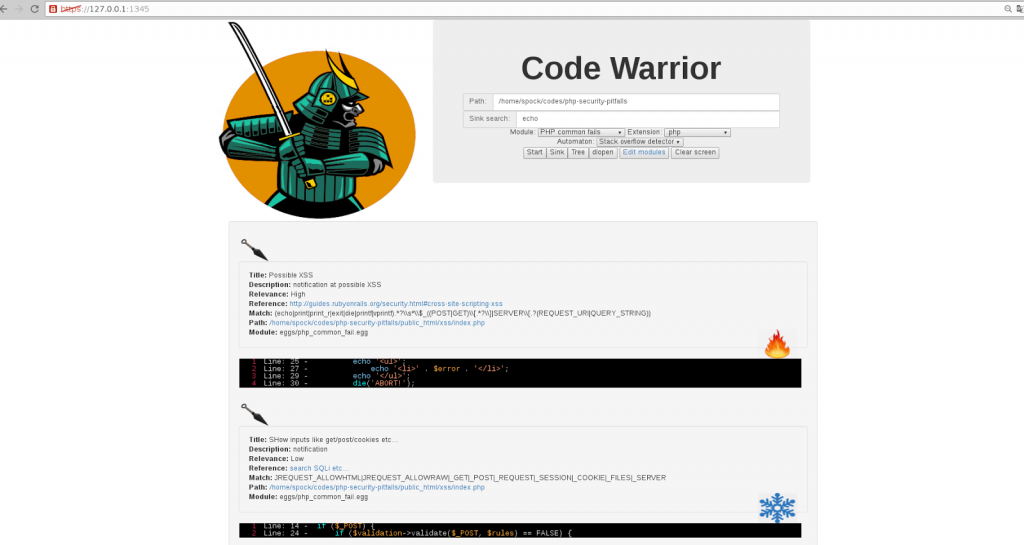
246CodeWarrior – Code Analysis Tool And Static Analysis Tool
Just another manual code analysis tool and static analysis tool Codewarrior runs at HTTPd with TLS, uses KISS principle( https://en.wikipedia.org/wiki/KISS_principle ) Directories:...
-
 282
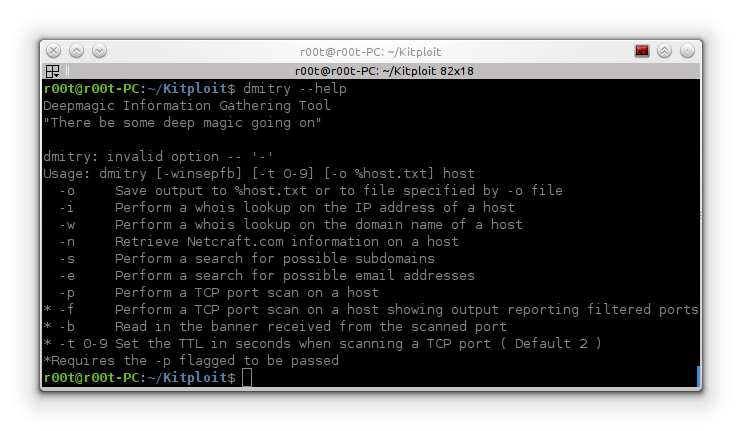
282DMitry – Deepmagic Information Gathering Tool
DMitry (Deepmagic Information Gathering Tool) is a UNIX/(GNU)Linux Command Line Application coded in C language. DMitry has the ability to gather as...
-
 317
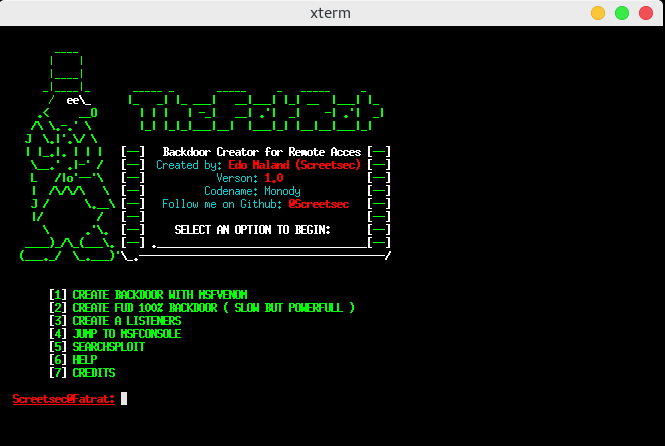
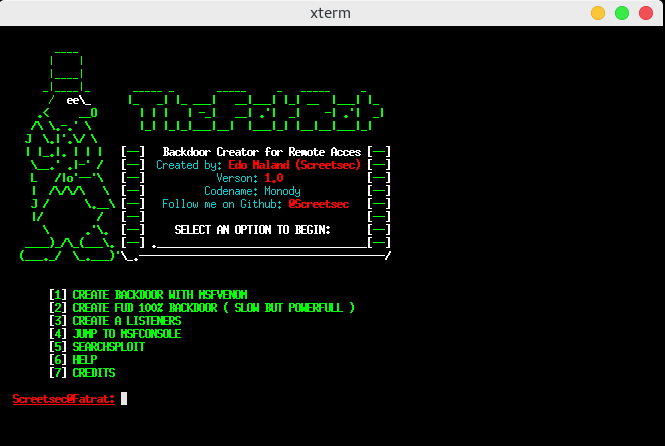
317TheFatRat – Easy Tool to Generate Backdoor
Easy tool for generate backdoor with msfvenom ( part of metasploit framework ) and program compiles a C program with a meterpreter...
-
 195
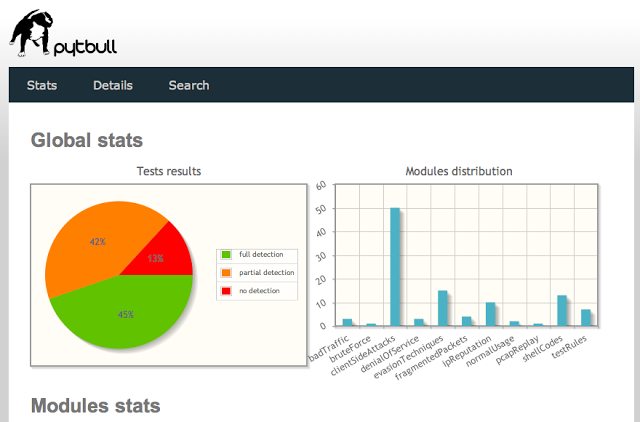
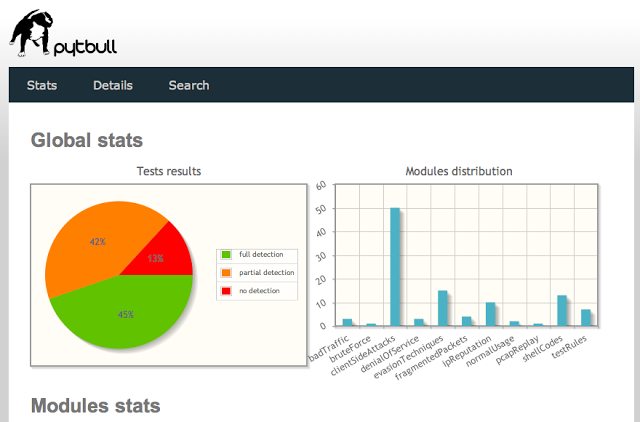
195pytbull – Intrusion Detection/Prevention System (IDS/IPS) Testing Framework
pytbull is an Intrusion Detection/Prevention System (IDS/IPS) Testing Framework for Snort, Suricata and any IDS/IPS that generates an alert file. It can...
-

 310
310SimpleEmailSpoofer – A simple Python CLI to Spoof Emails
A few Python programs designed to help penetration testers with email spoofing.SimpleEmailSpoofer.py A program that spoofs emails. Currently in development spoofcheck.py A...






