Hackers Repository
-
WebRTC can leak your IP address even if your behind a VPN
WebRTC (Web Real-Time Communication) is a collection of communications protocols and application programming interfaces that enable real-time communication over peer-to-peer connections....
-
brut3k1t – Server Side Bruteforce Module
Brute-force (dictionary attack, jk) attack that supports multiple protocols and services http://ex0dus-0x.github.io Introduction brut3k1t is a server-side bruteforce module that supports dictionary...
-
Wifi-Dumper – Tool that Dumps Wifi Profiles in Cleartext
This is an open source tool to dump the wifi profiles and cleartext passwords of the connected access points on the Windows...
-
mitmproxy – An Interactive TLS-Capable HTTP Proxy
Man in the middle Proxy is An interactive TLS-capable intercepting HTTP proxy for penetration testers and software developers http://mitmproxy.org. Documentation & Help:...
-
OWASP Passfault – Evaluates Passwords and Enforces Password Policy
OWASP Passfault evaluates passwords and enforces password policy in a completely different way. https://passfault-hrd.appspot.com Running the Command-line Interface: install java 8 jdk...
-
iptodomain
iptodomain This tool was created by Juan Esteban Valencia Pantoja it extracts domains information from IP address based in the information saved in...
-
 263
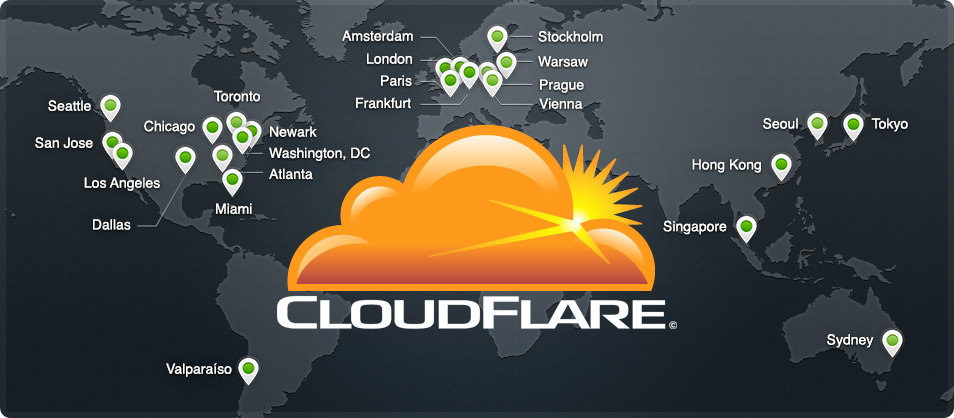
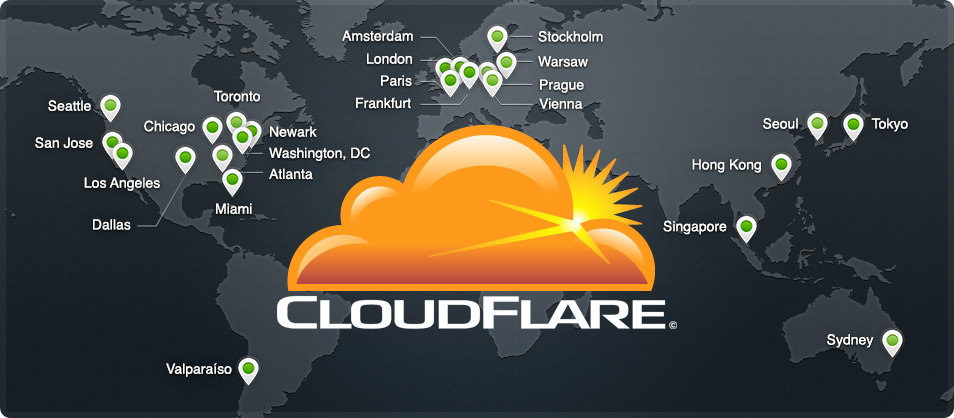
263HatCloud – Bypass Cloudflare to Discover IP
HatCloud, built with Ruby. A simple tool to bypass CloudFlare to discover the real IP. This can be useful if you need...
-
 146
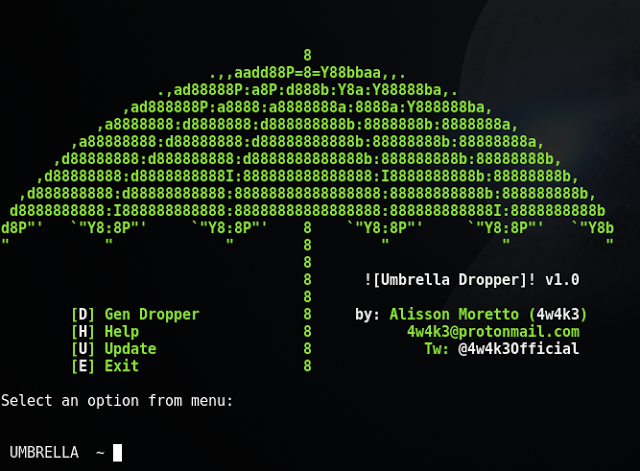
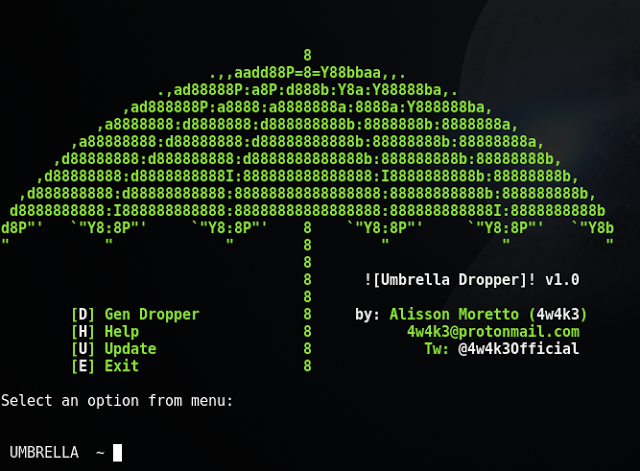
146Umbrella – A Phishing Dropper designed for Pentest
Umbrella is a file dropper dedicated to pentesting, it downloads a file on target system and then executes without the need of...
-
Insanity-Framework a Tool To Generate Payloads and Control Remote Machines
Insanity-Framework to Generate Payloads and Control Remote Machines. Insanity-Framework ** VERSION 1.6 RELEASED !!! ** * Copyright 2017 Insanity Framework (IF) Written...
-
Fluxion – Easy to use wifi cracker, to test your own network
Fluxion is a easy to use wifi cracker, to test your own network. Fluxion is the future of MITM WPA attacks Fluxion...
-
Pupy – Open Source Cross Platform Python Remote Access Tool
Puppy Pupy is an opensource, cross-platform (Windows, Linux, OSX, Android), multi function RAT (Remote Administration Tool) and post-exploitation tool mainly written in...
-
WPS-SLAUGHTER
WPS-SLAUGHTER is a tool that helps to automate the process of testing router WPS vulnerability to flood attacks using multiple* wireless adapters to...
-
Unicorn – PowerShell Downgrade Attack Evade Anti-Virus
Unicorn is a simple tool for using a PowerShell downgrade attack and inject shellcode straight into memory. Based on Matthew Graeber’s powershell...
-
Useful Msfvenom and Metasploit Commands
Useful Msfvenom and Metasploit Commands The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in...
-
 262
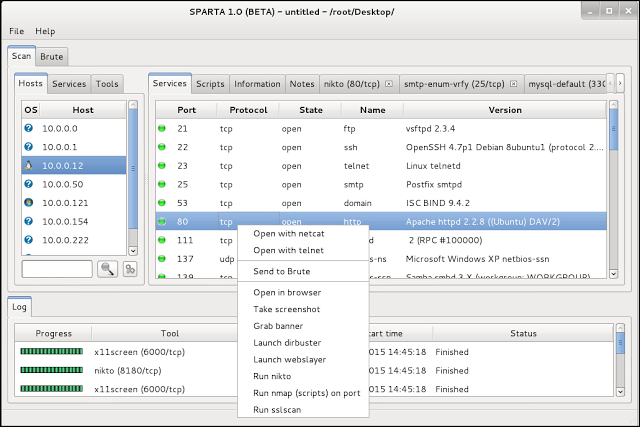
262SPARTA – Network Infrastructure Penetration Testing Tool
SPARTA is a python GUI application which simplifies network infrastructure penetration testing by aiding the penetration tester in the scanning and enumeration...
-
Kali Linux Man in the Middle Attack Arpspoofing/Arppoisoning
Welcome back today we will talk about Man-in-the-middle attacks. In computer security, a man-in-the-middle attack (often abbreviated mitm, or the same using all...
-
Slowloris Layer 7 DDOS Attack
Slow Loris is Layer 7 Application (Protocol Attack) it was developed by Robert “RSnake” Hansen don’t be fooled by its power even...
-
Dr0p1t-Framework – Dropper that bypass most AVs
Dr0p1t-Framework Dr0p1t-Framework A framework that creates a dropper that bypass most AVs, some sandboxes and have some tricks ? Credits: D4Vinci –...
-
Facebrok – Social Engineering Tool Oriented to facebook
ABOUT Download Facebrok Credits: PowerScript facebrok is a social tool for exploiting social network accounts facebook, this platform brings together various Templates...
-
wifijammer
wifijammer Continuously jam all wifi clients and access points within range. The effectiveness of this script is constrained by your wireless card....
-
PytheM – Multi-purpose pentest framework
PytheM – Penetration Testing Framework v0.6.6 Credits: m4n3dw0lf Download PytheM PytheM is a python multi-purpose pentest framework. It has been developed in...






