Hackers Repository
-
PytheM – Multi-purpose pentest framework
PytheM – Penetration Testing Framework v0.6.6 Credits: m4n3dw0lf Download PytheM PytheM is a python multi-purpose pentest framework. It has been developed in...
-
TheFatRat Tutorial – Generate Undetectable Payload FUD, Bypass Anti-Virus, Gain Remote Access
In this tutorial I will show you how to use TheFatRat to generate a Undetectable payload (FUD) to gain remote access to...
-
Snoopy Tutorial – Finding Previously Connected SSID’S of a Device
Wireless Networks can leak a treasure trove of information. In this tutorial we will use Snoopy to find various Wireless Access Points...
-
Smith – Client/Server Style Agent For Testing Network Connectivity
smith Credits: jidir (Leave him a star on Github) Download Smith A client/server style agent meant for testing connectivity to and from...
-
Davscan – A Tool That Fingerprints servers, finds exploits, scans WebDAV
DAVScan Credits: Graph-X Download Davscan DAVScan is a quick and lightweight webdav scanner designed to discover hidden files and folders on DAV...
-
Java Deserialization Scanner
All-in-one plugin for Burp Suite for the detection and the exploitation of Java deserialization vulnerabilities Download Java-Deserialization-Scanner Credits: federicodotta Java Deserialization Scanner...
-
Cracking WPA/WPA2 WPA Key Wireless Access Point Passphrase
In this article we will learn how to brute force a WPS key using Airodump-ng, Reaver with Pixie Dust addon if your running...
-
Portspoof
Portspoof Effective defense against port scanners Short description: Art of Annoyance The Portspoof program primary goal is to enhance OS security through...
-
Change or Spoof Network Interface Mac Address Using Macchanger
Macchanger is a tool that is used for manipulating the mac address of a wireless or wired network interface. Today I...
-
Social Engineering Credential Harvester Method Phishing in SET
Social Engineering relies heavily on human interaction and deception, trickery you get the picture it is a specialist way of extracting data...
-
Embedding a Metasploit Payload to an original Android Apk.
Embed a Metasploit Payload in an original Android Apk. Welcome back in the last part of the Android Hacking Series we discussed...
-
 114
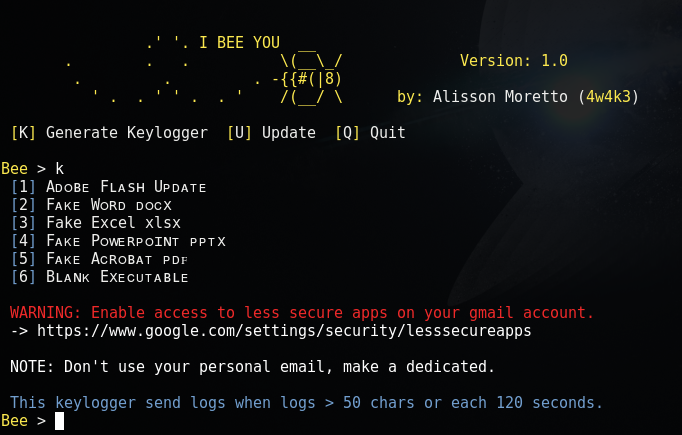
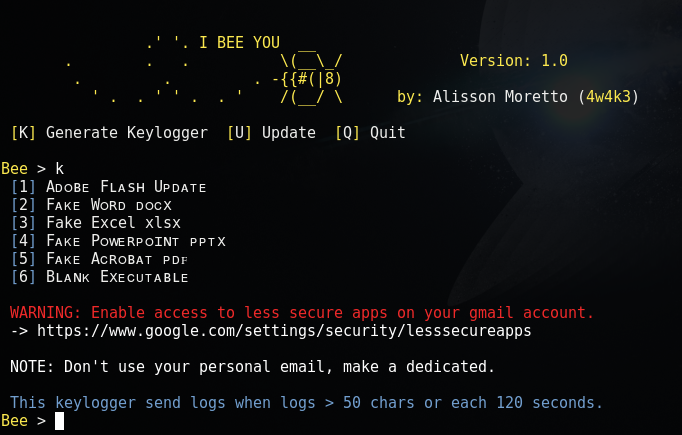
114BeeLogger – Generate Email Keyloggers
Beelogger allows you to generate a keylogger in a document format which can be executed via emails Features Send logs each 120...
-
 215
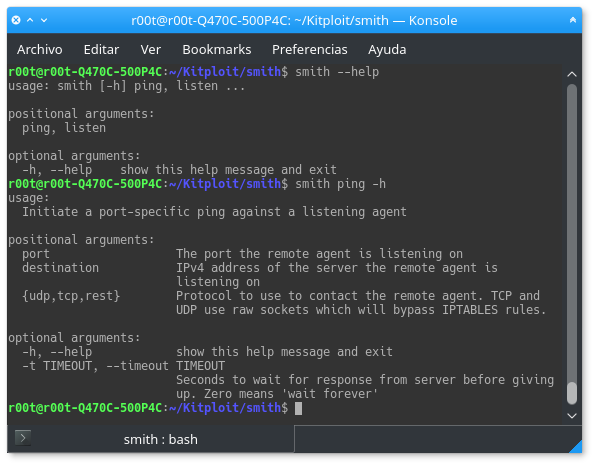
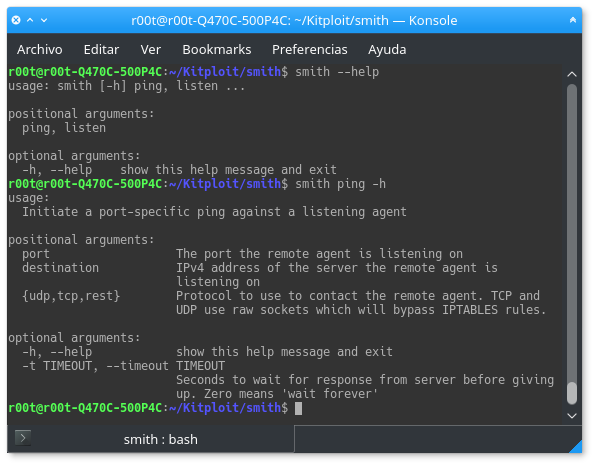
215Smith – A Very Quick And Dirty Server Tool For Testing Firewalls
A client/server style agent meant for testing connectivity to and from a machine on a network. Installation python setup.py install or pip...
-
 244
244FSEC – A Website Dedicated to Hacking Books
A website launched recently called FSEC or Futursec aiming to be a library for Hackers and computer enthusiasts. You will be greeted...
-

 285
285TCHunt-ng v1.2 – Reveal encrypted files
TCHunt-ng attempts to reveal encrypted files stored on a filesystem. The program is successful in finding TrueCrypt, VeraCrypt, CipherShed containers, EncFS encrypted...
-

 197
197Tater – A PowerShell implementation of the Hot Potato Windows Privilege Escalation Exploit
Tater is a PowerShell implementation of the Hot Potato Windows Privilege Escalation exploit. Included In p0wnedShell – https://github.com/Cn33liz/p0wnedShell PowerShell Empire – https://github.com/PowerShellEmpire/Empire...
-

 217
217Windows SMB zero-day exploit goes live on Github after Microsoft fails to fix
AN EXPLOIT taking advantage of a Windows Server zero-day security vulnerability has been released into the wild after Microsoft failed to issue...
-
 233
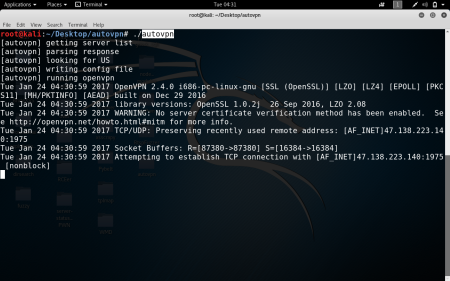
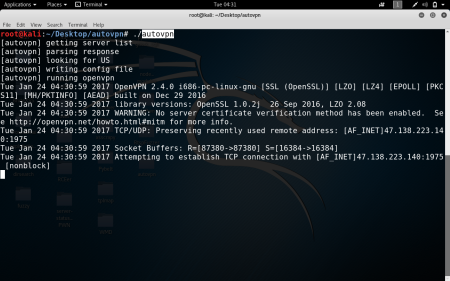
233Autovpn – Easily connect to a VPN in a country of your choice
autovpn is a tool to automatically connect you to a random VPN in a country of your choice. It uses openvpn to...
-
 134
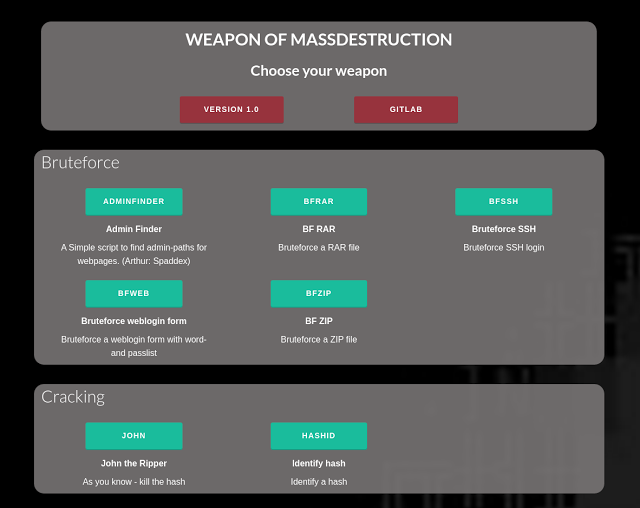
134WMD (Weapon of Mass Destruction) – Python framework for IT security tools
This is a python tool with a collection of IT security software. The software is incapsulated in “modules”. The modules does consist...
-
 209
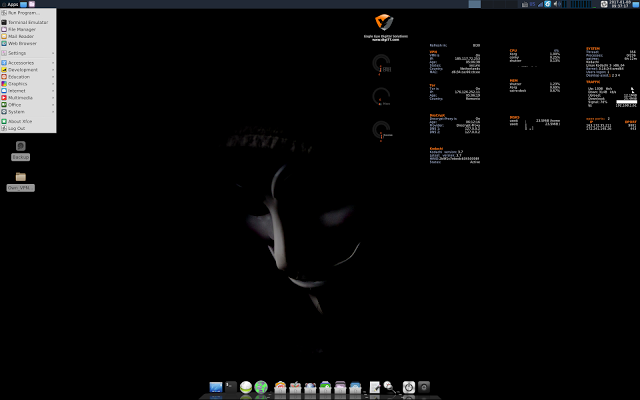
209Linux Kodachi3 – Secure Open Source Linux Distribution
Linux Kodachi operating system is based on Debian 8.6 it will provide you with a secure, anti forensic, and anonymous operating system...
-

 87
87Insanity Framework – Generate Payloads and Control Remote Machines
With the dynamics of persuasion that prove effective in a pentest, several painstaking means of making a payload has emerged, Insanity Framework...






