Hackers Repository
-
 212
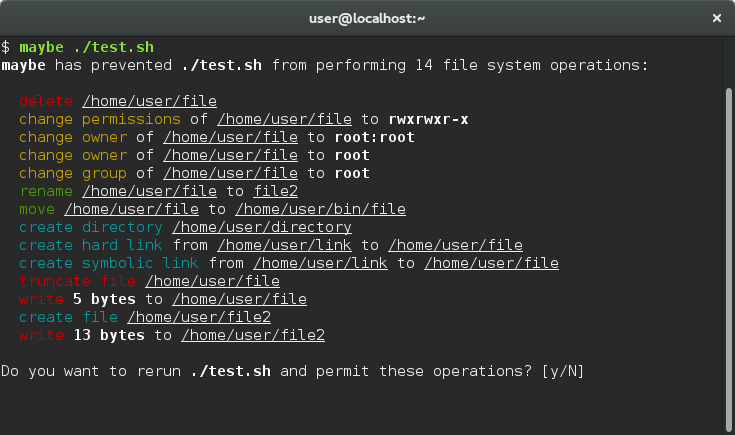
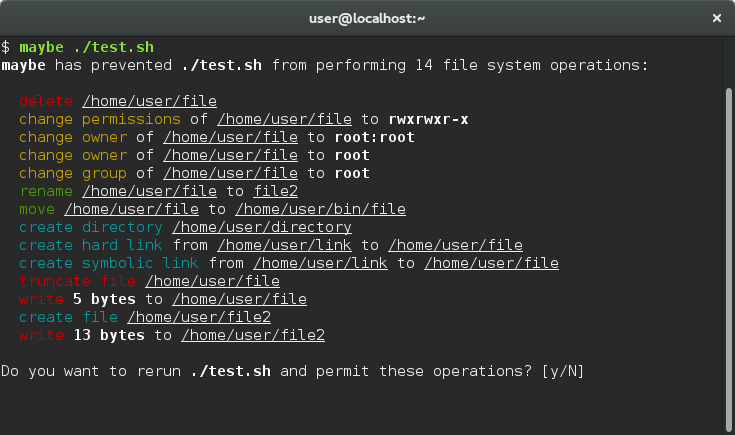
212Maybe – See What A Program Does Before Installing
rm -rf pic* Are you sure? Are you one hundred percent sure? … allows you to run a command and...
-
 176
176QRLJacking – New Social Engineering Attack Vector
QRLJacking or Quick Response Code Login Jacking is a simple-but-nasty attack vector affecting all the applications that relays on “Login with QR...
-

 232
232Burp Suite Professional 1.7.14 – The Leading Toolkit for Web Application Security Testing
Burp Suite is an integrated platform for performing security testing of web applications. Its various tools work seamlessly together to support the...
-
 199
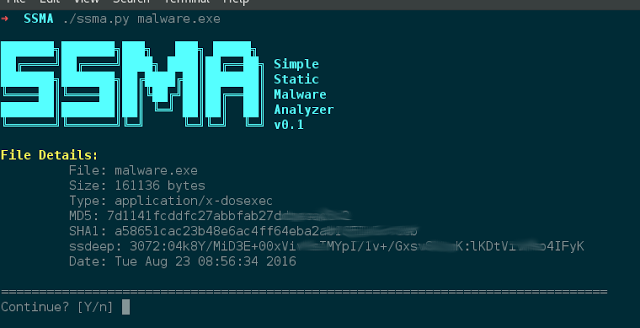
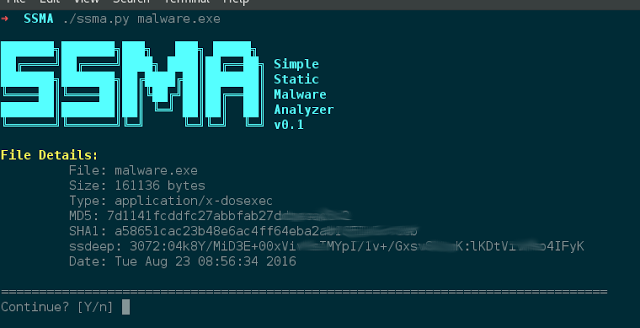
199SSMA – Simple Static Malware Analyzer
SSMA is a simple malware analyzer written in Python 3. Features: Searches for websites, e-mail addresses, IP addresses in the strings of...
-
 220
220BackdoorMan – Toolkit That Helps You Find Malicious, Hidden And Suspicious PHP Scripts And Shells
A Python open source toolkit that helps you find malicious, hidden and suspicious PHP scripts and shells in a chosen destination, it...
-

 167
167InsecureBankv2 – Vulnerable Android Application
Information security awareness training may include several demo that describe how attacker may exploit vulnerabilities on system to gain full control on...
-

 95
95Hacking Android Device – New Method 2016
Creating a malicious application is becoming easier by using some tools. Users of this shell script should have working knowledge of Linux,...
-

 124
124Serpico – SimplE RePort wrIting and COllaboration tool
Serpico is a penetration testing report generation and collaboration tool. It was developed to cut down on the amount of time it...
-
 148
148Metasploitable3 – An Intentionally Vulnerable Machine for Exploit Testing
Metasploitable3 is a VM that is built from the ground up with a large amount of security vulnerabilities. It is intended to...
-
 260
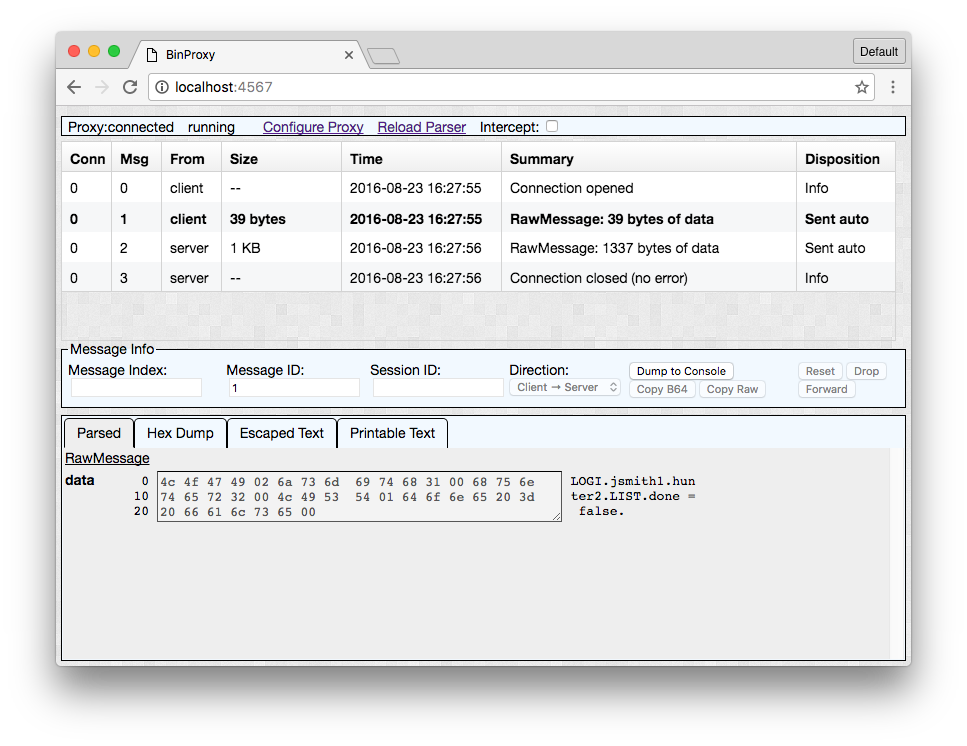
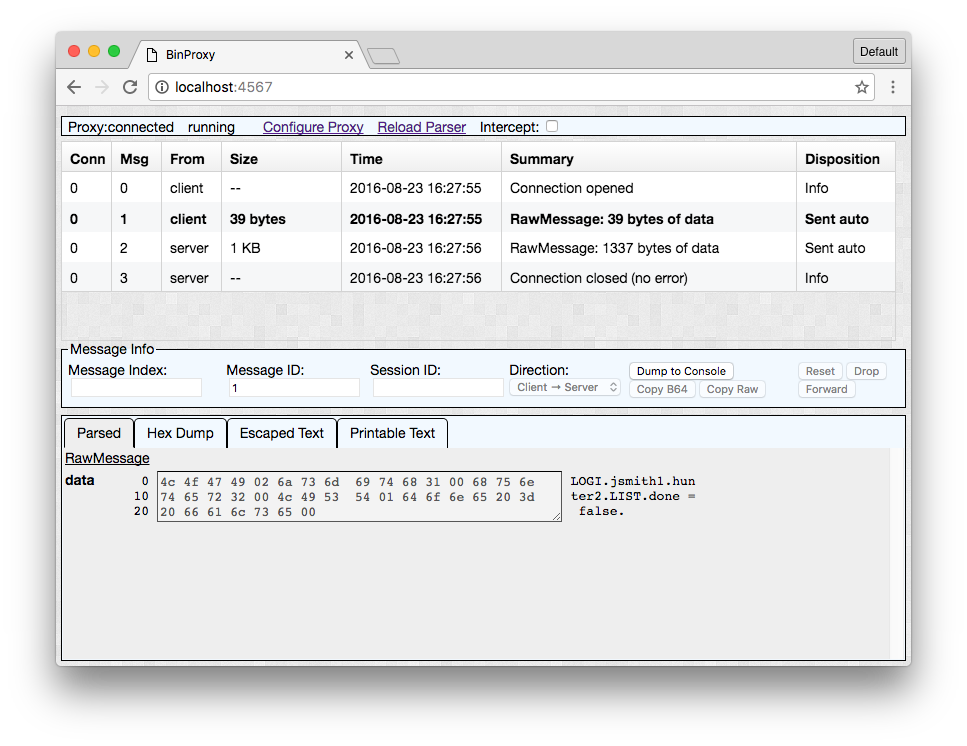
260BinProxy – a Tool for understanding and manipulating binary network traffic
One of the tools NCC Group released at this year’s Black Hat Arsenal is BinProxy, a tool for understanding and manipulating binary network...
-
 255
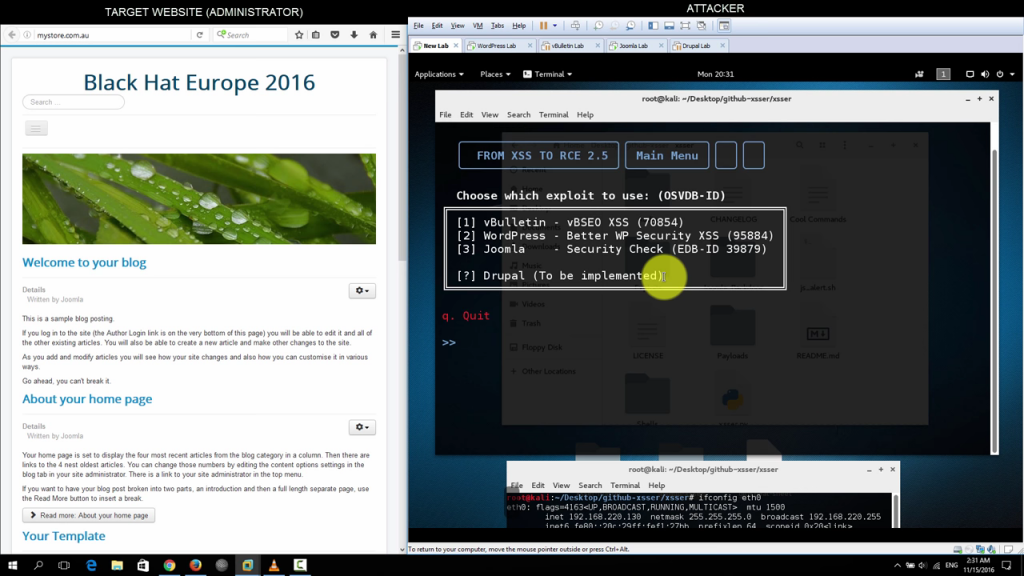
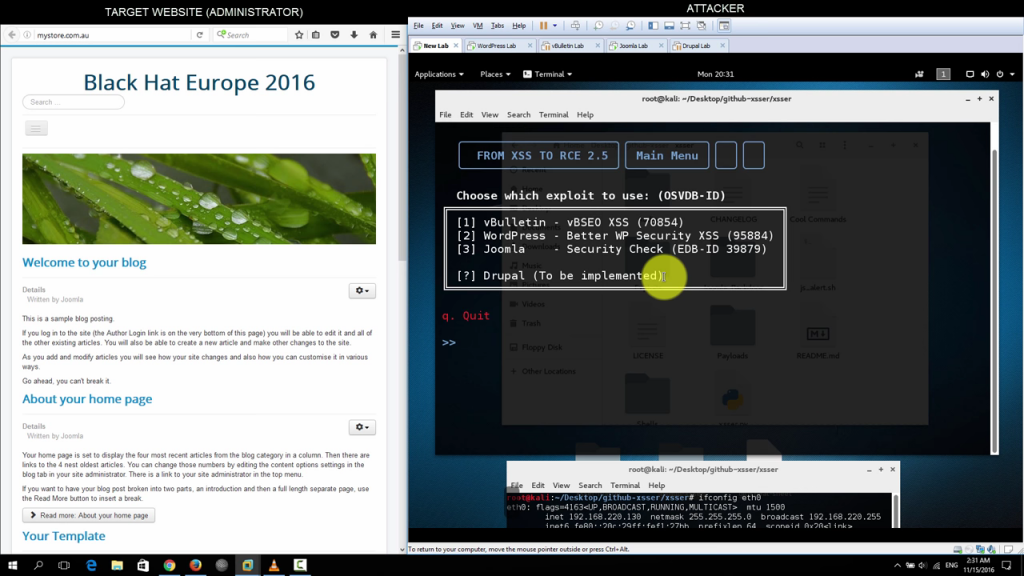
255XSSER – From XSS to RCE
This presentation demonstrates how an attacker can utilise XSS to execute arbitrary code on the web server when an administrative user inadvertently...
-
 241
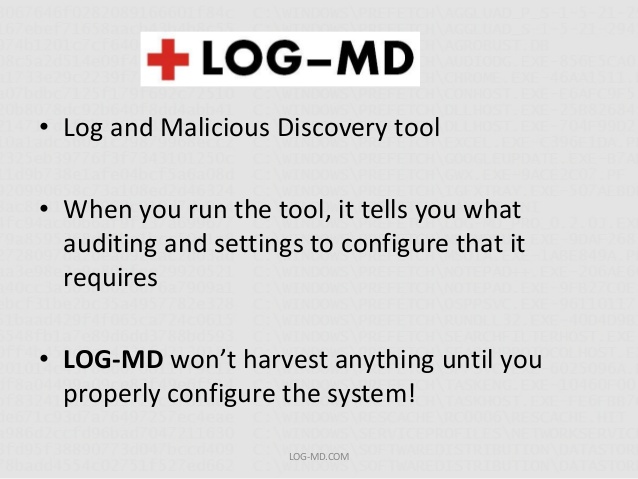
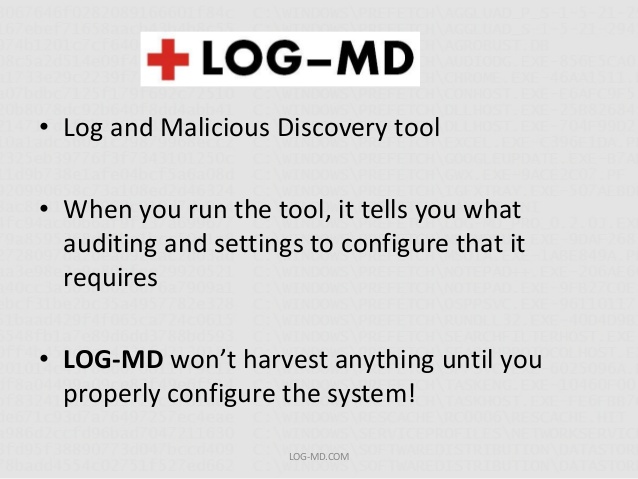
241LOG-MD – Log Malicious Detection tool
LOG-MD was designed for Windows based systems to audit log and advanced audit policy settings and guide users to enable and configure...
-
 225
225APT2 – Automated Penetration Testing Toolkit
This tool will perform an NMap scan, or import the results of a scan from Nexpose, Nessus, or NMap. The processesd results...
-
 192
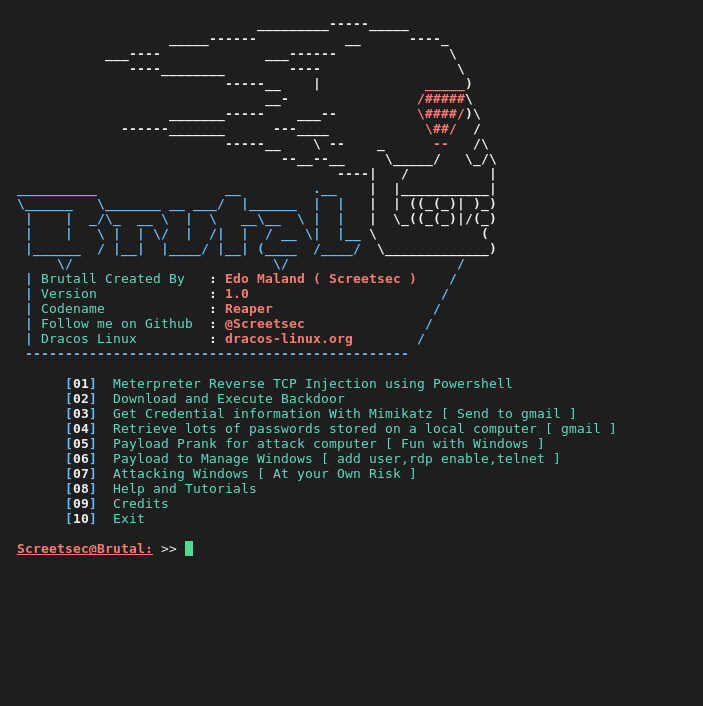
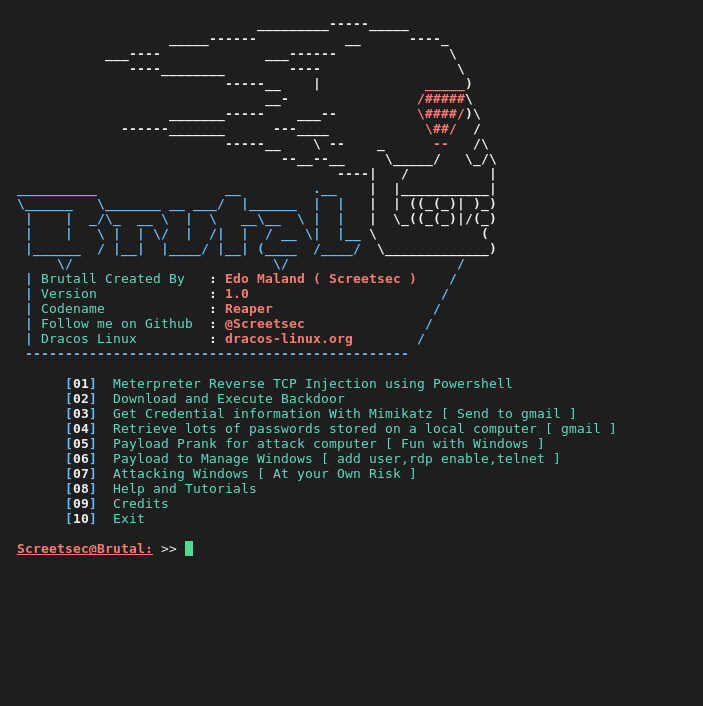
192Brutal – Toolkit to quickly create various payloads,powershell and virus attacks
Brutal is extremely useful for executing scripts on a target machine without the need for human-to-keyboard interaction ( HID -ATTACK )...
-
 188
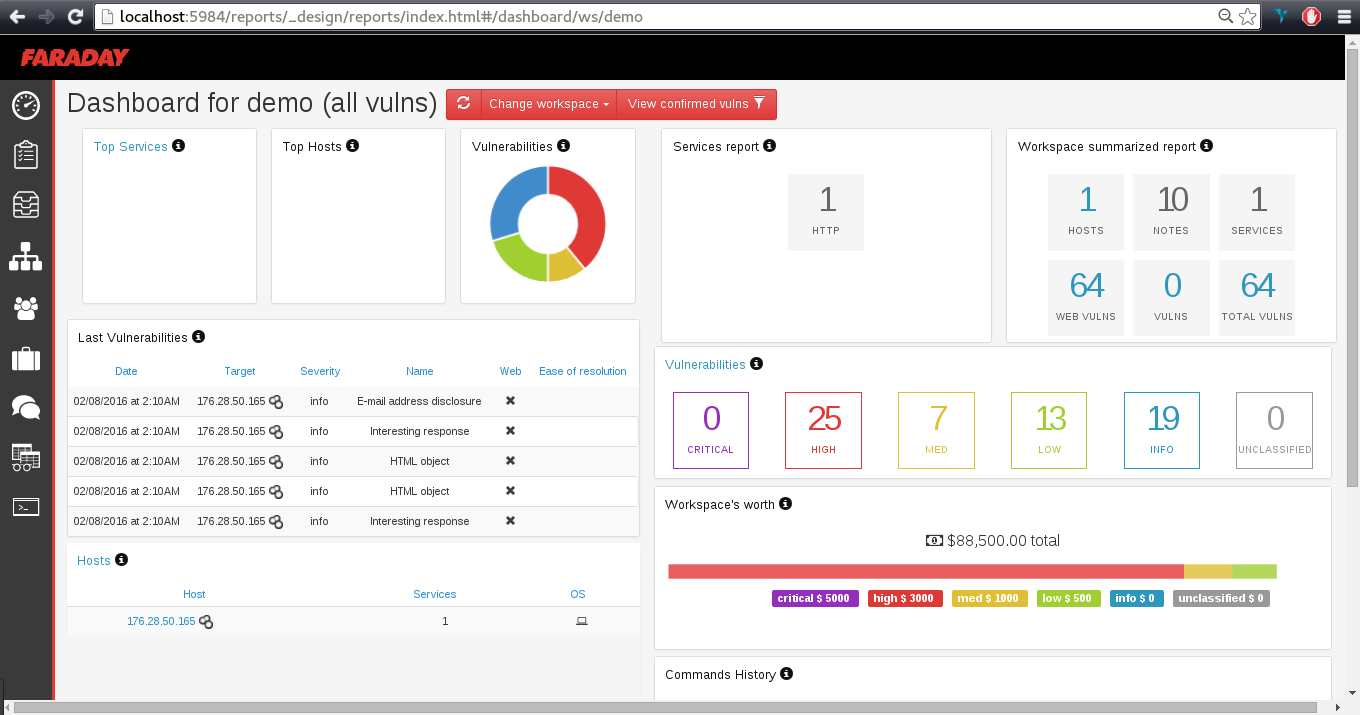
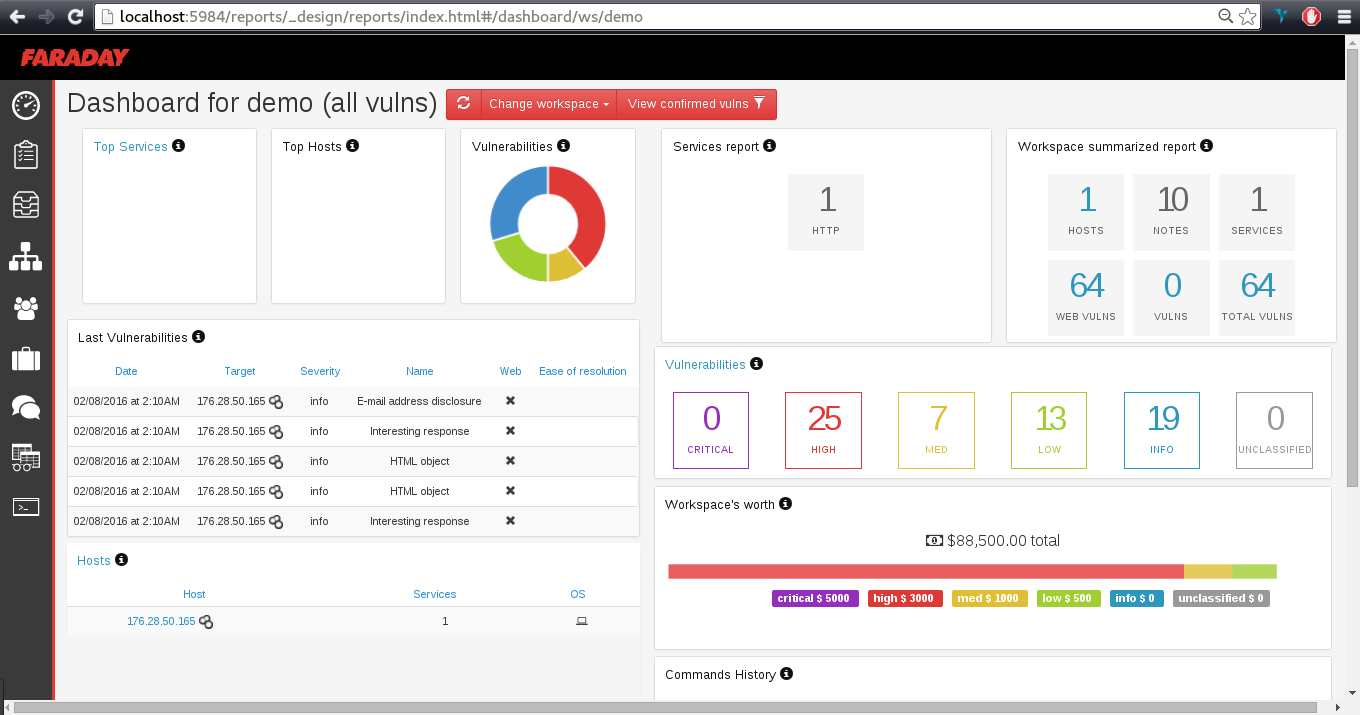
188Faraday – Penetration Test and Vulnerability Management Platform
Faraday introduces a new concept – IPE (Integrated Penetration-Test Environment) a multiuser Penetration test IDE. Designed for distribution, indexation and analysis of...
-

 116
116Creak – ARP Poison Attack Script
Deny navigation and download capabilities of a target host in the local network performing an ARP poison attack and sending reset TCP...
-

 261
261Anonymous Offline Communications System: PirateBox
PirateBox creates offline wireless networks designed for anonymous file sharing, chatting, message boarding, and media streaming. You can think of it as...
-
 303
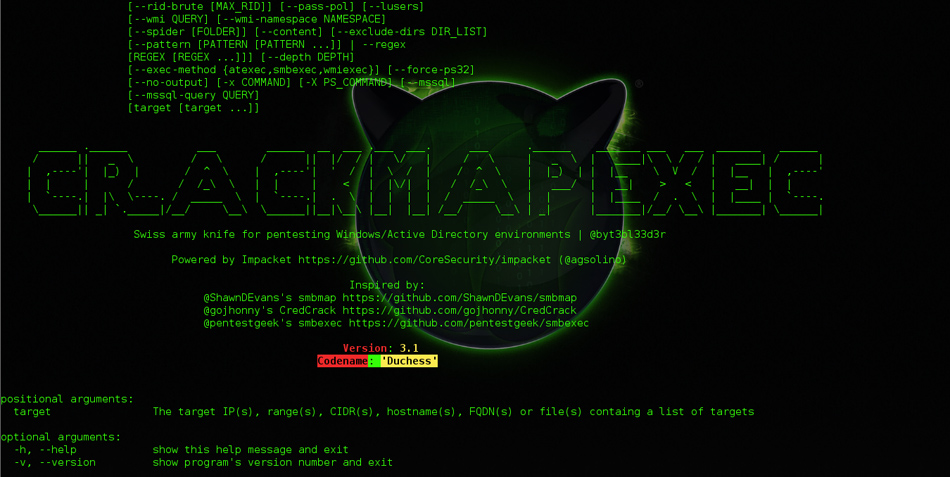
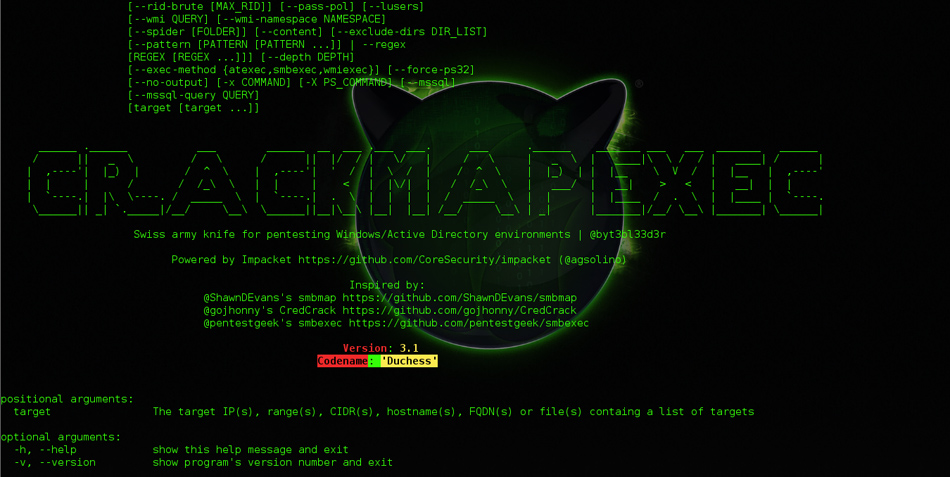
303CrackMapExec – Swiss army knife for pentesting Windows/Active Directory
CrackMapExec is your one-stop-shop for pentesting Windows/Active Directory environments! From enumerating logged on users and spidering SMB shares to executing psexec style...
-
 315
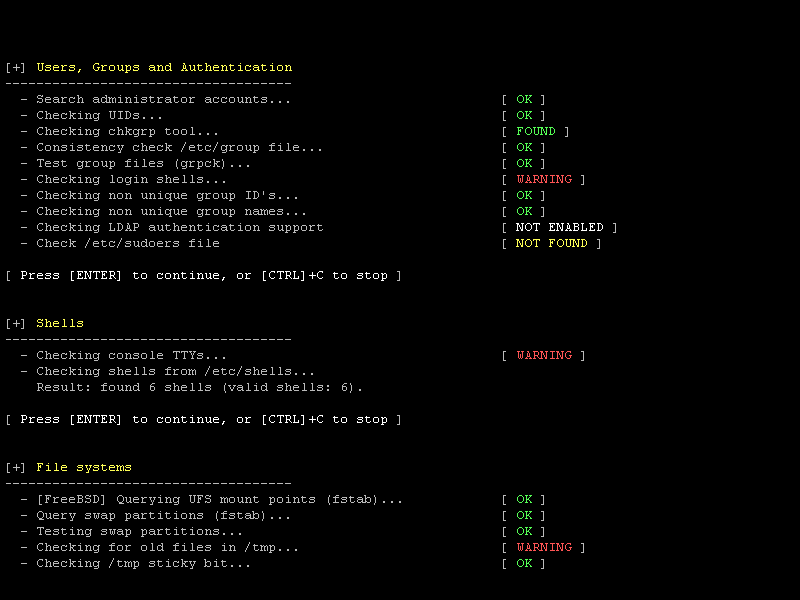
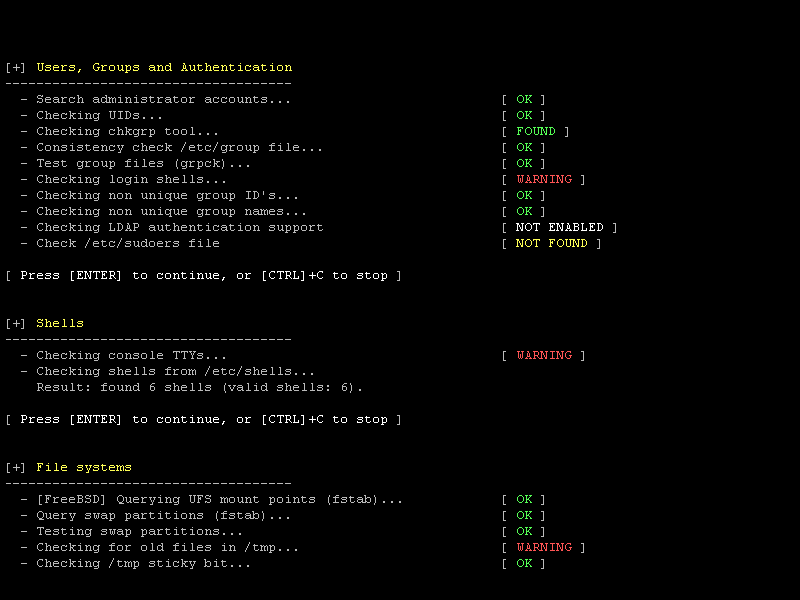
315Lynis – Security auditing tool for Linux, macOS, and UNIX-based systems
Lynis is a security auditing for UNIX derivatives like Linux, macOS, BSD, and others. It performs an in-depth security scan and runs...
-
 103
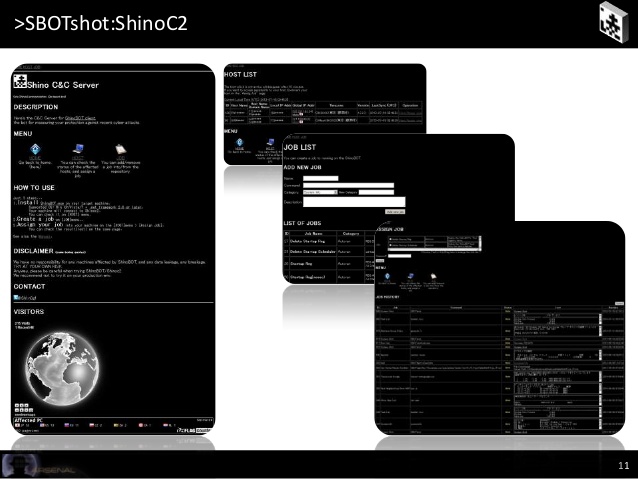
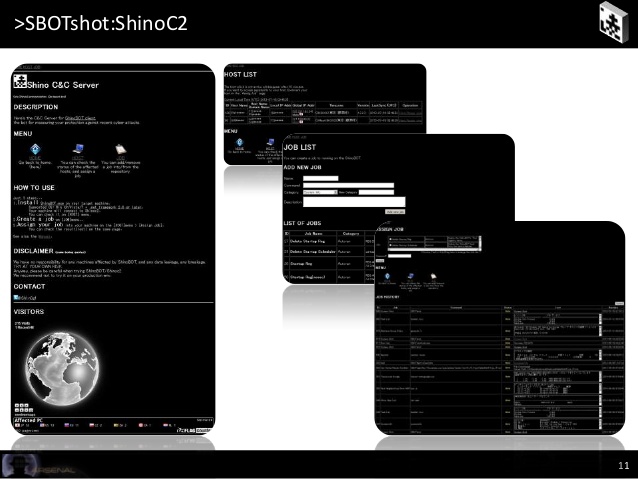
103ShinoBOT – The Rat/Bot Malware Simulator
Are you sure that you can detect an APT malware? YES or NO, whichever, try ShinoBOT; this is a BOT or RAT...
-
 214
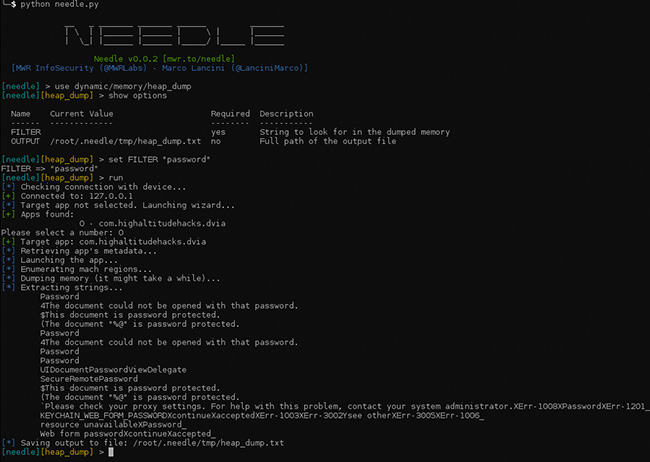
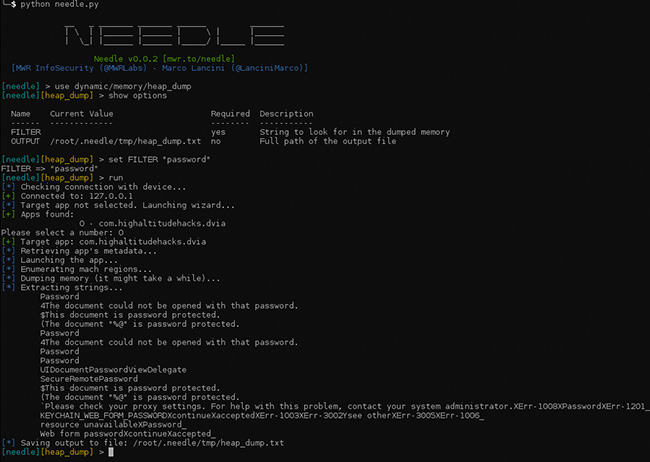
214needle – The iOS Security Testing Framework
Needle is an open source, modular framework to streamline the process of conducting security assessments of iOS apps. Description Assessing the security...






