Hackers Repository
-

 108
108Rollmac – Bypass Free Wifi Time & Data Restriction
Rollmac (Credits: violentshell) Free networks often impose either a time or data restriction and this can be used quickly. When this happens...
-

 111
111Hacking Linux Operating System for Remote Access: Malicious Debian Package
Welcome back today we will be talking about Remote Access of machines running on Linux Operating Systems. Why would someone want to...
-

 170
170NSA’s Hacking Tools and Exploits revealed by Shadow Brokers Group
Hot topics now trending is the leak of thousands of documents from CIA’s vault 7 series of documents, these leaks are continuously exposing...
-
 95
95CIA’s Grasshopper Windows Hacking Framework Revealed
Trending website WikiLeaks today April 7th, 2017, released new 27 documents of vault 7 series of leaked documents, which belonged to US...
-

 195
195Exploit XSS with an Image: Force download
Welcome back today we will talk about Injecting some malicious XSS code into a Image. We will be using Kali Linux for...
-

 130
130V3n0M-Scanner – Python Pentesting Scanner
Popular Pentesting scanner in Python3.6 for SQLi/XSS/LFI/RFI and other Vulns. [Live Project – Python3.6] https://github.com/v3n0m-Scanner/V3n0M-Scanner V3n0M is a free and open source...
-

 105
105EaST – Exploits and Security Tools Framework 2.0.0
Exploits and Security Tools Framework 2.0.0 (Credits C0reL0ader) http://eastfw.com/ «EAST» – «Exploits And Security Tools» penetration testing framework. Overview Pentest framework environment...
-
 184
184Inside Internet Security – What Hackers Don’t want You To Know – Addison Wesley 2002 [E-Book]
This book is a practical guide for anyone designing or administering a corporate or e-business network that runs across a number of...
-
 269
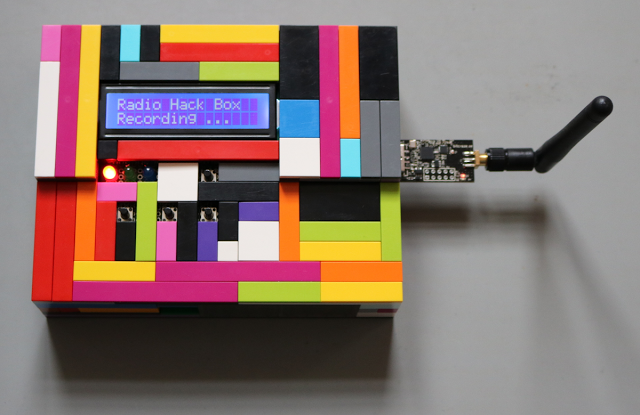
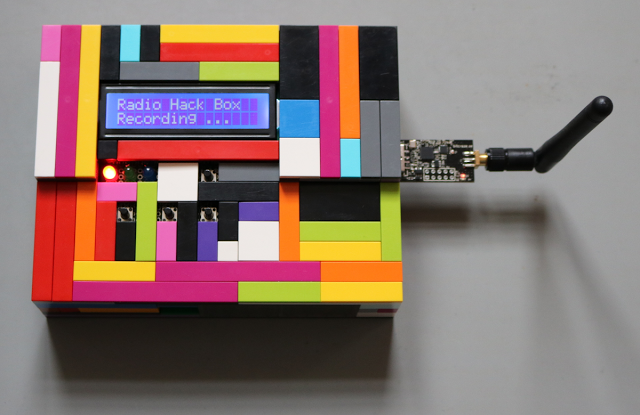
269Radio Hack Box – Tool to Demonstrate Vulnerabilities in Wireless Input Devices
The SySS Radio Hack Box is a proof-of-concept software tool to demonstrate the replay and keystroke injection vulnerabilities of the wireless keyboard...
-
 191
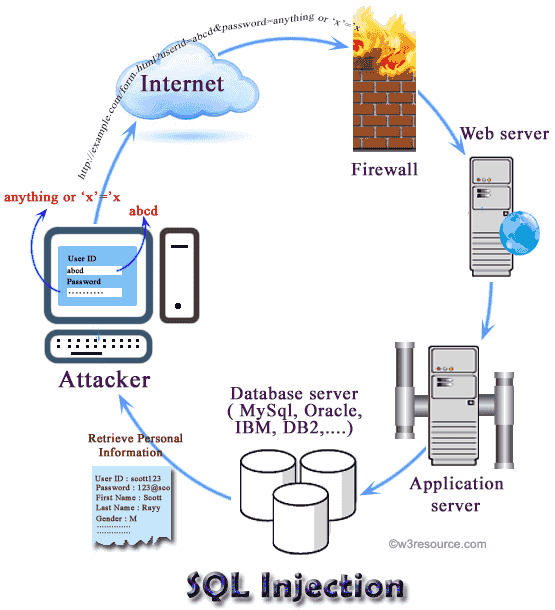
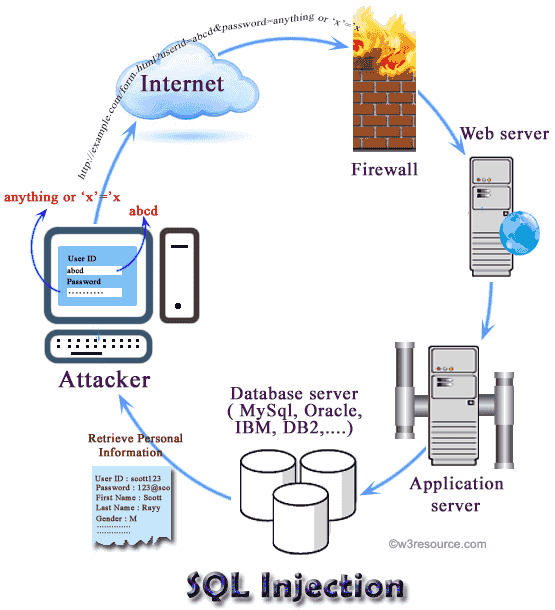
191SQL Inject Me -Firefox Extension used to test for SQL Injection vulnerabilities
SQL Inject Me is a Firefox addon created by Security Compass it is used for finding SQL vulnerabilities in Web applications. SQL...
-

 90
90Browser Extension Shows How Facebook AI Handles Your Data
Browser Extension shows how Facebook handles and tracks your data using machine learning alogorithms. We recently came across this really cool browser...
-

 86
86JuNest – Arch Linux distro that runs upon any Linux distro
The Arch Linux based distro that runs upon any Linux distros without root access. JuNest (Jailed User NEST) is a lightweight Arch...
-

 168
168WAFNinja – Tool to attack Web Application Firewalls
WAFNinja is a tool which contains two functions to attack Web Application Firewalls. WAFNinja - Penetration testers favorite for WAF Bypassing WAFNinja...
-
 101
101The First Human ChatBot to understand Emotions
Today Researchers have been finding a way to make Robots and Artificial intelligence part of our daily life. Artificial intelligent again is...
-

 102
102Researcher Developed A WMI-Based Hacking Tool in PowerShell
Windows Management Instrumentation (WMI) is a set of specifications from Microsoft for combining the management of devices and applications in a network...
-
 257
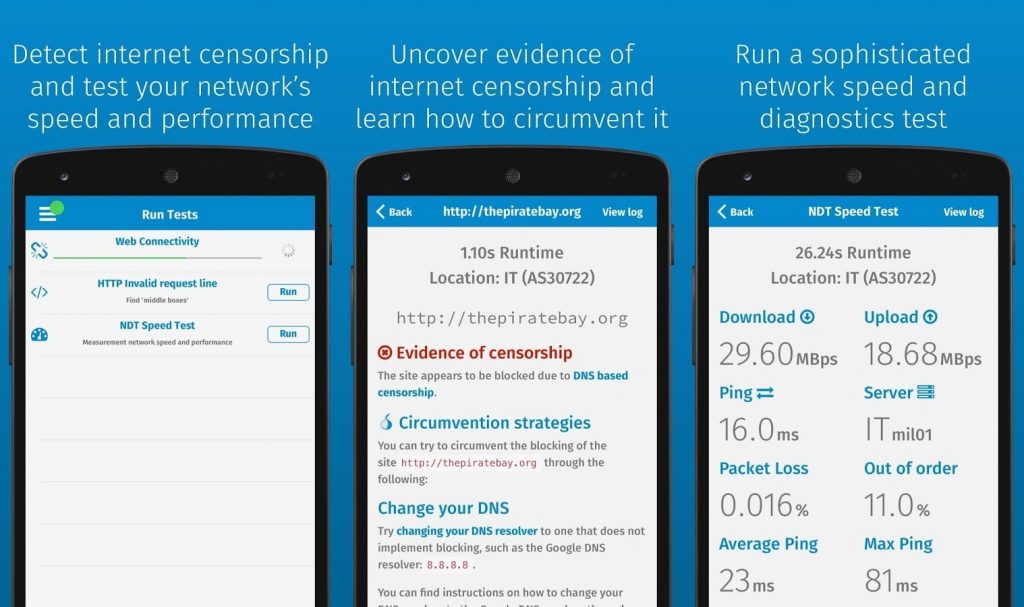
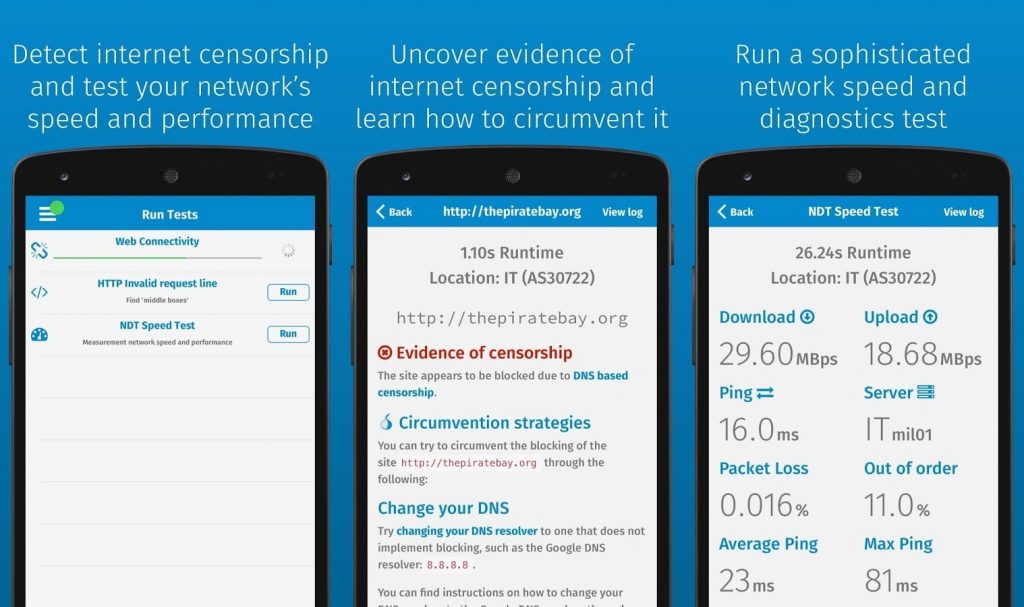
257OONIprobe – Measure Internet Censorship & Speed
Interested in collecting evidence of Internet censorship? Curious about the speed and performance of the network that you are using? By running...
-
 77
77Create an SSH Botnet Client manager Botdr4g0n
The Botdr4g0n is a security tool for DDOS attack on SSH BOT management for distributed attacks. How to Install python 2.7 git...
-
 126
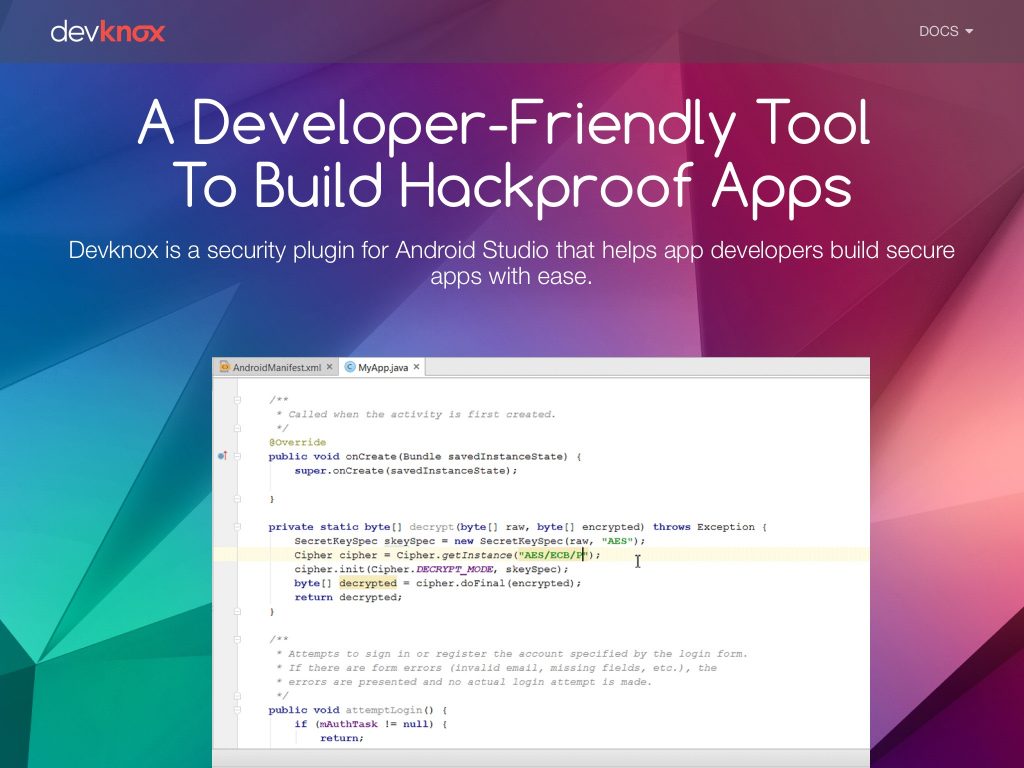
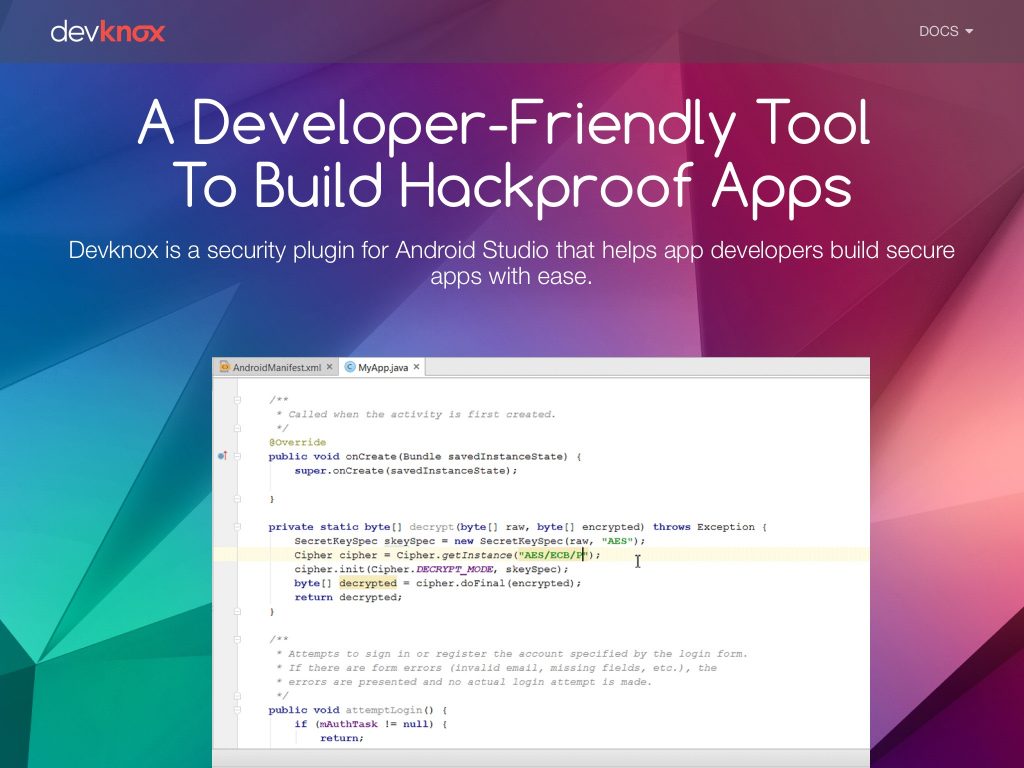
126DevKnox – Autocorrect Security Issues As You Write Code
DevKnox is a first of its kind security tool that enables developers to detect and resolve security issues as they write code...
-
RCE Finder – Scan For Remote Code Execution Exploits
RCE_FINDER How to use root@kali:/rce_finder # python scan_rce.py # LOGO ########################################## #| By Rudra Sarkar - @rudr4_sarkar # #| Loaded Modules :...
-
Clickbait Detector – Detects Clickbait Headlines Using Deep Learning.
Clickbait Detector Detects clickbait headlines using deep learning. If you like this software please consider leaving the author a star on github....
-

 233
233BrainDamage – A fully featured backdoor that uses Telegram as a C&C server
A python based backdoor which uses Telegram as C&C server. Setup Telegram setup: Install Telegram app and search for “BOTFATHER”. Type /help...






