Hackers Repository
-

 202
202BruteSpray – Brute-Forcing from Nmap
BruteSpray takes nmap GNMAP/XML output and automatically brute-forces services with default credentials using Medusa. BruteSpray can even find non-standard ports by using...
-
 287
287Wikileaks Vault 7 Releases New CIA Tool ‘Pandemic.’
The Latest release of Wikileaks Vault 7 Pandemic, which roles of a persistent implant for Microsoft Windows file server and can access...
-

 121
121Top 10 Hacking Tools
Top 10 Hacking Tools Wireshark Wireshark is an open source packet analyzer. It is used to troubleshoot networks, it provides quick and...
-

 335
335Malware Analysis Tools and Cheat list
A large number of computer intrusions involve some form of malicious software (malware), which finds its way to the victim’s workstation or...
-
 259
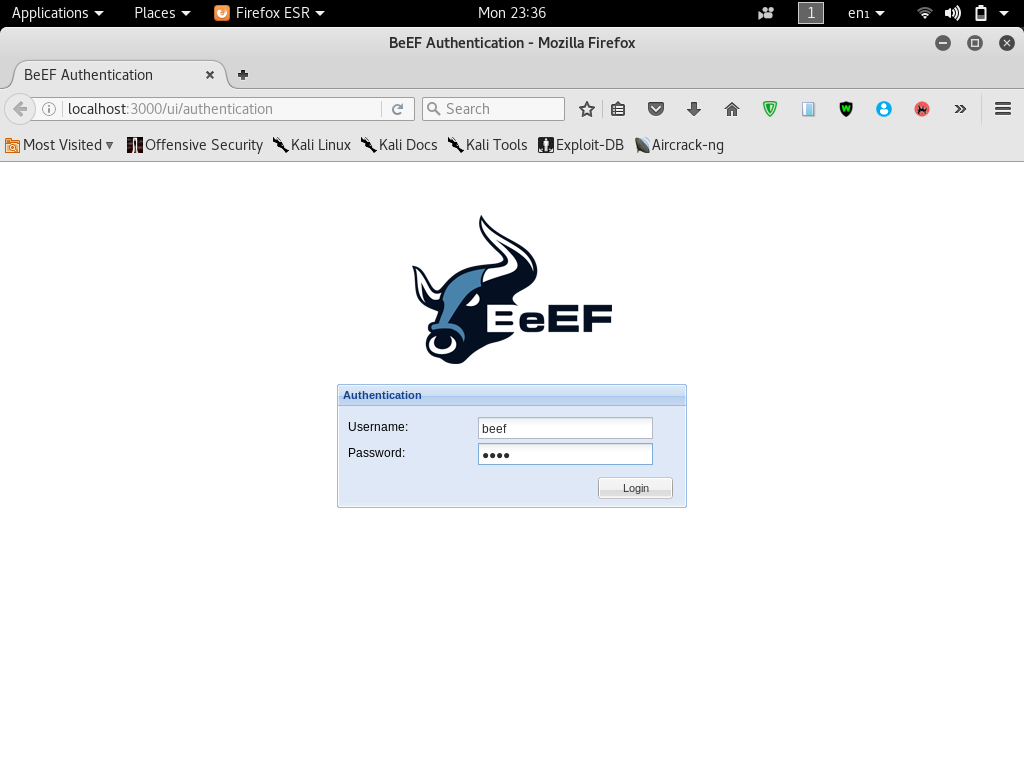
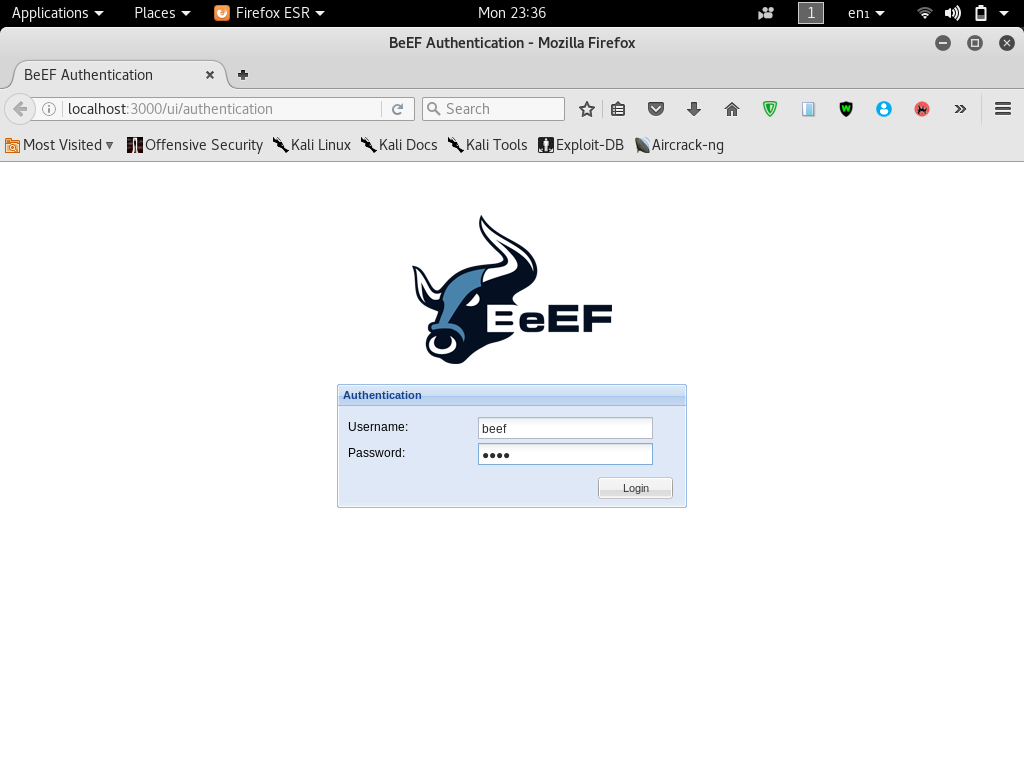
259How to Hack Web Browsers Using BeEF Framework
How to Hack Web Browsers Using BeEF (The Browser Exploitation Framework) What is BeEF? BeEF is short for The Browser Exploitation Framework....
-
 173
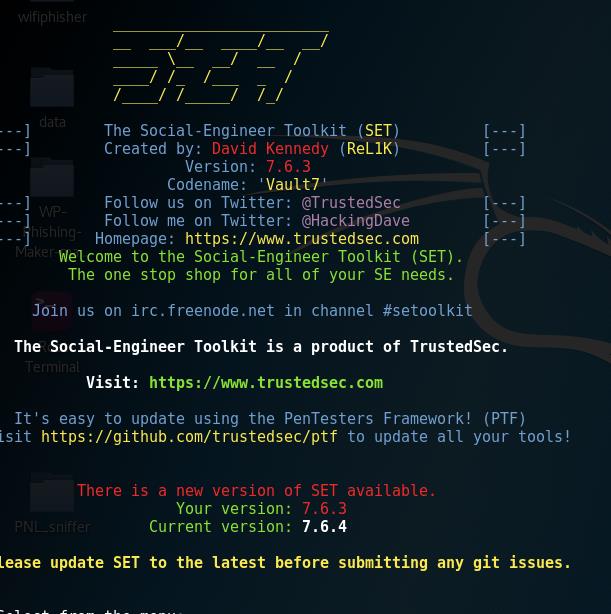
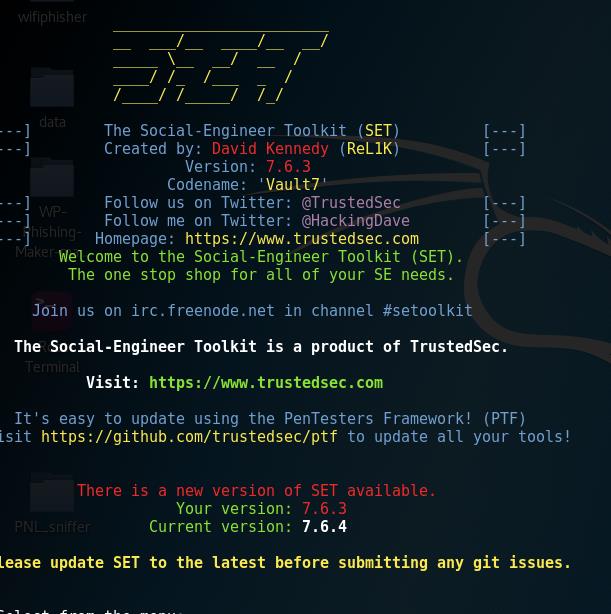
173The Social-Engineer Toolkit (SET) v7.6.4 released
The Social-Engineer Toolkit (SET) v7.6.4 released The Social-Engineer Toolkit (SET) is an open-source penetration testing framework designed to perform advanced and quick...
-

 125
125Around 25 Percent TalkTalk Customers Could Still Be Left With Vulnerable Routers
Up to 25 Percent of TalkTalk UK Customers Could Still Left With Vulnerable Routers Around 25 Percent TalkTalk UK Customers Could Still...
-

 204
204Find Out Who’s Tracking You Through Your Smartphone
With the help of just a few short codes, you can find out more about the settings of your phone and work...
-

 285
285Cameradar – An RTSP Surveillance Camera Access Multitool
Cameradar hacks its way into RTSP CCTV cameras Cameradar allows you to: Detect open RTSP hosts on any accessible target Get their...
-
 164
164Hacking Traffic Lights is Apparently Really Easy
Hacking Internet of Things (IoTs) have become an amazing practice for cyber criminals out there, but messing with Traffic lights would be...
-

 112
112scanless – Public Port Scan Scrapper
Command-line utility for websites that can perform port scans on your behalf. Useful for early stages of a penetration test or if...
-
 188
188WikiLeaks Reveals Athena CIA Spying Program Targeting All Versions of Windows
WikiLeaks has published a new batch of the ongoing Vault 7 leak, detailing a spyware framework – which “provides remote beacon and...
-
 215
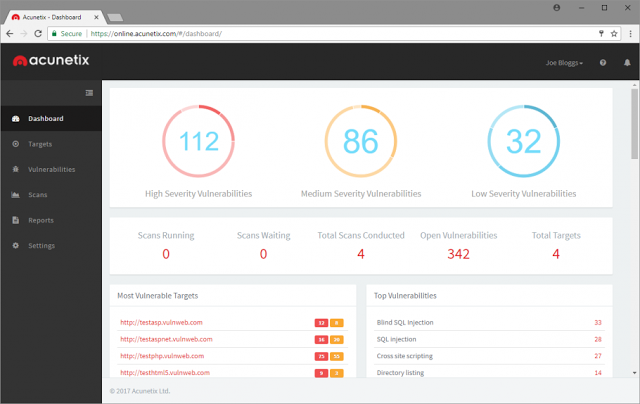
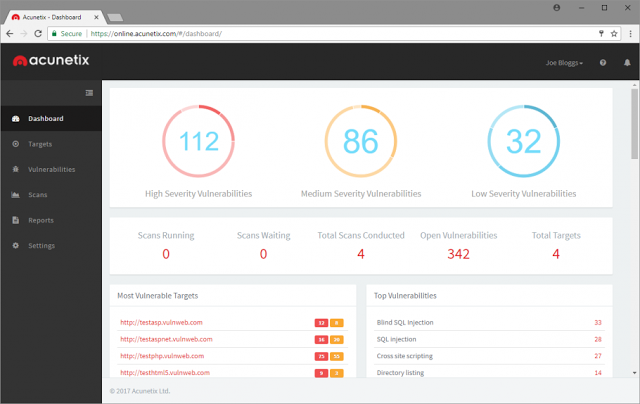
215Major Update of Acunetix Online Vulnerability Scanner
Acunetix Online has undergone a mammoth update, now enjoying all the features and benefits found in Acunetix On Premise, including: Integrated vulnerability...
-

 218
218Hack Wi-Fi Networks Without Cracking with Wifiphisher
Hack Wi-Fi Networks Without Cracking Wifiphisher Welcome back in the last wireless hacking tutorial we talked a little about hacking WPA/WPA2 passphases...
-

 290
290Shadow Brokers promise release of more NSA hacks to be used against the world
As if dealing with the continuing drama of the WannaCry global ransomware attack was not enough, the original group behind the leak...
-

 249
249How to make Fake Conversations on Popular Messenger Apps
People love to do pranks on their friends so that they can look like a fool. It’s also a great way to...
-
 211
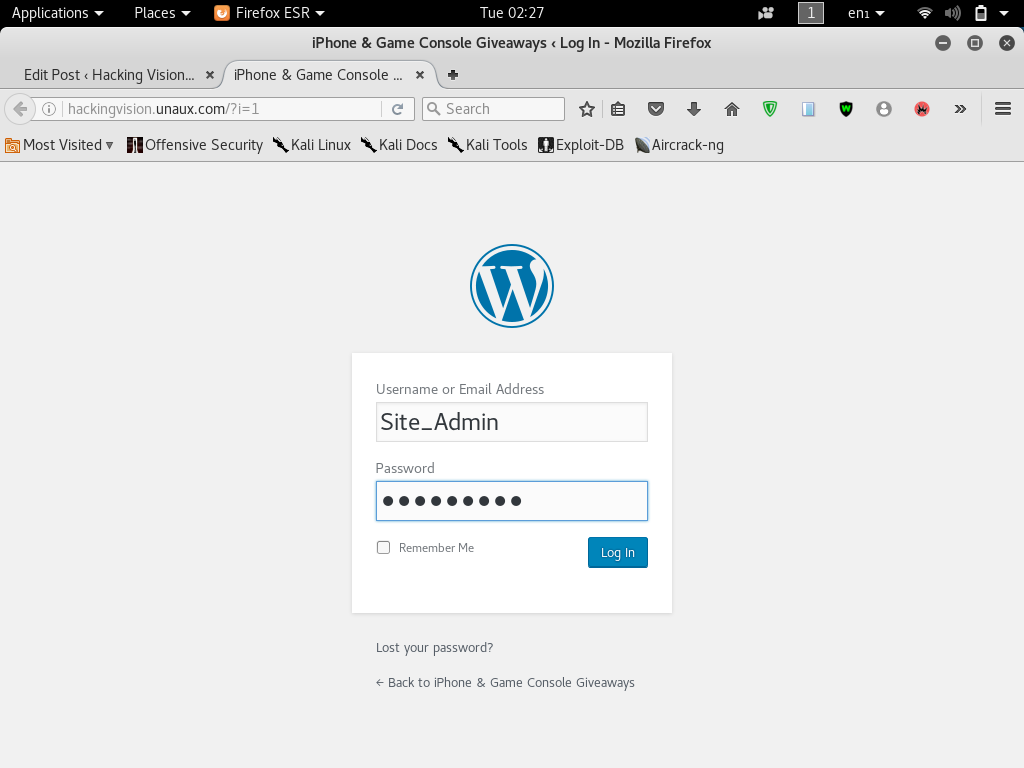
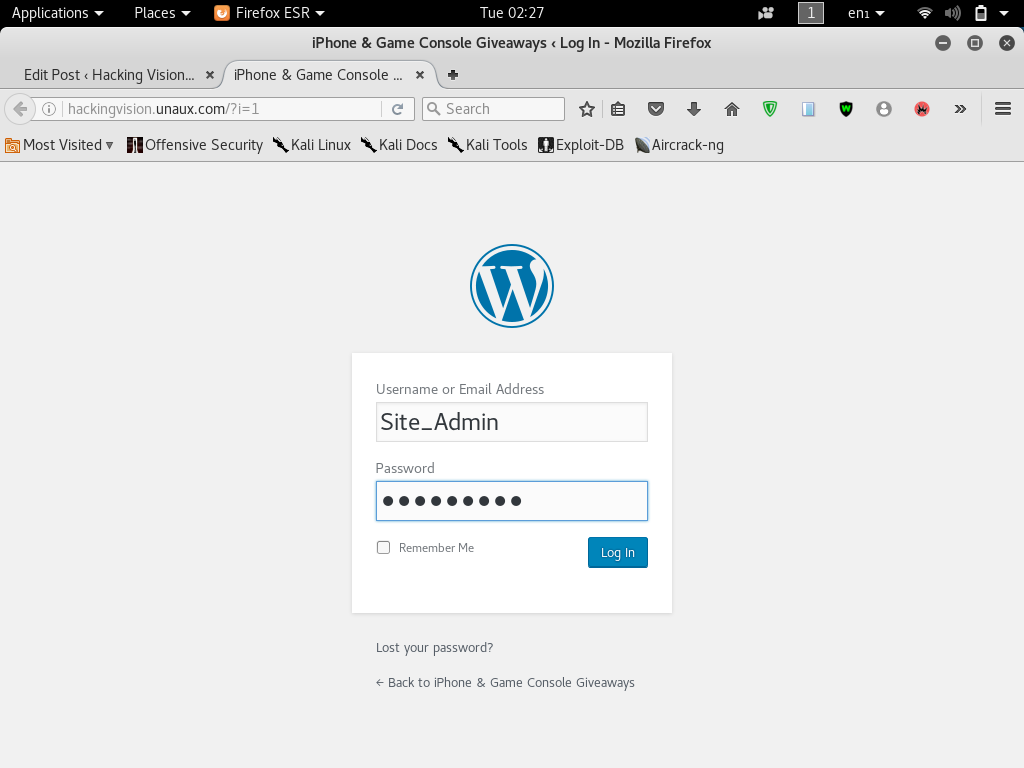
211Creating WordPress Admin Phishing Pages
Hi welcome back today I will show you how to create WordPress phishing pages. Phishing is the practice of sending emails or...
-
 351
351WikiLeaks Reveals ‘AfterMidnight’ & ‘Assassin’ CIA Windows Malware Frameworks
When the world was dealing with the threat of the self-spreading WannaCry ransomware, WikiLeaks released a new batch of CIA Vault 7...
-
 205
205Web Exploit Detector – Tool To Detect Possible Infections, Malicious Code And Suspicious Files In Web Hosting Environments
The Web Exploit Detector is a Node.js application (and NPM module) used to detect possible infections, malicious code and suspicious files in...
-
 147
147Protect Against WannaCry: Microsoft Issues Patch for Unsupported Windows
In the wake of the largest ransomware attack in the history that had already infected over 114,000 Windows systems worldwide since last...
-
 285
285World Biggest Ransomware Attack Hits 74 Countries
World Biggest Ransomware Attack Hits 74 Countries Approx 74 countries affected Currently, 45000 computers are infected Many Hospitals have reported about Ransomware...






