Hackers Repository
-
 261
261Hacking TOR Hidden Services
Hacking TOR Hidden Services What is Tor ? Tor stands for The Onion Route it aims to conceal its users identities and...
-

 314
314Twittor: A Fully Featured Backdoor That Uses Twitter As Command And Control Server
A stealthy Python based backdoor that uses Twitter (Direct Messages) as a command and control server This project has been inspired by...
-

 179
179The LAZY Script – Script to Automate WiFi Penetration & Hacking Tasks
The LAZY script will make your life easier, and of course faster. Credits: arismelachroinos If you like this script follow the project...
-

 250
250RED HAWK – All In One Tool For Information Gathering, SQL Vulnerability Scanning And Crawling
RED HAWK is An All In One Tool For Information Gathering, SQL Vulnerability Scanning and Crawling. Features Of The Tool: Server detection...
-

 145
145Self Destructing Encrypted LUKs Partitions Emergency Nuke Kali Linux
Self Destructing Encrypted LUKs Partitions Emergency Nuke Kali Linux Welcome back today I will show you to set up a self destructing...
-
Explanation of Rootkits & How To Stay Safe From Rootkits
Explanation of Rootkits & How To Stay Safe From Rootkits In this article I will explain what Rootkits are and how we...
-
 143
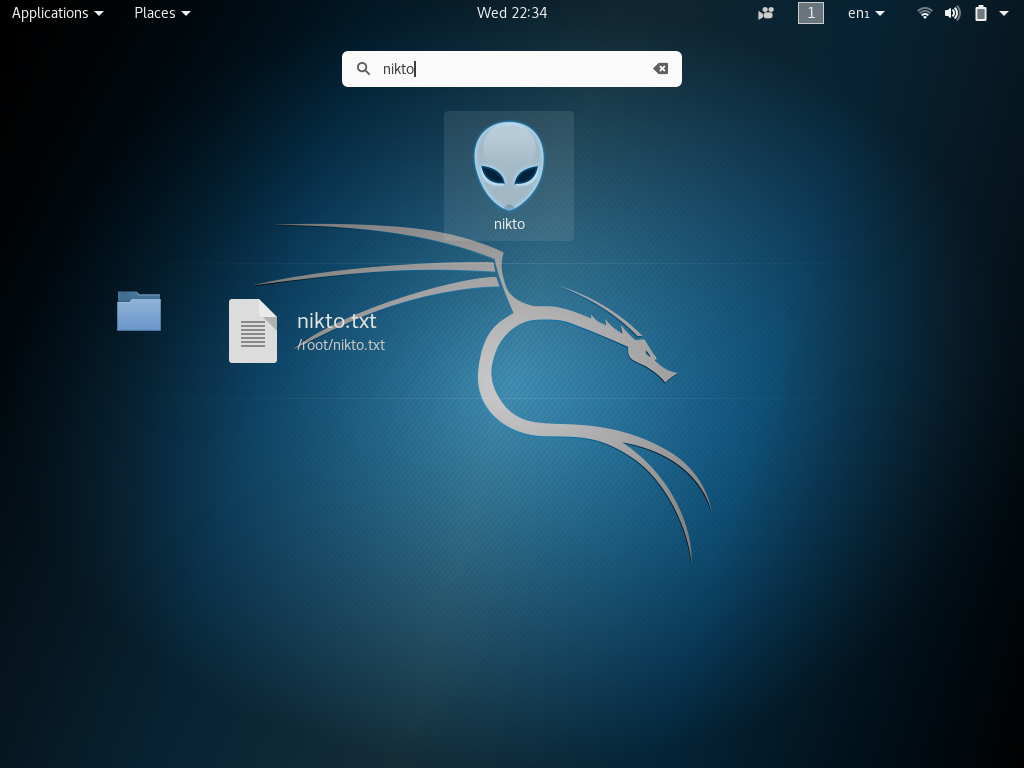
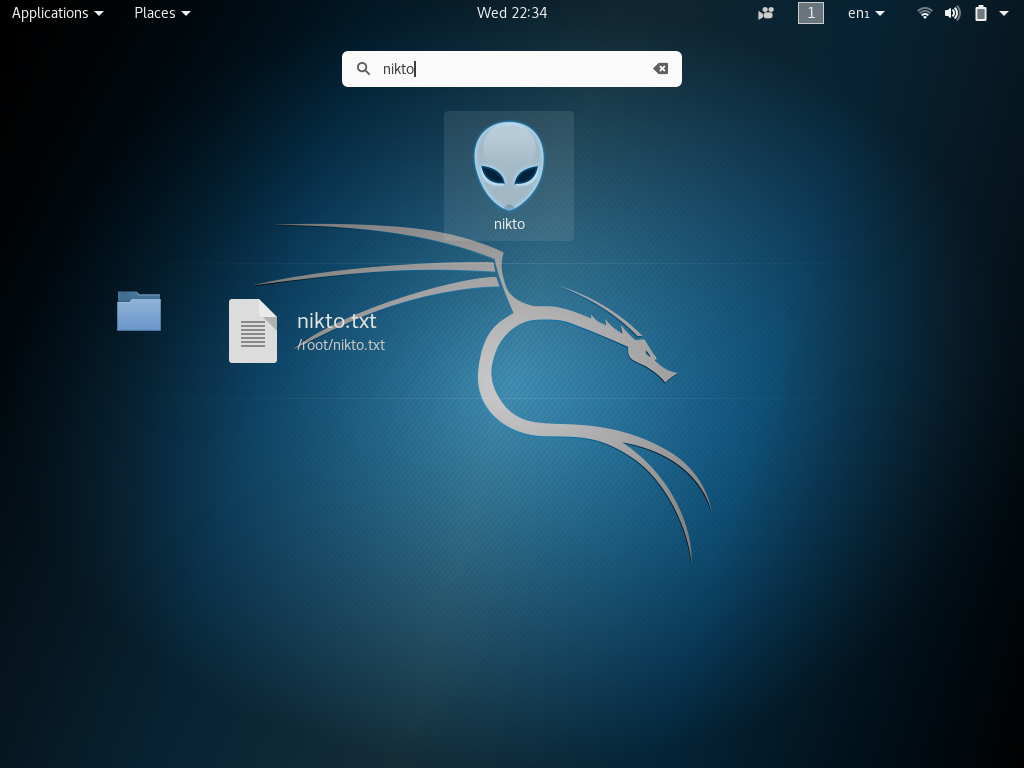
143Scan Web Servers For Vulnerabilities Using Nikto Kali Linux
Scan Web Servers For Vulnerabilities Using Nikto Kali Linux Scan Web Servers with Nikto Welcome back today we will be talking a...
-
 286
286How to Use Metasploit, SEToolkit, AndroRAT Without Opening Ports in Kali Linux
It can be quite annoying when you have limited access to ports on a network and causes problems when pentesting, as you...
-

 128
128Collection of Extra Phishing Scenarios for Wifiphisher
Collection of Extra Phishing Scenarios for Wifiphisher Wifiphisher is a security tool that mounts automated victim-customized phishing attacks against WiFi clients in...
-
 122
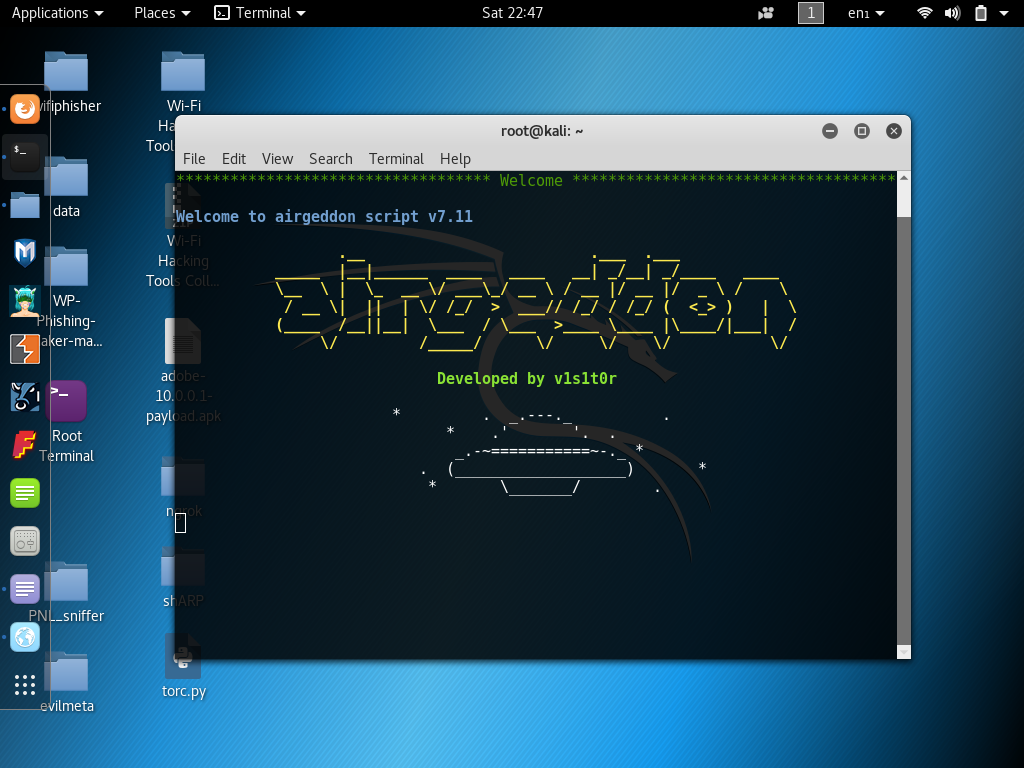
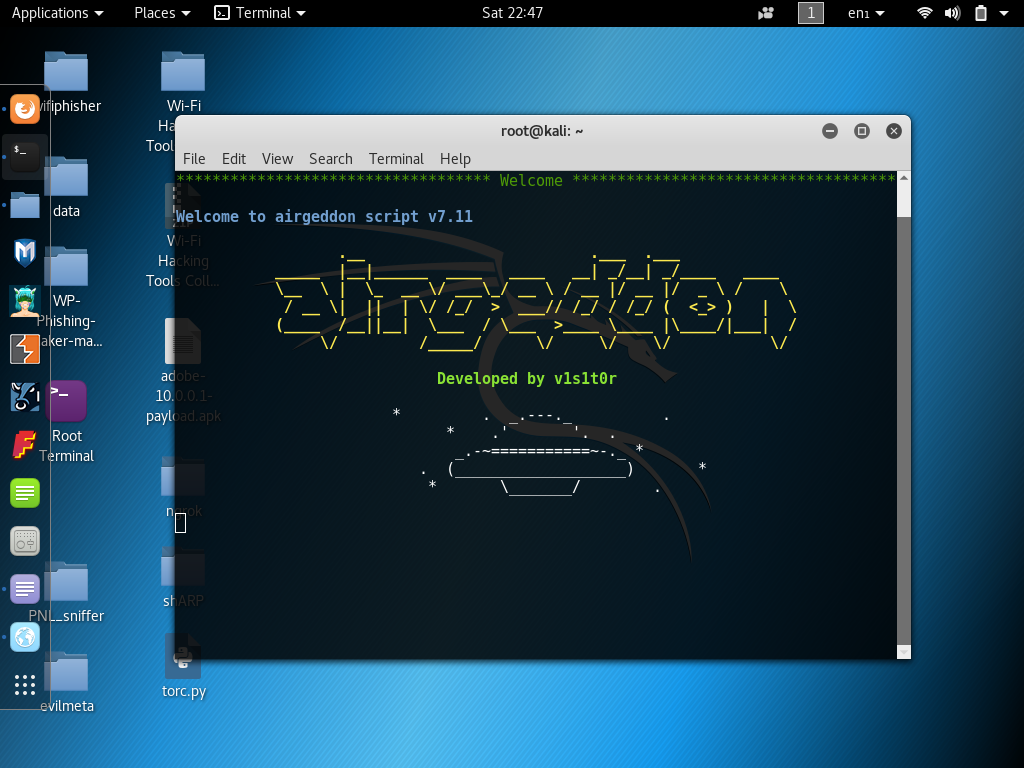
122airgeddon – multi-use bash script to audit wireless networks
airgeddon – multi-use bash script to audit wireless networks Credits: v1s1t0rsh3e3 HackingVision Notes: One of the best scripts around for automating various...
-

 139
139Alexa – Go Hacker Mode
Now you can say “Alexa, hacker mode!” and ask her a series of questions about encodings, command line help for programs like...
-

 118
118How Thieves Can Target High End Devices Using Wifi Signals
How Thieves Can Target High-End Devices Using Wifi Signals Disclaimer HackingVision does not condone illegal use of this software nor does it...
-
 117
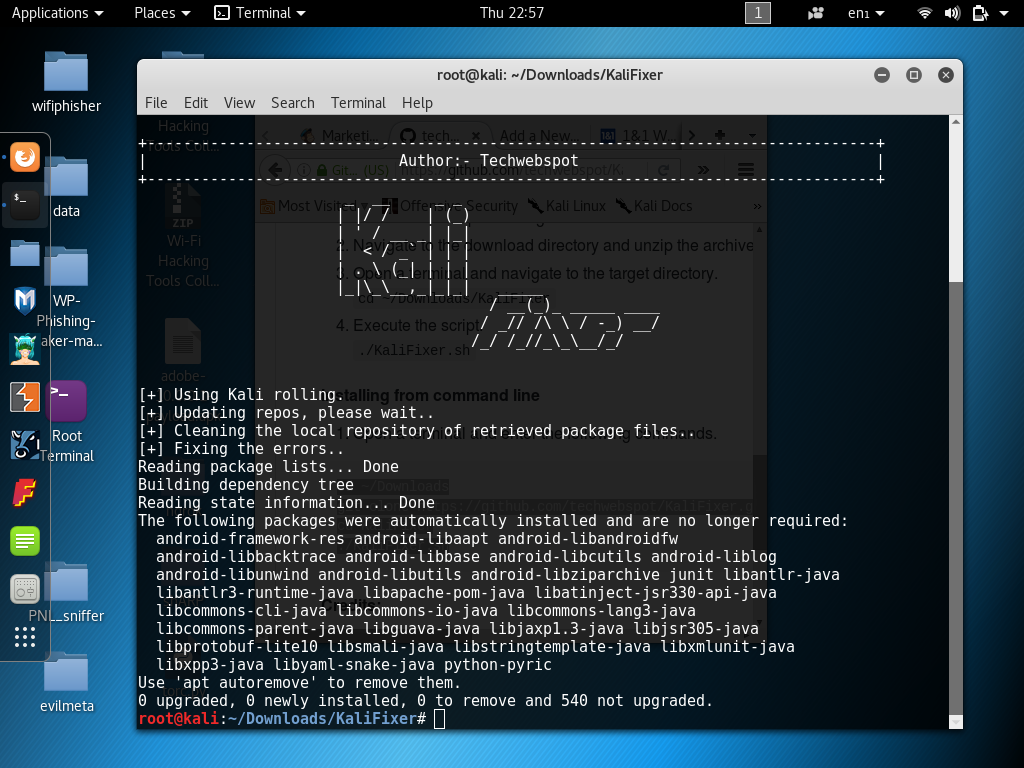
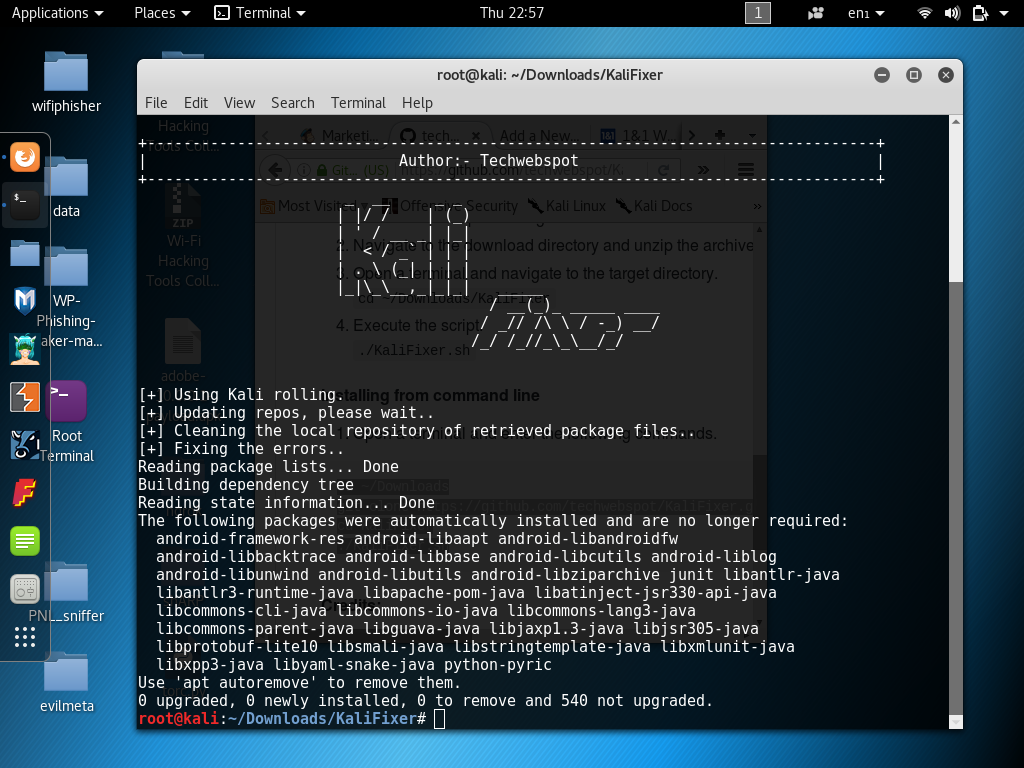
117KaliFixer – Bash Script Fix Kali Linux Repositories Update Errors
KaliFixer Description: KaliFixer is a bash script created to help newbies in Kali Linux. We have all been there that dreaded moment...
-
 257
257WikiLeaks CIA Malware “ELSA” Tracking Geo-Location of WiFi Enabled Windows Computers
WikiLeaks Revealed another Document of CIA Malware Called “ELSA” have an ability to Tracking Geo-Location information of WiFi enabled nearby Target Windows...
-

 161
161pymultitor – Python Multithreaded Tor Script (Algorithm)
pymultitor – Python Multithreaded Tor Script (Algorithm) pymultitor is a Python script designed to run multiple instances of Tor using multi-threading its...
-
 217
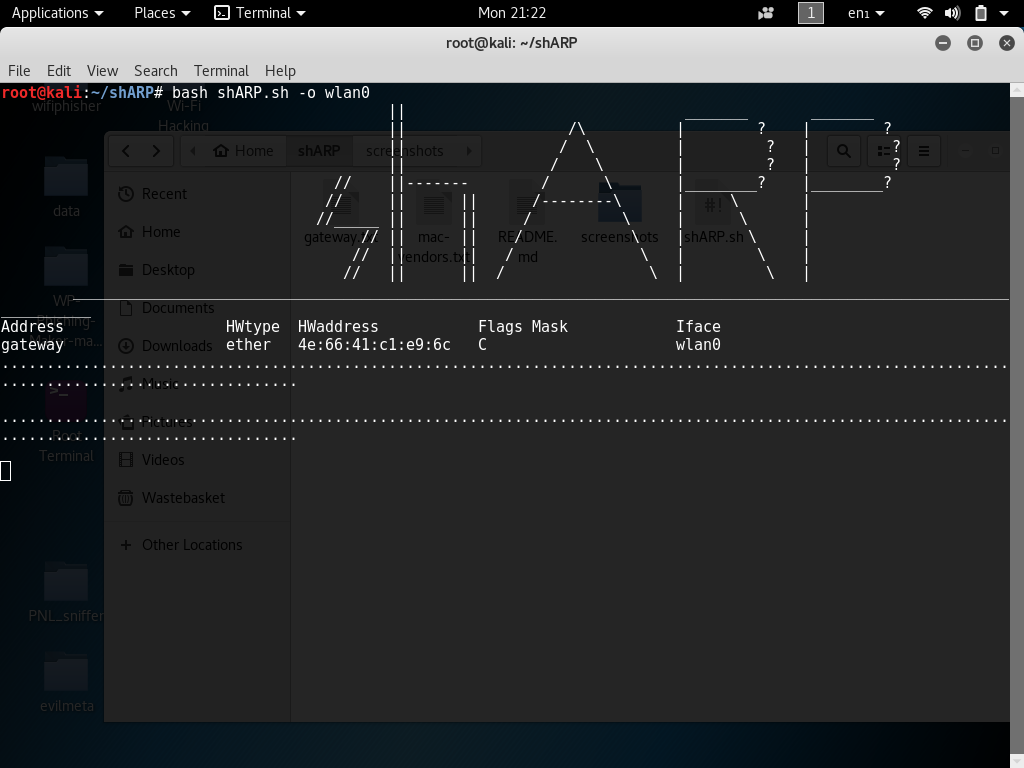
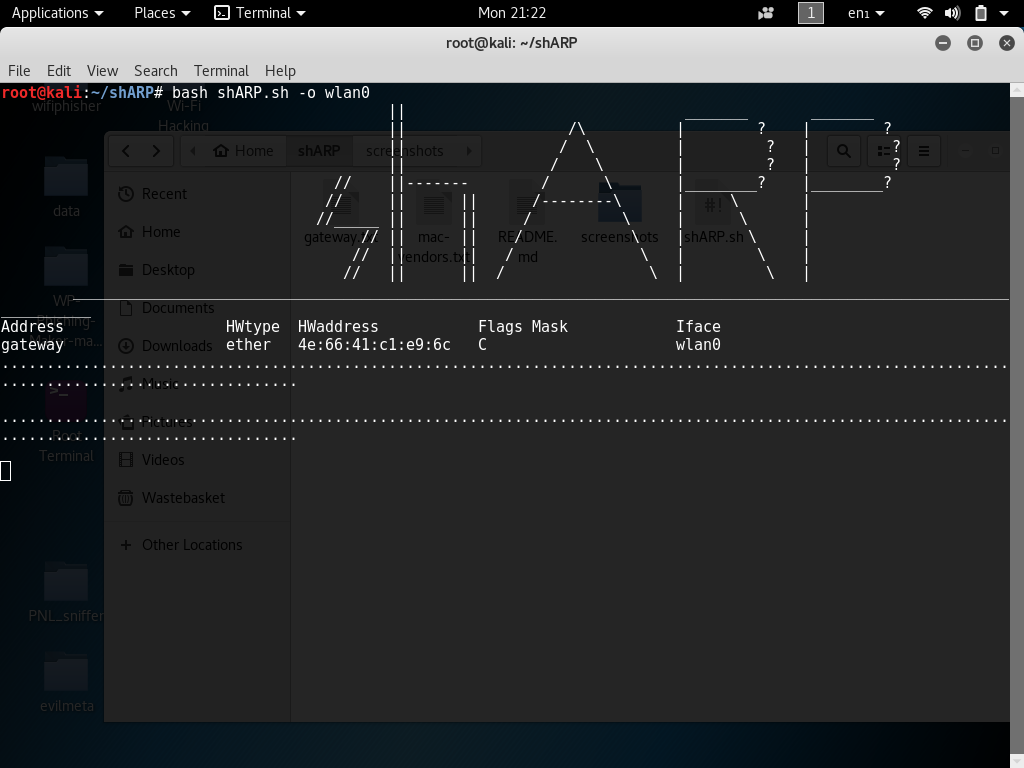
217Prevent Man-In-The-Middle Attacks, ARP-spoofing using shARP
Prevent Man-In-The-Middle Attacks, ARP-spoofing using shARP ARP spoofing is a type of MiTM (Man-in-the-middle) attack it may allow an attacker to intercept...
-

 106
106The Most Dangerous Town on the Internet – Where Cybercrime Goes to Hide (Norton Documentary)
Where Cybercrime Goes to Hide Norton explores the secretive world of bulletproof hosting also known as uncensored hosting. Bulletproof hosts are no...
-

 199
199How to Grab a IP Address Using Fake Cloud Hosting Service
How to Grab IP Address Using Fake Cloud Hosting Service Welcome back today we will be looking in to grabbing IP address’s...
-

 322
322How to use Traceroute Command In Linux
How to use Traceroute Command In Linux Hi, welcome back. Today I will be explaining a little about Traceroute and how we...
-

 152
152Leviathan Framework – Wide Range Mass Audit Toolkit
Leviathan is a mass audit toolkit which has wide range service discovery, brute force, SQL injection detection and running custom exploit capabilities....
-

 270
270SEToolkit – Hacking Windows Machines Using USB/CD Infectious Media Generator
SEToolkit – Hacking Windows Machines Infectious Media Generator Requirements Linux based Operating System (In this tutorial we are using Kali Linux) SEToolkit...






