Hackers Repository
-

 103
103FaceNiff – Hacking Tool for Android Intercept Web Sessions
FaceNiff -Android App Intercept web session profiles over WiFi Connection FaceNiff – Hacking Tool: Faceniff is an Android app for hackers &...
-

 364
364Using BeEF to Hack Facebook Credentials
Are you trying to know the Username and Password of any FB Account but you don’t want to hack their Account? It’s...
-

 92
92DEFCON – The Full Documentary
DEFCON – The Full Documentary Defcon is the world’s longest running and largest underground hacking conference hosted in Las Vegas it was Started...
-
 101
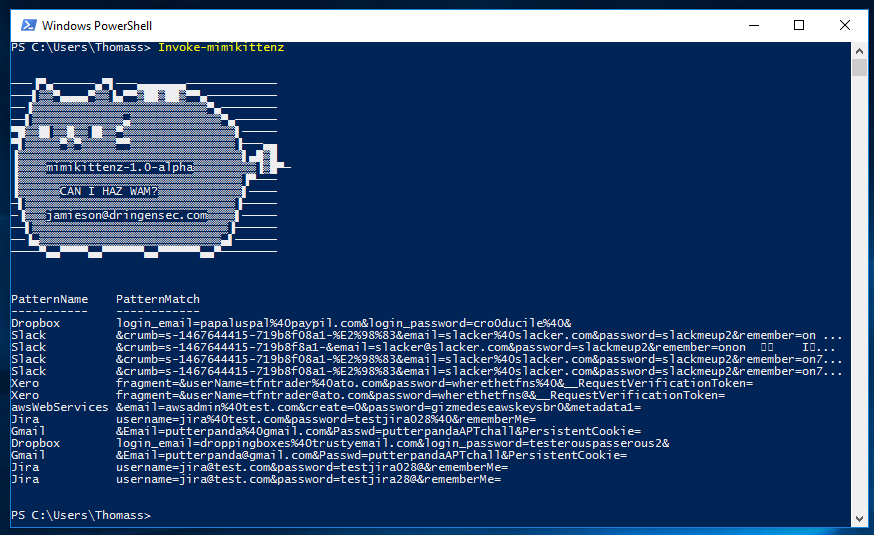
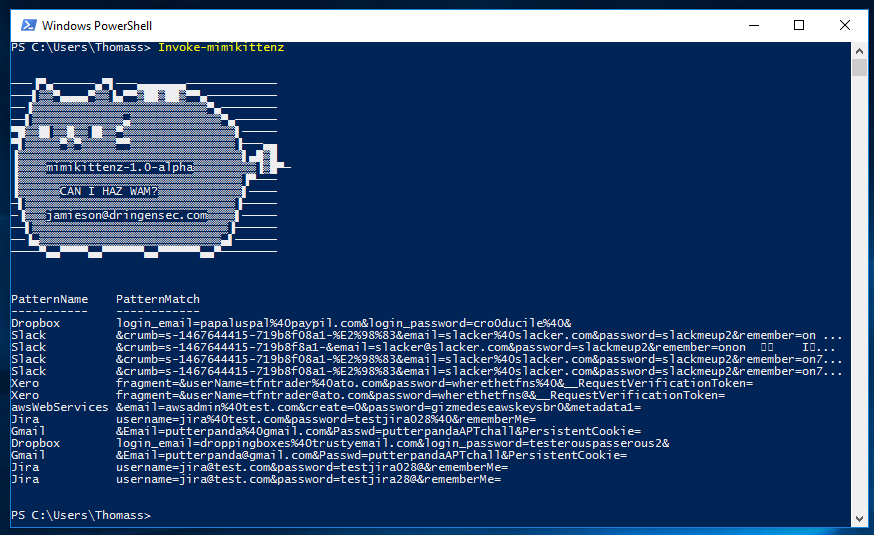
101mimikittenz – Powershell Tool for Extracting Juicy info from Memory RAM
A post-exploitation powershell tool for extracting juicy info from memory. mimikittenz mimikittenz is a post-exploitation powershell tool that utilizes the Windows function...
-

 250
250NSA’s GitHub Account Has 32 Open Source Projects For The Public
The American security agency NSA was very secretive in its operations in the past. But with time, and unwanted revelations coming to...
-
 242
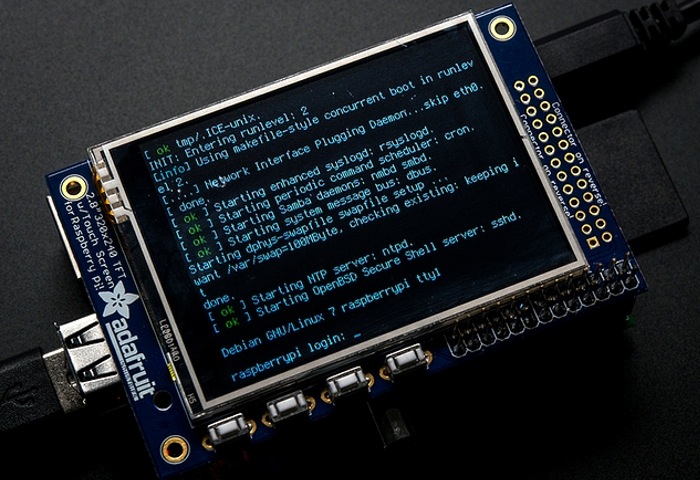
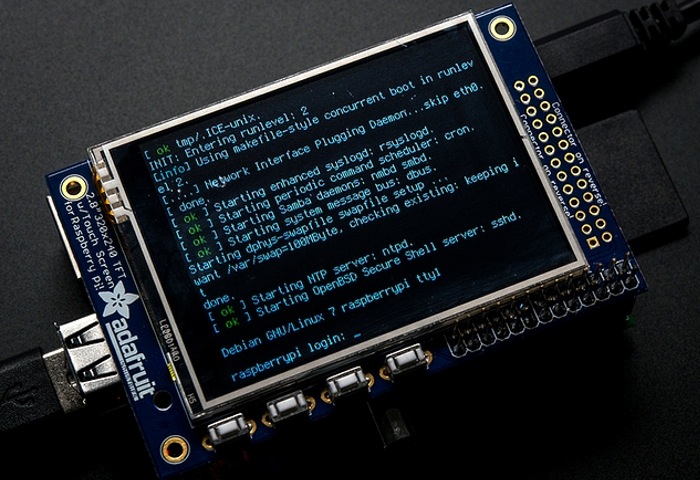
242HoneyPi – Build your own reliable Honeypot
It is astonishingly easy as an attacker to move around on most networks undetected. Let’s face it, unless your organization is big...
-

 298
29830 Best Free Hacking Apps & Tools For Android
In this article we will list the Top 30 Android Hacking Tools to help with networking & pentesting tasks. 30 Best Free...
-

 241
241The Bicho – An Advanced Car Backdoor Maker
For the first time, a hardware backdoor tool is presented having several advanced features, such as: remote control via SMS commands, automated...
-
 334
334How to use Hacking Tools Without Opening Ports on Router NAT Firewall
Hello, welcome back in a recent tutorial (How to Use Metasploit, SEToolkit Without Opening Ports Kali Linux) we worked with Ngrok creating...
-

 244
244DDOS a website anonymously by using kali linux
DDOS tools are capable of putting heavy loads on HTTP servers and bring them to their knees by exhausting it’s resources. What...
-
 345
345Wikileaks Revealed New CIA Wireless Hacking Tool “Cherry Blossom” Compromise Your Wireless Network Devices using MITM Attack
Wikileaks Revealed another CIA Cyber weapon called “CherryBlossom” which is Specially Developed to compromise the Wireless Network Devices including wireless routers and...
-
 282
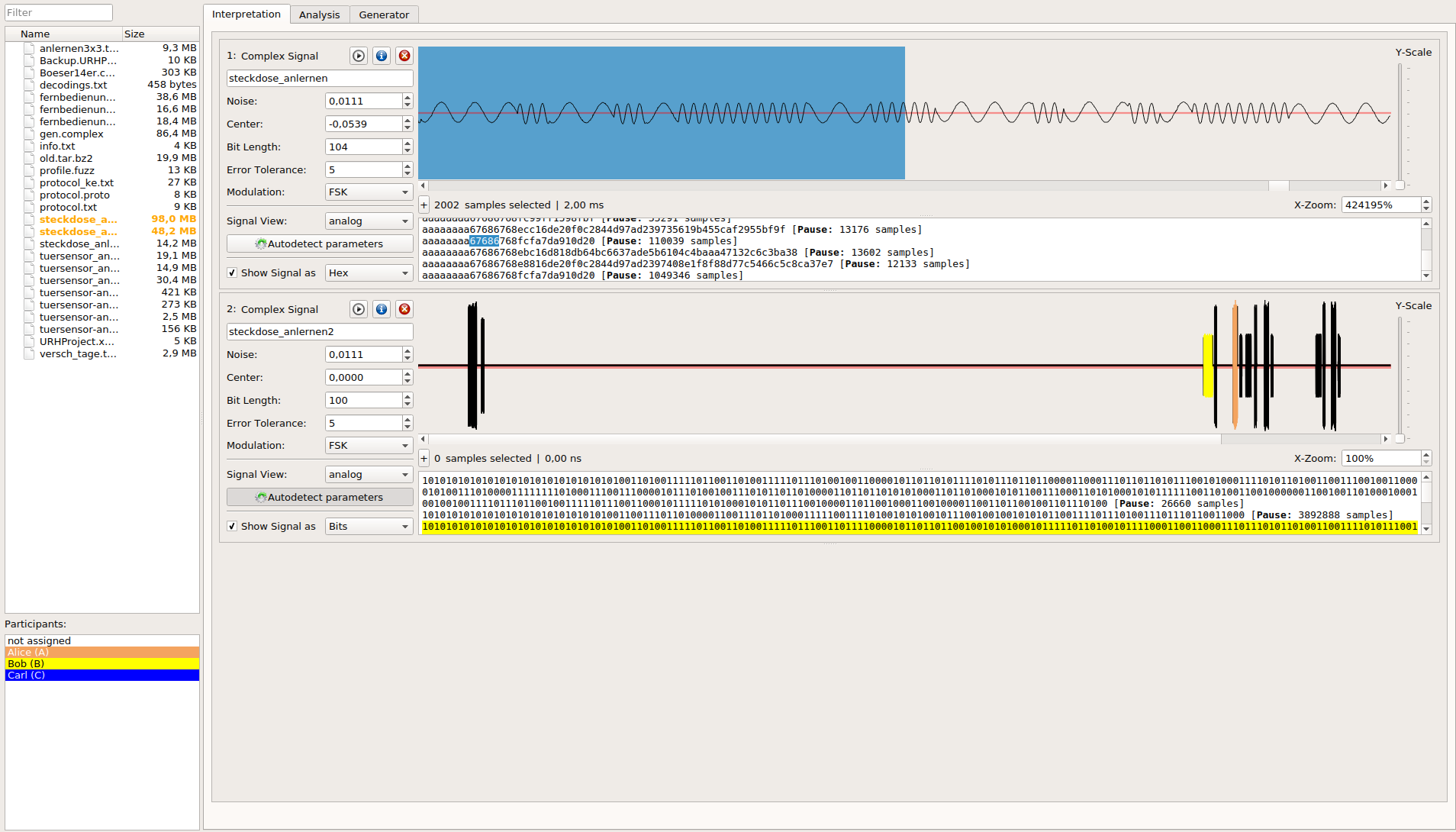
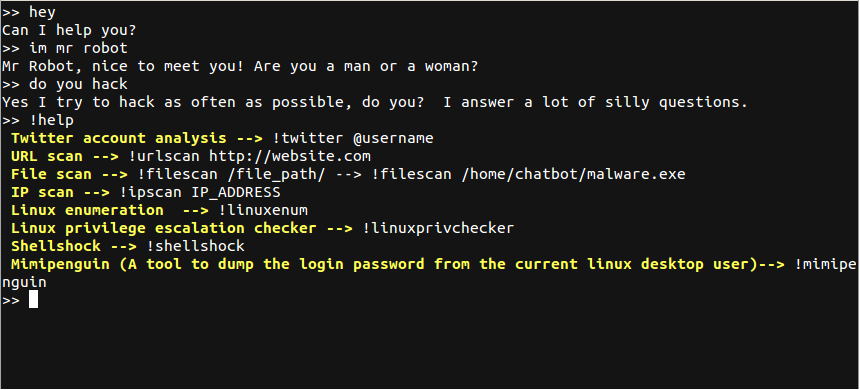
282Universal Radio Hacker
The Universal Radio Hacker is a software for investigating unknown wireless protocols Features include hardware interfaces for common Software Defined Radios easy...
-
 196
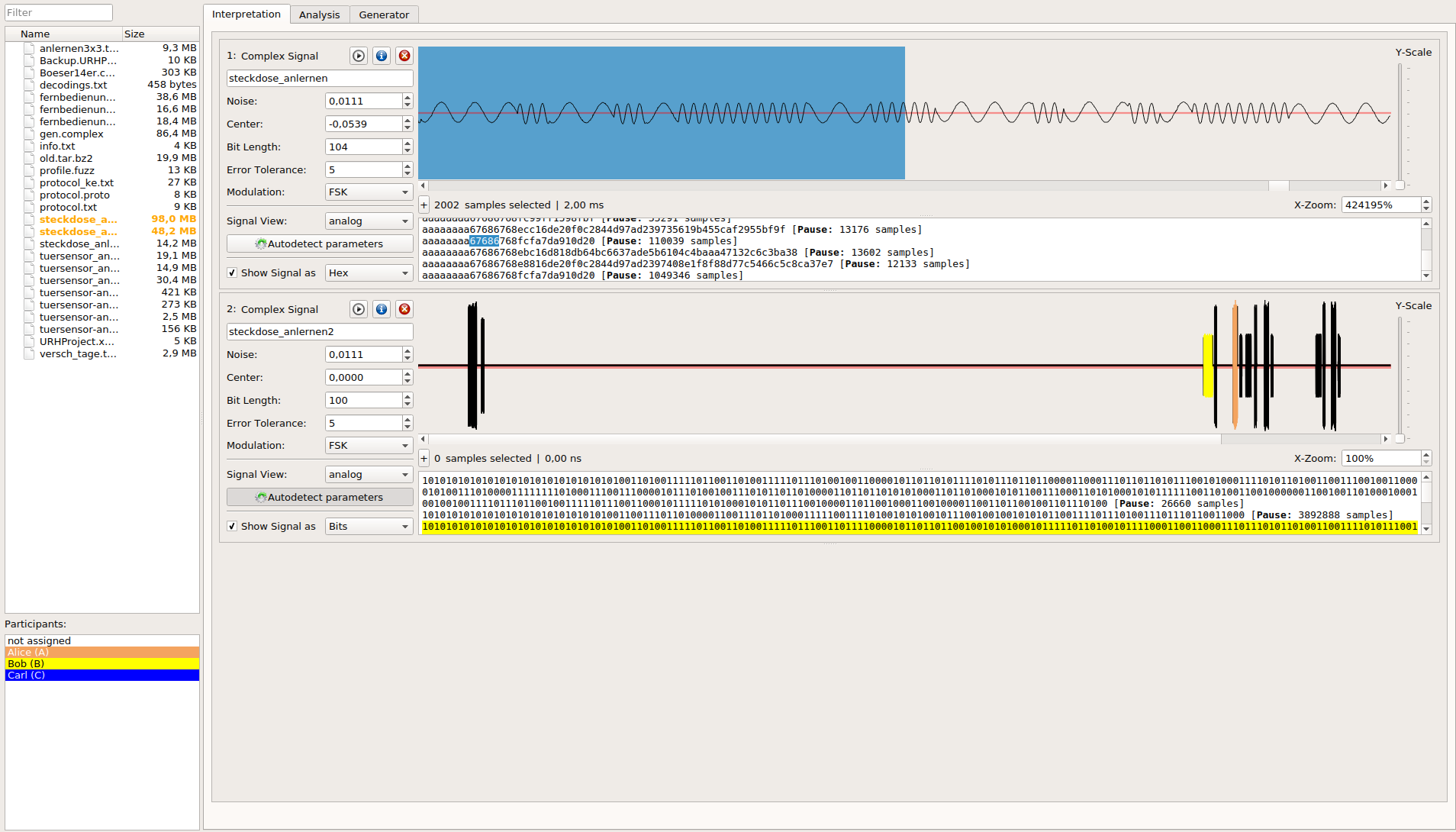
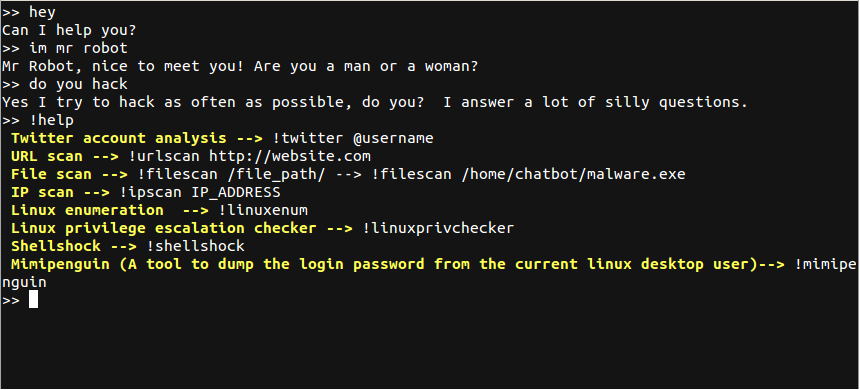
196HackerBot – Chat with your assistant and enjoy hacking
This bot is a combination of chatbot and hacking tools Chatting Twitter account analysis Url scan File scan Ip scan Linux enumeration...
-

 323
323How to Use Metasploit, SEToolkit Without Opening Ports Kali Linux
How to Use Metasploit, SEToolkit Without Opening Ports Kali Linux It can be quite annoying when you have limited access to ports...
-
 273
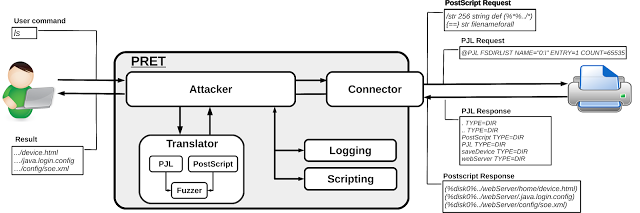
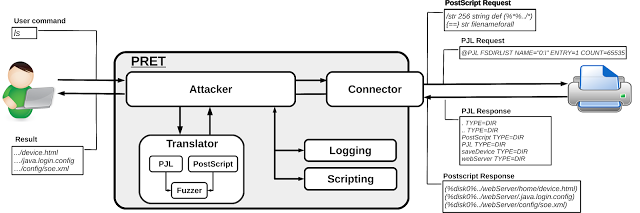
273Printer Exploitation Toolkit – Hacking Printers
PRET is a new tool for printer security testing developed in the scope of a Master’s Thesis at Ruhr University Bochum. It...
-
 168
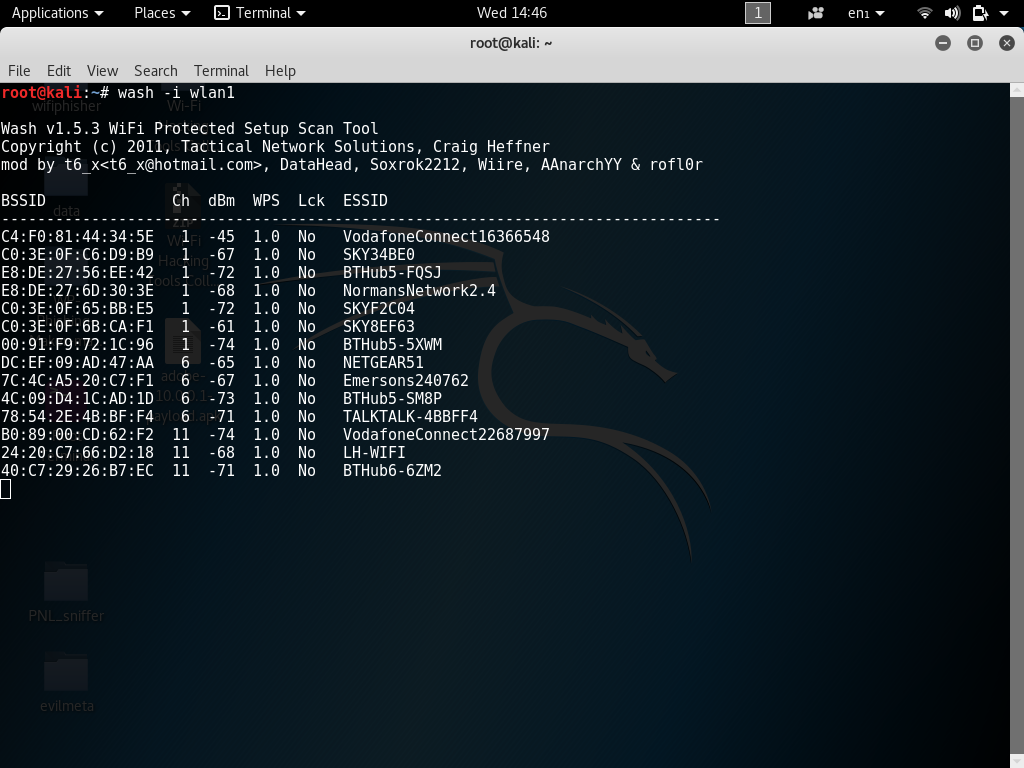
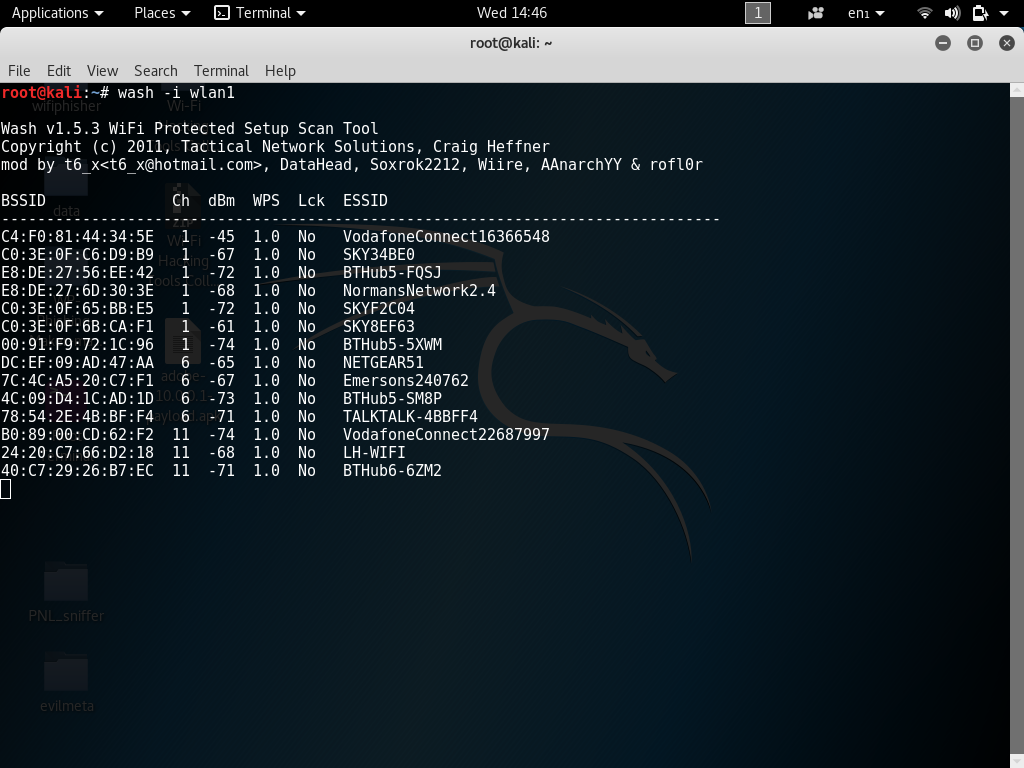
168Finding WPS enabled AP’s Kali Linux Wash – HackingVision
Welcome back today I will be showing you how to find if a nearby router is WPS enabled in Kali Linux using...
-

 231
231Hacking Wi-Fi Clients for Remote Access Using Rouge Access Point Evil Twin Metasploit, BeEF, Wifiphisher
Hacking Wi-Fi Clients for Remote Access Using Rouge Access Points Welcome back in this Tutorial you will learn how to compromise a...
-

 119
11910 Youngest Hackers Who Caused Chaos
10 Youngest Hackers Who Caused Chaos Today we are going to be looking at the 10 youngest hackers who Caused Chaos. When...
-

 380
380Kwetza – Python script to inject existing Android applications with a Meterpreter payload
Kwetza is a tool that allows you to infect an existing Android application with a Meterpreter payload. What does it do? Kwetza...
-
 202
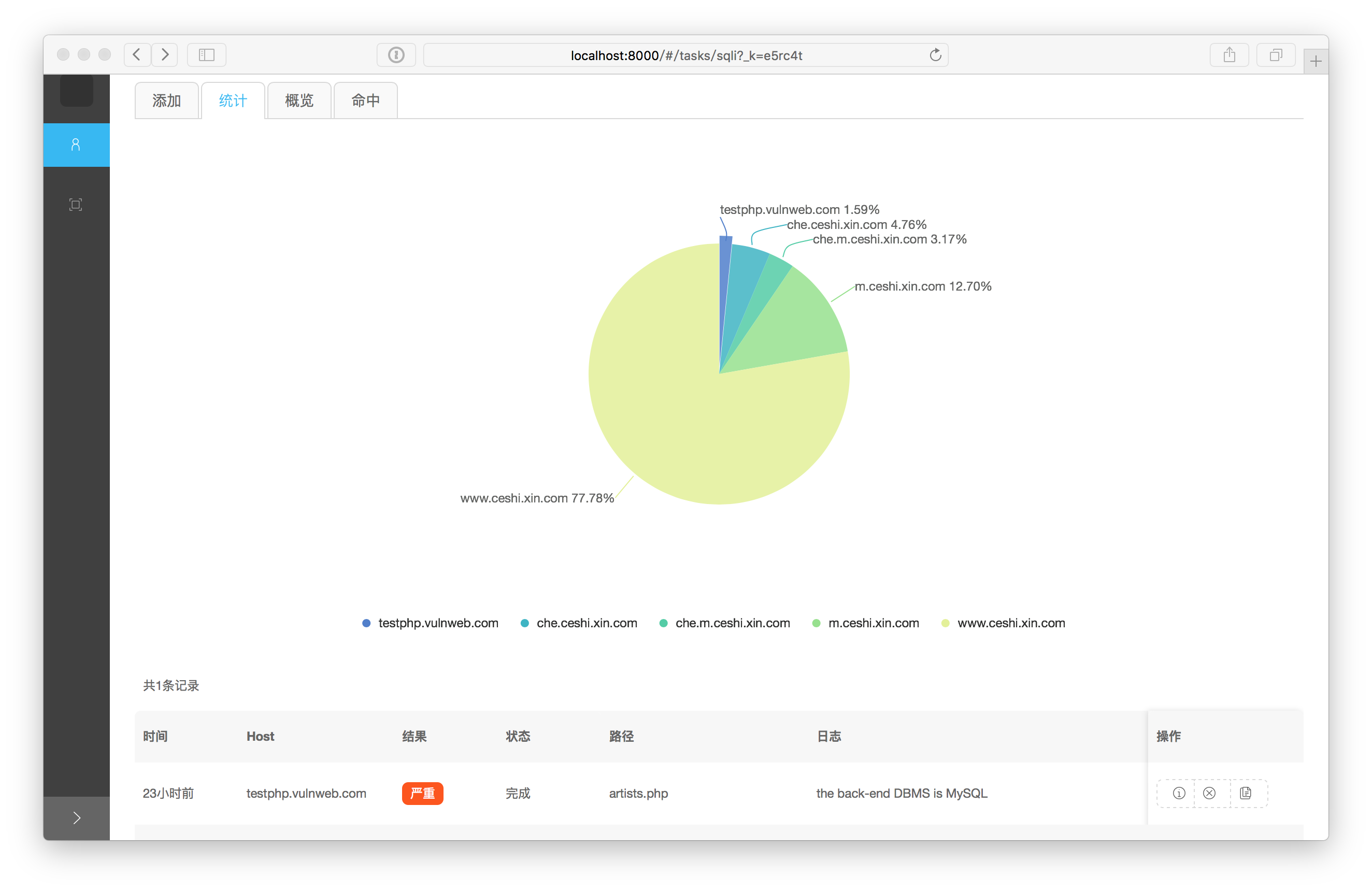
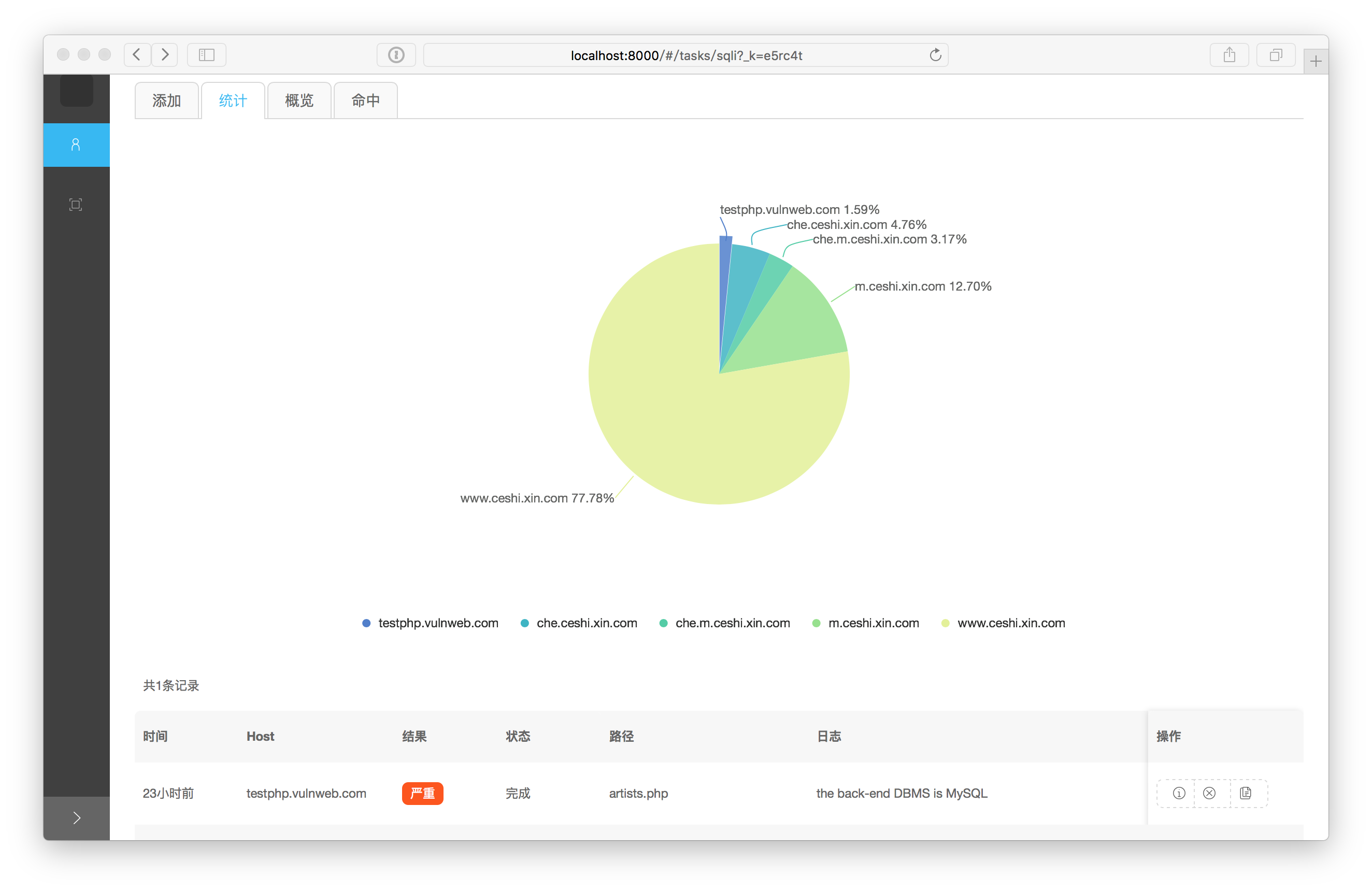
202SQLiScanner – Automatic SQL injection with Charles and SQLMap API
Automatic SQL injection with Charles and sqlmap api Download SQLiScanner (Credits 0xbug) – http://0r1.me/SQLiScanner/ Github: https://github.com/0xbug/SQLiScanner Installation Preferably, you can download SQLiScanner...
-

 179
179WiFi-Pumpkin – Framework for Rogue Wi-Fi Access Point Attack
WiFi-Pumpkin – Framework for Rogue Wi-Fi Access Point Attack WiFi-Pumpkin is a very complete framework for auditing Wi-Fi security. The main feature...






