Hackers Repository
-

 234
234Apple and Facebook Behind The Shutting Down of KickassTorrents
KickassTorrents (KAT), one of the most popular websites for illegal file sharing was shut down after the alleged 30-year-old Ukranian owner and...
-
 174
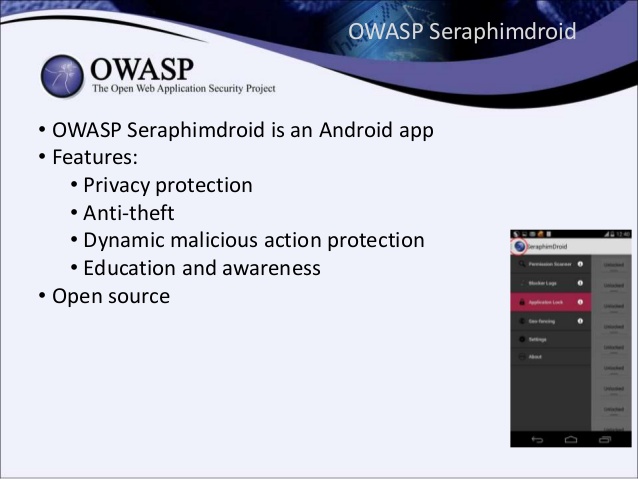
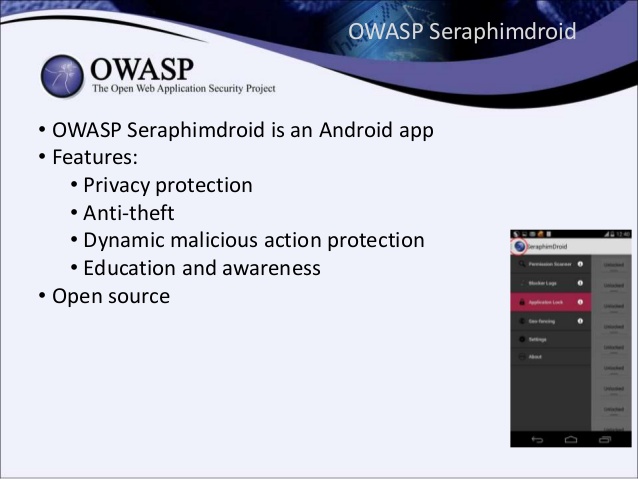
174OWASP SeraphimDroid Project
OWASP Seraphimdroid is a privacy and security protection app for Android devices. It enables users to protect their devices against malicious software...
-
 272
272Infoga – Email Information Gathering
Infoga is a tool, similar to The Harvester, for gathering e-mail accounts information from different public sources (search engines, pgp key servers)....
-

 221
221malwaresearch – A command line tool to find and download malware
A Tool developed for searching malwares at openmalware.org by command line, allowing specific malware to be downloaded via shell. The tool was...
-

 358
358Top Hacking Sites, CTFs and Wargames To Practice Your Hacking Skills
As the world continues to turn everything into an app and connect even the most basic devices to the internet, the demand...
-

 254
254Kali Linux 2017.1 Released
As with all new releases, you have the common denominator of updated packages, an updated kernel that provides more and better hardware...
-

 84
84VAMPY – Minimal tool for RAM dumping
VAMPY – Minimal tool for RAM dumping. Installation git clone https://github.com/m4n3dw0lf/vampy cd vampy python vampy.py Basics usage: -o, --output <DIRECTORY/PATH> Output directory...
-
 409
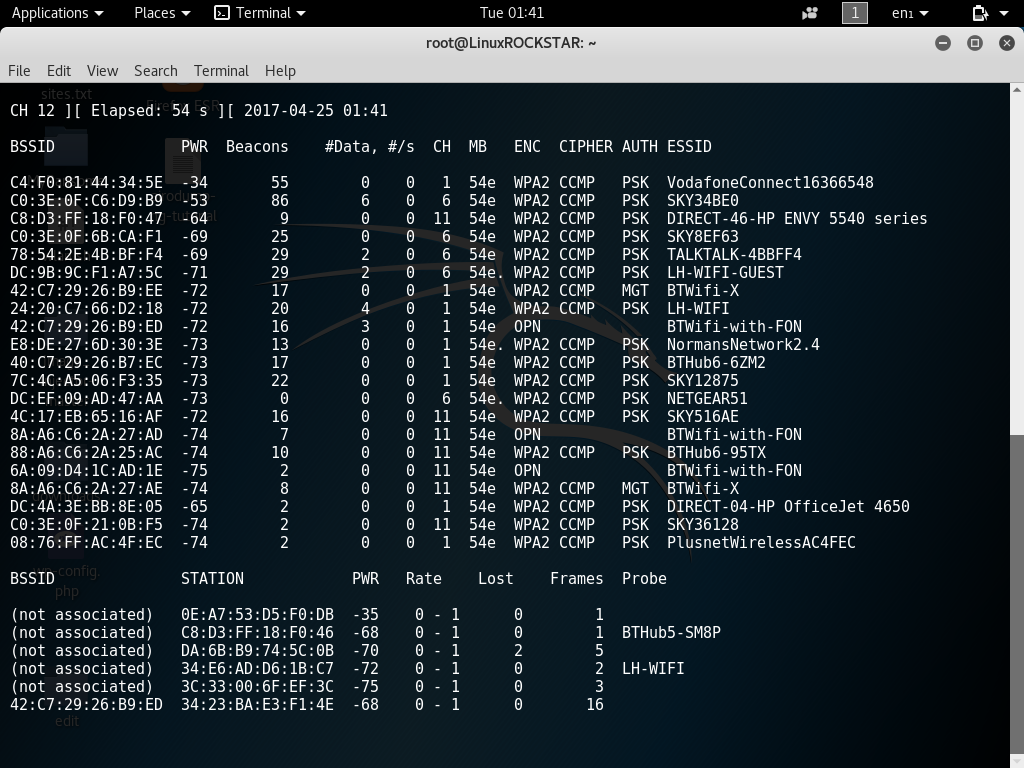
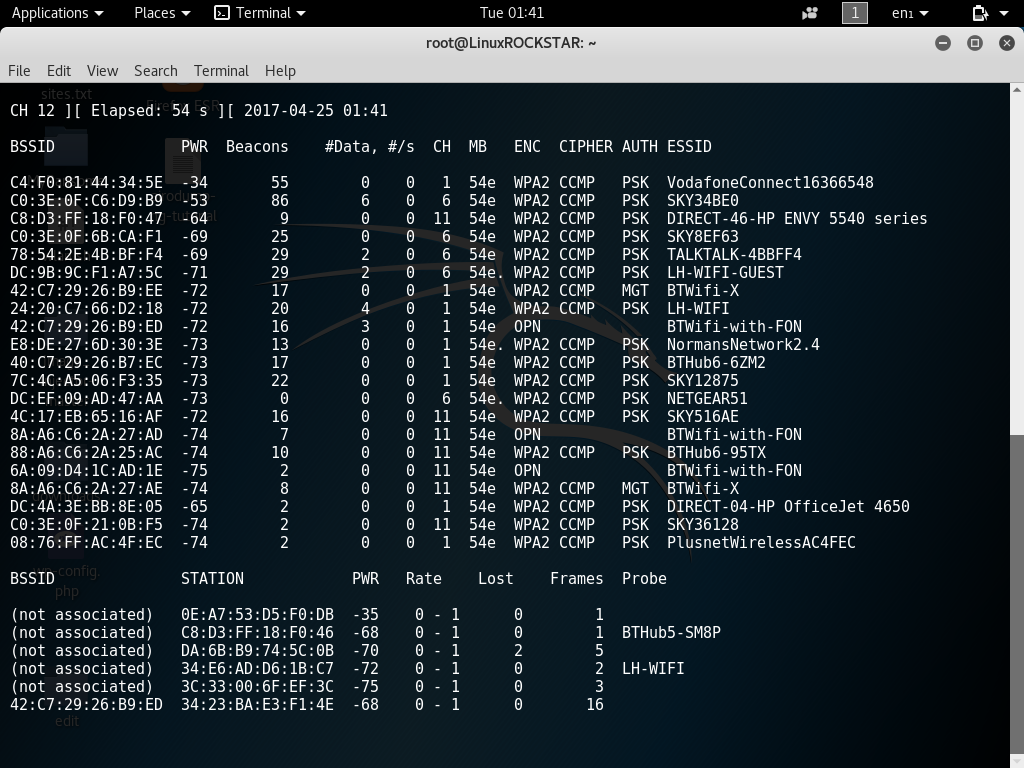
409Scanning For Wireless Access Point Information Using Airodump-ng Kali Linux Tutorial
Hi welcome back today in this tutorial you will learn how to scan for various wireless network information using airodump-ng. This information...
-

 210
210Generate-Macro – Powershell Script To Generate a Malicious Microsoft Office document with a Specified Payload and Persistence Method
Credits Matt Nelson (enigma0x3) – Coded by Matt Nelson (@enigma0x3) DOWNLOAD GENERATE-MACRO https://github.com/enigma0x3/Generate-Macro This Powershell script will generate a malicious Microsoft Office...
-
 317
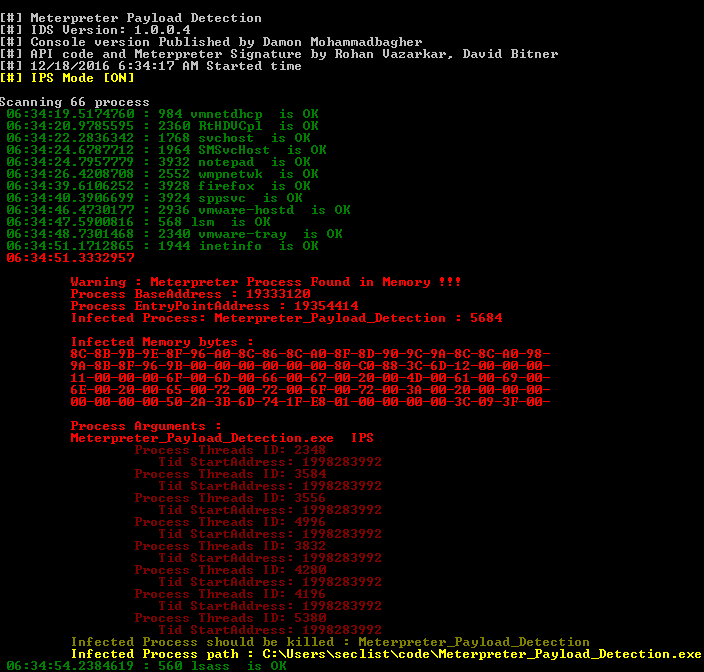
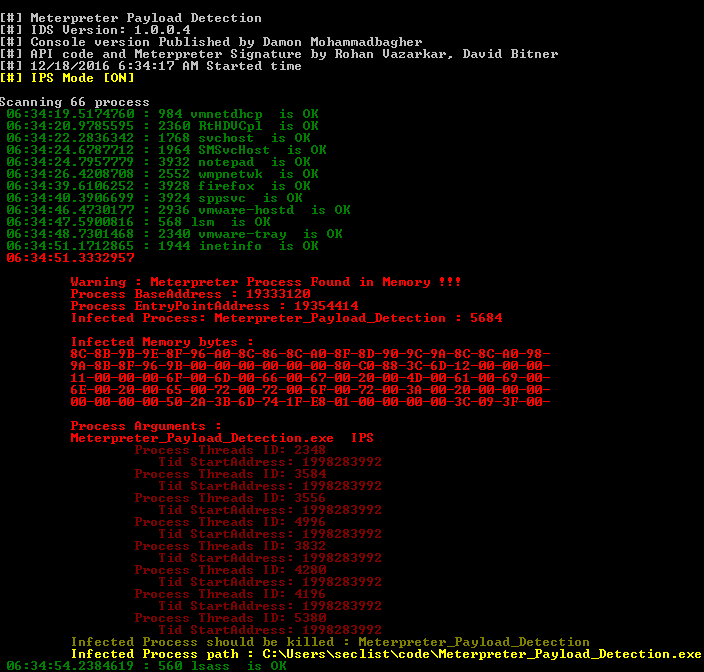
317Meterpreter Payload Detection – Tool for detecting Meterpreter in memory like IPS-IDS and Forensics tool
Meterpreter_Payload_Detection.exe tool for detecting Meterpreter in memory like IPS-IDS and Forensics tool DOWNLOAD Meterpreter_Payload_Detection https://github.com/DamonMohammadbagher/Meterpreter_Payload_Detection CREDITS: DamonMohammadbagher Install Notes Download Meterpreter_Payload_Detection Compile...
-
 161
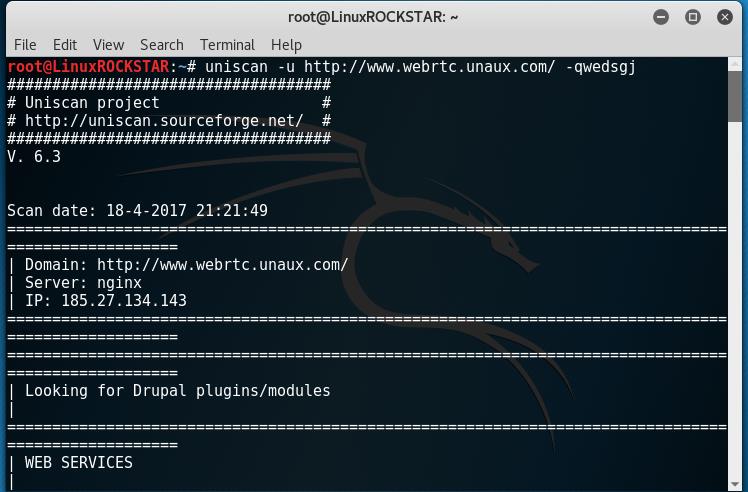
161Scan website for vulnerabilities with Uniscan Kali Linux Tutorial
Welcome back, in this tutorial you will learn how to scan and fingerprint a web server or device to find vulnerabilities. To...
-
 220
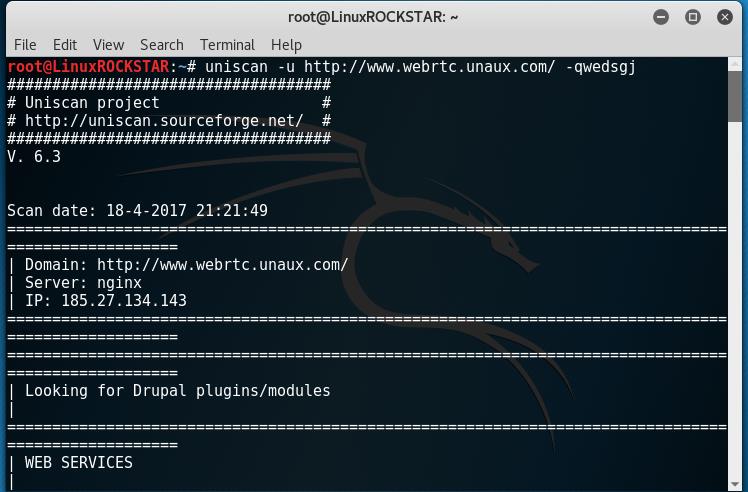
220WebRTC can leak your IP address even if your behind a VPN Part 2 (Proof of Concept)
Welcome back in the last article (WebRTC can leak your IP address even if your behind a VPN). we talked a little about...
-
 189
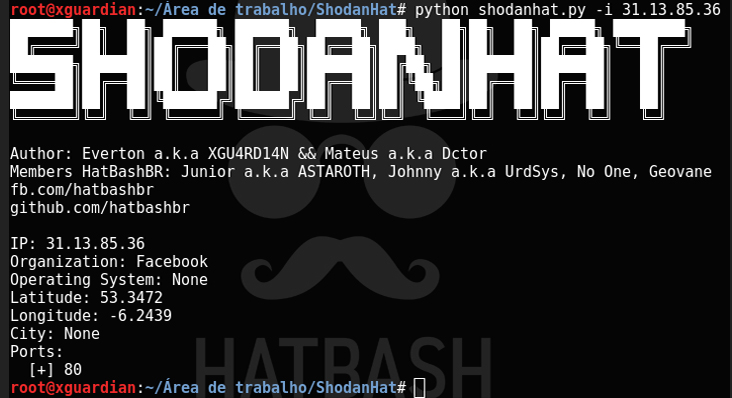
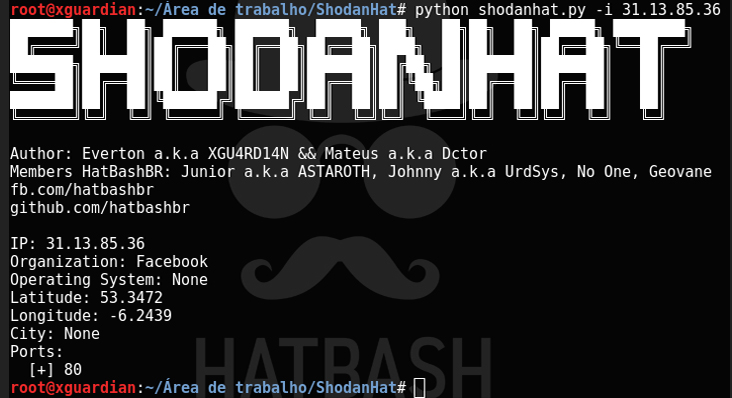
189ShodanHat – Search for hosts info with Shodan
DOWNLOAD SHODANHAT https://github.com/HatBashBR/ShodanHat Credits: HatBashBR Dependencies You need to install shodan with pip install shodan or easy_install shodan. You need to install...
-

 111
111Gattacker – A Node.js package for BLE (Bluetooth Low Energy) security assessment
A Node.js package for BLE (Bluetooth Low Energy) security assessment using Man-in-the-Middle and other attacks DOWNLOAD GATTACK http://www.gattack.io Install npm install gattacker...
-
 207
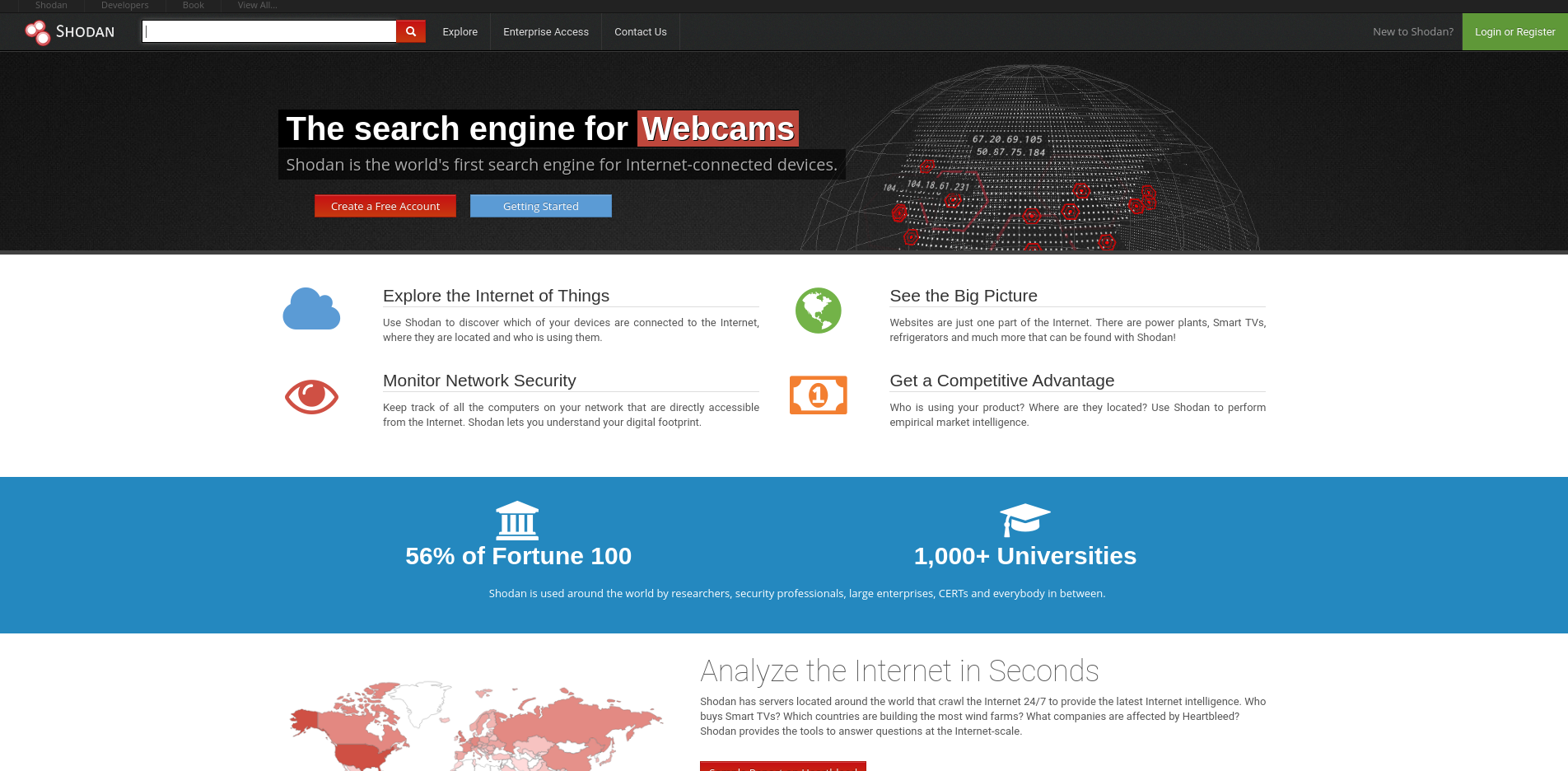
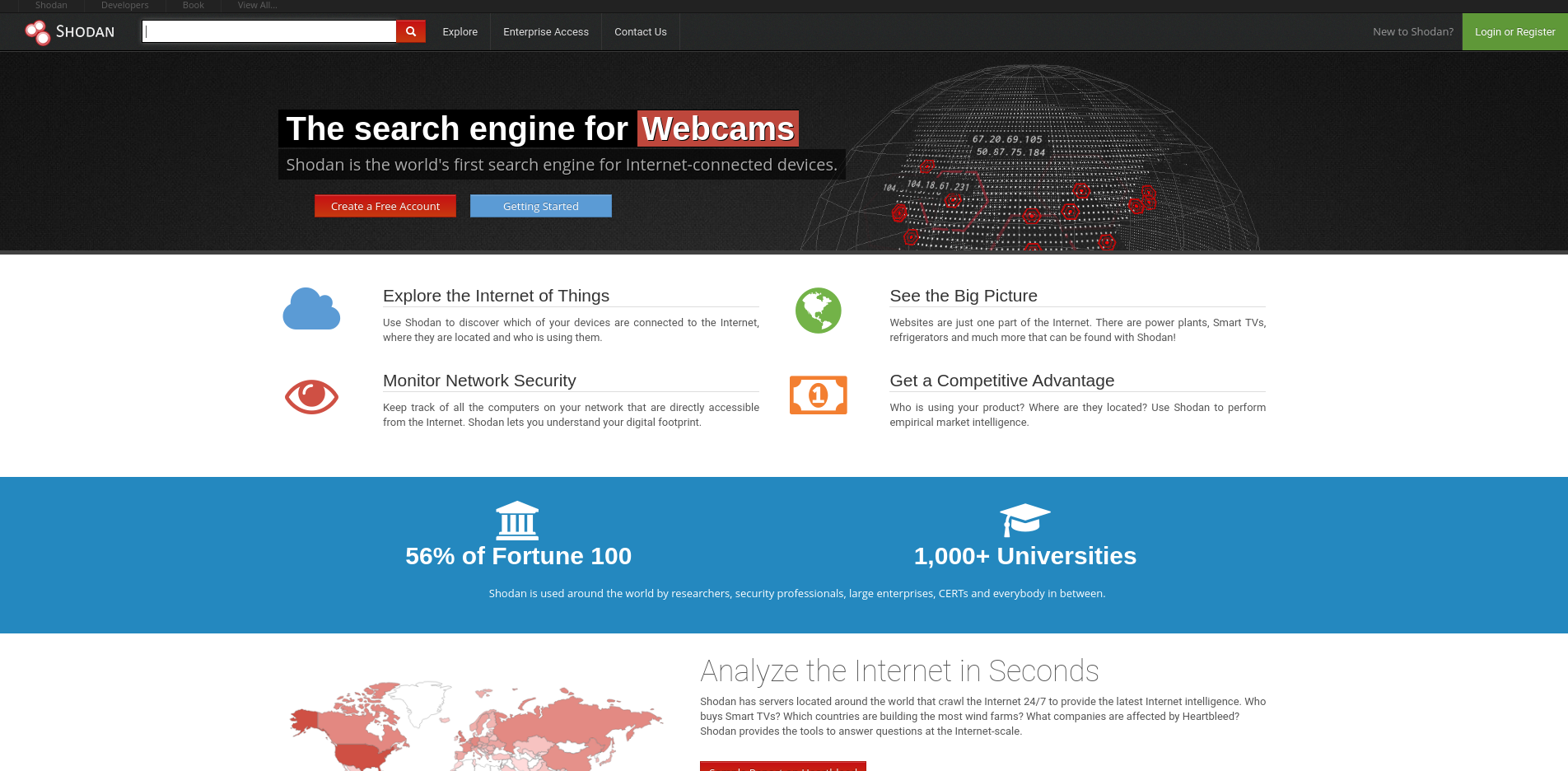
207Shodan – world’s first search engine for Internet connected devices
Shodan is the world’s first search engine for Internet-connected devices. Shodan is a search engine that lets the user find specific types...
-
 123
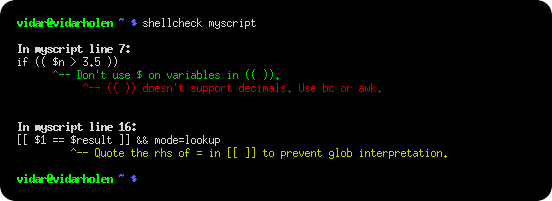
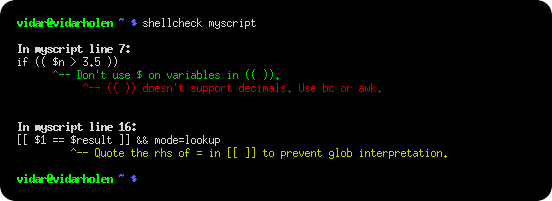
123ShellCheck – A shell script static analysis tool
DOWNLOAD SHELLCHECK https://github.com/koalaman/shellcheck ShellCheck is a GPLv3 tool that gives warnings and suggestions for bash/sh shell scripts. The goals of ShellCheck are...
-
 135
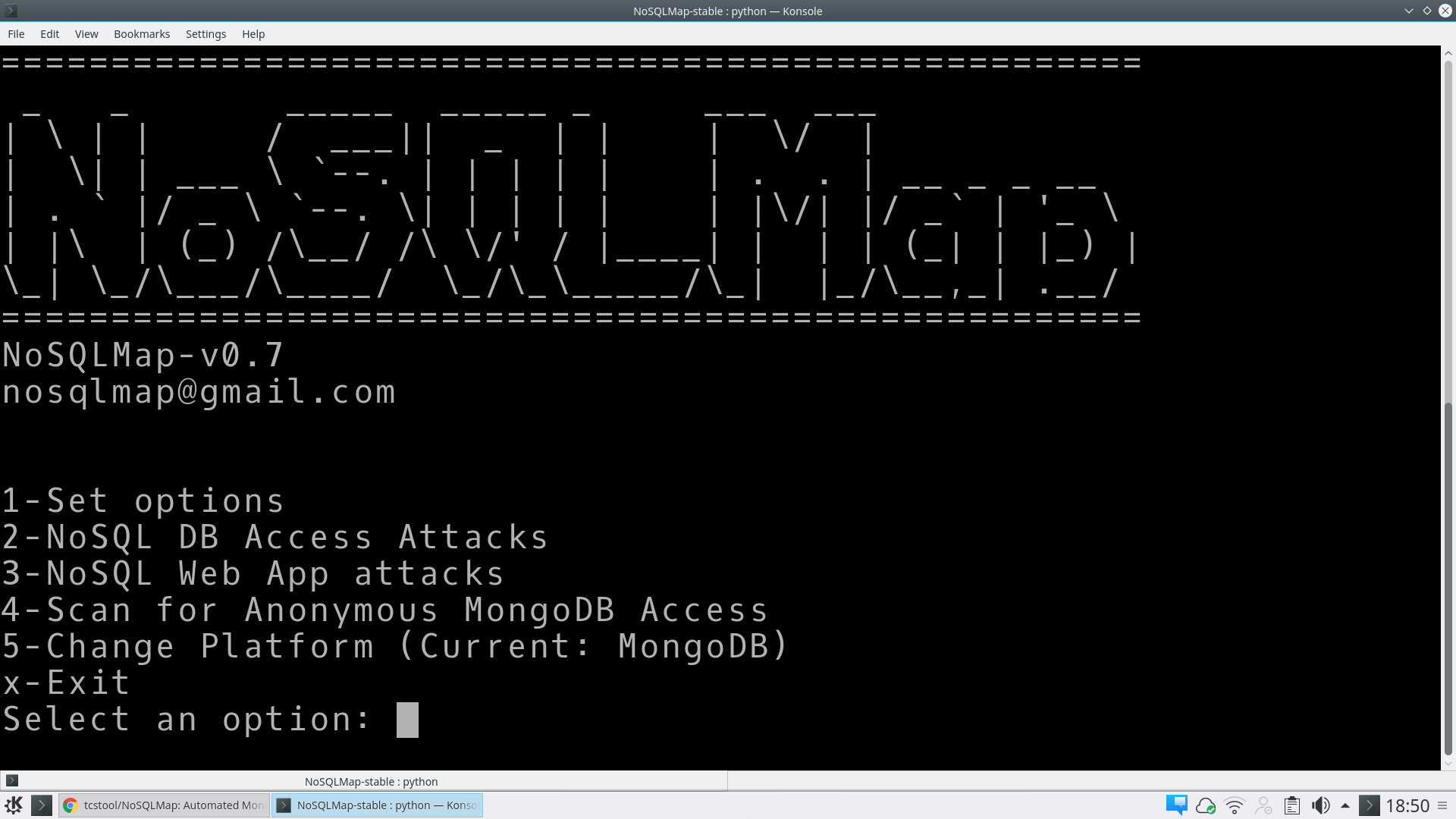
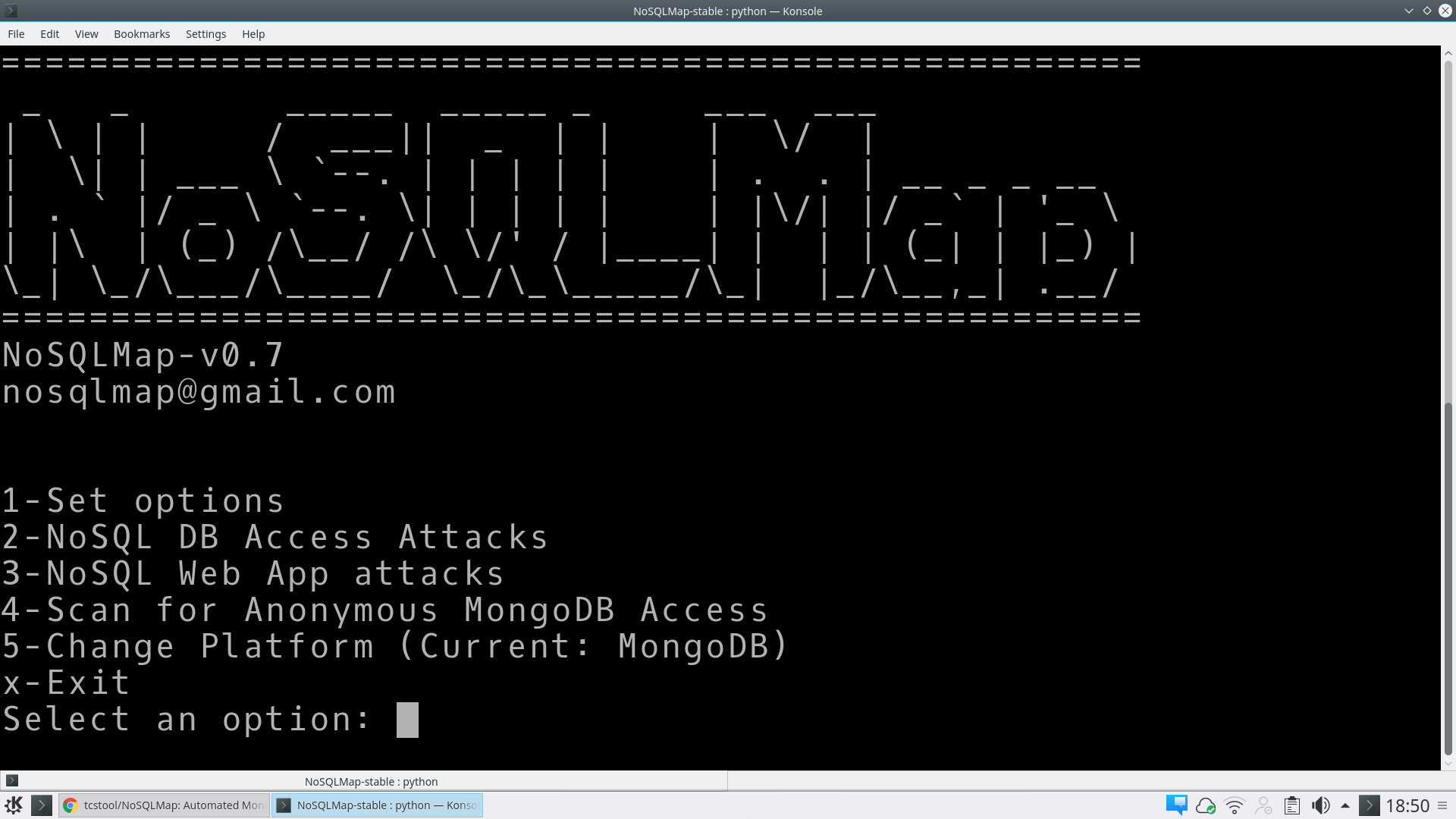
135NoSQLMap – Automated Mongo database and NoSQL web application exploitation tool
Automated Mongo database and NoSQL web application exploitation tool http://www.nosqlmap.net DOWNLOAD NOSQL https://github.com/tcstool/NoSQLMap NoSQLMap NoSQLMap v0.7 Introduction NoSQLMap is an open source...
-

 195
195SQLMap Tutorial SQL Injection to hack a website and database in Kali Linux
Hi, today I will demonstrate how an attacker would target and compromise a MySQL database using SQL Injection attacks. SQL Injection attacks...
-

 212
212Google Dorks for SQL Injection 2017 – HackingVision
Google Dorks for SQL Injection Google Dorks, Google Dorks List, Find SQL Injectable Websites, Hack Websites using Google Dorks, Google Dorks List...
-

 109
109Hacking WordPress Website with Malicious Plug-in
Welcome back today we will talk about how we could compromise a WordPress website for a reverse meterpreter shell though use of...
-

 89
89Proctal – Tool that Manipulates Address Space PID
Proctal 0.0.0 Proctal provides a command line interface and a C library to manipulate the address space of a running program on...






