Hackers Repository
-
How to inbox Facebook users from anyone’s account
Facebook hacking has been a major “topic” for the curious user,but today i’ll be focusing on an easy trick to send messages...
-
 221
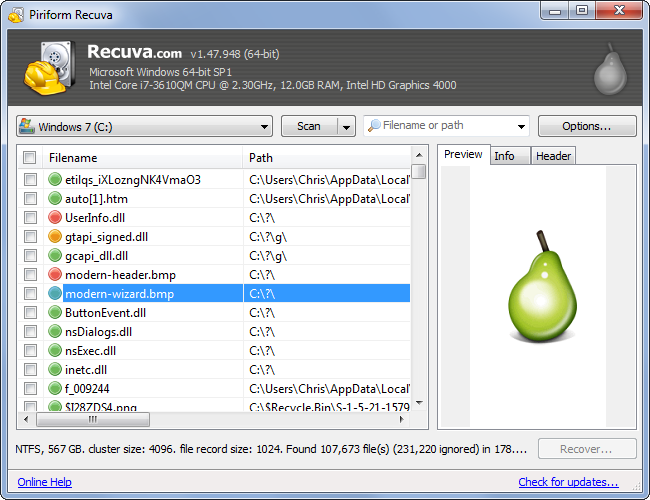
221Recovering your Deleted Files
It has happened to most of us. You deleted a file and realize you need it back. But is it really deleted?...
-
 160
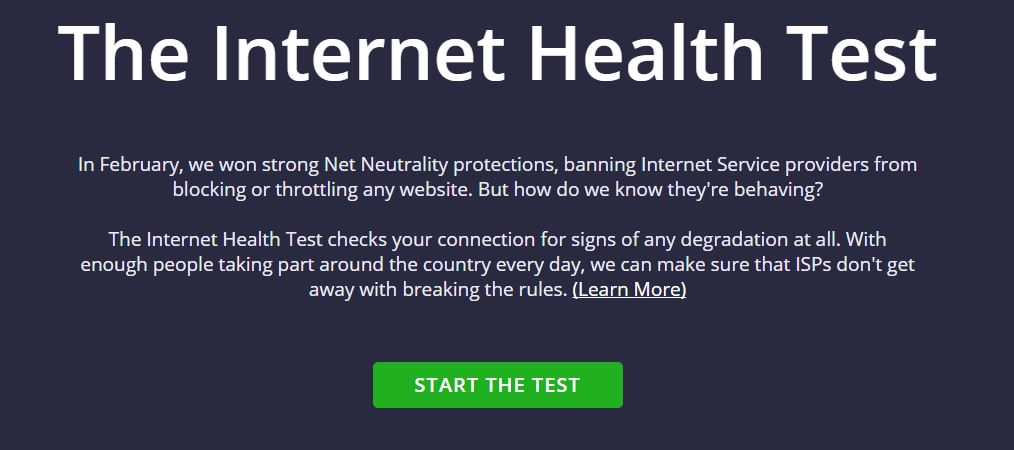
160How to check whether your ISP is Throttling your Internet speeds.
You, the usual and the average consumer, doesn’t know the boundaries that define the exploitation when it comes to the net neutrality...
-
 314
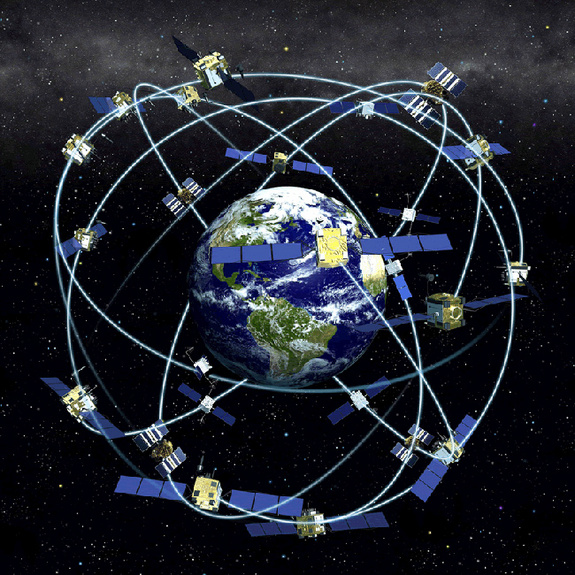
314Satellite & GPS Hacking
A satellite is a moon, planet or machine that orbits a planet or a star. Earth is a satellite because it orbits...
-

 283
283How to detect SQL Injection attacks
SQL Injection (SQLi) attacks have been around for over a decade. You might wonder why they are still so prevalent. The main...
-
Penetration Testing Procedures
Penetration testing (otherwise known as pentesting, or the more general security testing) is the process of testing your applications for vulnerabilities, and...
-
 158
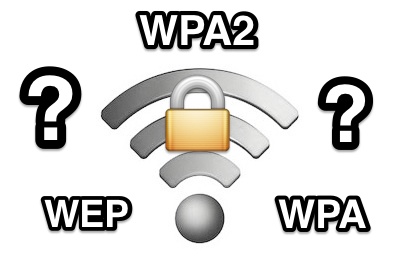
1586 Ways to Secure a Wireless Wi-Fi Network
Wireless Networking (Wi-Fi) has made it so easy for anyone to use Internet on your computer, mobile phones, tablets and other wireless...
-

 187
187Install Windows in 15 minutes
We do have to spend so much time when formatting PC. We are obliged because of windows installation speed. But using simple...
-

 210
210How to Delete yourself from the Internet
Have you ever wondered what information web pages have on you? Just perform a simple google search and check out the results! You...
-

 209
209Live Stream Twitch in VLC to avoid buffering
Twitch has been making some very awful encoding and additional bad choices for streamers and viewers of Twitch.tv. This method has been...
-

 230
230Bypass Internet Censorship
Internet censorship is the control or suppression of what can be accessed, published, or viewed on the Internet. It may be carried...
-
 216
216Simple Brute Force Method
Brute Forcing is simply testing a list of passwords to a list of usernames and hopefully you will have matched a username...
-
 266
266DNS Spoofing – Hacking Technique
This tutorial was meant to inform the community of a modern technique countless hackers are using to harm innocent people. This tutorial...
-

 213
213How to protect yourself against Phishing
Phishing is the method of stealing login info(usernames and passwords) by directing the victim to a clone(fake) login page, that logs the...
-
 159
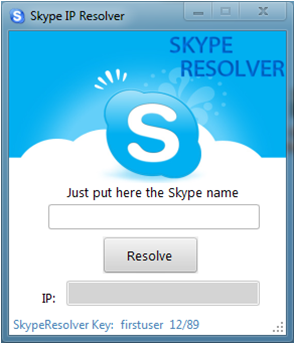
159Reverse Skype Resolver (How-to)
A Resolver will “lookup” a username on a VPS hosting the hacked skype, which allows the skype to pull data from the...
-

 257
257Cyborg Hawk Linux is ready to take on Kali ?
Today I will be reviewing Cyborg Hawk Linux, the distro is based on Ubuntu and designed to be a penetration testing platform The download...
-
How to create a keylogger in notepad
Here is a basic keylogger script for beginners to understand the basics of how keylogging works in notepad. This script should be...
-
 220
220How to find out if you’ve been HACKED with CMD
There are numerous methods to see if you have been hacked. Using the Command Prompt, you can run a command which will...
-

 284
284TOP 100 Unique sites
These sites solve at least one problem really well and they all have simple web addresses(URLs) that you can easily memorize thus...
-

 235
235How to Check If A Used iPhone Is Stolen
Apple attempted to address this issue with the Find My iPhone service in 2010, but that could be defeated by turning the...
-

 216
216Reveal Asterix Symbols with Javascript
How to do it 1) Open the Login Page of any website. E.g http://www.gmail.com 2) Type your ‘Username’ and ‘Password’. (DONT CLICK...






