Malware
-

 2.6K
2.6KSecuriDropper: New Android Dropper-as-a-Service Bypasses Google’s Defenses
Cybersecurity researchers have shed light on a new dropper-as-a-service (DaaS) for Android called SecuriDropper that bypasses new security restrictions imposed by Google...
-

 4.5K
4.5KGoogle Warns How Hackers Could Abuse Calendar Service as a Covert C2 Channel
Google is warning of multiple threat actors sharing a public proof-of-concept (PoC) exploit that leverages its Calendar service to host command-and-control (C2)...
-
 3.3K
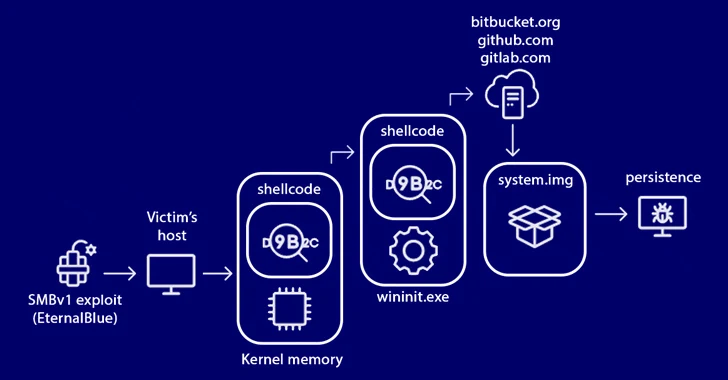
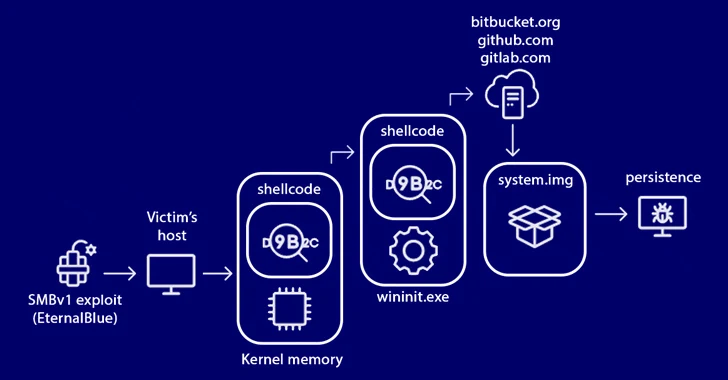
3.3KStripedFly Malware Operated Unnoticed for 5 Years, Infecting 1 Million Devices
An advanced strain of malware masquerading as a cryptocurrency miner has managed to fly the radar for over five years, infecting no...
-

 2.1K
2.1KNodeStealer Malware Hijacking Facebook Business Accounts for Malicious Ads
Compromised Facebook business accounts are being used to run bogus ads that employ “revealing photos of young women” as lures to trick...
-
 4.5K
4.5KResearchers Find 34 Windows Drivers Vulnerable to Full Device Takeover
As many as 34 unique vulnerable Windows Driver Model (WDM) and Windows Driver Frameworks (WDF) drivers could be exploited by non-privileged threat...
-

 4.2K
4.2KNorth Korean Hackers Targeting Crypto Experts with KANDYKORN macOS Malware
State-sponsored threat actors from the Democratic People’s Republic of Korea (DPRK) have been found targeting blockchain engineers of an unnamed crypto exchange...
-

 2.1K
2.1KTurla Updates Kazuar Backdoor with Advanced Anti-Analysis to Evade Detection
The Russia-linked hacking crew known as Turla has been observed using an updated version of a known second-stage backdoor referred to as...
-
 1.4K
1.4KMalicious NuGet Packages Caught Distributing SeroXen RAT Malware
Cybersecurity researchers have uncovered a new set of malicious packages published to the NuGet package manager using a lesser-known method for malware...
-
 1.5K
1.5KPro-Hamas Hacktivists Targeting Israeli Entities with Wiper Malware
A pro-Hamas hacktivist group has been observed using a new Linux-based wiper malware dubbed BiBi-Linux Wiper, targeting Israeli entities amidst the ongoing...
-

 960
960N. Korean Lazarus Group Targets Software Vendor Using Known Flaws
The North Korea-aligned Lazarus Group has been attributed as behind a new campaign in which an unnamed software vendor was compromised through...
-

 2.6K
2.6KiLeakage: New Safari Exploit Impacts Apple iPhones and Macs with A- and M-Series CPUs
A group of academics has devised a novel side-channel attack dubbed iLeakage that exploits a weakness in the A- and M-series CPUs...
-
 901
901Critical Flaw in NextGen’s Mirth Connect Could Expose Healthcare Data
Users of Mirth Connect, an open-source data integration platform from NextGen HealthCare, are being urged to update to the latest version following...
-
 4.5K
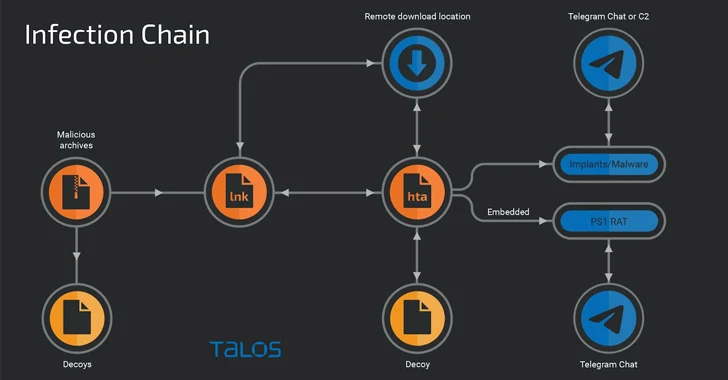
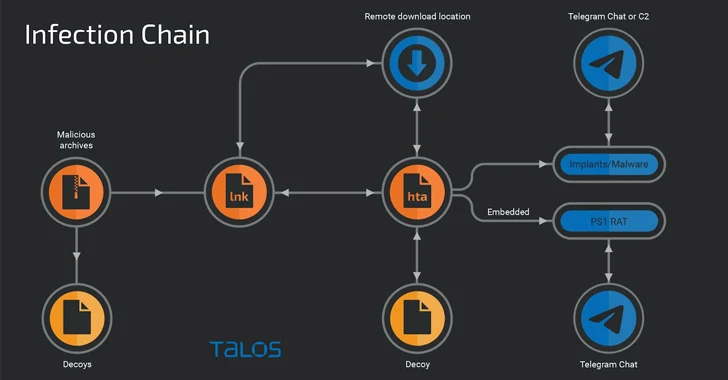
4.5KYoroTrooper: Researchers Warn of Kazakhstan’s Stealthy Cyber Espionage Group
A relatively new threat actor known as YoroTrooper is likely made up of operators originating from Kazakhstan. The assessment, which comes from...
-

 2.5K
2.5KMalvertising Campaign Targets Brazil’s PIX Payment System with GoPIX Malware
The popularity of Brazil’s PIX instant payment system has made it a lucrative target for threat actors looking to generate illicit profits...
-

 2.6K
2.6KDoNot Team’s New Firebird Backdoor Hits Pakistan and Afghanistan
The threat actor known as DoNot Team has been linked to the use of a novel .NET-based backdoor called Firebird targeting a...
-

 1.1K
1.1KQuasar RAT Leverages DLL Side-Loading to Fly Under the Radar
The open-source remote access trojan known as Quasar RAT has been observed leveraging DLL side-loading to fly under the radar and stealthily...
-
 3.0K
3.0KEuropol Dismantles Ragnar Locker Ransomware Infrastructure, Nabs Key Developer
Europol on Friday announced the takedown of the infrastructure associated with Ragnar Locker ransomware, alongside the arrest of a “key target” in...
-

 2.6K
2.6KVietnamese Hackers Target U.K., U.S., and India with DarkGate Malware
Attacks leveraging the DarkGate commodity malware targeting entities in the U.K., the U.S., and India have been linked to Vietnamese actors associated...
-

 3.8K
3.8KLazarus Group Targeting Defense Experts with Fake Interviews via Trojanized VNC Apps
The North Korea-linked Lazarus Group (aka Hidden Cobra or TEMP.Hermit) has been observed using trojanized versions of Virtual Network Computing (VNC) apps...
-

 1.4K
1.4KQubitstrike Targets Jupyter Notebooks with Crypto Mining and Rootkit Campaign
A threat actor, presumably from Tunisia, has been linked to a new campaign targeting exposed Jupyter Notebooks in a two-fold attempt to...
-
 834
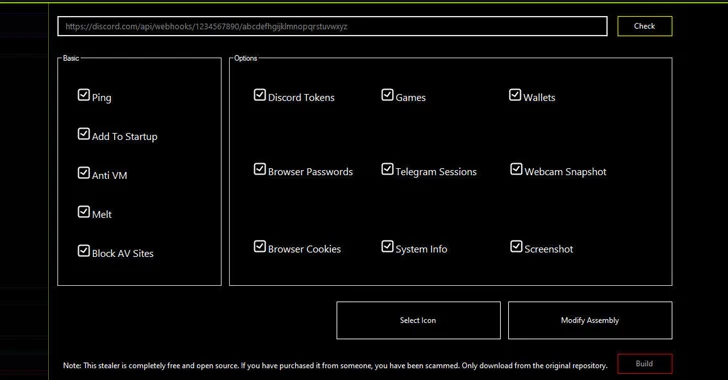
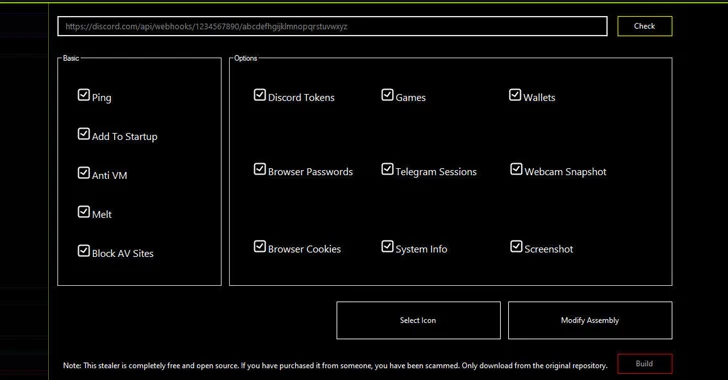
834Discord: A Playground for Nation-State Hackers Targeting Critical Infrastructure
In what’s the latest evolution of threat actors abusing legitimate infrastructure for nefarious ends, new findings show that nation-state hacking groups have...






