Malware
-
 1.4K
1.4KHow hrserver.dll stealthy webshell can mimic Google’s Web Traffic to hide and compromise networks
In a striking revelation shaking the cybersecurity world, researchers have unearthed a sophisticated web shell, dubbed ‘HrServ,’ hidden within a seemingly innocuous...
-

 460
460Alert: New WailingCrab Malware Loader Spreading via Shipping-Themed Emails
Delivery- and shipping-themed email messages are being used to deliver a sophisticated malware loader known as WailingCrab. “The malware itself is split...
-
 4.9K
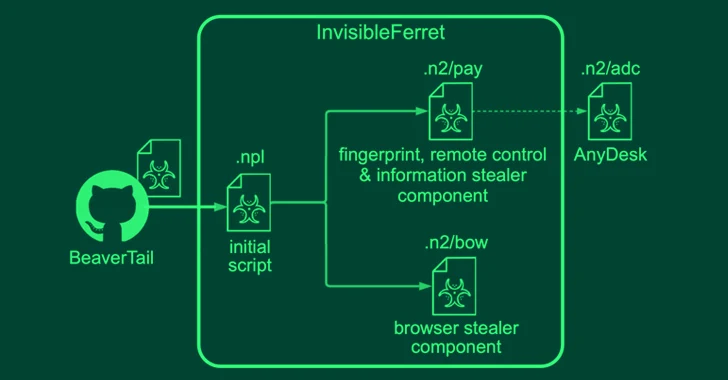
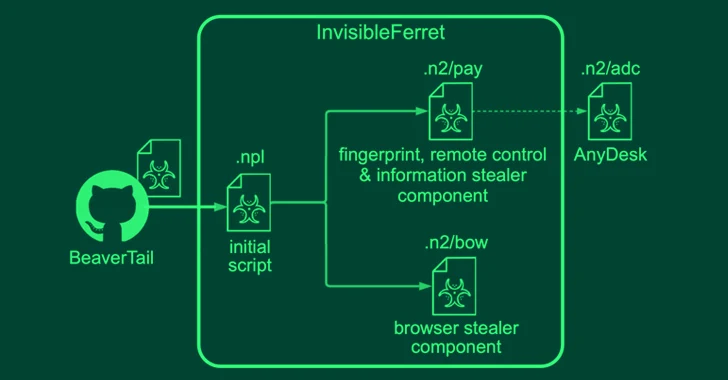
4.9KNorth Korean Hackers Pose as Job Recruiters and Seekers in Malware Campaigns
North Korean threat actors have been linked to two campaigns in which they masquerade as both job recruiters and seekers to distribute...
-
 4.0K
4.0KNew Agent Tesla Malware Variant Using ZPAQ Compression in Email Attacks
A new variant of the Agent Tesla malware has been observed delivered via a lure file with the ZPAQ compression format to...
-

 1.9K
1.9KHow Multi-Stage Phishing Attacks Exploit QRs, CAPTCHAs, and Steganography
Phishing attacks are steadily becoming more sophisticated, with cybercriminals investing in new ways of deceiving victims into revealing sensitive information or installing...
-

 3.1K
3.1KMalicious Apps Disguised as Banks and Government Agencies Targeting Indian Android Users
Android smartphone users in India are the target of a new malware campaign that employs social engineering lures to install fraudulent apps...
-
 3.0K
3.0KNetSupport RAT Infections on the Rise – Targeting Government and Business Sectors
Threat actors are targeting the education, government and business services sectors with a remote access trojan called NetSupport RAT. “The delivery mechanisms...
-

 2.6K
2.6KDarkGate and PikaBot Malware Resurrect QakBot’s Tactics in New Phishing Attacks
Phishing campaigns delivering malware families such as DarkGate and PikaBot are following the same tactics previously used in attacks leveraging the now-defunct...
-

 3.8K
3.8KLummaC2 Malware Deploys New Trigonometry-Based Anti-Sandbox Technique
The stealer malware known as LummaC2 (aka Lumma Stealer) now features a new anti-sandbox technique that leverages the mathematical principle of trigonometry...
-

 2.9K
2.9K8Base Group Deploying New Phobos Ransomware Variant via SmokeLoader
The threat actors behind the 8Base ransomware are leveraging a variant of the Phobos ransomware to conduct their financially motivated attacks. The...
-
 3.6K
3.6KBeware: Malicious Google Ads Trick WinSCP Users into Installing Malware
Threat actors are leveraging manipulated search results and bogus Google ads that trick users who are looking to download legitimate software such...
-

 1.7K
1.7K27 Malicious PyPI Packages with Thousands of Downloads Found Targeting IT Experts
An unknown threat actor has been observed publishing typosquat packages to the Python Package Index (PyPI) repository for nearly six months with...
-

 1.1K
1.1KCISA and FBI Issue Warning About Rhysida Ransomware Double Extortion Attacks
The threat actors behind the Rhysida ransomware engage in opportunistic attacks targeting organizations spanning various industry sectors. The advisory comes courtesy of...
-

 1.4K
1.4KU.S. Takes Down IPStorm Botnet, Russian-Moldovan Mastermind Pleads Guilty
The U.S. government on Tuesday announced the takedown of the IPStorm botnet proxy network and its infrastructure, as the Russian and Moldovan...
-

 1.2K
1.2KNew Campaign Targets Middle East Governments with IronWind Malware
Government entities in the Middle East are the target of new phishing campaigns that are designed to deliver a new initial access...
-

 3.0K
3.0KVietnamese Hackers Using New Delphi-Powered Malware to Target Indian Marketers
The Vietnamese threat actors behind the Ducktail stealer malware have been linked to a new campaign that ran between March and early...
-

 4.6K
4.6KNew Ransomware Group Emerges with Hive’s Source Code and Infrastructure
The threat actors behind a new ransomware group called Hunters International have acquired the source code and infrastructure from the now-dismantled Hive...
-

 2.7K
2.7KMicrosoft Warns of Fake Skills Assessment Portals Targeting IT Job Seekers
A sub-cluster within the infamous Lazarus Group has established new infrastructure that impersonates skills assessment portals as part of its social engineering...
-

 3.4K
3.4KRussian Hackers Sandworm Cause Power Outage in Ukraine Amidst Missile Strikes
The notorious Russian hackers known as Sandworm targeted an electrical substation in Ukraine last year, causing a brief power outage in October...
-
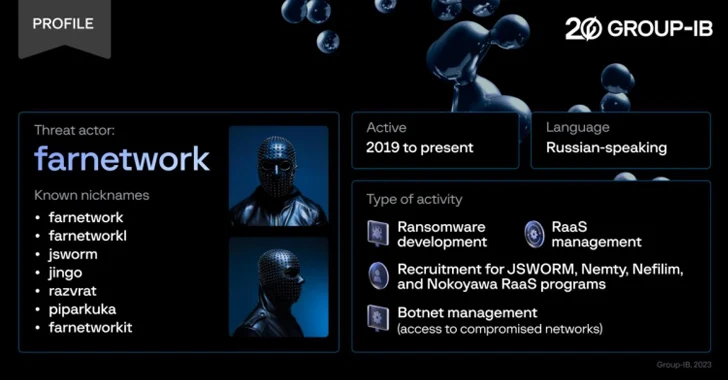
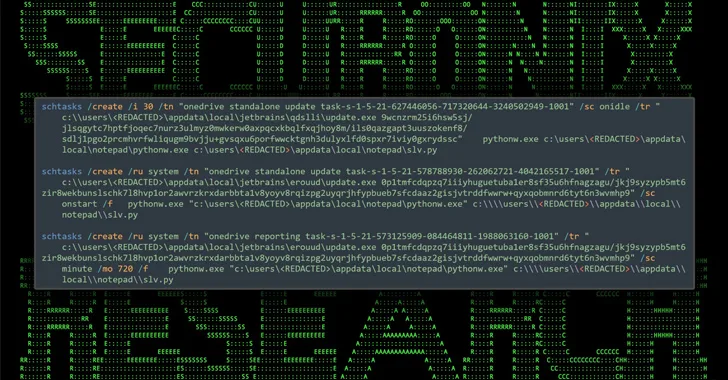
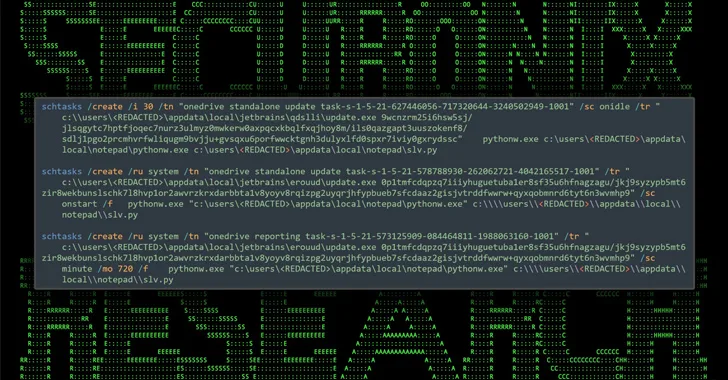
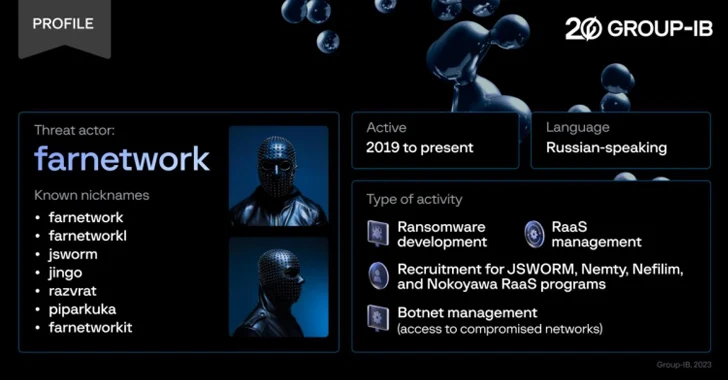 4.9K
4.9KExperts Expose Farnetwork’s Ransomware-as-a-Service Business Model
Cybersecurity researchers have unmasked a prolific threat actor known as farnetwork, who has been linked to five different ransomware-as-a-service (RaaS) programs over...
-

 1.1K
1.1KNew GootLoader Malware Variant Evades Detection and Spreads Rapidly
A new variant of the GootLoader malware called GootBot has been found to facilitate lateral movement on compromised systems and evade detection....






