Pentest
-
 220
220Bad Rabbit Ransomware Uses Leaked ‘EternalRomance’ NSA Exploit
A new widespread ransomware worm, known as “Bad Rabbit,” that hit over 200 major organisations, primarily in Russia and Ukraine this week...
-
Security Flaw in LG IoT Software Left Home Appliances Vulnerable
LG has updated its software after security researchers spotted a flaw that allowed them to gain control of devices like refrigerators, ovens,...
-
Google Play Protect System Failed To Succeed First Security Test
Google’s new Play Protect security system did not success first real-world tests, and the system was rated dead in an experiment conducted...
-
sqlmate – Tool Which Will Do What you Always Expected from SQLmap
There are some features that we think SQLMap should have. Like finding admin panel of the target, better hash cracking etc. If...
-
 203
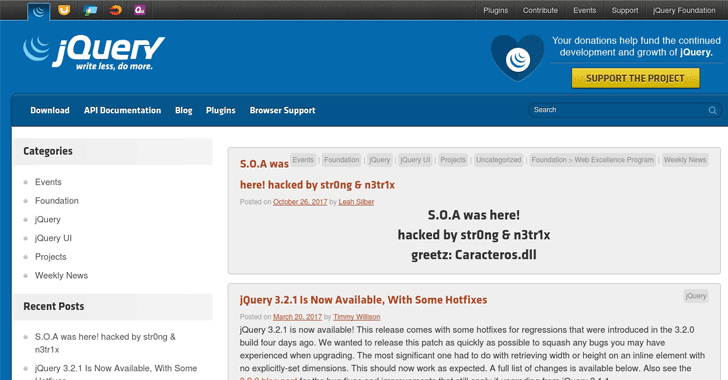
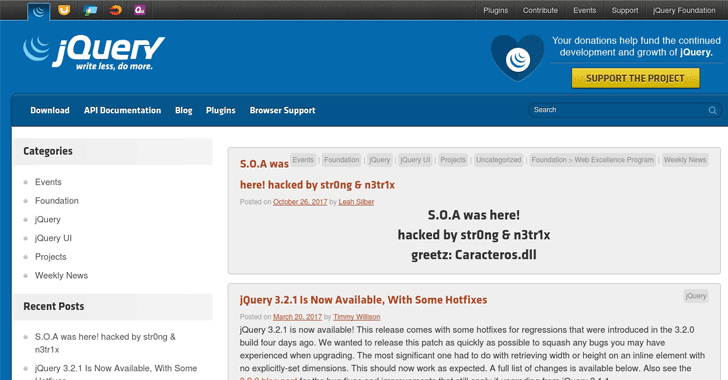
203jQuery hacked: Site was hit, but not the library
The official blog of jQuery—most popular JavaScript library used by millions of websites—has been hacked by some unknown hackers, using the pseudonym...
-

 195
195Ethereum phishing attack that earns $15K in two hours
Wesley Neelen (security researcher) has received a phishing email that seems to be from the legal online Ethereum wallet site Myetherwallet.com. Cybercriminals...
-
ZeroDoor – A Script Written Lazily For Generating Cross-Platform Backdoors
A script written lazily for generating reverse shell backdoors on the go whenever you need without any hassle for your daily penetration...
-

 216
216Reptile – LKM Linux Rootkit
Reptile is a LKM rootkit for evil purposes. If you are searching stuff only for study purposes, see the demonstration codes. Features...
-
Entire Europe is being affected by the BadRabbit Ransomware
According to various cybersecurity firms, the growing virus is dubbed “BadRabbit” and is a form of ransomware that bolts down machines and...
-
Pixel 2 XL Displays are burning up already
News reported the issue, revealing a picture of a Pixel 2 XL with some fierce image remembrance around the navigation bar. Shortly...
-

 237
237Intel and Lenovo are trying to build UAF and U2F authentication into their devices
81 percent of data breaks last year involved weak, default or stolen passwords, and phishing attacks have advanced 65 percent year-on-year. Protecting...
-
 246
246DUHK (Don’t Use Hard-coded Keys) Attack Recovers Encryption Keys & Reveals VPN Connections
DUHK (Don’t Use Hard-coded Keys) is a new crypto implementation attack that could enable attackers to obtain secret keys that secure VPN...
-
LeakManager – A Tool To Help You Manage Your Leaks
A Tool To Help You Manage Your Leaks Install sudo apt-get install mongodb-org screen pip3 install -r requeriments.txt Usage screen -S leakManager...
-

 212
212Four Darknet Markets Simultaneously Go Offline
In an astonishing hit to the Darknet, four of it’s most popular marketplaces all went down at the same time. Marketplaces involved...
-
OWASP ZAP 2.6.0 – Penetration Testing Tool for Testing Web Applications
The OWASP Zed Attack Proxy (ZAP) is one of the world’s most popular free security tools and is actively maintained by hundreds...
-

 188
188Russia Fights to Keep Founder of BTC-e from Extradition to United States
In a tale as old as time, the United States and Russia are at it again. Alexander Vinnik, the founder of a...
-
Exploit Pack – Penetration Testing Framework
Exploit Pack has been designed by an experienced team of software developers and exploit writers to automate processes so penetration testers can...
-
srum-dump – A Forensics Tool to Convert the Data in the Windows srum
srum-dump This program will create an excel spreadsheet containing forensics artifacts contained the SRUM (System Resource Utilization Manager) database. The program can...
-
DNS over TLS is being developed for the next Android Update
DNS over TLS is a protocol where DNS inquiries will be encrypted to the equivalent level as HTTPS and therefore a DNS...
-
The Value of Bitcoin has surpassed $6000 for the first time
The cryptocurrency hit an all-time high of $6,147.07 just a time after forcing through the $6,000 mark, according to data from application...
-
 200
200Machine Learning Software created by Google is replicating itself
Now, Google has declared that AutoML has defeated the human AI engineers at their own game by setting machine-learning software that’s more...






