Pentest
-
 225
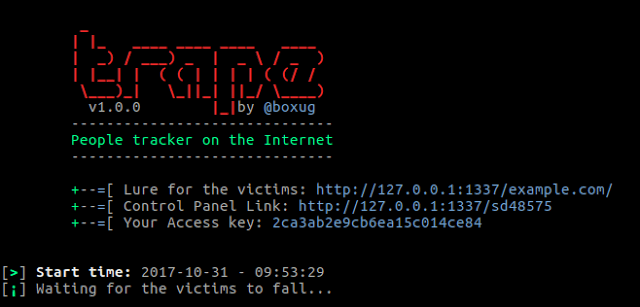
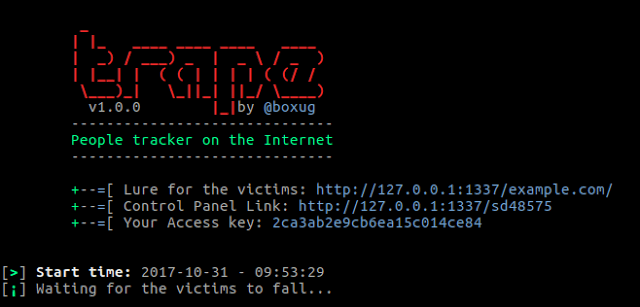
225Trape – People tracker on the Internet (The evolution of phishing attacks) OSINT
Trape is a recognition tool that allows you to track people, the information you can get is very detailed. We want to...
-

 195
195Donald Trump’s Twitter account has been deactivated by a Twitter employee
A rogue Twitter employee deactivated President Trump’s personal Twitter account (@realdonaldtrump) on his last day as a customer support rep for the...
-

 280
280Apple iPhone X is Providing Developers access to Facial Data
Apple’s privacy signs do not spread to the thousands of app developers who will gain access to facial data in order to...
-

 239
239Hackers are using Google search results to spread banking Trojan
Cybercriminals decided to use the Search Engine Optimization (SEO) to make their malicious links more widespread in the search results, allowing them...
-
 236
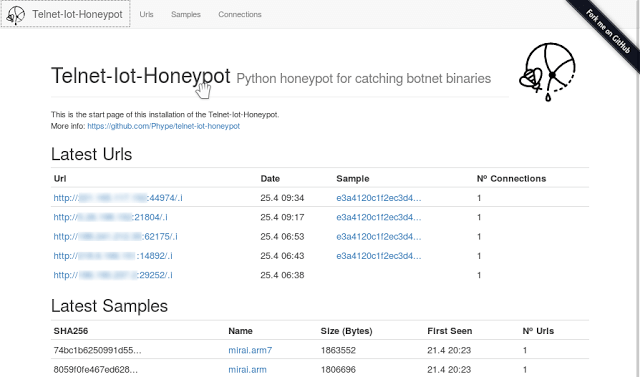
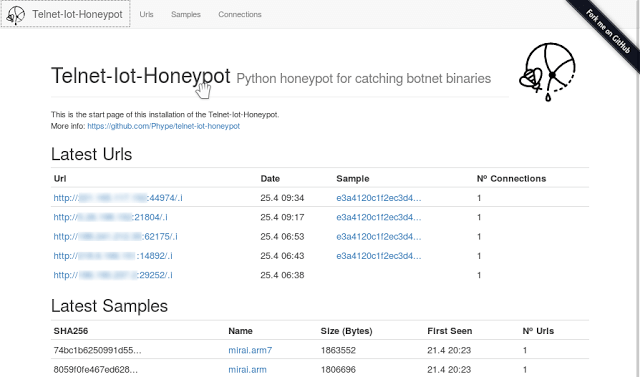
236Telnet IoT Honeypot – Python Telnet Honeypot For Catching Botnet Binaries
This project implements a python telnet server trying to act as a honeypot for IoT Malware which spreads over horribly insecure default...
-
 199
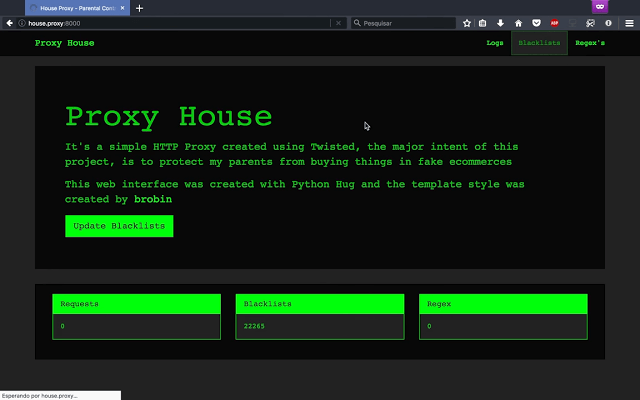
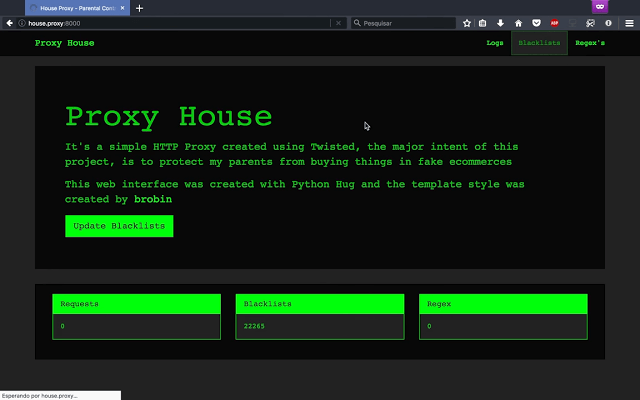
199HouseProxy – HTTP proxy focused on block phishing URL’s
Protect your parents from phishing, HTTP proxy focused on block phishing URL’s Install git clone https://github.com/mthbernardes/HouseProxy.git cd HouseProxy/ pip install -r requeriments.txt...
-
 176
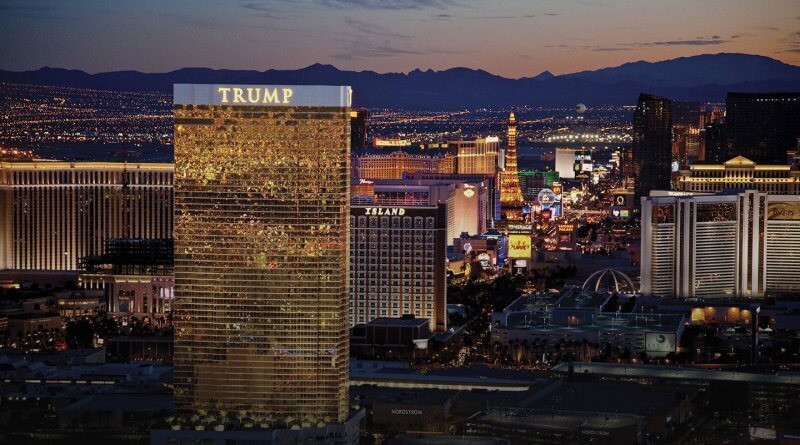
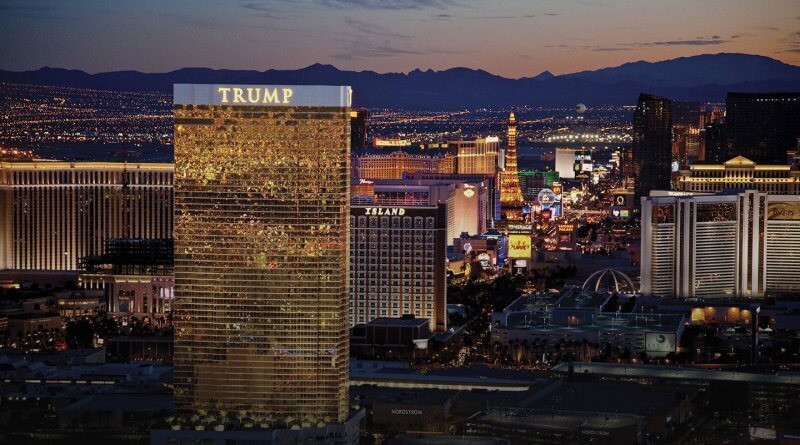
176Trump’s Organization got compromised by Hackers 4 years Ago
In 2013, Hackers apparently gained access to the Trump Organization’s domain booking account and created at least 250 website subdomains that cybersecurity...
-

 217
217CryptoShuffler malware made over $150,000 worth of Bitcoin
The CryptoShuffler malware has been discovered by security researchers from Kaspersky Lab, cybercriminals are using this malware to steal cryptocurrencies from the...
-
 252
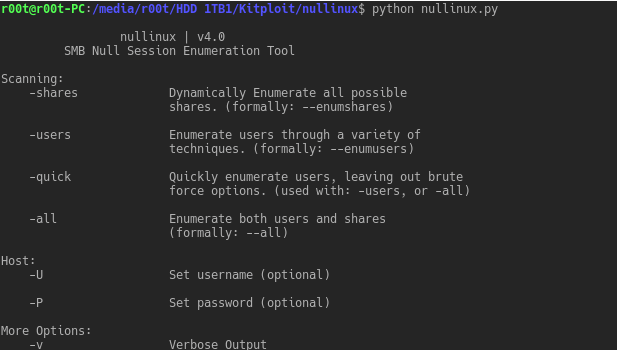
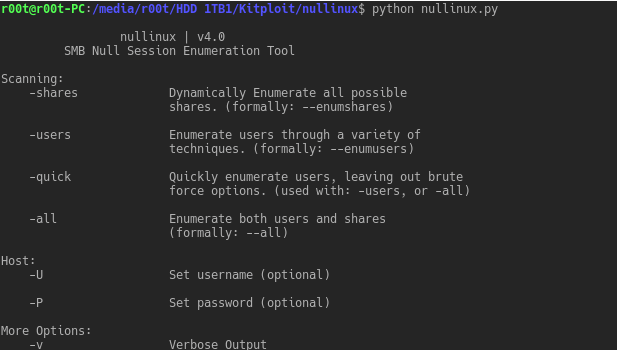
252nullinux – SMB null Session Identification and Enumeration Tool
nullinux is an internal penetration testing tool for Linux that can be used to enumerate OS information, domain information, shares, directories, and...
-

 146
146The Value of Bitcoin has surpassed $6,800
The cryptocurrency has had a bullish streak completely the week following the CME’s statement that it will introduce bitcoin expectations contracts. According to data...
-
 301
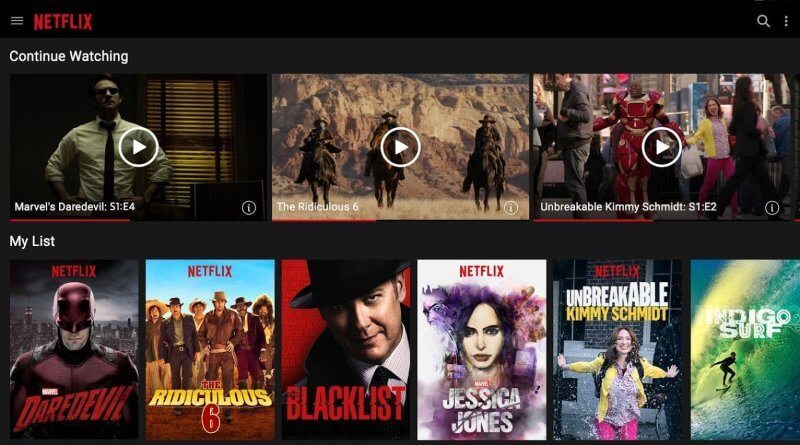
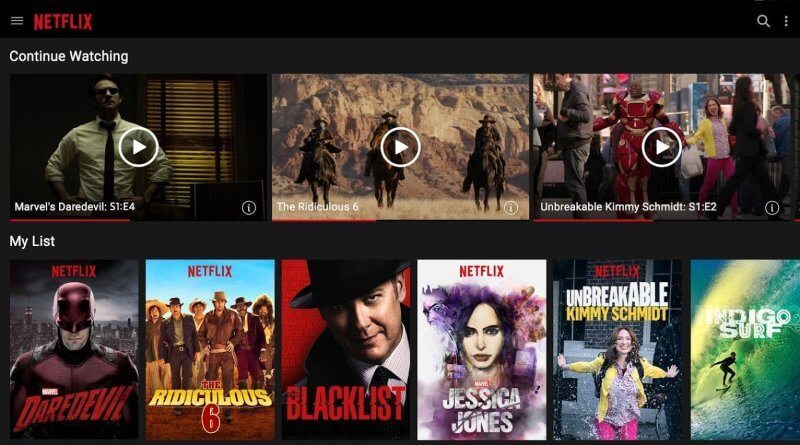
301Results Reveal that 74% of Customers will stop their Subscription if Netflix Shows Ads in their Platform
As we’ve seen, that’s been shifting. With a new game from companies like Hulu and Amazon, Netflix has seen running deals get...
-
 188
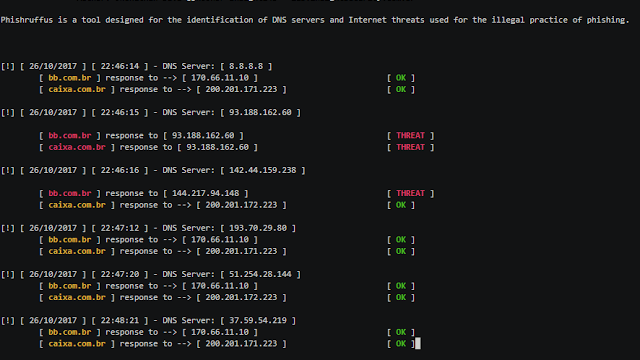
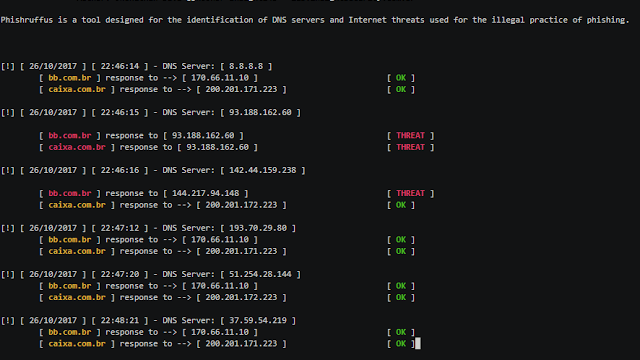
188Phishruffus – Intelligent Threat Hunter And Phishing Servers
Phishruffus is a tool designed to identify threats and malicious DNS servers on the Internet that are used for the illicit practice...
-

 157
157Apple has released Mac OS 10.13.1 that fixes WiFi KRACKS Vulnerability
Critically, both OS updates address the KRACK Wi-Fi vulnerability for any devices. It is a dangerous vulnerability in the WPA2 Wi-Fi assurance standard that allowed hostile...
-

 255
255Diamorphine – LKM Rootkit for Linux Kernels 2.6.x/3.x/4.x
Diamorphine is a LKM rootkit for Linux Kernels 2.6.x/3.x/4.x Features When loaded, the module starts invisible; Hide/unhide any process by sending a...
-
 220
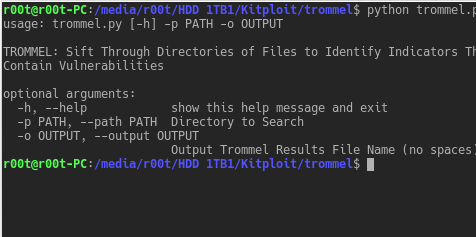
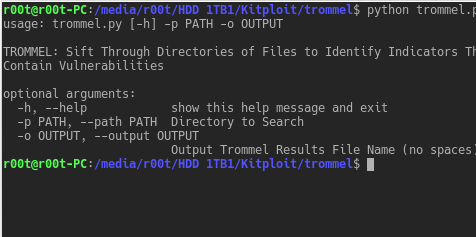
220TROMMEL – Sift Through Directories of Files to Identify Indicators That May Contain Vulnerabilities
TROMMEL sifts through directories of files to identify indicators that may contain vulnerabilities. TROMMEL identifies the following indicators related to: Secure Shell...
-
 169
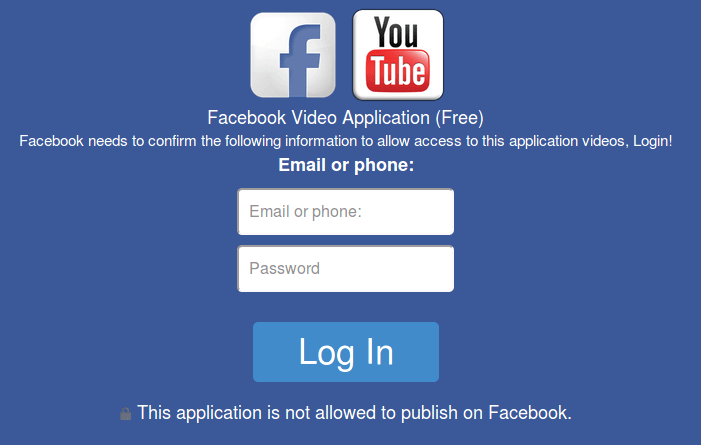
169A new Facebook phishing targeted iOS and Android users
A new Facebook spam campaign has been detected by F-Secure security researchers, the campaign attracting users to phishing pages that attempt to...
-

 206
206Number of Launches at SpaceX has doubled over the past year
SpaceX has begun, on average, about 1.5 times per period during this year. From that view, the company’s 16th launch of 2017...
-
 225
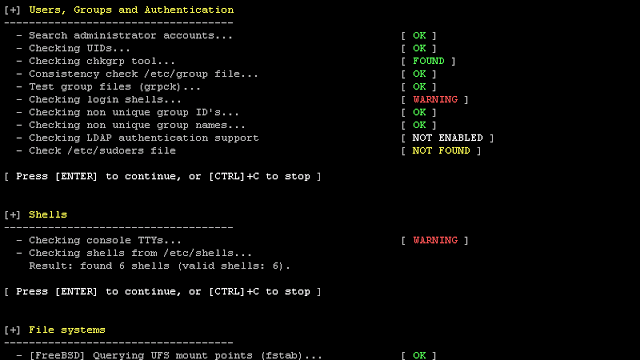
225Lynis 2.5.7 – Security Auditing Tool for Unix/Linux Systems
We are excited to announce this major release of auditing tool Lynis. Several big changes have been made to core functions of...
-

 191
191cve-search – Perform Local Searches For Known Vulnerabilities
cve-search is a tool to import CVE (Common Vulnerabilities and Exposures) and CPE (Common Platform Enumeration) into a MongoDB to facilitate search...
-
Websites need to ask permission to extract fingerprints from the user in Firefox 58
Canvas fingerprinting relies on websites meaning able to receive data from HTML canvas details calmly. In future, Firefox users will be required...
-
After Equifax Breach Woman’s ID got stolen for 15 Times
“I don’t remember if my data has been sold to the dark web or where this goes,” she said. “I keep getting...






