Pentest
-
 216
216Reddit’s Site’s ReDesign is going happen in Early 2018 Said by Steve Huffman
In January, Huffman published the plan. In July, Reddit grew $200 million at a cost of $1.8 billion to redesign its website....
-
 312
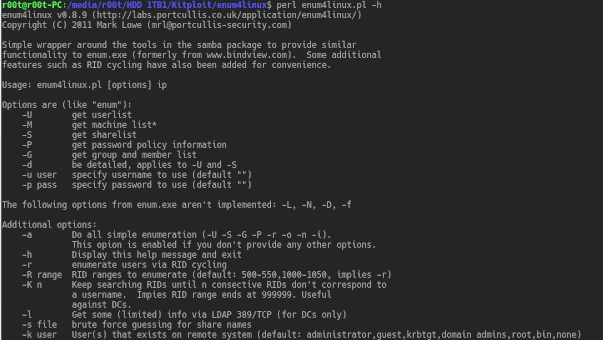
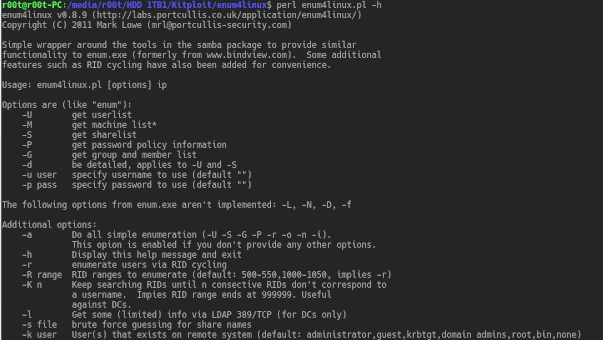
312enum4linux – Tool for Enumerating Information from Windows and Samba Systems
A Linux alternative to enum.exe for enumerating data from Windows and Samba hosts. Enum4linux is a tool for enumerating information from Windows...
-
 342
342WikiLeaks Publishes the Source Code and Development logs to Hive, a major component of the CIA infrastructure to Control its Malware
Today, 9 November 2017, WikiLeaks publishes the source code and development logs to Hive, a major component of the CIA infrastructure to...
-

 219
219Apple Claims that the Company has offered the FBI to help unlock the suspect’s iPhone
Turns out all they ought to do was ask Apple for help. In a comment the tech titan has issued to the...
-

 235
235Yahoo still don’t know How Three Billion Accounts were Hacked
When ironed about how Yahoo failed to realize that 3 billion accounts and not 500 million as first proclaimed were endangered in...
-
 246
246Parrot Security 3.9 – Security GNU/Linux Distribution Designed with Cloud Pentesting and IoT Security in Mind
Security GNU/Linux distribution designed with cloud pentesting and IoT security in mind. It includes a full portable laboratory for security and digital...
-

 195
195German Authorities Take Down Another Darknet Drug Dealer
A recent press release given by German police stated that they had made a substantial Darknet-related arrest after investigating a 43 year...
-

 304
304Google Play Store Security Breach: Fake WhatsApp Update
The Google Play store has made headlines recently when cyber criminals were able to hack in and post a fake WhatsApp messenger...
-

 240
240Parrot Security OS New Released with a Collection of tools for Penetration Testing and Forensic Analysis
Parrot Security Operating System is a Penetration Testing & Forensics Distro dedicated to Ethical Hackers & Cyber Security Professionals. With the new...
-

 154
154Comcast’s Internet Service is Down all over the US
Comcast verified the statements in a tweet on its customer care account. The outage seems to have begun around 1 PM ET....
-
 252
252Weird Bug prevents some iPhone users typing “I” and replacing it with the letter “A” with a symbol
A strange text error has left some iPhone users unable to write the letter “I”. But, every time they try to use...
-
 236
236CrunchRAT – HTTPS-based Remote Administration Tool (RAT)
CrunchRAT currently supports the following features: File upload File download Command execution It is currently single-threaded (only one task at a time),...
-
 306
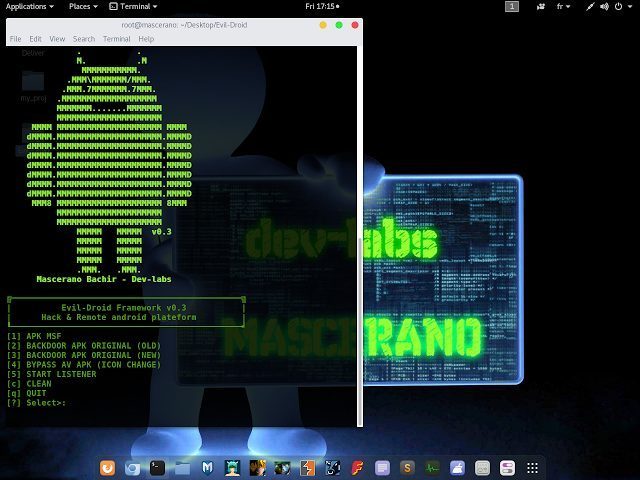
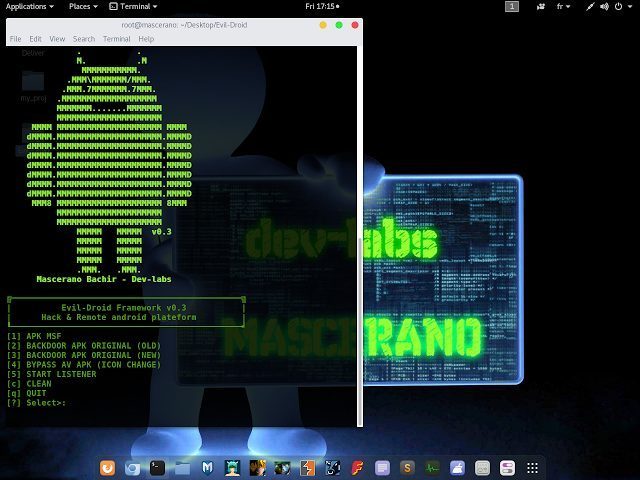
306Evil-Droid – Framework to Create, Generate & Embed APK Payloads
Evil-Droid is a framework that create & generate & embed apk payload to penetrate android platforms. Screenshot: Dependencies : 1 - metasploit-framework...
-

 249
249Phishing Emails are being sent to the users of Netflix by Hackers
This scam email is nearly well designed. The scammers are using a template system to create individualized reports with specific recipient data....
-

 195
195Student has been Hacking his grades from the past 21-Months at University of Iowa
The FBI apprehended the suspect Trevor Graves, age 22 at the close of October, in Denver, his hometown. According to an FBI...
-

 254
254Security Onion – Network Security Monitoring
Network Security Monitoring (NSM) is, put simply, monitoring your network for security related events. It might be proactive, when used to identify...
-

 301
301Fake WhatsApp On Google Play Store Downloaded By Over 1 Million Android Users
Cybercriminals are known to take advantage of everything that’s popular among people in order to spread malware, and Google’s official Play Store...
-

 190
190Child Abuse posts are not being removed by Facebook even after a year
A Facebook post promoting rape videos was also allowed to stay online despite being informed several times, the court listened, while police...
-
 199
199More than 150 Websites of Trump got Hacked
The Trump Organization dismissed the domain names were ever Hacked. But a review of internet credentials by the AP and cybersecurity specialists...
-
 249
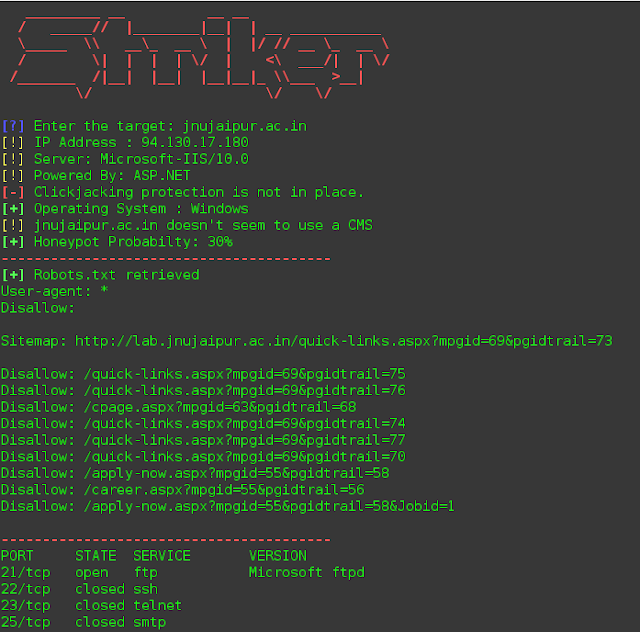
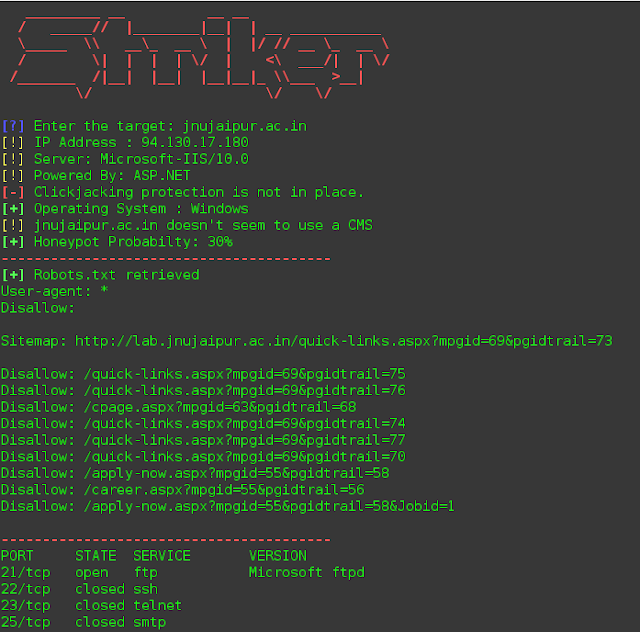
249Striker – Offensive Information And Vulnerability Scanner
Striker is an offensive information and vulnerability scanner. Features Just supply a domain name to Striker and it will automatically do the...
-
 323
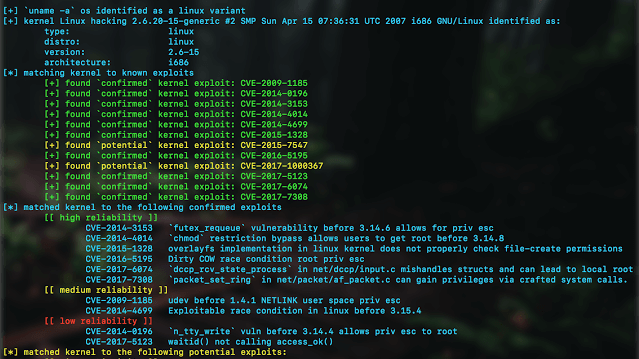
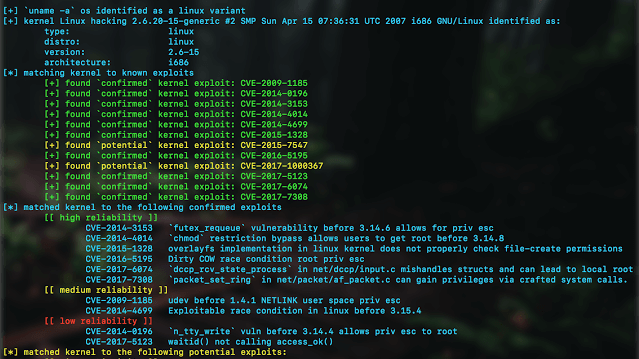
323Kernelpop – Kernel Privilege Escalation Enumeration And Exploitation Framework
kernelpop is a framework for performing automated kernel exploit enumeration on Linux, Mac, and Windows hosts. Requirementspython3 Currently supported CVE’s: *CVE-2017-1000367 *CVE-2017-1000112...






