Pentest
-

 223
223Bitcoin exchange NiceHash hacked, $68 million stolen
Bitcoin is breaking every record—after gaining 20% jump last week, Bitcoin price just crossed the $14,800 mark in less than 24 hours—and...
-
 193
193Bitcoin will be no longer supported by Steam
In the past few periods, we’ve seen an escalation in the volatility in the state of Bitcoin and a notable increase in...
-
 245
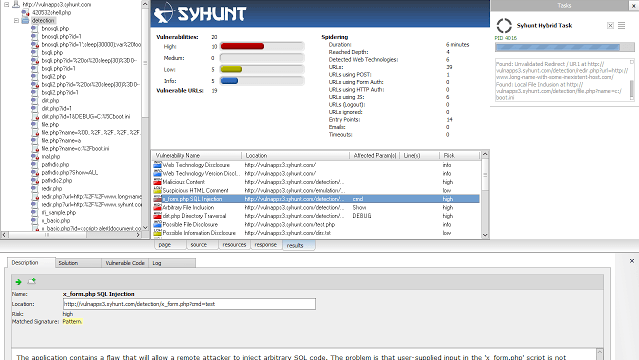
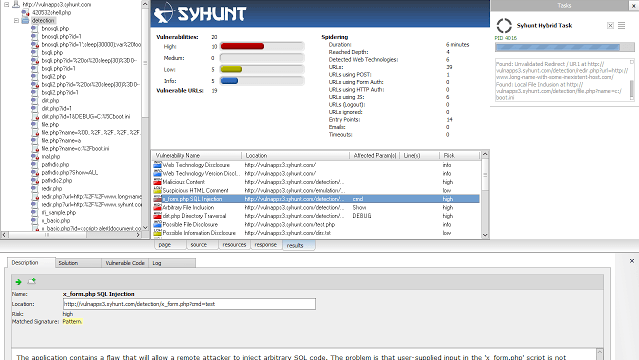
245Syhunt ScanTools 6.0 – Console Web Vulnerability Scan Tools
Syhunt ScanTools 6.0 adds advanced fingerprinting capabilities, enhanced spidering, injection and code scan capabilities, and a large number of improved checks. Adds...
-

 319
319Dr0p1t-Framework 1.3.2.1 – A Framework That Creates An Advanced FUD Dropper With Some Tricks
Have you ever heard about trojan droppers ? In short dropper is type of malware that downloads other malwares and Dr0p1t gives...
-
 213
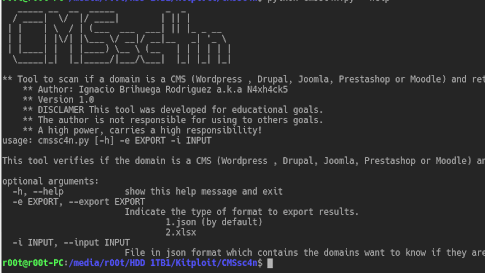
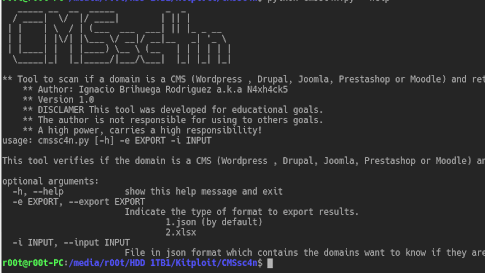
213CMSsc4n – Tool to identify if a domain is a CMS such as WordPress, Moodle, Joomla, Drupal or Prestashop
Tool to identify if a domain is a CMS such as WordPress, Moodle, Joomla, Drupal or Prestashop. Use python cmssc4n.py -h _____...
-
 287
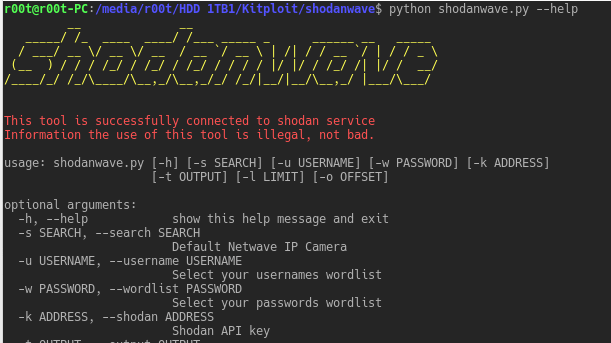
287Shodanwave – Exploring and Obtaining Information from Netwave IP Camera
Shodanwave is a tool for exploring and obtaining information from cameras specifically Netwave IP Camera. The tool uses a search engine called...
-

 178
17840 Million users are suffering the virtual keyboard data breach
The researchers demanded data left visible entered names, phone numbers, locations and Google queries. The chief of the Israeli company back the...
-

 238
238YouTube services are being Cut off from the Amazon Products
It’s the latest movement in a clash between Amazon and Google, which has seen the two businesses hold their products off the...
-
 223
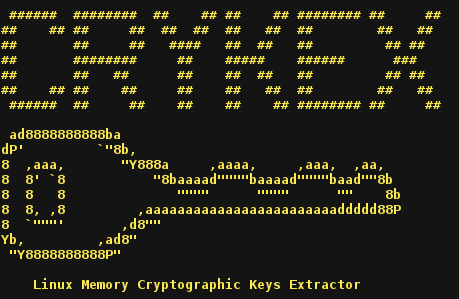
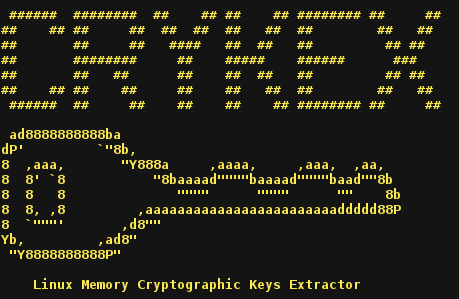
223CryKeX – Linux Memory Cryptographic Keys Extractor
Some work has been already published regarding the subject of cryptograhic keys security within DRAM. Basically, we need to find something that looks like...
-

 187
187Intel Management Engine is being disabled by the Computer Vendors
These ME security holes affect millions of computers. ME continues Intel’s Active Management Technology (AMT). This is a great tool that allows admins...
-
 339
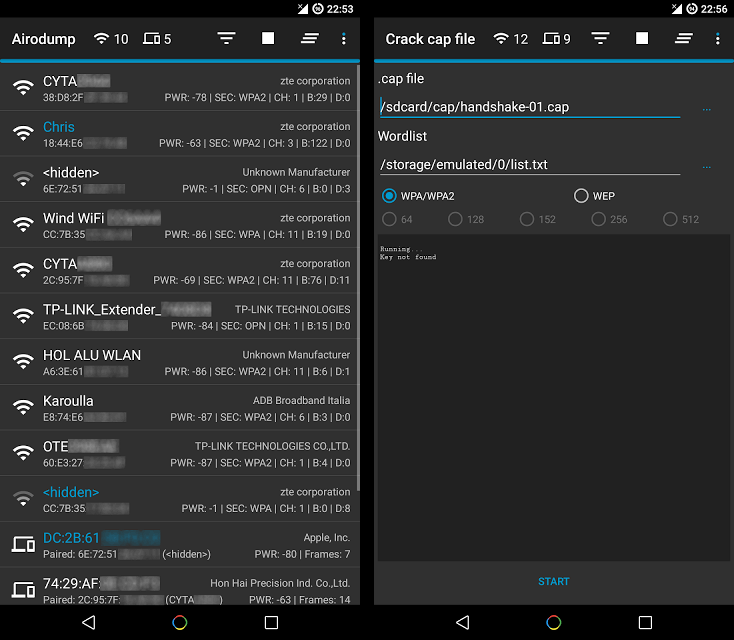
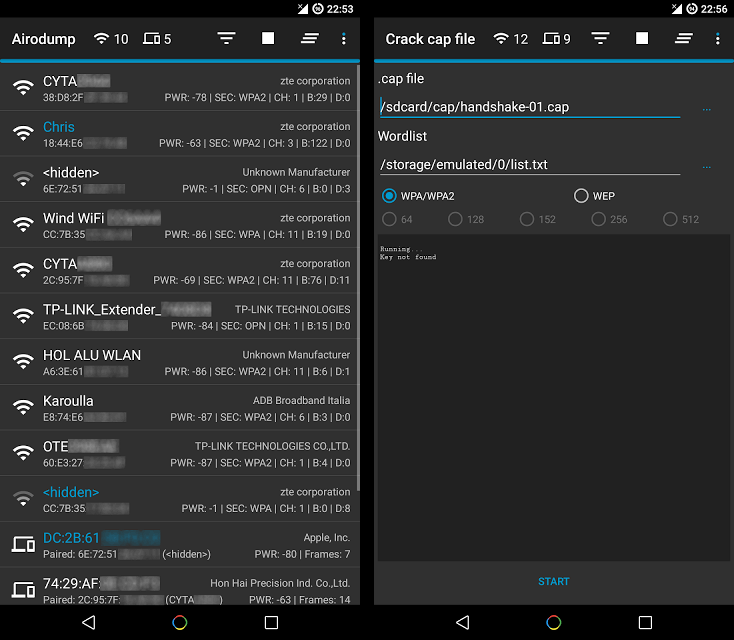
339Hijacker v1.4 – All-in-One Wi-Fi Cracking Tools for Android
Hijacker is a Graphical User Interface for the penetration testing tools Aircrack-ng, Airodump-ng, MDK3 and Reaver. It offers a simple and easy...
-
 269
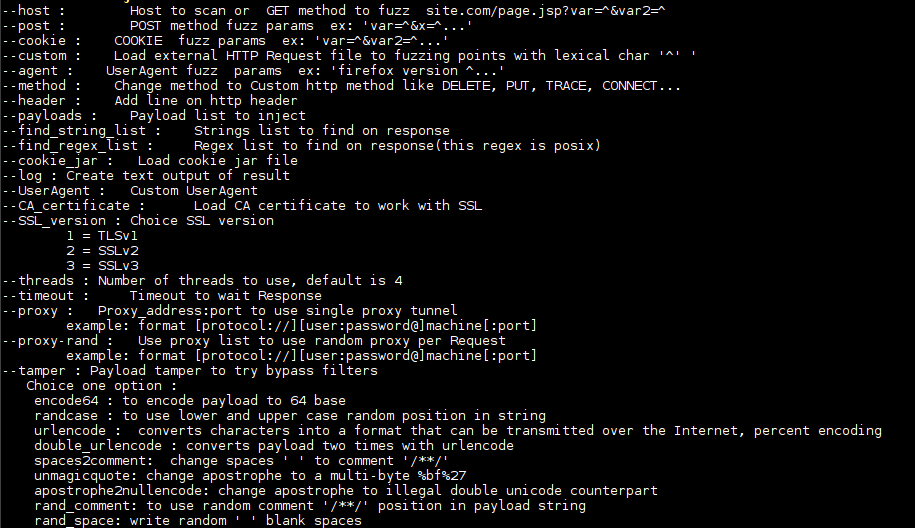
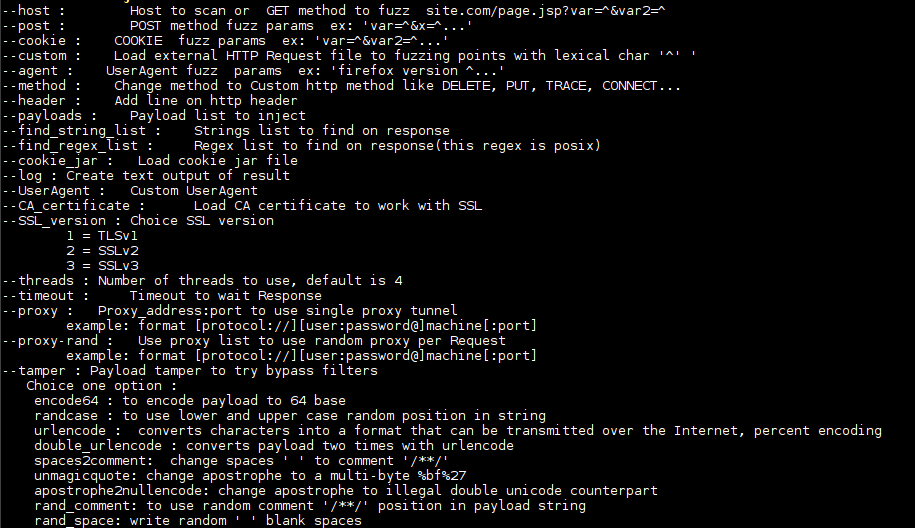
2690d1n v2.5 – Web Security Tool to Make Fuzzing at HTTP/S
Web security tool to make fuzzing at HTTP inputs, made in C with libCurl. 0d1n is a tool for automating customized attacks...
-

 285
285ratched – Transparent Man-in-the-Middle TLS Proxy
ratched is a Man-in-the-Middle (MitM) proxy that specifically intercepts TLS connections. It is intended to be used in conjunction with the Linux...
-
 246
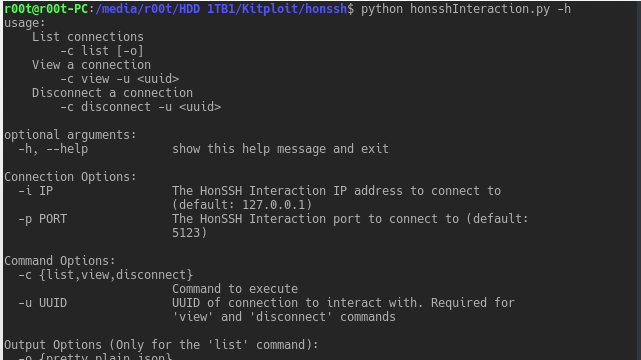
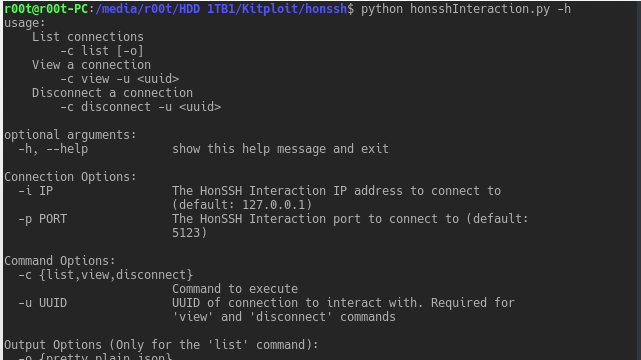
246HonSSH – Log all SSH communications between a client and server
HonSSH is a high-interaction Honey Pot solution. HonSSH will sit between an attacker and a honey pot, creating two separate SSH connections...
-
 280
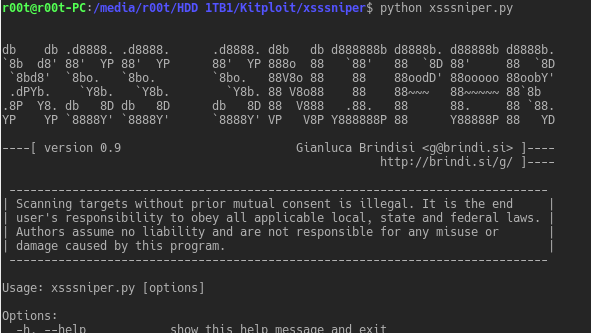
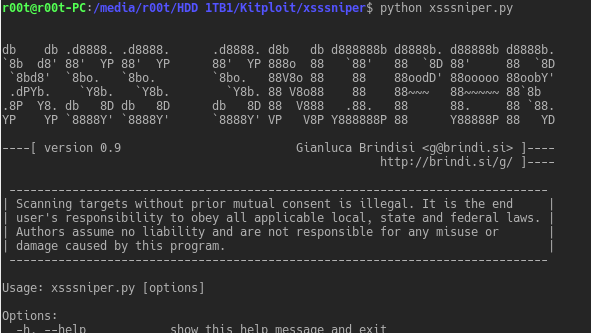
280XSSSNIPER – An Automatic XSS Discovery Tool
XSSSNIPER is an handy xss discovery tool with mass scanning functionalities. Usage: Usage: xsssniper.py [options] Options: -h, --help show this help message...
-
 260
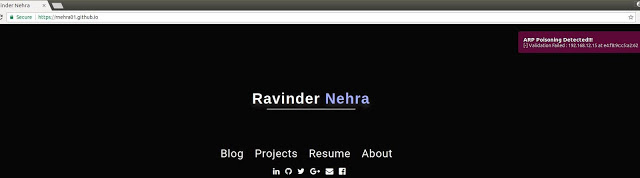
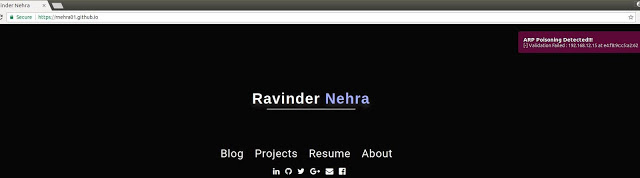
260arp-validator – Security Tool To Detect ARP Poisoning Attacks
Security Tool to detect arp poisoning attacks. Features Uses a faster approach in detection of arp poisoning attacks compared to passive approaches...
-
Bucket Stream – Find interesting Amazon S3 Buckets by watching certificate transparency logs
Some quick tips if you use S3 buckets: Randomise your bucket names! There is no need to use company-backup.s3.amazonaws.com. Set appropriate permissions...
-

 229
229NSA employee pleads guilty after stolen classified data landed in Russian hands
A former National Security Agency hacker has admitted to illegally taking highly classified information from the agency’s headquarters, which was later stolen...
-
 194
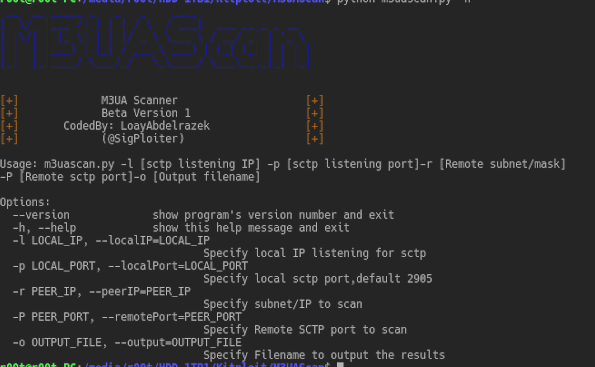
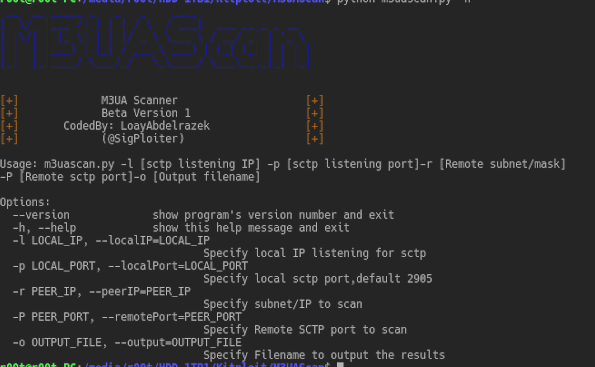
194M3UAScan – A Scanner for M3UA protocol to detect Sigtran supporting nodes
A Scanner for M3UA protocol to detect Sigtran supporting nodes M3UA stands for MTP Level 3 (MTP3) User Adaptation Layer as defined...
-
 239
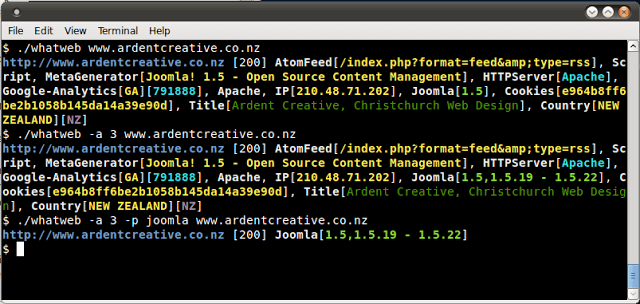
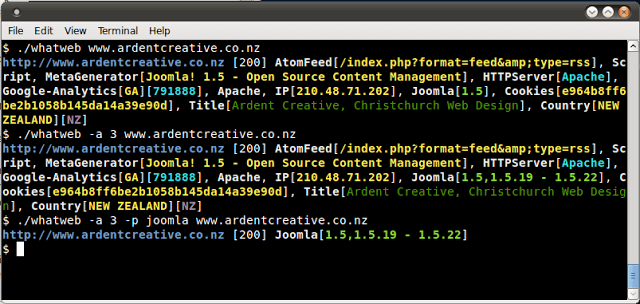
239WhatWeb v0.4.9 – Next Generation Web Scanner
WhatWeb identifies websites. Its goal is to answer the question, “What is that Website?”. WhatWeb recognises web technologies including content management systems...
-

 235
235Cr3dOv3r v0.2 – Know The Dangers Of Credential Reuse Attacks
Your best friend in credential reuse attacks. Cr3dOv3r simply you give it an email then it does two simple jobs (but useful)...






