Pentest
-

 173
173FCC’s plan is being criticized by Republicans in Congress
That’s frequently the case with net impartiality: a handful of Republican delegates have joined their voices to those demanding the FCC to...
-

 211
211Bitfinex (cryptocurrency exchange) is down due to DDoS attacks
Bitfinex (the world’s biggest cryptocurrency exchange by volume) was forced to shut down its continuous operations after experiencing a distributed denial of...
-
 274
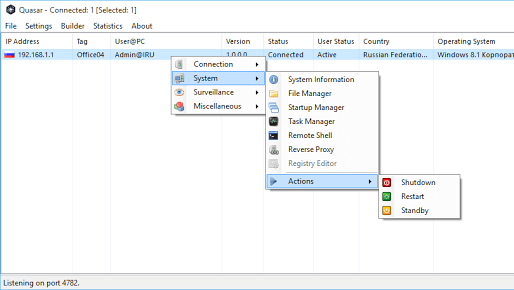
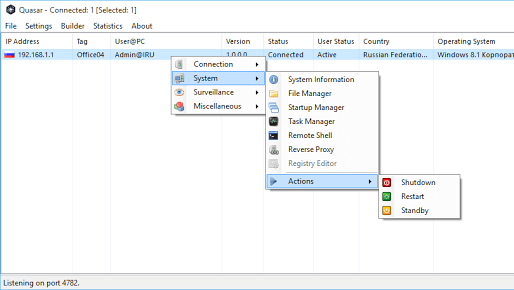
274QuasarRAT – Remote Administration Tool for Windows
Quasar is a fast and light-weight remote administration tool coded in C#. Providing high stability and an easy-to-use user interface, Quasar is...
-
 264
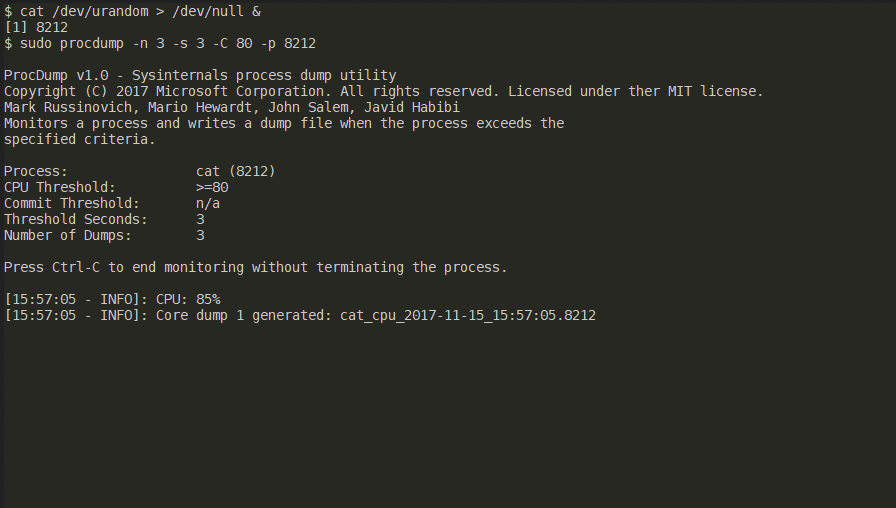
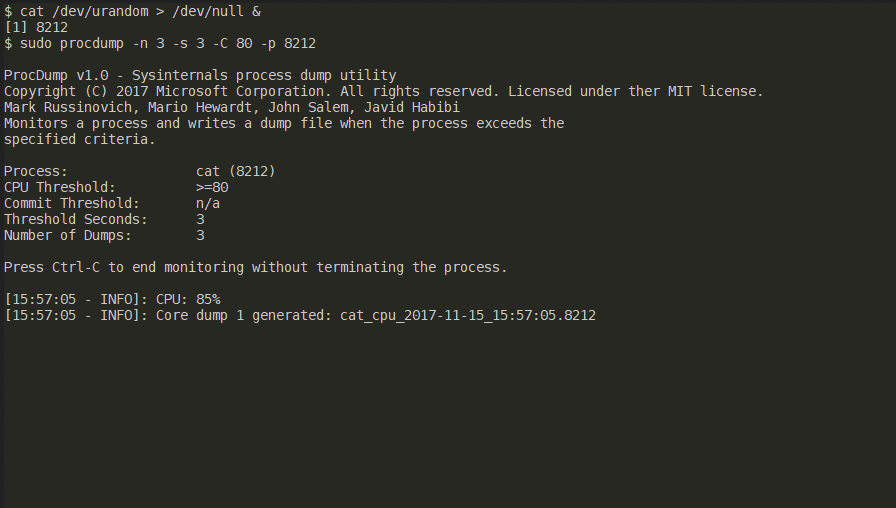
264ProcDump for Linux – A Linux version of the ProcDump Sysinternals tool
ProcDump is a Linux reimagining of the classic ProcDump tool from the Sysinternals suite of tools for Windows. ProcDump provides a convenient...
-

 199
199Google Project Zero ‘tpf0’ exploit whets appetite for iOS 11 jailbreak
Google’s Project Zero iOS bug hunter Ian Beer has released details about an iOS 11 exploit that could offer up a jailbreak...
-

 126
126Social Media is Ripping apart the society said by former Facebook Executive
Palihapitiya’s judgments were directed not only at Facebook but the broader online ecosystem. “The short-term, dopamine-driven feedback circles we’ve produced are destroying...
-
 295
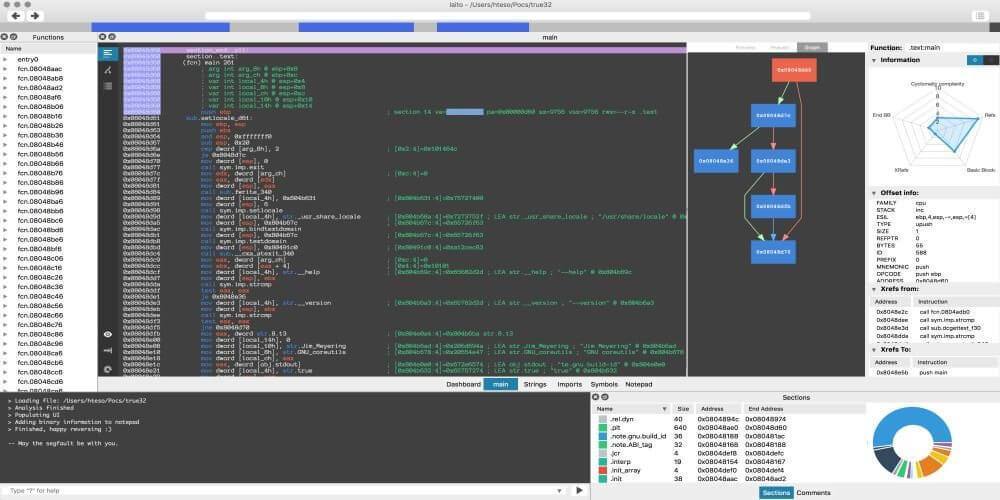
295Cutter – Qt C++ radare2 GUI Reverse Engineering Framework
A Qt and C++ GUI for radare2 reverse engineering framework (originally named Iaito). Cutter is not aimed at existing radare2 users. It instead...
-
 215
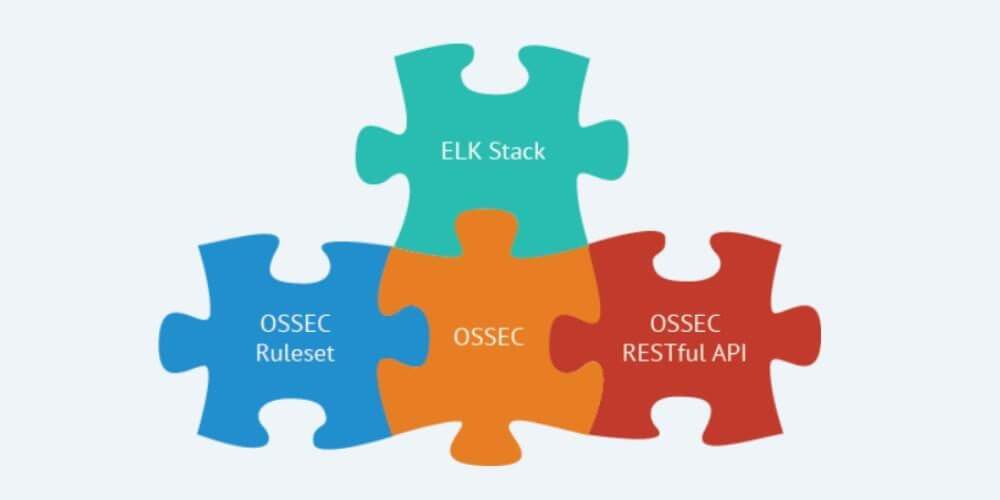
215Wazuh – Open Source Host & Endpoint Security
Wazuh is a security detection, visibility, and compliance open source project. It was born as a fork of OSSEC HIDS, later was...
-
 258
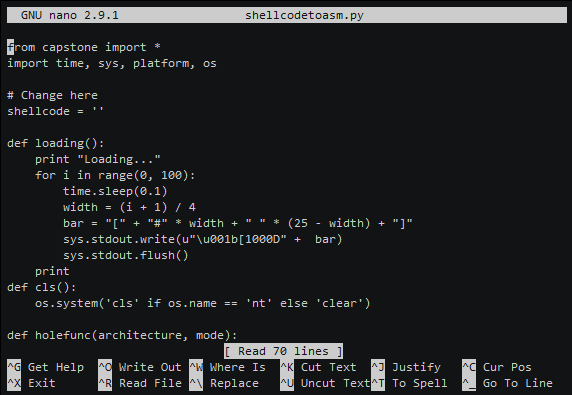
258ShellcodeToAssembly – Transform your Shellcode to Assembly (ARM, ARM64, MIPS, PPC, X86)
Transform your Shellcode to Assembly (ARM, ARM64, MIPS, PPC, X86) Replace in shellcodetoasm.py with your shellcode. shellcode = '' Installation git clone https://github.com/blacknbunny/ShellcodeToAssembly.git...
-
 311
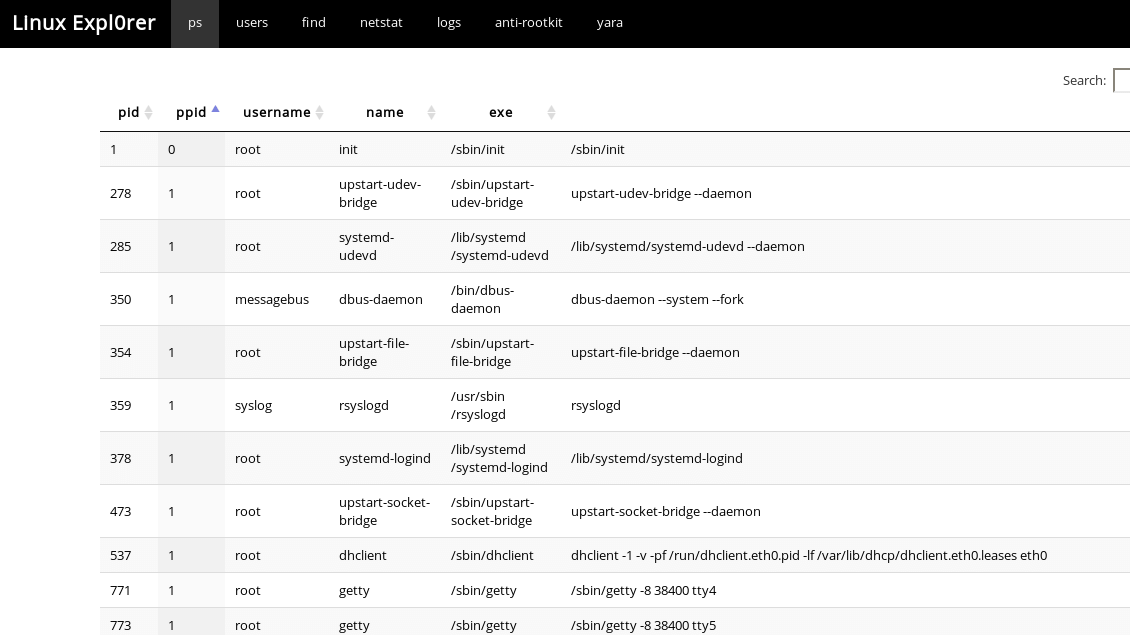
311Linux Expl0rer – Easy-To-Use Live Forensics Toolbox For Linux Endpoints
Easy-to-use live forensics toolbox for Linux endpoints written in Python & Flask. Capabilities ps View full process list Inspect process memory map...
-
 170
170Net Neutrality Rules are going to be repealed this week
On December 14, the company will vote to repeal the net neutrality practices it put in place in 2015. With Republicans agents...
-

 195
195Microsoft Has Fixed A Critical Vulnerability In Malware Protection Engine
On Wednesday, Microsoft has released a patch for the Microsoft Malware Protection Engine (MPE) to fix a critical severity remote code execution...
-
 221
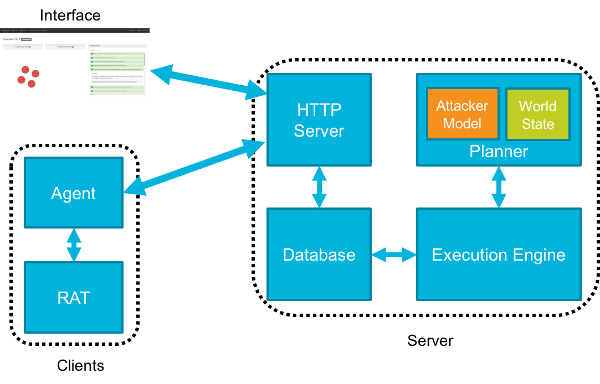
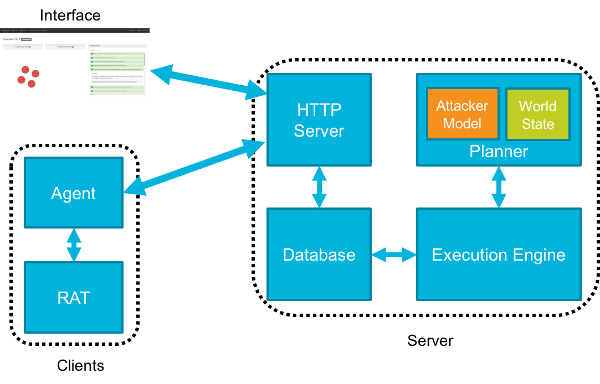
221CALDERA – Automated Adversary Emulation System
CALDERA is an automated adversary emulation system that performs post-compromise adversarial behavior within enterprise networks. It generates plans during operation using a planning...
-
 270
270Aletheia – Machine Learning Image Steganalysis
Aletheia is a steganalysis tool for the detection of hidden messages in images. The goal of steganalysis is to identify suspected packages,...
-

 168
168Apple Quick To Fix Bug That Allowed Hackers to Control HomeKit
Apple is one of the biggest companies today, but its devices are not free from issues. Recently, it was reported that the...
-

 242
242A New WordPress Malware called “wp-vcd” Distributes Via Pirated Themes
Denis Sinegubko (a security researcher from Sucuri) has discovered a new wave of the known malware wp-vcd that injects malicious WordPress admin...
-
 236
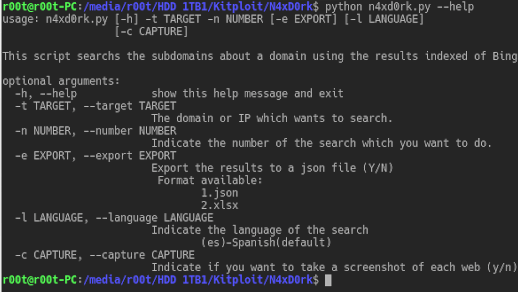
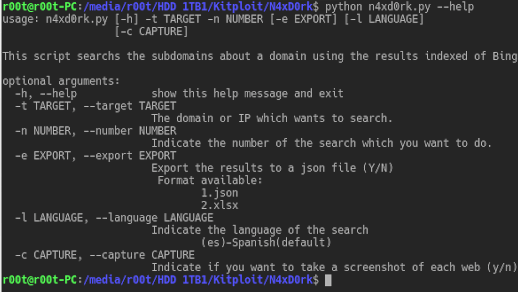
236N4xD0rk – Listing Subdomains About A Main Domain
Listing subdomains about the main domain using the technique called Hacking with search engines. Usage usage: n4xd0rk.py [-h] [-d DOMAIN] [-i IP]...
-
 185
185HP laptops have keylogger attached to their Synaptics Touchpad driver
The keylogging code was embedded in the SynTP.sys file, which is a module of the Synaptics Touchpad driver that ships with HP...
-
 197
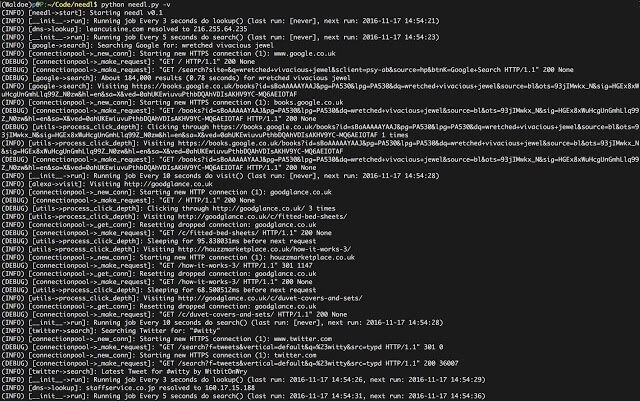
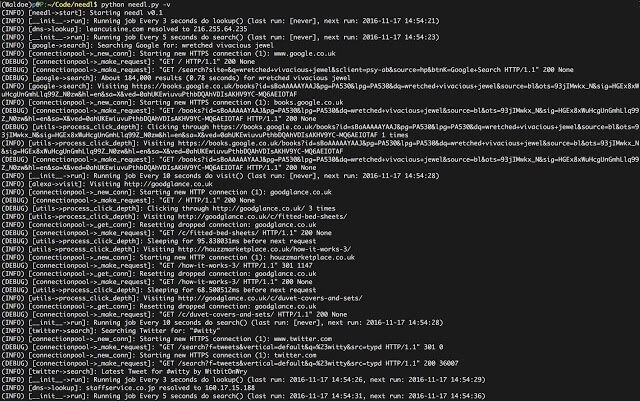
197Needl – Take Back Your Privacy. Lose Yourself In The Haystack
Take back your privacy. Lose yourself in the haystack. Your ISP is most likely tracking your browsing habits and selling them to...
-

 211
211Reddit is partnering with Sprinklr to improve customer engagement
The Partnership sounds like something that would result on Facebook or Twitter, which are rife with imprinted content not on a site...
-

 287
287Security vulnerability discovered in banking apps, leaving millions at risk
The flaw has been discovered by security researchers from the University of Birmingham, who tested hundreds of various banking applications and discovered...






