Pentest
-
 200
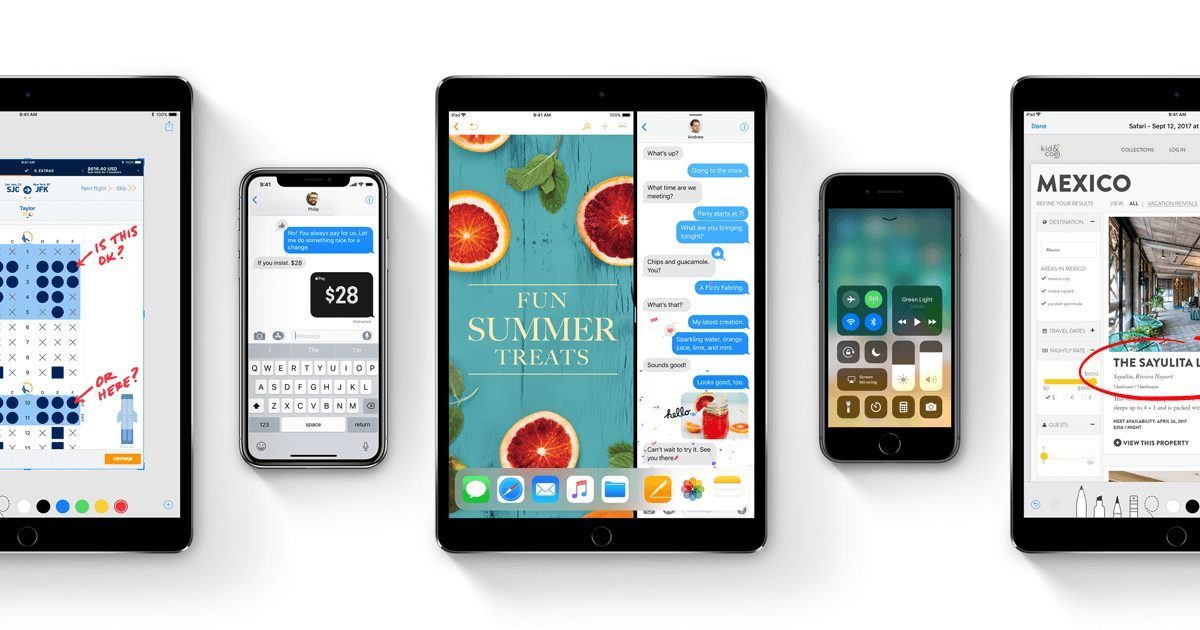
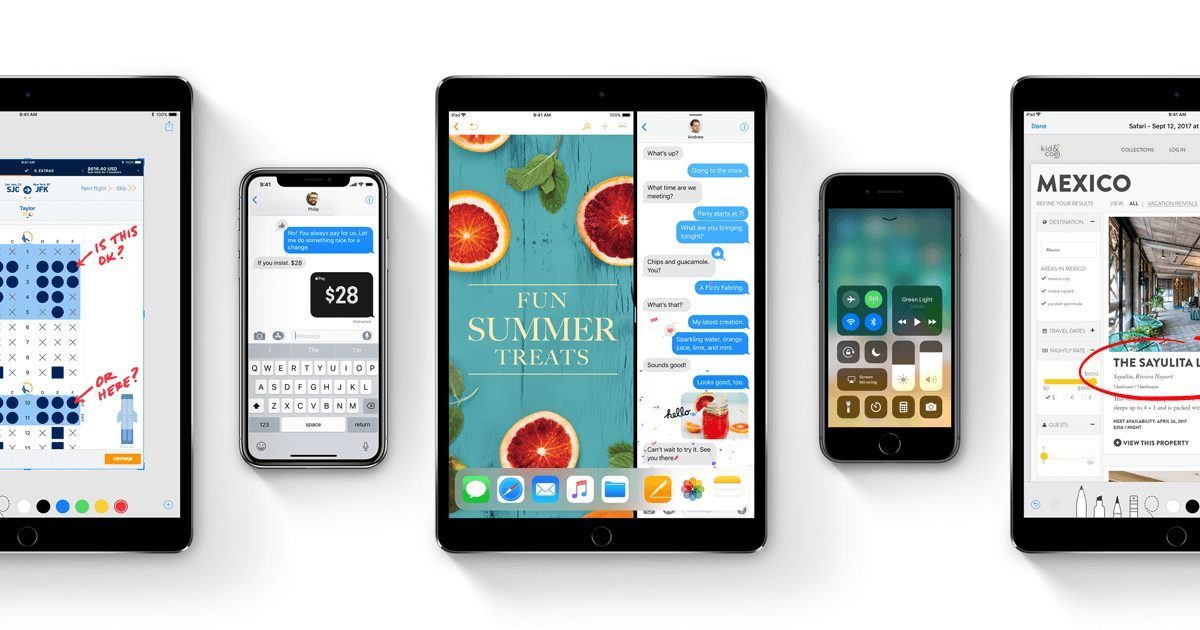
200Security Researcher Claims that Apple’s iOS 11 Devices are Prone to Single Point of Failure
After rapidly reinforcing a flaw that acknowledged anyone with access to a High Sierra Mac to take administrative control, Apple still has...
-

 199
199Privacy of 5 Million iPhone users is being affected by Google
The group, called Google You Owe Us, said in a declaration Thursday that it was the first case of its sort in...
-

 232
232Amber – POC Reflective PE Packer
Amber is a proof of concept packer, it can pack regularly compiled PE files into reflective PE files that can be used...
-
 245
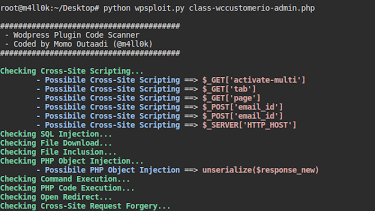
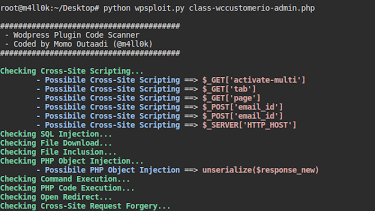
245WPSploit – WordPress Plugin Code Scanner
This tool is intended for Penetration Testers who audit WordPress plugins or developers who wish to audit their own WordPress plugins. For...
-
 241
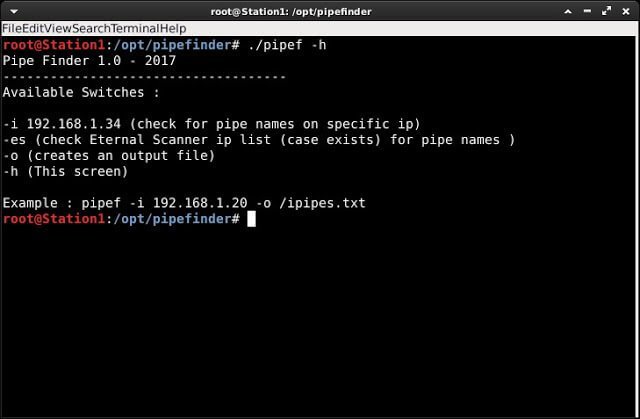
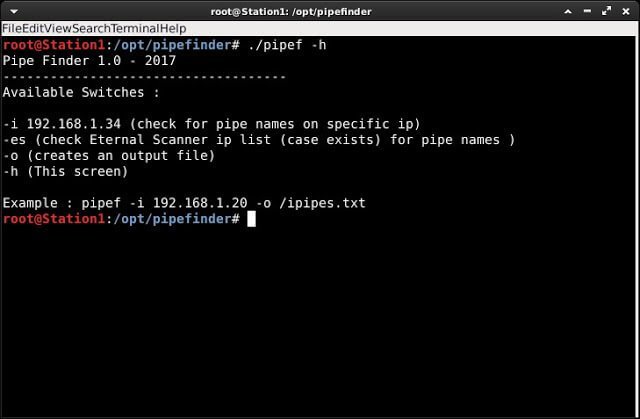
241Pipe Finder – Automated script to search in SMB protocol for available pipe names
Automated script to search in SMB protocol for availables pipe names. Requirements metasploit-framework wget pipe_audit_v2.rb module (https://github.com/peterpt/pipe_auditor_fb) – It will be installed...
-
 226
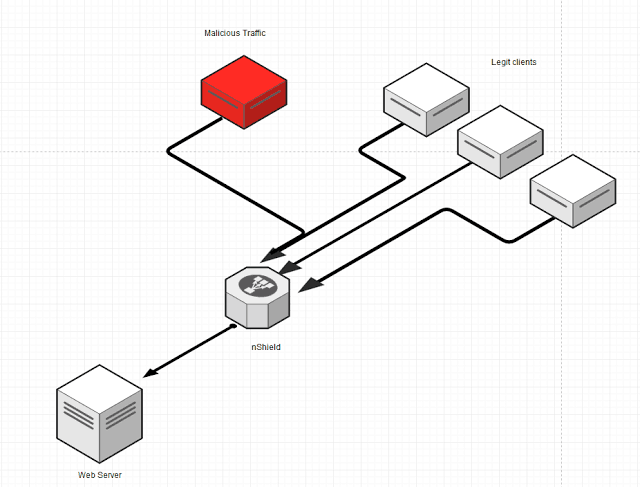
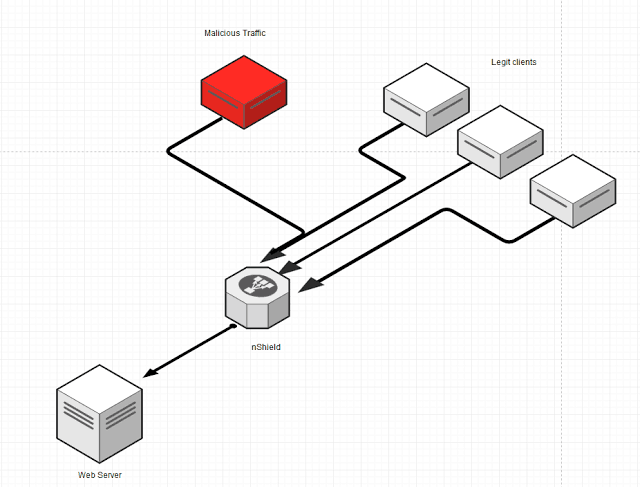
226net-Shield – An Easy and Simple Anti-DDoS solution for VPS, Dedicated Servers and IoT devices
An Easy and Simple Anti-DDoS solution for VPS,Dedicated Servers and IoT devices based on iptables. Requirements Linux System with python, iptables Nginx...
-
 237
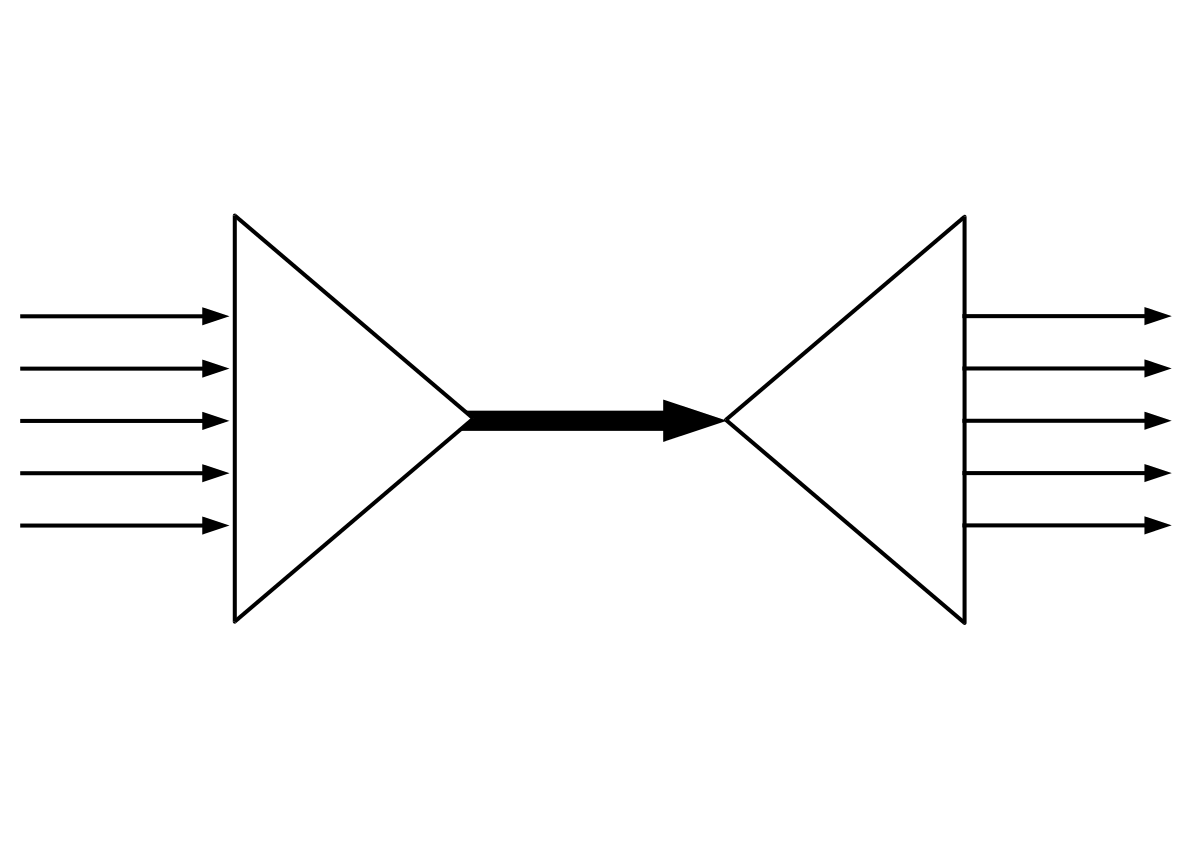
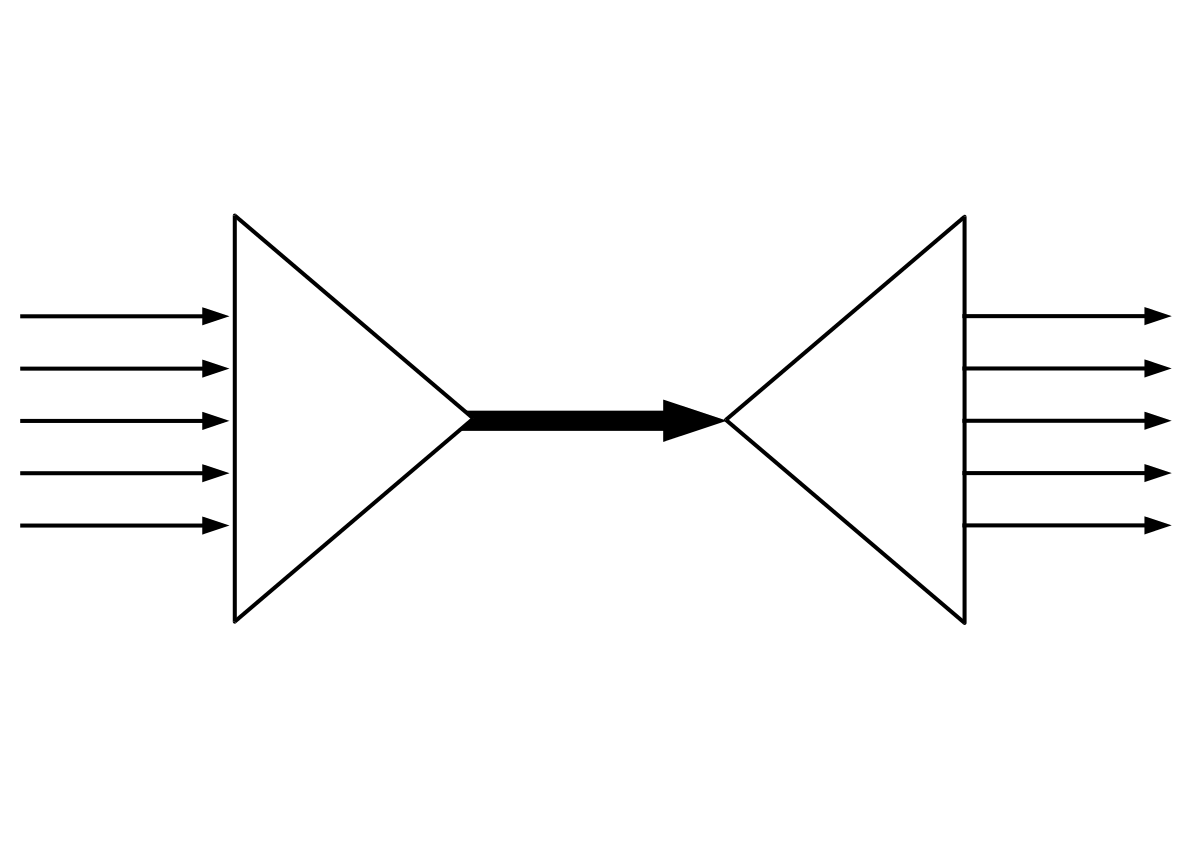
237SSLH – Applicative Protocol Multiplexer
sslh accepts connections on specified ports, and forwards them further based on tests performed on the first data packet sent by the...
-

 185
185Suspicious Lock Screen Apps are finally banned from Google Play Store
Google has explicitly rejected them from the Play Store. Identify Airpush? The current advertisement scourge is ad-infused lock screens, which have shown up...
-

 166
166Bitcoin has lost 8% of it’s value in the last 24 Hours
The cryptocurrency fell as greatly as 8 percent on Thursday on the Luxembourg confirmed Bitstamp exchange to hit $9,000 exactly, considering a...
-
 259
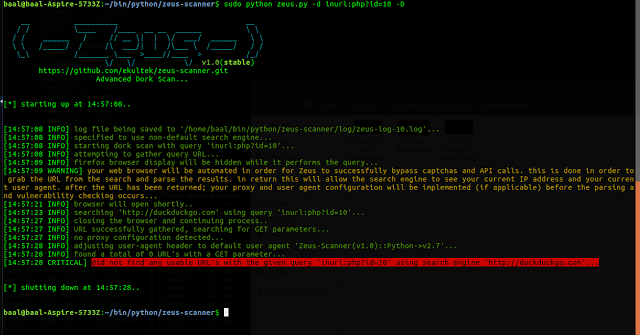
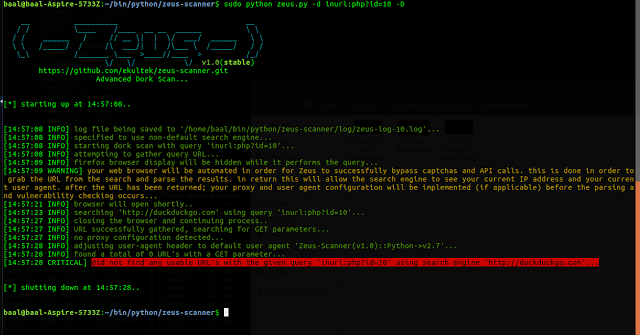
259Zeus-Scanner – Advanced Reconnaissance Utility
Zeus is an advanced reconnaissance utility designed to make web application reconnaissance simple. Zeus comes complete with a powerful built-in URL parsing...
-

 243
243TeleShadow v2 – Advanced Telegram Desktop Session Hijacker
Advanced Telegram Desktop Session Hijacker! Stealing desktop telegrams has never been so easy ! Set the email and sender details of the...
-
 249
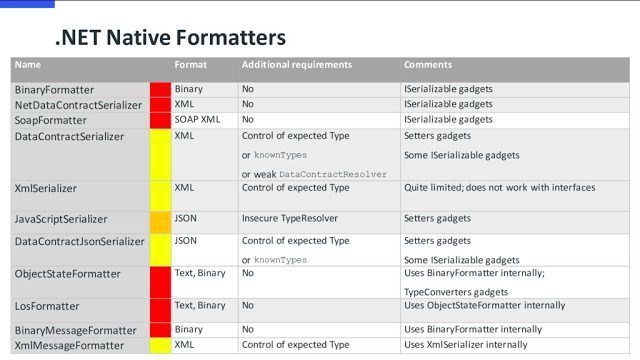
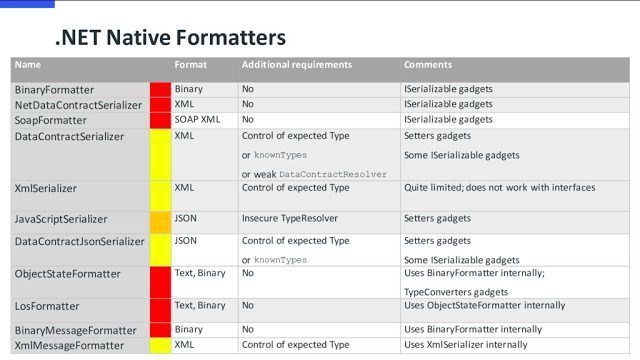
249ysoserial.net – Deserialization payload generator for a variety of .NET formatters
A proof-of-concept tool for generating payloads that exploit unsafe .NET object deserialization. Description ysoserial.net is a collection of utilities and property-oriented programming...
-
 246
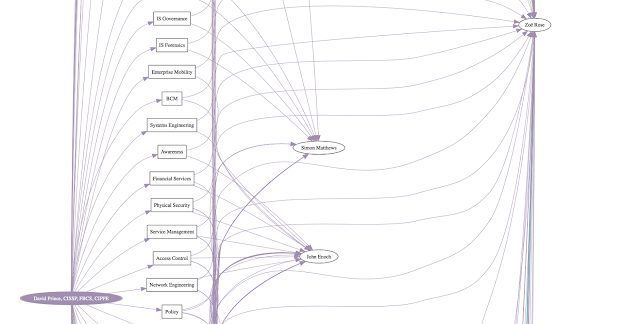
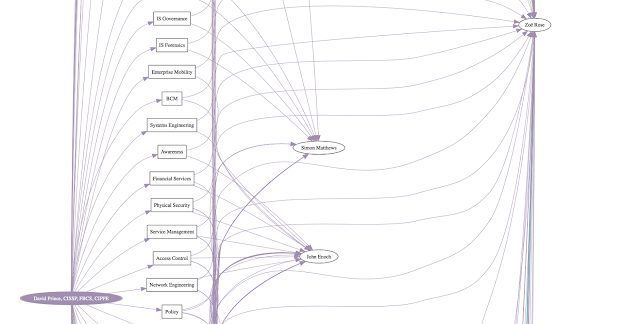
246The Endorser – An OSINT tool that allows you to draw out relationships between people on LinkedIn via endorsements/skills
An OSINT tool that allows you to draw out relationships between people on LinkedIn via endorsements/skills. Check out the example (digraph), which...
-

 266
266OpenWPM – Web Privacy Measurement Framework
Web Privacy Measurement is the observation of websites and serves to detect, characterize and quantify privacy-impacting behaviors. Applications of Web Privacy Measurement...
-
 241
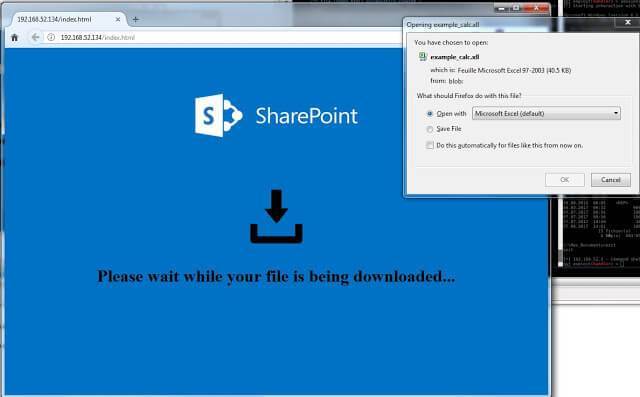
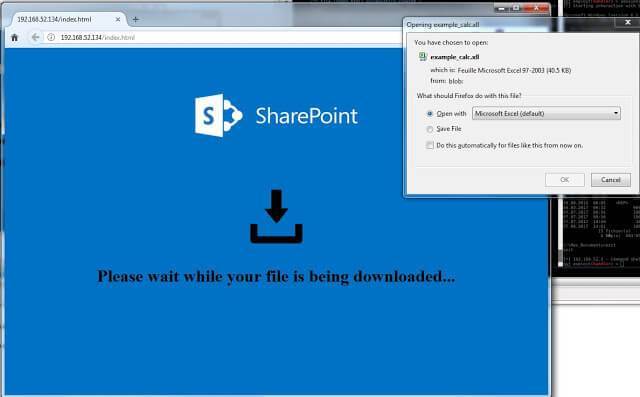
241EmbedInHTML – Embed and hide any file in an HTML file
What this tool does is taking a file (any type of file), encrypt it, and embed it into an HTML file as...
-

 323
323Sublist3r – Fast Subdomains Enumeration Tool for Penetration Testers
Sublist3r is a python tool designed to enumerate subdomains of websites using OSINT. It helps penetration testers and bug hunters collect and...
-
 292
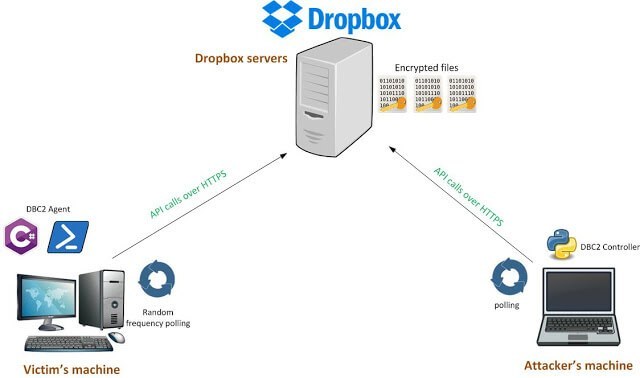
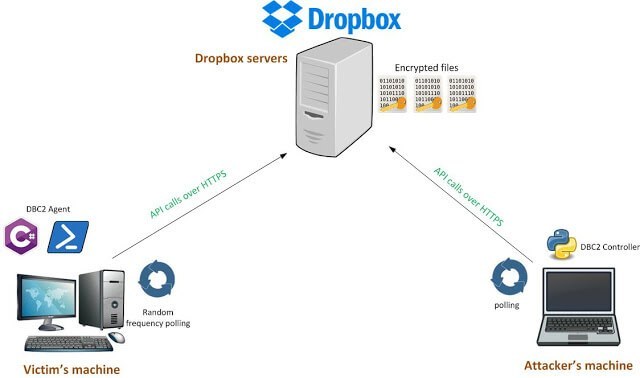
292DBC2 (DropboxC2) – A Modular Post-Exploitation Tool, Composed Of An Agent Running On The Victim’S Machine
DBC2 (DropboxC2) is a modular post-exploitation tool, composed of an agent running on the victim’s machine, a controler, running on any machine,...
-
 216
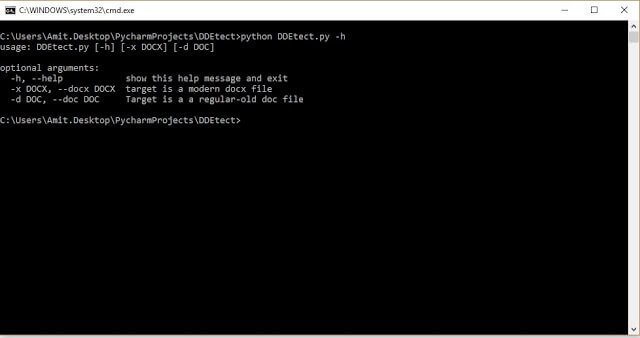
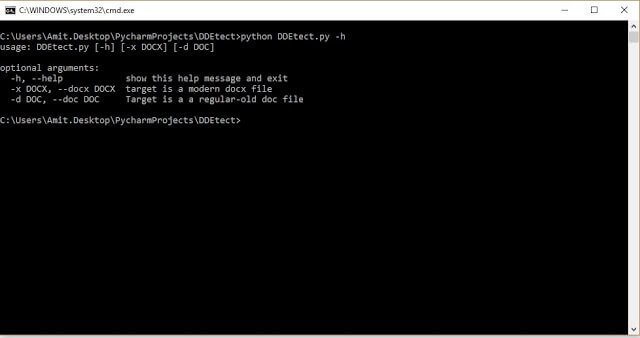
216DDEtect – Simple DDE Object Detector
Written by Amit Serper, @0xAmit DDEtector is a simple DDE object detector written in python Currently supports only word DOCX and legacy...
-
 140
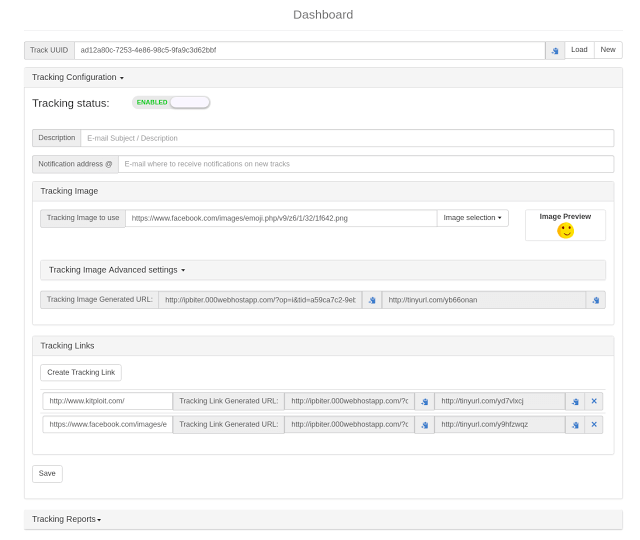
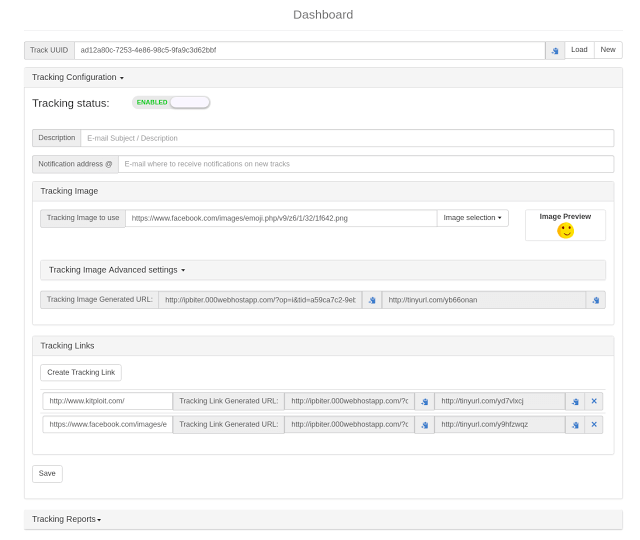
140IP-Biter – The Hacker-friendly E-Mail Tracking Framework
IP-Biter is an open source, easy to deploy, tracking framework that generate high configurables and uniques tracking images and links to embed...
-

 283
283PortEx – Java library to analyse Portable Executable files with a special focus on malware analysis and PE malformation robustness
PortEx is a Java library for static malware analysis of Portable Executable files. Its focus is on PE malformation robustness, and anomaly...
-

 120
120Facebook doesn’t care about your privacy according to the Ex-Facebook Operations Manager
A former operations manager existed for Facebook’s privacy works said the company “prioritized data gathering from its users overprotecting them from abuse.”...






