Pentest
-
 243
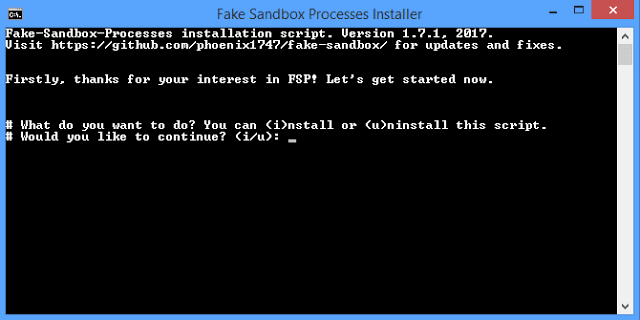
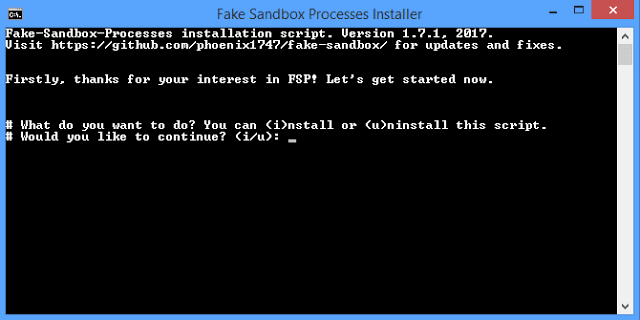
243Fake Sandbox Processes (FSP) – Tool to simulate fake processes of analysis sandbox/VM software
This small script will simulate fake processes of analysis, sandbox and/or VM software that some malware will try to avoid. You can...
-
 197
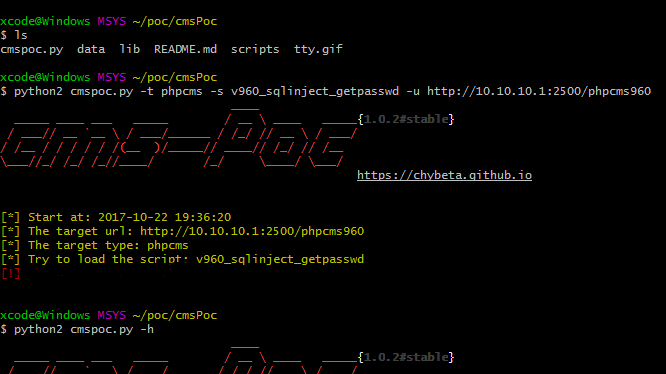
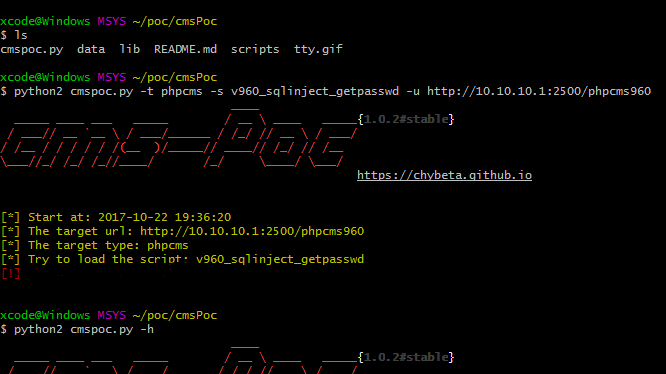
197cmsPoc – A CMS Exploit Framework
A CMS Exploit Framework. Requirements python2.7 Works on Linux, Windows Usage usage: cmspoc.py [-h] -t TYPE -s SCRIPT -u URL optional arguments:...
-

 185
185Adobe Patches 67 Vulnerabilities in Flash, Acrobat, and Reader
Adobe’s latest security update has swatted a total of 67 bugs, some of them critical, in Adobe Flash, Acrobat, and Reader. On...
-

 185
185Forever 21 Reveals Potential Data Breach
Forever 21 is investigating a potential data breach which may have compromised customer information and payment cards. On Tuesday, the US clothing...
-
DHS, FBI describe North Korea’s use of FALLCHILL malware
The federal government on Tuesday issued an alert detailing the North Korean government’s use of malware known as FALLCHILL, warning that North...
-

 305
305Security vulnerability in IoT cameras could allow remote control by hackers
Newly uncovered vulnerabilities in a popular brand of indoor internet-connected cameras could be exploited by attackers in order to gain complete control...
-

 229
229ooniprobe – Network Interference Detection Tool
OONI, the Open Observatory of Network Interference, is a global observation network which aims is to collect high quality data using open...
-
 316
316Nishang – PowerShell Penetration Testing Framework
Nishang is an open source framework and collection of powerful PowerShell scripts and payloads that you can use during penetration testing audit,...
-
 253
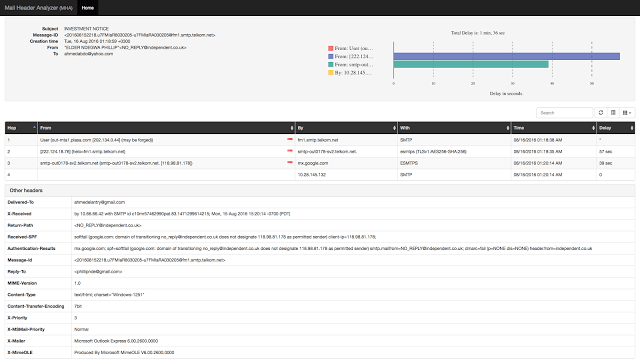
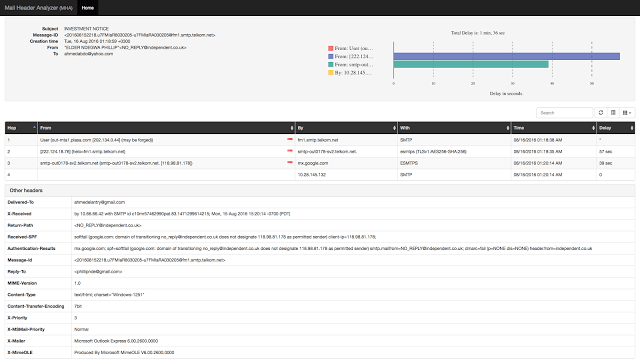
253MHA – Mail Header Analyzer
Mail header analyzer is a tool written in flask for parsing email headers and converting them to a human readable format and...
-
 215
215Sandboxing support has been added to Firefox for Linux
The Firefox sandboxing innovation confines the browser from the operating system in a way to block web attacks from using a vulnerability...
-

 273
273Texas is spying on Thousands of Phones using Surveillance Drones and Planes
Similar to questionable stingray devices, DRT’s operations nicknamed “dirt boxes” mimic cellphone pillars, relating to every smartphone within a specific area. Because...
-
 182
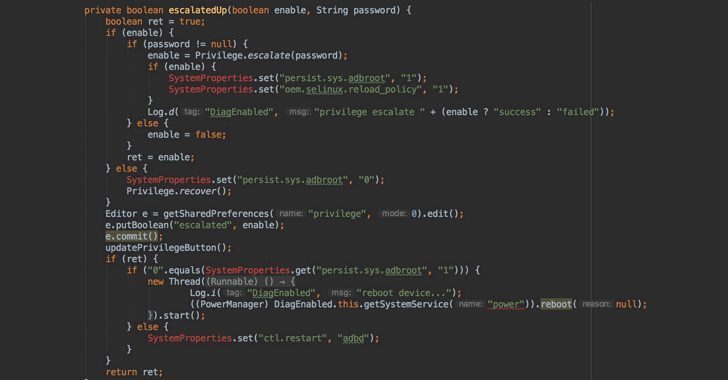
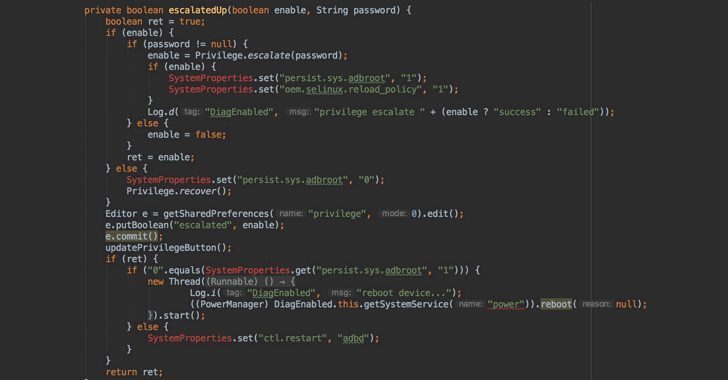
182OnePlus Left A Backdoor That Allows Root Access Without Unlocking Bootloader
Just over a month after OnePlus was caught collecting personally identifiable information on its users, the Chinese smartphone company has been found...
-
 259
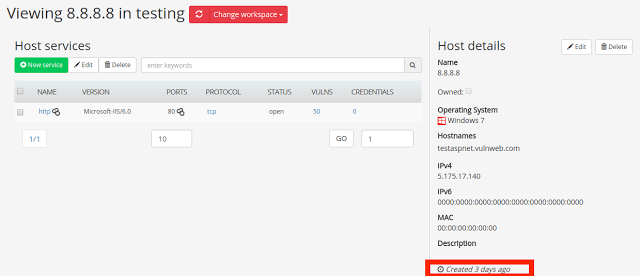
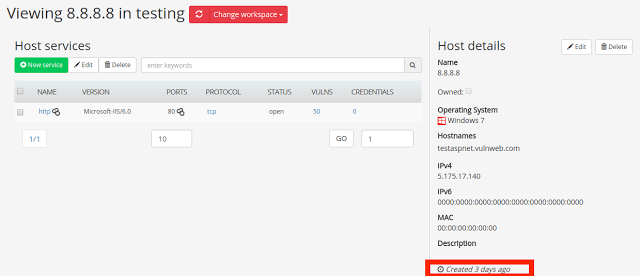
259Faraday v2.7 – Collaborative Penetration Test and Vulnerability Management Platform
Faraday is the Integrated Multiuser Risk Environment you have always been looking for! It maps and leverages all the data you generate in real time,...
-
 322
322Mentalist – Graphical Tool For Custom Wordlist Generation
Mentalist is a graphical tool for custom wordlist generation. It utilizes common human paradigms for constructing passwords and can output the full...
-

 238
238Face ID just got Hacked with the help of a mask by a security firm
Apple uses the Tenth Anniversary iPhone X Phone to replace Touch ID. Because the award handset features an edge-to-edge protection and has...
-

 169
169Bitcoin rebounds over $1,000 after losing almost a third of value
Bitcoin surged on Monday, recovering more than $1,000 after losing almost a third of its value in less than four days as...
-
 259
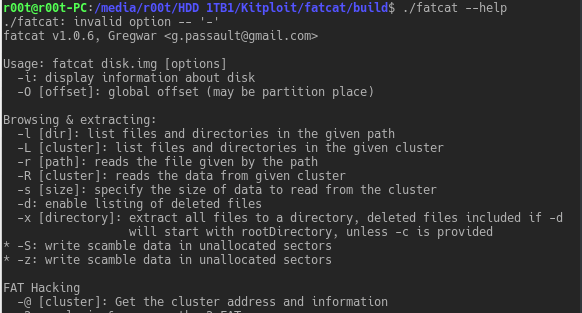
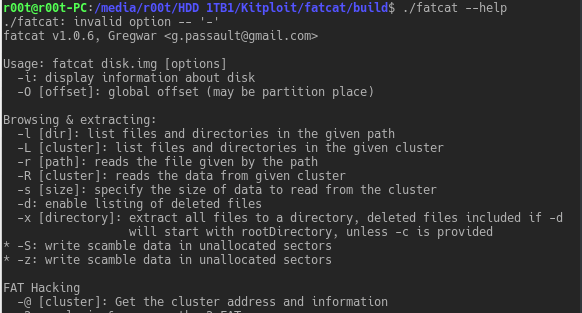
259fatcat – FAT Filesystems Explore, Extract, Repair, And Forensic Tool
This tool is designed to manipulate FAT filesystems, in order to explore, extract, repair, recover and forensic them. It currently supports FAT12,...
-

 233
233North Korean Radio Station got Hacked and the station broadcasted “The Final Count Down”
News of the event was posted on Twitter by vigilante hacker, “The Jester,” who has in the past increased fame by hacking...
-

 168
168Blockchain.info Vulnerability Allows Attackers to Steal Bitcoin Wallet Backups
Blockchain.info is a bitcoin cryptocurrency wallet and block explorer service. Started in August 2011, the service presents information on new transactions, mined...
-
 180
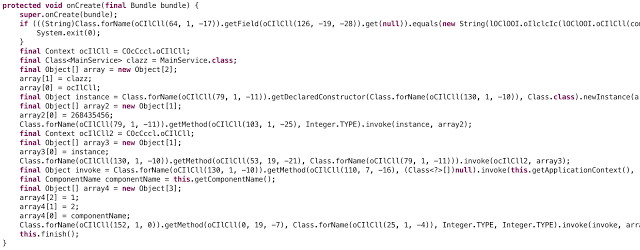
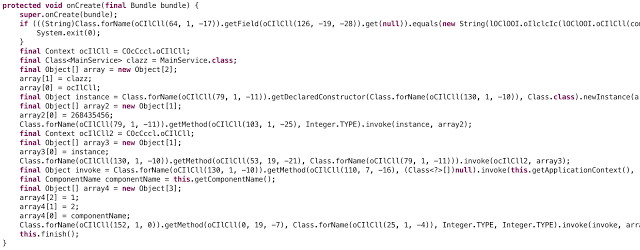
180Dex-Oracle – A pattern based Dalvik deobfuscator which uses limited execution to improve semantic analysis
A pattern based Dalvik deobfuscator which uses limited execution to improve semantic analysis. Also, the inspiration for another Android deobfuscator: Simplify. Before...
-

 213
213Kaspersky Anti-Virus is being impersonated by a CIA’s Spying Program
The tool itself is impressive enough, serving as the backbone of the CIA’s malware processes, but there’s more. What’s interesting about the...






