Pentest
-

 231
231$8.9 Million fine was imposed on Uber for allowing unqualified drivers to drive cars in Colorado
The business allowed 57 people to drive vehicles although they required valid driver’s licenses or had performed other offenses that would have...
-
 319
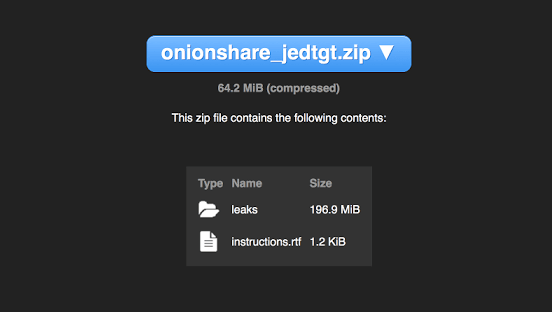
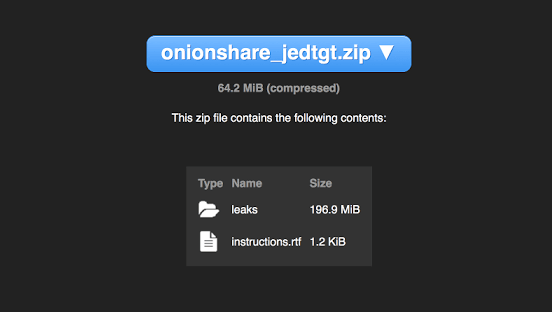
319OnionShare – Securely and anonymously share a file of any size
OnionShare lets you securely and anonymously share files of any size. It works by starting a web server, making it accessible as...
-
 318
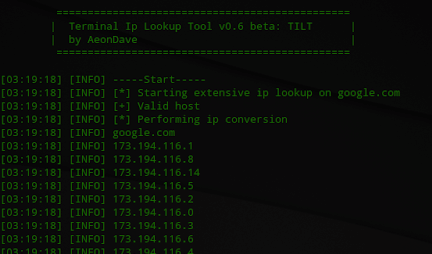
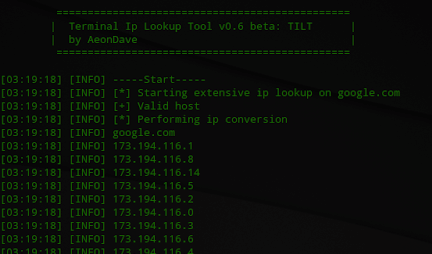
318Tilt – Terminal IP Lookup Tool
Tilt: Terminal ip lookup tool, is an easy and simple open source tool implemented in Python for ip/host passive reconnaissance. It’s very...
-
 195
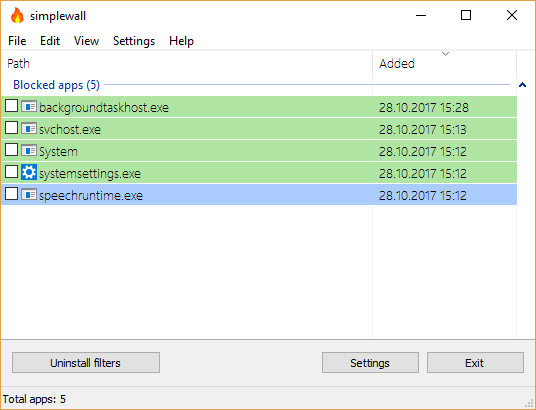
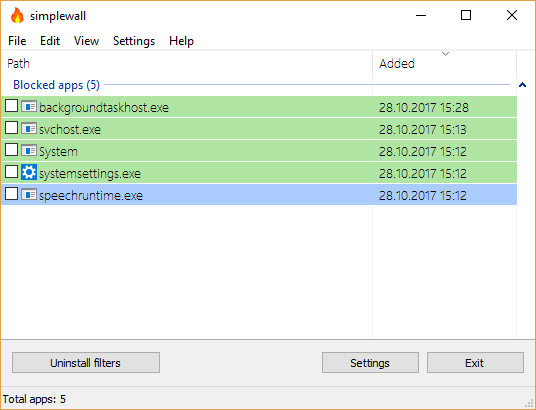
195SimpleWall – Simple tool to configure Windows Filtering Platform (WFP)
Simple tool to configure Windows Filtering Platform (WFP) which can configure network activity on your computer. The lightweight application is less than...
-

 255
255Excalibur – An Eternalblue exploit payload based Powershell
Excalibur is an Eternalblue exploit based “Powershell” for the Bashbunny project. It’s purpose is to reflect on how a “simple” USB drive...
-

 286
286Children’s Smart Watches are being banned by the German Government
It had earlier banned an internet-associated doll called, My Friend Cayla, for similar reasons. Telecoms regulator the Federal Network Agency urged parents...
-
 187
187Web Monitoring Data Archive has been left open to public
Discovered by UpGuard defense researcher Chris Vickery, the databases were entitled “CENTCOM-backup,” “CENTCOM-archive,” and “pacom-archive.” Based on their titles, it was obvious...
-

 271
271SpookFlare – Meterpreter Loader Generator With Multiple Features For Bypassing Client-Side And Network-Side Countermeasures
SpookFlare has a different perspective to bypass security measures and it gives you the opportunity to bypass the endpoint countermeasures at the...
-

 166
166Unprotected .gov email addresses are being spoofed by the Russians
The firm looked at nearly 70 million emails sent during October from 5,000 different .gov origin domains preserved by Proofpoint, the company’s...
-

 201
201Terdot Banking Trojan Gains Ability to Steal Facebook, Twitter and Gmail Accounts
Security researchers have discovered a new, sophisticated form of malware based on the notorious Zeus banking Trojan that steals more than just bank account...
-

 164
164Third Party People can Disable your Amazon Key’s Camera allowing couriers to reenter into your home
Now security researchers have discovered that the camera can be silenced and frozen from a script run from any machine within Wi-Fi...
-
 252
252Prochunter – Linux Process Hunter
Prochunter aims to find hidden process with all userspace and most of the kernelspace rootkits. This tool is composed of a kernel...
-

 234
234Bluebox-ng – Node.js VoIP Penetration Testing Framework
Features Auto VoIP/UC penetration test Report generation Performance RFC compliant SIP TLS and IPv6 support SIP over websockets (and WSS) support (RFC...
-
 553
553GOSINT – Open Source Threat Intelligence Gathering & Processing Framework
The GOSINT framework is a project used for collecting, processing, and exporting high quality indicators of compromise (IOCs). GOSINT allows a security...
-
 217
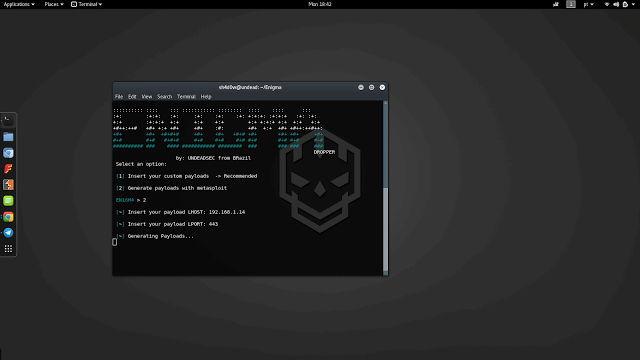
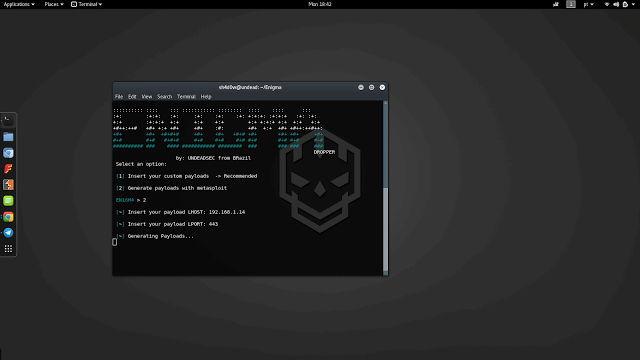
217Enigma – Multiplatform Payload Dropper
Enigma is a Multiplatform payload dropper. Run git clone https://github.com/UndeadSec/Enigma.git cd Enigma python enigma.py or python3 enigma3.py Prerequisites python 2.7 for enigma.py python...
-
 278
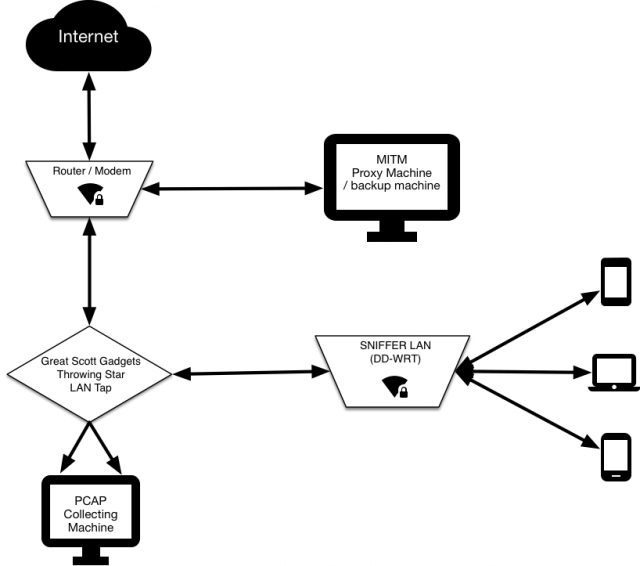
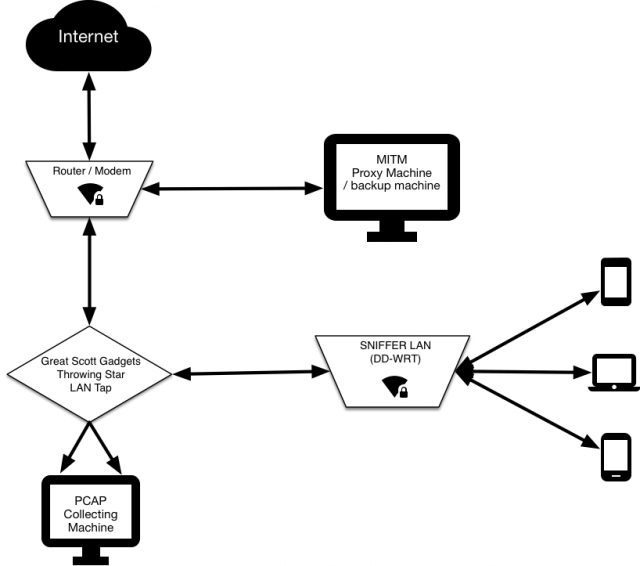
278SNIFFlab – Create Your Own MITM Test Environment
Essentially it’s a WiFi hotspot that is continually collecting all the packets transmitted across it. All connected clients’ HTTPS communications are subjected...
-
 227
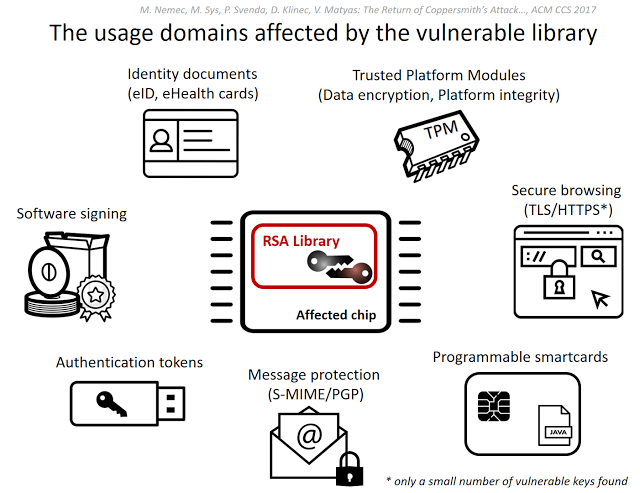
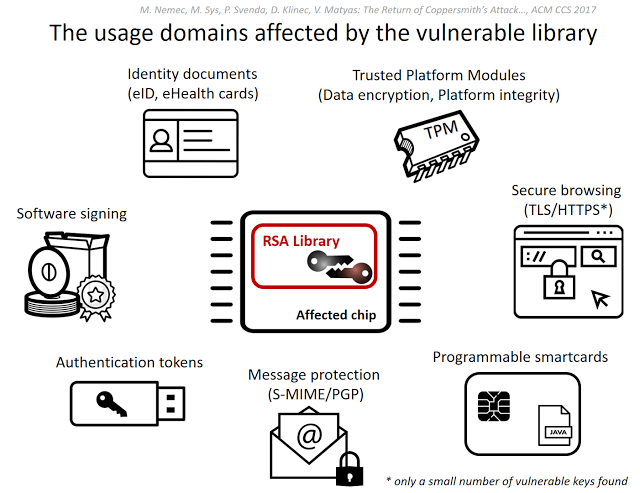
227ROC – Infineon RSA Vulnerability
This tool is related to ACM CCS 2017 conference paper #124 Return of the Coppersmith’s Attack: Practical Factorization of Widely Used RSA...
-

 224
224Sneaky three-stage malware found in Google Play store
Another crop of Android apps hiding malware have been discovered in – and removed from – the Google Play store. Researchers at...
-

 262
262Bluetooth Hack Affects 20 Million Amazon Echo and Google Home Devices
A series of recently disclosed critical Bluetooth flaws that affect billions of Android, iOS, Windows and Linux devices have now been discovered...
-

 225
225Department of Homeland Security has Hacked the Boeing 757 remotely
This hack was not conducted in a laboratory, but on a 757 gathered at the airport in Atlantic City, N.J. And the...
-

 151
151According to the stats, Top 1% of the Rich People in the world can only benefit from AI
Right now, while artificial intelligence is concentrating on profit-generation, natural knowledge has proven to be higher than up to the task of...






