Vulnerabilities
-
 213
213All Versions of MS Office Affected with Critical Zero-day Vulnerability Allows Attackers Take Full Control of your System
A Critical MS Office Zero-day Remote Code Execution Vulnerability discovered in Microsoft Office that could allow attacker to take complete control of...
-
 212
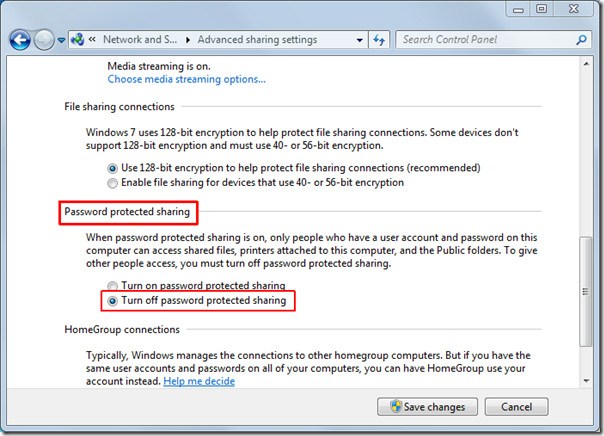
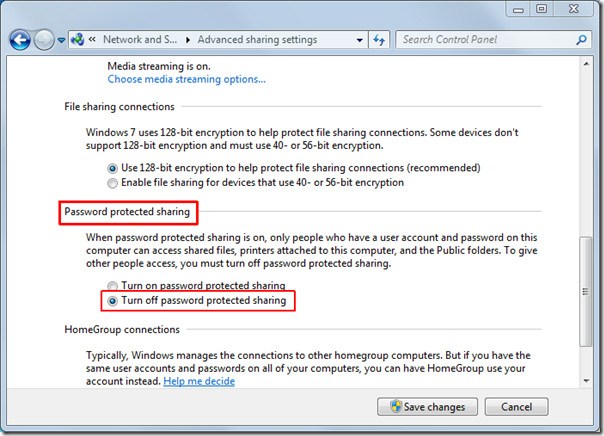
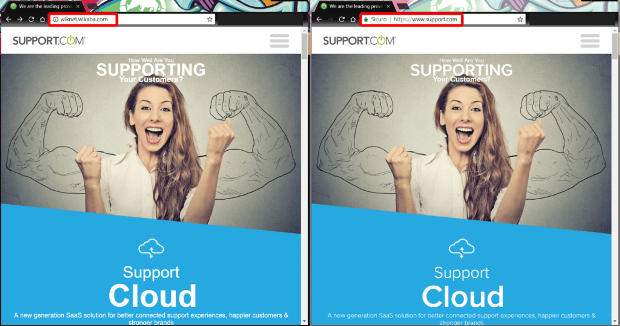
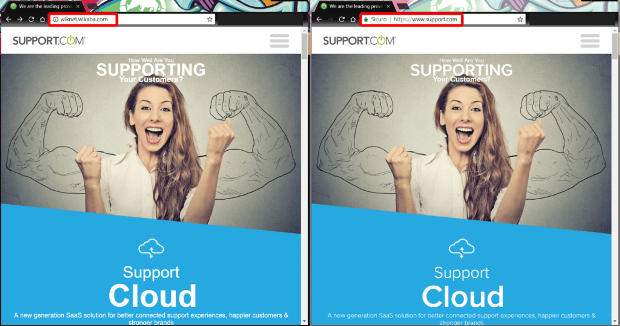
212Mysterious hack allows attackers stealing Windows login credentials without user interaction
Microsoft fixed a vulnerability that could allow hackers to steal Windows login credentials without any user interaction. Microsoft fixed a serious vulnerability...
-

 248
248HomeHack: How Hackers Could Have Taken Control of LG’s IoT Home Appliances
The second season of award-winning TV thriller Mr. Robotpremiered with a scene that sent shivers down the cybersecurity world’s spine. In uncomfortably realistic...
-

 154
154TWO CRITICAL VULNERABILITIES FOUND IN INMARSAT’S SATCOM SYSTEMS
UPDATE Researchers are warning of two critical vulnerabilities in global satellite telecommunications company Inmarsat’s SATCOM systems. The vulnerabilities impact thousands of customers running...
-

 168
168DUHK ATTACK EXPOSES GAPS IN FIPS CERTIFICATION
Despite the obligatory logo and clever name, this week’s assault on crypto, the so-called DUHK attack (Don’t Use Hardcoded Keys), isn’t likely to be...
-
 149
149Exclusive – CSE ZLab experts spotted a new Wonder botnet in the wild
The CSE CybSec Z-Lab Malware Lab spotted a new botnet, dubbed Wonder botnet, while it was investigating malicious code in the dark...
-

 193
193US warns of ongoing attacks on energy firms and critical infrastructure
The United States Department of Homeland Security (DHS) and the Federal Bureau of Investigation (FBI) have issued a warning that malicious hackers...
-

 338
338Hack These Apps And Earn $1,000 — Bug Bounty Program Launched By Google And HackerOne
Google has announced a bug bounty program called ‘Google Play Security Reward Program’ to detect flaws in Android apps. Security experts have the chance...
-
 203
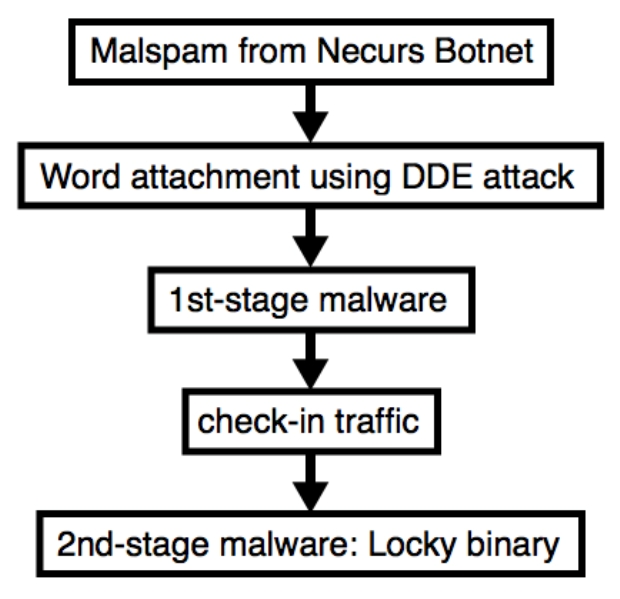
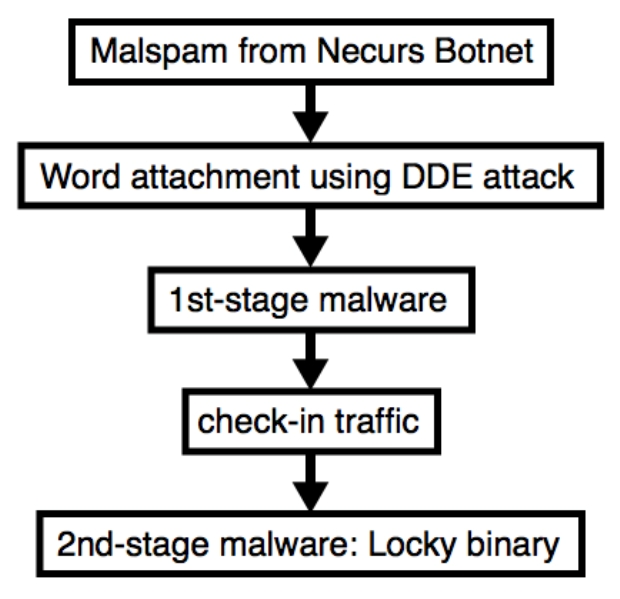
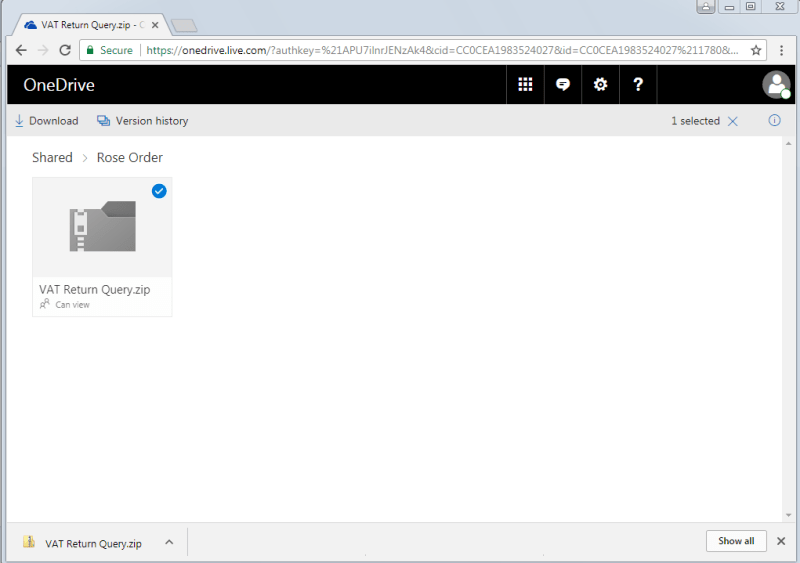
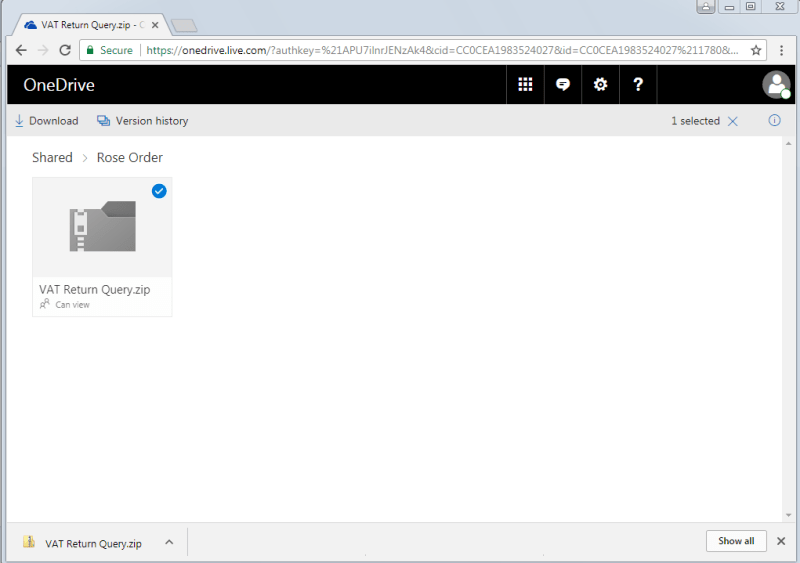
203Necurs Botnet malspam pushes Locky using DDE attack
I’ve seen Twitter traffic today about malspam from the Necurs Botnet pushing Locky ransomware using Word documents as their attachments. These Word...
-
 133
133Attacking a co-hosted VM: A hacker, a hammer and two memory modules
Row-hammer is hardware bug that can cause bit-flips in physical RAM. Mark Seaborn and Thomas Dullien were the first to exploit the DRAM row-hammer bug to...
-

 94
94Securing printed data in the ‘paperless’ office
While we are supposedly in the era of the paperless office, intentional leaks via printed documents remain very common and can be...
-

 113
113Microsoft never disclosed 2013 hack of secret vulnerability database
Database contained details required to carry out highly advanced software attacks. Hackers broke into Microsoft’s secret, internal bug-tracking database and stole information...
-

 205
205BlackOasis APT leverages new Flash zero-day exploit to deploy FinSpy
Security researchers from Kaspersky Labs spotted the BlackOasis APT group exploiting a new zero-day RCE vulnerability in Adobe Flash. Security researchers from...
-
 81
81Even With The Best Email Spoofing Defences in The World, HMRC is Spoofed
Even with the most advanced email protections in place and an entire government organization to support them, the bad actors were able...
-
 445
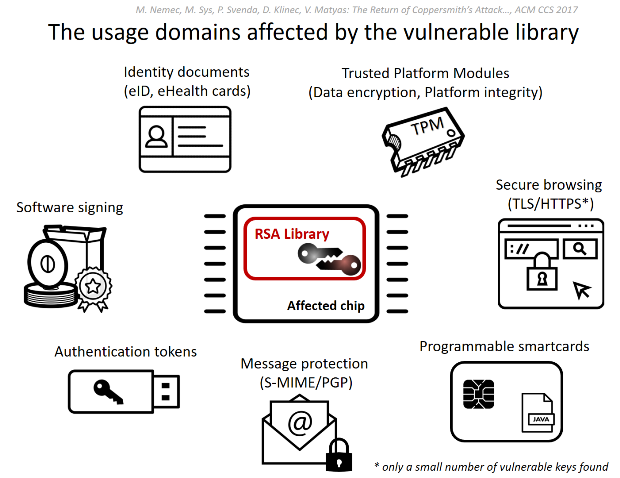
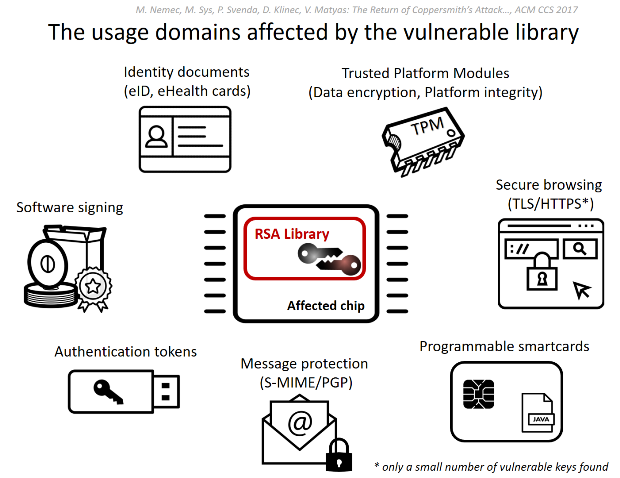
445ROCA: Vulnerable RSA generation (CVE-2017-15361)
A newly discovered vulnerability in generation of RSA keys used by a software library adopted in cryptographic smartcards, security tokens and other...
-

 263
263Key Reinstallation Attacks Breaking WPA2 by forcing nonce reuse
We discovered serious weaknesses in WPA2, a protocol that secures all modern protected Wi-Fi networks. An attacker within range of a victim...
-
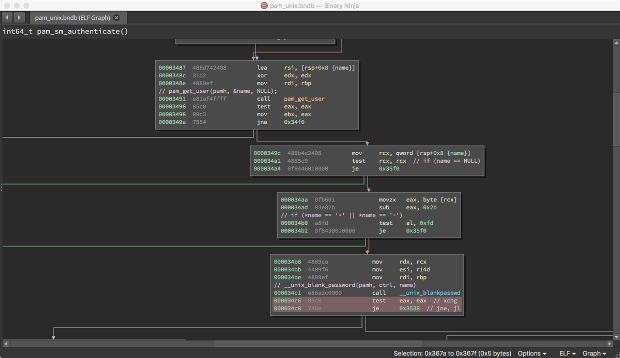
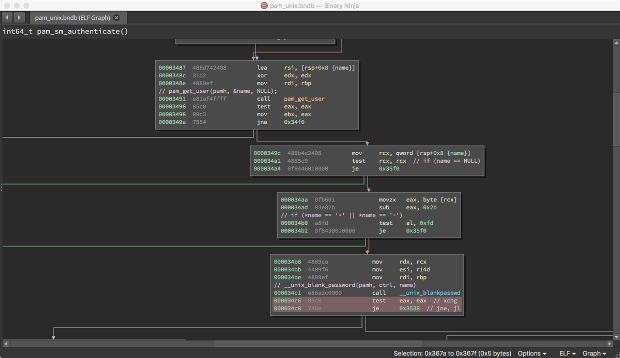
 156
156Linux kernel affected by a local privilege escalation vulnerability
Cisco issued a security advisory on a local privilege escalation vulnerability in the Linux Kernel, patch it as soon as possible. On...
-
 246
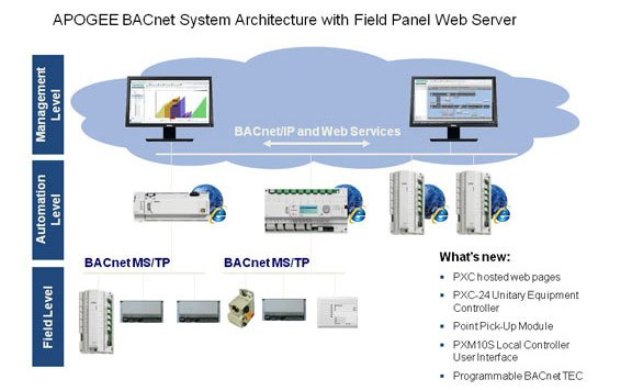
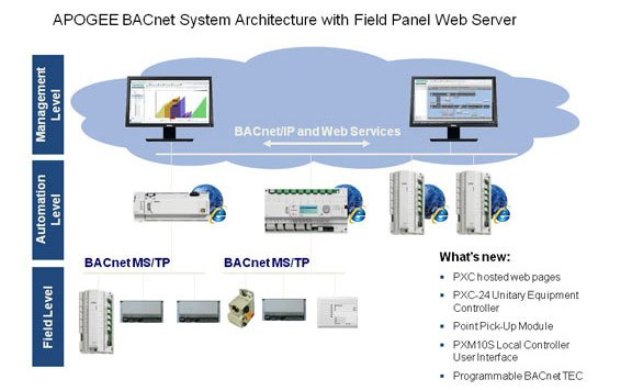
246Flaws in Siemens Building Automation Controllers open to hack. Fix them asap
Siemens has released a firmware update that addresses two vulnerabilities in its BACnet Field Panel building automation controllers. This week Siemens has...
-
 136
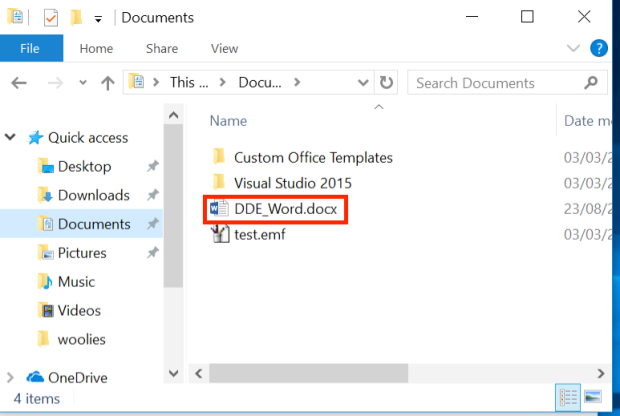
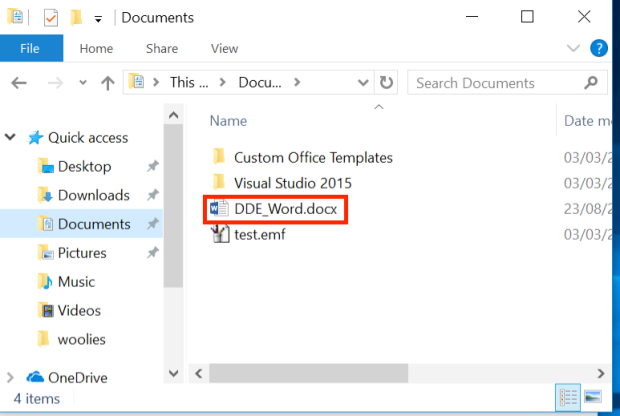
136Macro-less Code Exec in MSWord
In our context DDE works by executing an application, that will provide the data (data provider). In a previous post1 We discussed...
-
 262
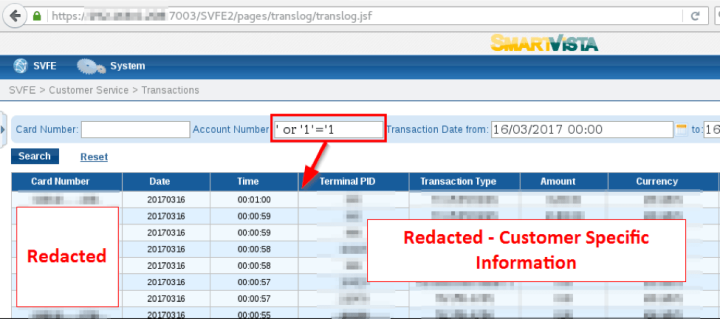
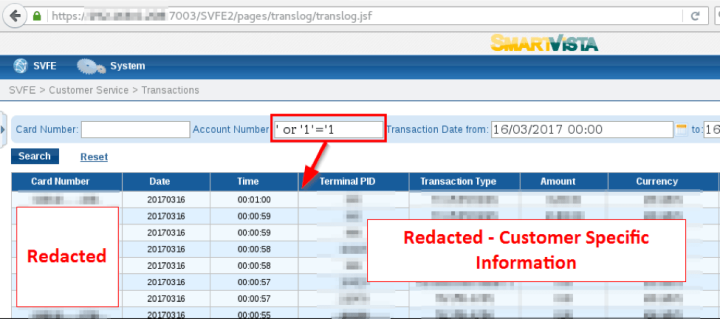
262Swiss BPC banking software SmartVista is vulnerable to SQL Injection attacks
The suite of payment infrastructure and management systems SmartVista created by the BPC Group is vulnerable to SQL Injection attacks. Researchers at...
-

 206
206A Bug Has No Name: Multiple Heap Buffer Overflows In the Windows DNS Client
CVE-2017-11779 fixed by Microsoft in October of 2017, covers multiple memory corruption vulnerabilities in the Windows DNS client. The issues affect computers running Windows...






