Vulnerabilities
-

 146
146Experimental Mozilla Send service allows users share encrypted copy of huge files
Mozilla Send service allows users to make an encrypted copy of a local file, store it on a remote server, and share...
-

 104
104Roughly 175,000 Chinese Internet Connected security cameras can be easily hacked
An estimated 175,000 Internet of Things (IoT) connected security cameras manufactured by Shenzhen Neo Electronics are vulnerable to cyber attacks. According to...
-
 188
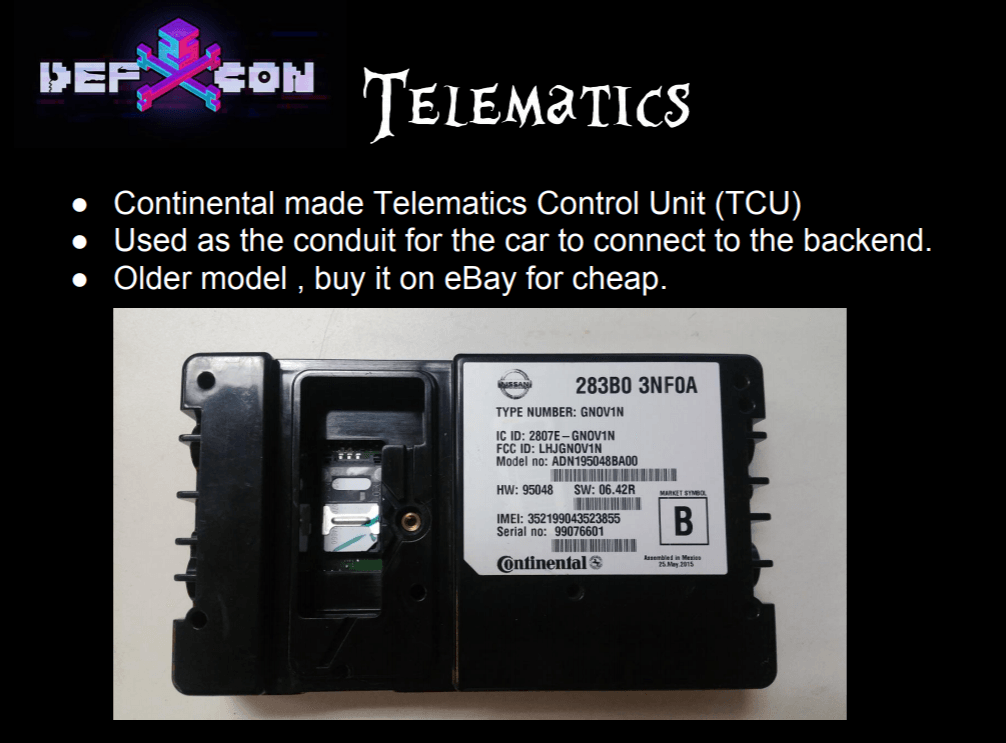
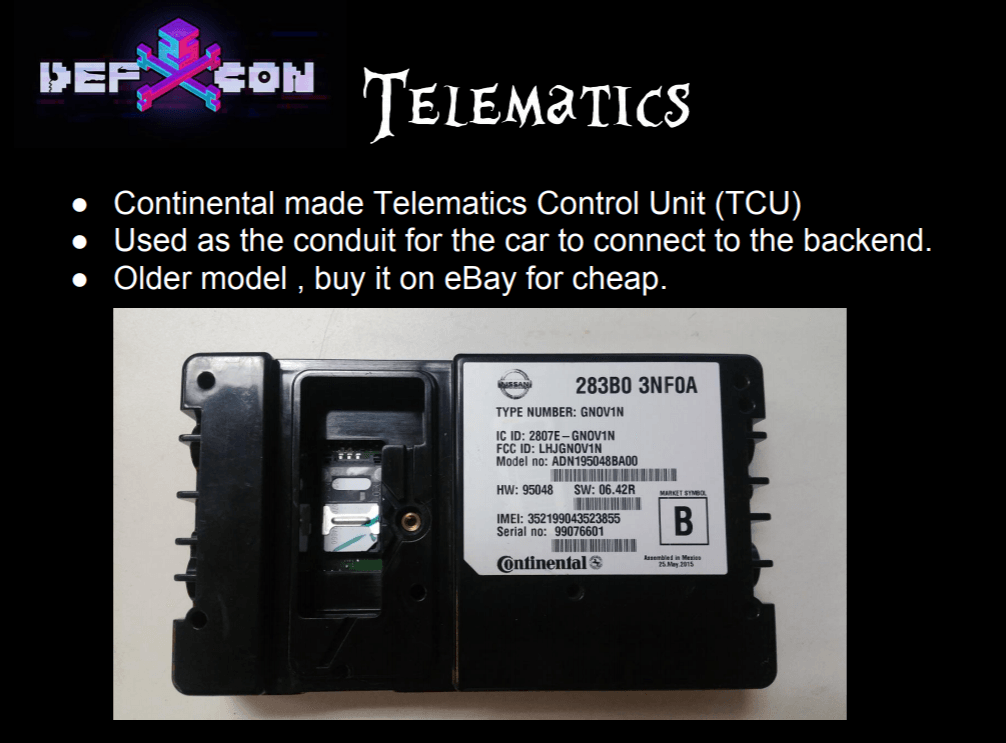
188Security flaws affect TCUs used in BMW, Ford, Infiniti, and Nissan vehicles
Three security researchers have discovered security vulnerabilities in the telematics control units (TCUs) used in BMW, Ford, Infiniti, and Nissan vehicles. Three...
-
 141
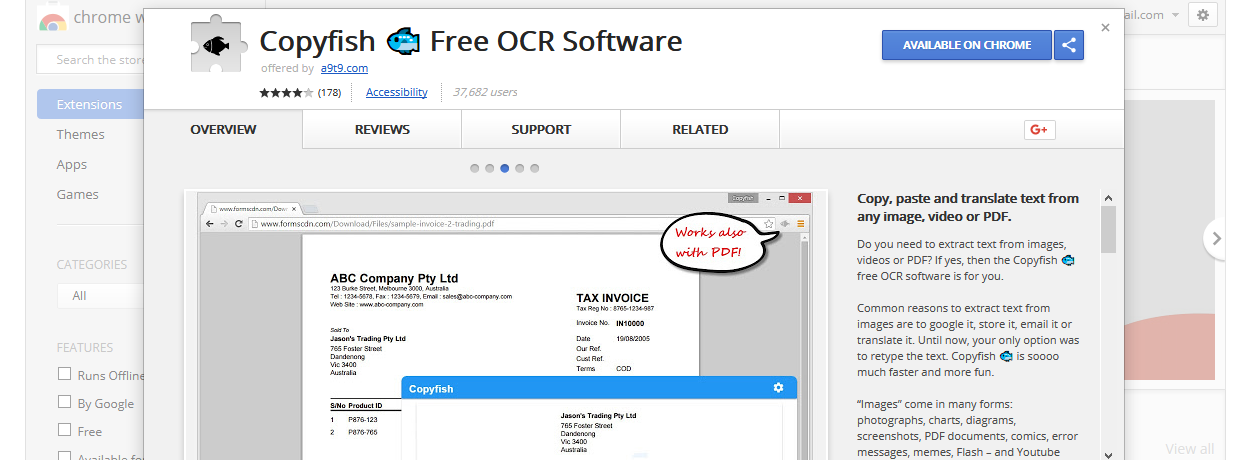
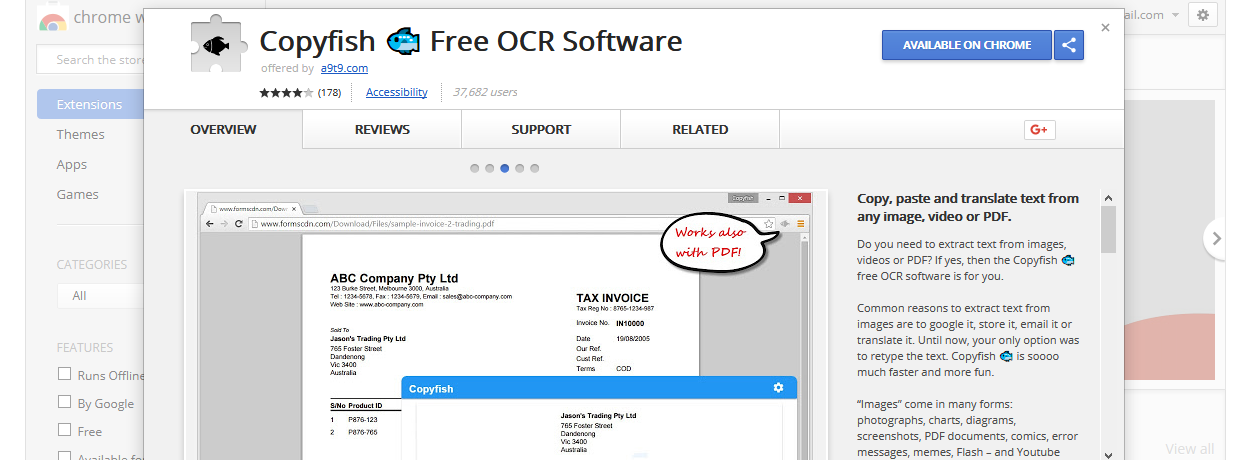
141Copyfish Chrome Extension Hijacked to Show Adware
On Friday, an unknown hacker hijacked the Copyfish Chrome extension from its original authors and pushed an update that inserted ads in people’s web...
-

 104
104BrickerBot Dev Claims Cyber-Attack That Affected Over 60,000 Indian Modems
EXCLUSIVE — The author of the BrickerBot malware has claimed a cyber-attack that took place in various Indian states and has caused...
-

 99
99Virgin America Hacked, Employee Passwords and Personal Information Compromised
Airline confirms hack that took place on March 13. Virgin America has confirmed in a letter sent to employees that its network was compromised by...
-

 150
150Security Flaws In “Smart” Car Wash Can Be Exploited to Cause Physical Injuries
Two US security researchers have found vulnerabilities in smart car wash solutions sold by PDQ, a US-based vendor of Internet-connected car wash...
-
 242
242ATTACK USES DOCKER CONTAINERS TO HIDE, PERSIST, PLANT MALWARE
LAS VEGAS—A novel attack vector allows for adversaries to abuse the Docker API to hide malware on targeted systems, and even execute...
-

 194
194Three Vendors Decline to Patch Vulnerabilities in Nuclear Radiation Monitors
Ruben Santamarta, a security researcher for IOActive, has found various vulnerabilities in nuclear radiation monitoring equipment from three vendors, who when contacted...
-

 200
200Chinese Researchers Hack Tesla Model X in Impressive Video
Security researchers from Chinese security firm Tencent Keen Security Lab have found and helped fix several vulnerabilities in Tesla Model X cars...
-
 135
135THE ‘CLOAK & DAGGER’ ATTACK THAT BEDEVILED ANDROID FOR MONTHS
USUALLY VULNERABILITIES IN software are accidents or mistakes—flaws that shouldn’t be there. But they can also stem from unintended consequences of features working...
-

 307
307Security Expert Hacks ATM By Drilling A Hole
ATM can be hacked by just drilling a hole ATMs have always had a target painted on their backs. Just last year,...
-

 136
136Crooks Reused Passwords on the Dark Web, so Dutch Police Hijacked Their Accounts
Dutch Police are aggressively going after Dark Web vendors using data they collected from the recently seized Hansa Market. Currently, the infosec...
-
 235
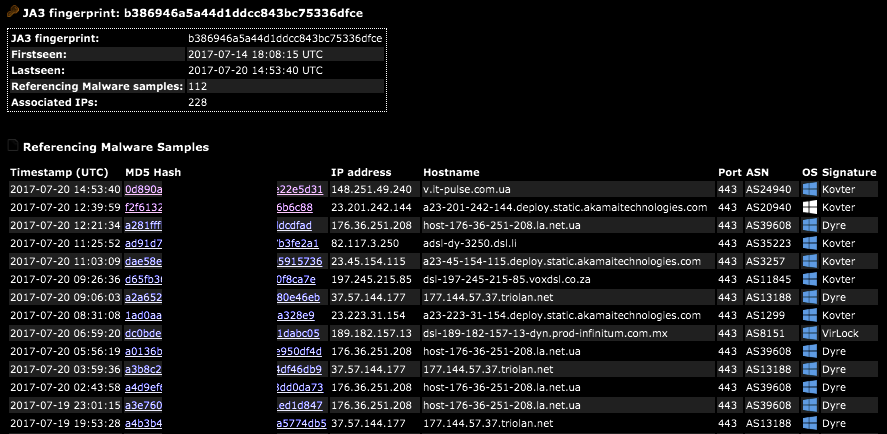
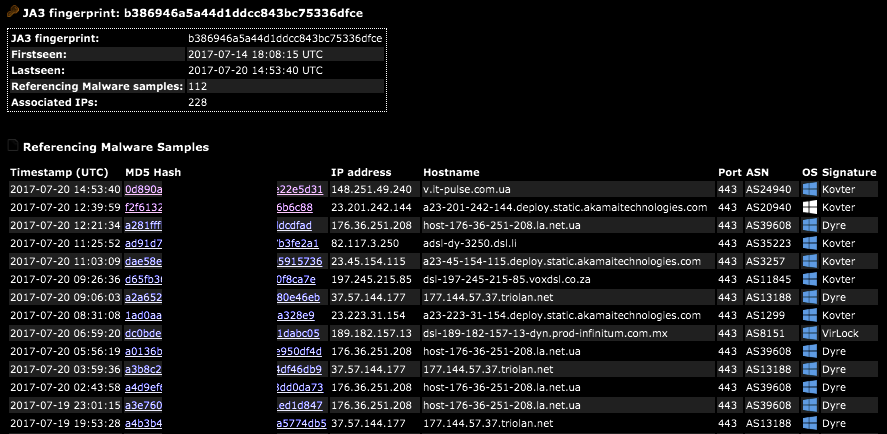
235SSL/TLS Client Fingerprinting for Malware Detection
A JA3 hash represents the fingerprint of an SSL/TLS client application as detected via a network sensor or device, such as Bro...
-

 91
91Experts detailed the new Operation Wilted Tulip campaign of the CopyKittens APT
Researchers from ClearSky and Trend Micro uncovered a new massive cyber espionage campaign conducted by CopyKittens dubbed ‘Operation Wilted Tulip’ A joint...
-

 105
105NOVEL ATTACK TRICKS SERVERS TO CACHE, EXPOSE PERSONAL DATA
LAS VEGAS—Researcher Omer Gil has devised a way to trick a web server into caching pages and exposing personal data. The so-called...
-
 242
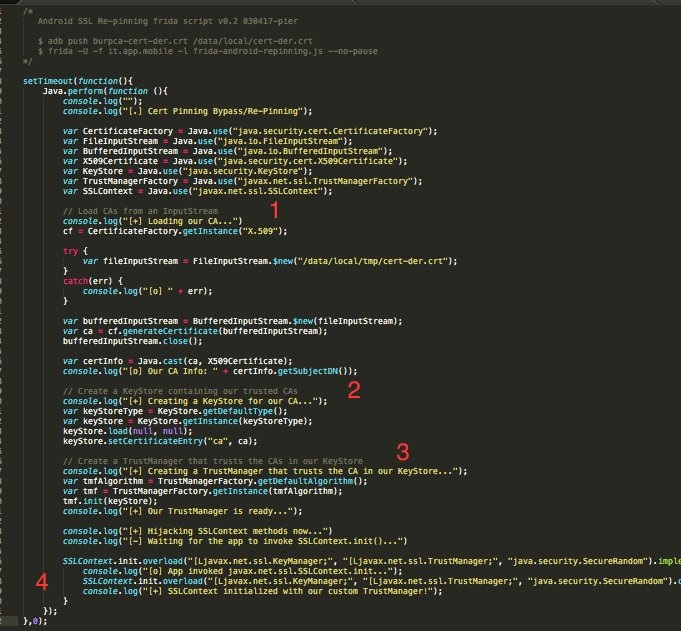
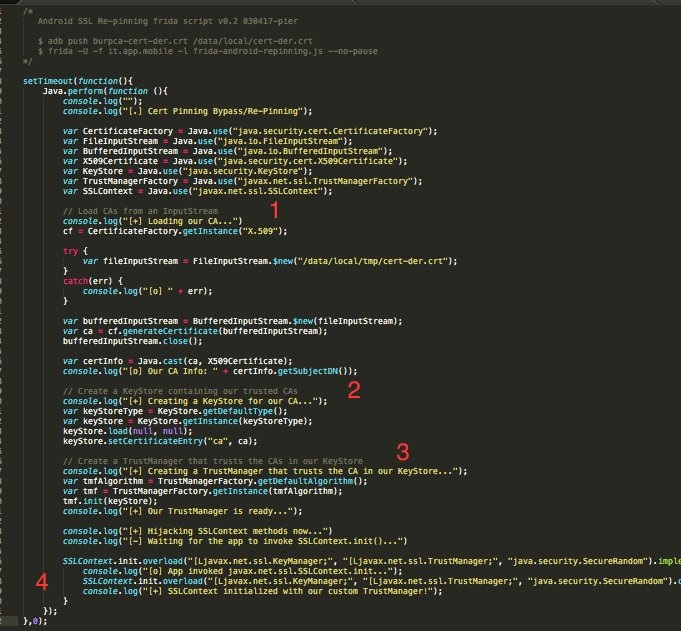
242Universal Android SSL Pinning bypass with Frida
Android SSL Re-Pinning Two kinds of SSL Pinning implementations can be found in Android apps: the home-made and the proper one. The...
-

 182
182Hacker Steals $8.4 Million Worth of Ethereum From Veritaseum Platform
Veritaseum has confirmed today that a hacker stole $8.4 million from the platform’s ICO on Sunday, July 23. This is the second...
-
 251
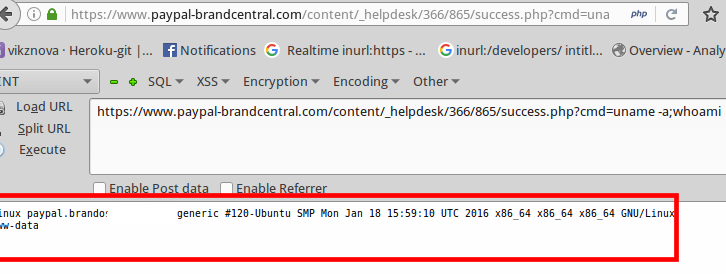
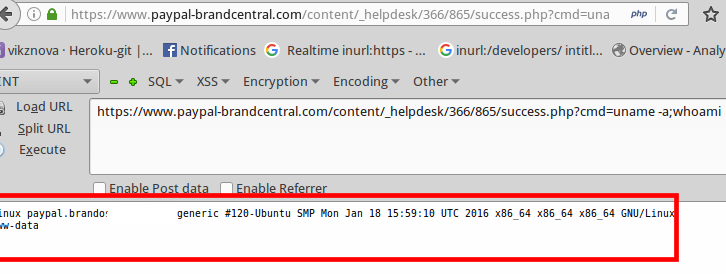
251Expert exploited an unrestricted File Upload flaw in a PayPal Server to remotely execute code
The security researcher Vikas Anil Sharma exploited an unrestricted File Upload vulnerability in a PayPal Server to remotely execute code. The security researcher...
-

 176
176Microsoft sued Fancy Bear to gain control of the domains used in the cyber espionage campaigns
Microsoft used the lawsuit to disrupt a large number of cyber espionage campaigns conducted by infamous Fancy Bear APT hacking group We...
-

 163
163Shut Up and Hack
I wrote most of the code of this small project, called ‘injectAllTheThings’, a while ago when I started developing custom tools for...






