Vulnerabilities
-
 171
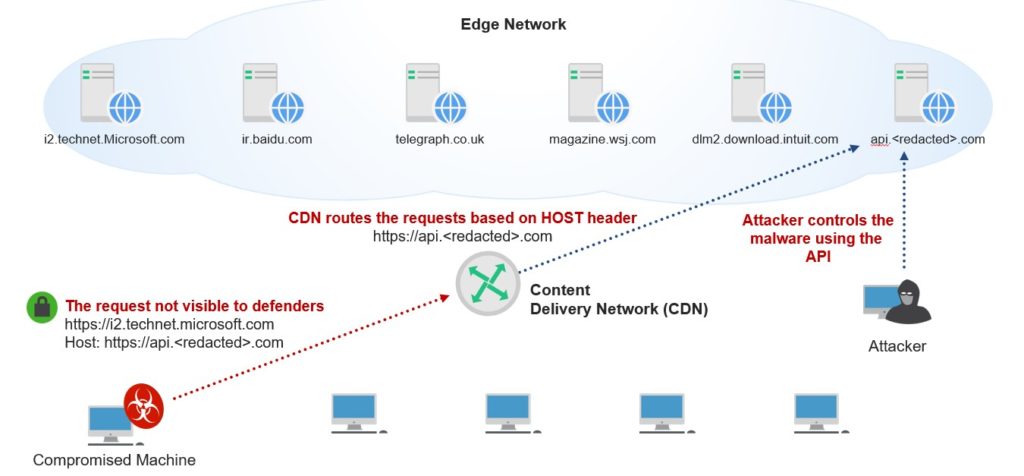
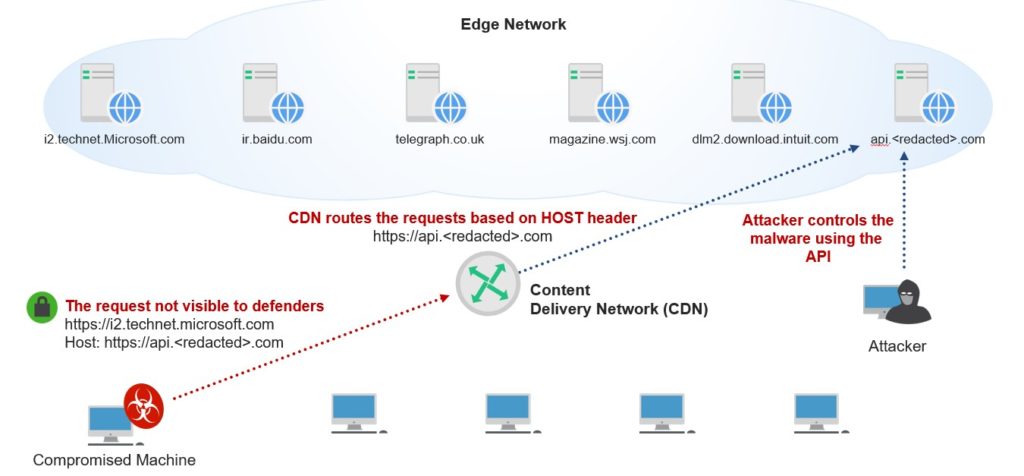
171Implementing Malware Command and Control Using Major CDNs and High-Traffic Domains
In this blog post, we will present a new technique for domain fronting, which enables attackers to abuse Content Delivery Networks (CDNs) to...
-

 184
184Coding Library Vulnerability May Trickle Down to Thousands of IoT Devices
A vulnerability codenamed Devil’s Ivy is putting thousands of Internet-connected devices at risk of hacking. Discovered by security researchers from Senrio, the...
-
 106
106Home Security System Fails at Being Secure, Opens Homes to Hacking & Burglaries
The maker of a smart home security system has failed to patch five security issues in the firmware of his product. These...
-

 150
150For the second time in the year, experts found a flaw in Cisco WebEx Extension
For the second time in a year, a highly critical remote code execution vulnerability was found in the Cisco WebEx Extension. For the second...
-
 223
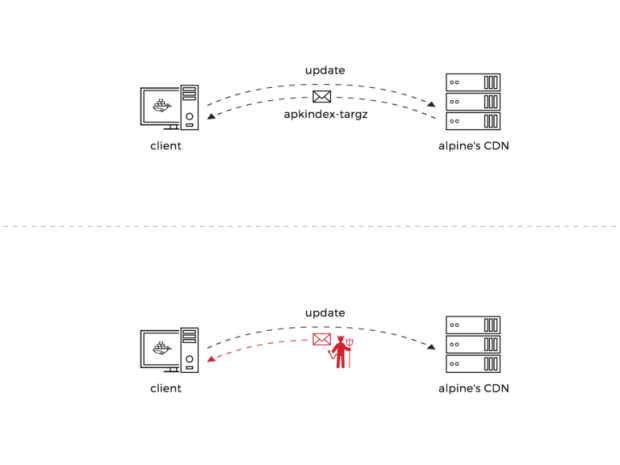
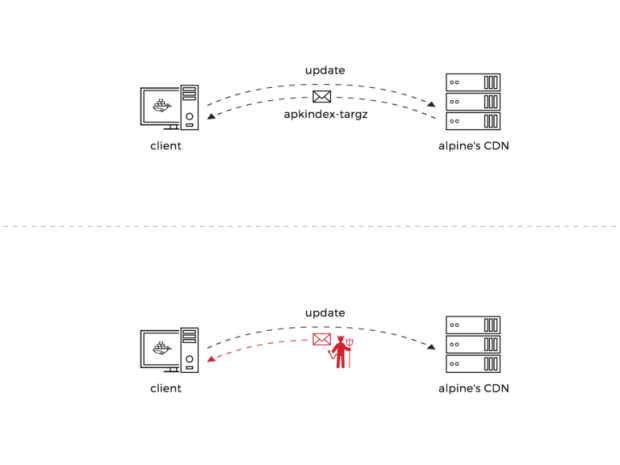
223Alpine Linux: From vulnerability discovery to code execution (Pt 1 of 2)
I recently uncovered two critical vulnerabilities in Alpine Linux’s package manager, assigned CVE-2017-9669 and CVE-2017-9671. These vulnerabilities could potentially lead to an...
-

 137
137CISCO issues security patches for nine serious RCEs in SNMP subsystem in IOS and IOS XE
Cisco has fixed nine serious remote code execution flaws in the SNMP subsystem running in all the releases of IOS and IOS XE software....
-
 132
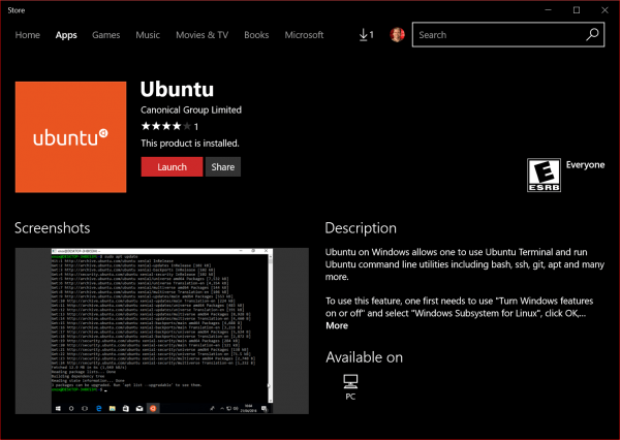
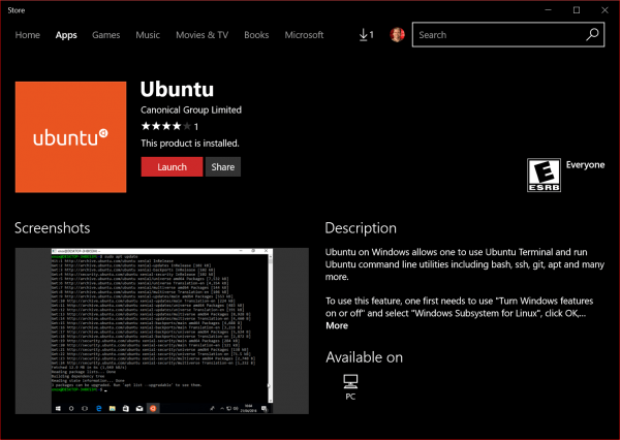
132Ubuntu Linux distro is now available for Windows 10
Microsoft announced that Canonical’s Ubuntu Linux Distro is now available in the Windows Store and can be installed on any Windows Insider...
-
 133
13321-Year-Old Bug in Kerberos Protocol Gets Patch in Windows, Linux
Two implementations of the Kerberos authentication protocol received patches this week against a vulnerability that allowed a threat actor to bypass authentication...
-

 202
202App Finds More Than 50,000 Computers Vulnerable to ETERNALBLUE Exploit
The developer of a tool named Eternal Blues that scans for computers vulnerable to the NSA’s ETERNALBLUE exploit has published statistics gathered...
-
 110
110VULNERABILITIES EXPOSE ORACLE OAM 10G TO REMOTE SESSION HIJACKING
Oracle’s next quarterly Critical Patch Update is slated for July 18, but two vulnerabilities in an older version of the company’s Oracle...
-
 224
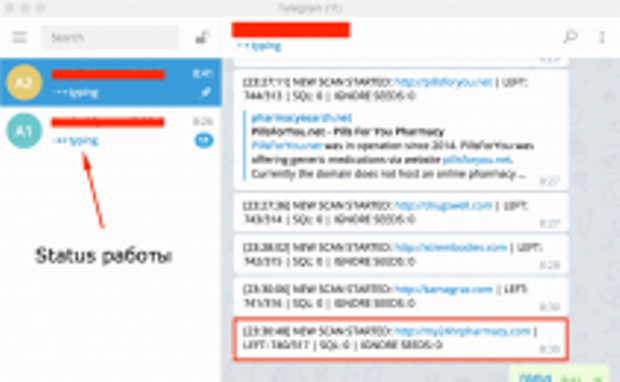
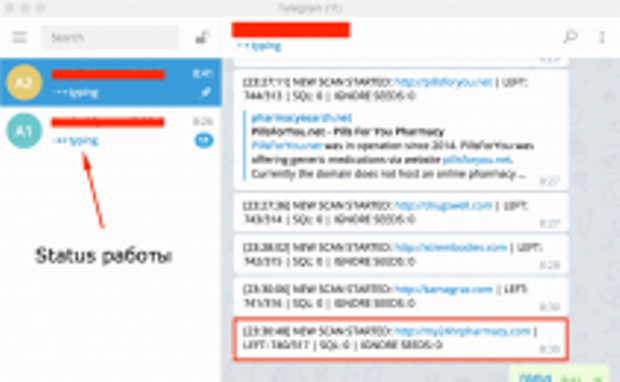
224Telegram-Based SQL Injection Scanner Available for $500 on Hacking Forum
A new tool is making the rounds on the criminal underground. Called Katyusha Scanner, this is a hybrid between a classic SQL injection...
-

 244
244TELEGRAM-CONTROLLED HACKING TOOL TARGETS SQL INJECTION AT SCALE
A black market hacking tool has the potential to rapidly conduct website scans for SQL injection vulnerabilities at a large scale, all...
-

 199
199NTLM Relay Attacks Still Causing Problems in 2017
Microsoft’s July 2017 Patch Tuesday includes a fix for an issue with the NT LAN Manager (NTLM) Authentication Protocol that can be...
-

 290
290Adobe patches Multiple Security Flaw in Flash Player and Adobe Connect
Adobe releases patches for critical security flaws which allows attackers to control your system. This bundle applies for Windows, Macintosh, Linux and...
-

 196
196Man Pleads Guilty to Manipulating Lottery Winning Tickets via Hacked Computer
One of the biggest lottery scams in the history of the US is coming to a close as the mastermind behind the...
-

 152
152iPhone, Android Exposed to Broadpwn Security Flaw, Google Patch Available
The world’s two most popular mobile platforms are affected by a security vulnerability called Broadpwn and which allows attackers to gain remote code execution...
-

 287
287The Weak Bug – Exploiting a Heap Overflow in VMware
Introduction In march 2017, I took part in the pwn2own contest with team Chaitin Security Research Lab. The target I was focused on was...
-

 145
145BroadPwn potentially expose to hack millions of Android devices using Broadcom Wi-Fi Chip
Google warned of a serious flaw dubbed BroadPwn in some Broadcom Wi-Fi chipsets that potentially impacts millions of Android devices. Google published...
-
 246
246Perl devs fix an important flaw in DBD—MySQL that affects encryption between client and server
Perl development team solved a flaw in DBD—MySQL in some configurations that wasn’t enforcing encryption allowing an attacker to power MiTM attacks....
-

 179
179Fourth Largest Cryptocurrency Exchange Was Hacked. Users Lose Ethereum & Bitcoin
Bithumb, the world’s fourth largest cryptocurrency exchange by volume, confirmed a security incident during which an unknown hacker was able to make...
-
 237
237Multiple Vulnerabilities with Pre-installed Packages open Dell systems to Hack
Security experts from Talos discovered a couple of vulnerabilities in Dell Precision software which allow attackers to disable security mechanisms, escalate privileges...






