Vulnerabilities
-
 113
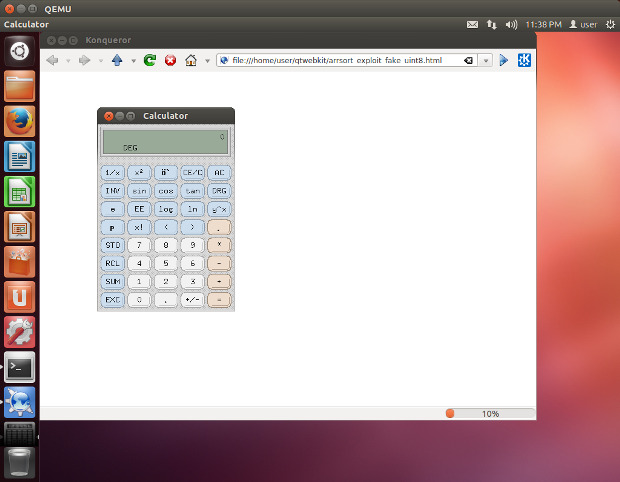
113Hacking everything, by Chris Evans / scarybeasts
Ode to the use-after-free: one vulnerable function, a thousand possibilities Overview This post explores an old but wonderful vulnerability that enables us...
-
 207
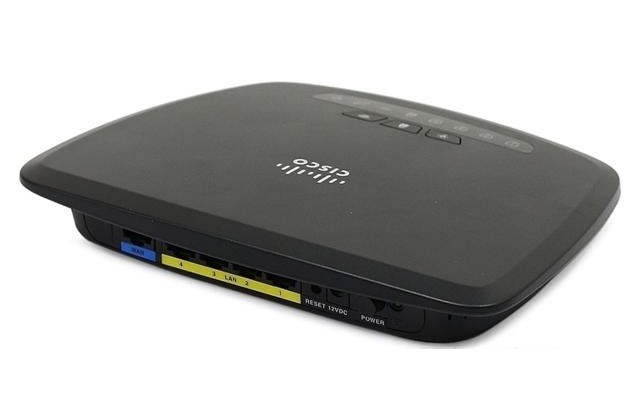
207Cisco fixes a critical flaw in CISCO CVR100W Wireless-N VPN Small Business Routers
Cisco released a firmware update to fix a critical buffer overflow vulnerability in CISCO CVR100W Wireless-N VPN Small Business Routers. Cisco has...
-
 168
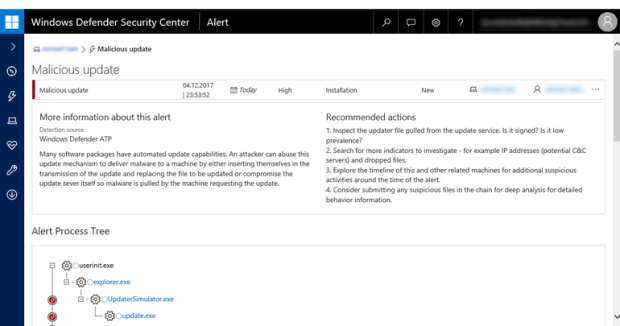
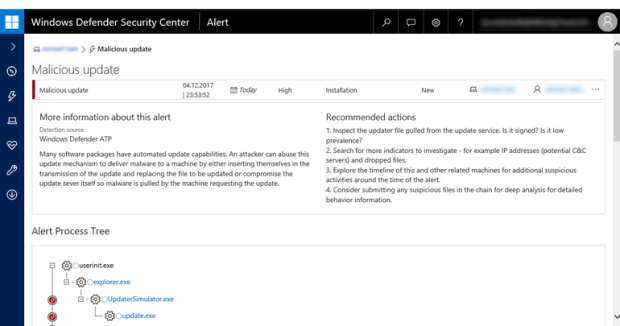
168Windows Defender ATP thwarts Operation WilySupply software supply chain cyberattack
Several weeks ago, the Windows Defender Advanced Threat Protection (Windows Defender ATP) research team noticed security alerts that demonstrated an intriguing attack...
-

 117
117WordPress Zero-Day Could Expose Password Reset Emails
Polish security expert Dawid Golunski has discovered a zero-day in the WordPress password reset mechanism that would allow an attacker to obtain...
-

 201
201PowerShell Injection with Diskless Payload Persistence and Bypass Techniques
PowerShell continues to be the tool of choice for defenders, IT administrators, and hackers. The extensibility, support, and ability to have a...
-
 130
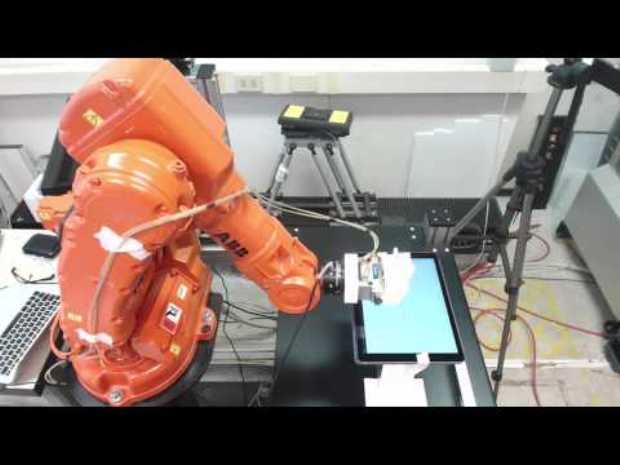
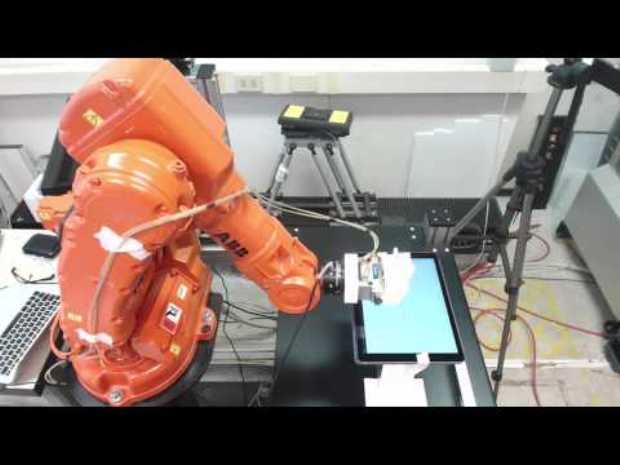
130Watch Researchers Hack an Industrial Robot and Sabotage Production
There is an insane amount of industrial robots connected to the Internet, and even worse, thousands are left with no form of...
-
 265
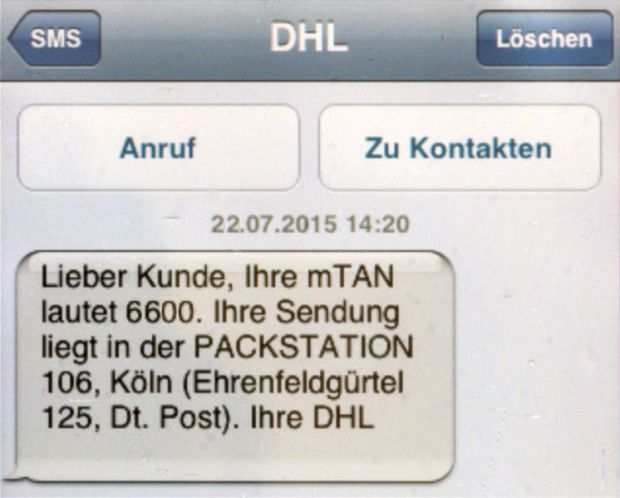
265Thieves drain 2fa-protected bank accounts by abusing SS7 routing protocol
The same weakness could be used to eavesdrop on calls and track users’ locations. A known security hole in the networking protocol...
-
 139
139Chinese TA459 APT exploits CVE-2017-0199 flaw to target Financial firms
Malware researchers at security firm ProofPoint reported the Chinese TA459 APT has exploited the CVE-2017-0199 vulnerability to target Financial firms. The notorious...
-

 201
201Information Security Practices of Aadhaar – 135 Million Indian government payment card details leaked
A CIS study estimated number of Aadhaar numbers leaked through 4 gov portals could be around 135 million and 100M bank account...
-

 140
140Hyundai Patches Mobile App Flaws That Allow Hackers to Steal Cars
Hyundai has patched a security flaw in the Blue Link mobile application that exposed sensitive information, which hackers could have used to...
-
 215
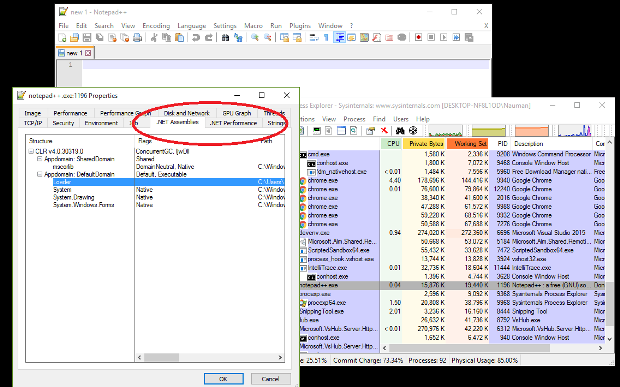
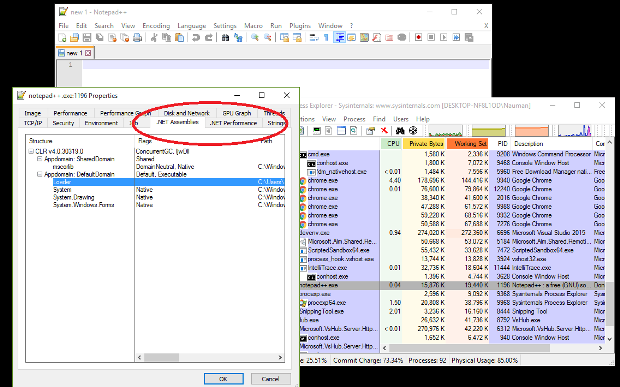
215DLL Injection Using LoadLibrary in C
Tutorials on Windows DLL injections in C have noticable gaps in what they explain. This blog post plus the comments on my...
-
 170
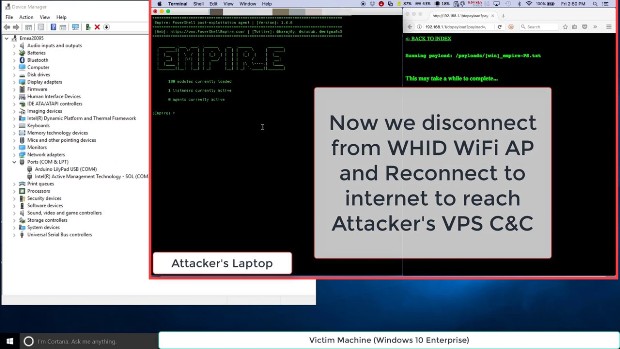
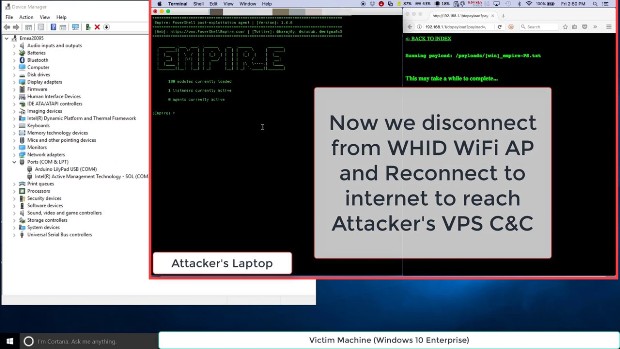
170WHID Injector: How to Bring HID Attacks to the Next Level
Luca Bongiorni was working on a cheap and dedicated hardware that he could remotely control (i.e. over WiFi or BLE), that is...
-
 193
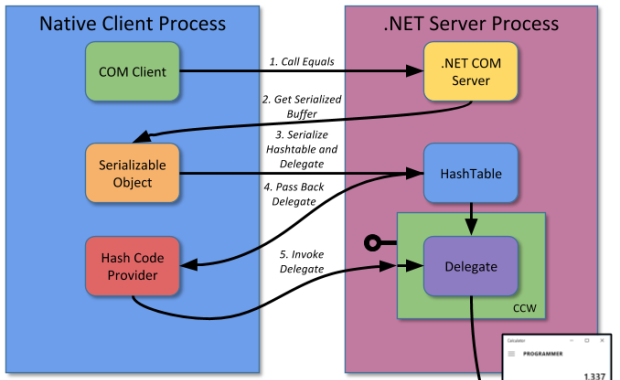
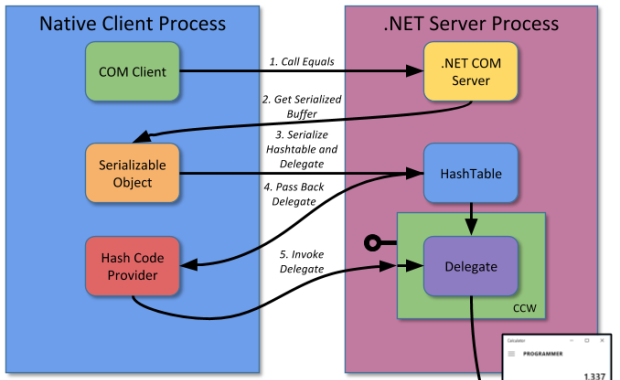
193Exploiting .NET Managed DCOM
One of the more interesting classes of security vulnerabilities are those affecting interoperability technology. This is because these vulnerabilities typically affect any...
-

 278
278WIKILEAKS REVEALS CIA TOOL ‘SCRIBBLES’ FOR DOCUMENT TRACKING
WikiLeaks released details on what it said is a Central Intelligence Agency document tracking program called Scribbles, part of the agency’s effort to...
-

 233
233Expert discovered online data belonging to the trading firm AMP
Security expert Chris Vickery reported a data breach at online trading firm AMP that exposed customer credit reports, and Social Security numbers....
-

 148
148Hacker Leaks “Orange Is the New Black” Season 5 Episodes After Netflix Extortion Attempt Fails
A hacker (or hacker group) known as The Dark Overlord (TDO) has leaked the first ten episodes of season 5 of the...
-
 158
158Nomx, the “most secure” email service, can be easily hacked, say researchers
I was recently invited to take part in some research by BBC Click, alongside Professor Alan Woodward, to analyse a device that...
-
 220
220Lawsuit: Fox News group hacked, surveilled, and stalked ex-host Andrea Tantaros
Lawsuit: After a sexual harassment claim, Fox News planted spyware on ex-host’s computer. Comparing their actions to the plot this season on...
-

 197
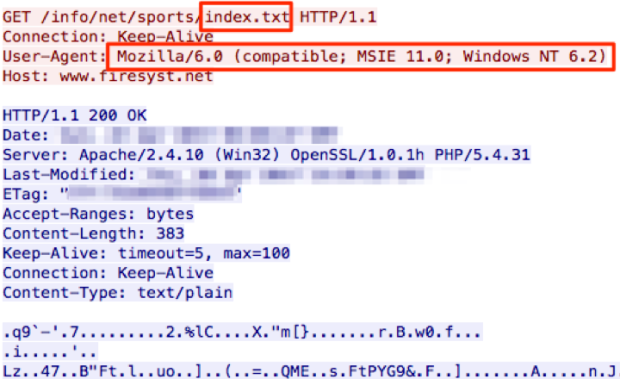
197Cracking APT28 traffic in a few seconds
Security experts from security firm Redsocks published an interesting report on how to crack APT28 traffic in a few seconds. Introduction APT28...
-
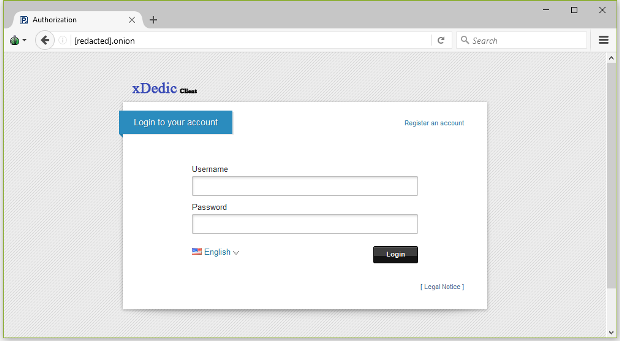
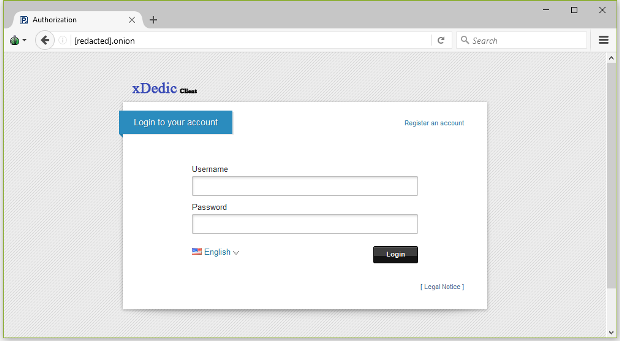 108
108Over 85,000 Hacked RDP Servers Still Available for Sale on xDedic Marketplace
There are over 85,000 RDP servers available for sale or rent via xDedic, a marketplace for selling or renting hacked servers that...
-

 162
162Security vulnerabilities in Hyundai Blue Link mobile app allowed hackers to steal vehicles
Security vulnerabilities in the Hyundai Blue Link mobile apps allowed hackers to steal vehicles, the car maker fixed them. Security vulnerabilities in...






