Vulnerabilities
-

 203
203Every website that uses jQuery Mobile, and has any open redirect is vulnerable to XSS
Every website that uses jQuery Mobile, and has any open redirect anywhere is vulnerable to cross-site scripting (XSS) attacks. The jQuery Foundation’s...
-

 85
85DynA-Crypt not only Encrypts Your Files, but Also Steals Your Info
A new ransomware called DynA-Crypt was discovered by GData malware analyst Karsten Hahn that not only encrypts your data, but also tries to steal a...
-
 149
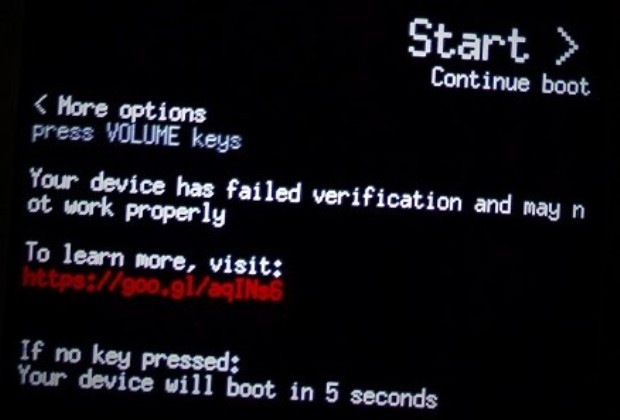
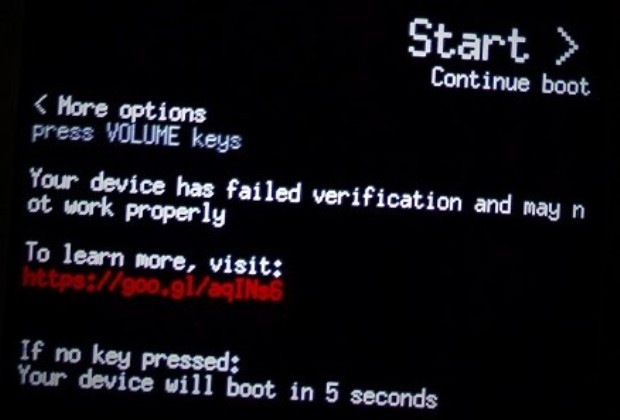
149Owning a Locked OnePlus 3/3T: Bootloader Vulnerabilities
In this blog post I disclose two vulnerabilities in the OnePlus 3/3T bootloader. The first one, CVE-2017-5626, is a critical severity vulnerability...
-

 267
267Valve is going to fix a serious vulnerability in Steam online gaming platform
The online game platform Steam is fixing a serious bug that could be exploited to redirect users to malicious websites and take...
-

 78
78ATTACKERS CAPITALIZING ON UNPATCHED WORDPRESS SITES
Attackers didn’t wait long to capitalize on laggards slow in updating their WordPress sites to patch a critical content injection vulnerability addressed...
-

 222
222A rash of invisible, fileless malware is infecting banks around the globe
Once the province of nation-sponsored hackers, in-memory malware goes mainstream. Two years ago, researchers at Moscow-based Kaspersky Lab discovered their corporate network...
-
 144
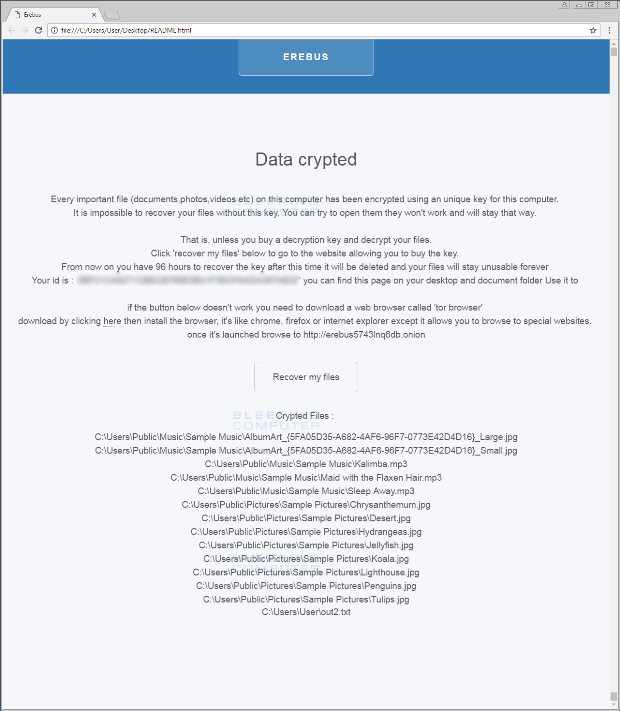
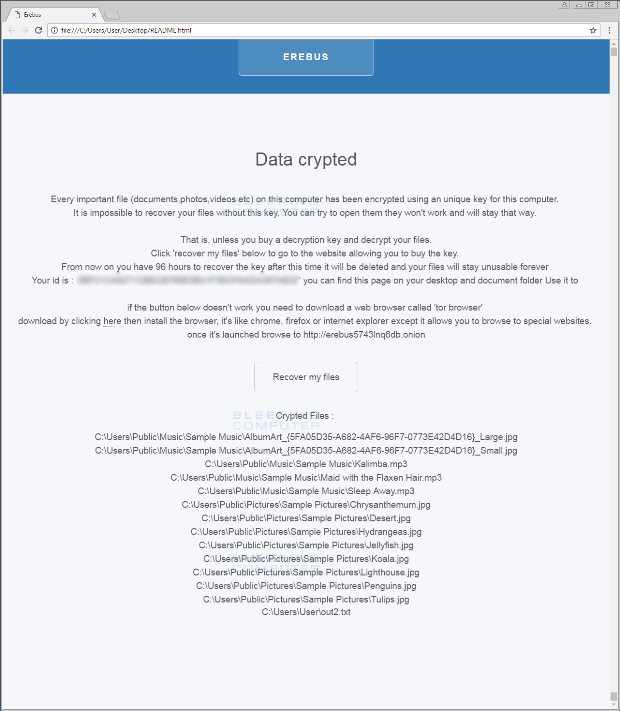
144Erebus Ransomware Utilizes a UAC Bypass and Request a $90 Ransom Payment
A sample of a potentially new ransomware called Erebus has been discovered by MalwareHunterTeam on VirusTotal. I say that this is a potentially...
-

 168
168New BSOD Devil Comes From The Internet And Crashes Your Windows 10, 8, 7, XP
Short Bytes: A security researcher, who goes by the username lgandx, reported a severe vulnerability affecting Windows versions ranging from Windows XP to...
-

 170
170Denuvo forgets to secure server, leaks years of messages from game makers
Massive log file includes user complaints, apparently legitimate developer requests. The developers at Denuvo have been in the news thanks to cracks against...
-

 166
166Important Kernel Updates Patch 7 Vulnerabilities in All Supported Ubuntu OSes
Canonical announced a few hours ago the availability of new kernel updates for all supported Ubuntu Linux operating systems, patching a total...
-

 307
307Critical Cisco security Authentication Bypass Vulnerability leads to hack thousands of home routers
Remote unauthenticated control over a vulnerable ISP’s gear, could allow an attacker to log into the software as an administrator and remotely...
-

 98
98Radio stations that ignored major vulnerability start playing anti-Trump song
Vulnerability had been known for nearly a year, flared up shortly after inauguration. A certain model of Low Power FM radio transmitter...
-

 196
196Popular hacking toolkit Metasploit adds hardware testing capabilities
The Metasploit hacking toolkit now includes a new hardware bridge that makes it easier for users to analyze hardware devices. The popular...
-

 287
287WordPress Team Secretly Fixed A Zero-Day Critical Content Injection Vulnerability
The WordPress security team revealed that they’ve secretly fixed a zero-day vulnerability in the WordPress CMS REST API.The vulnerability in this case...
-

 190
190Content Injection Vulnerability in WordPress 4.7.0 or 4.7.1
As part of a vulnerability research project for our Sucuri Firewall (WAF), we have been auditing multiple open source projects looking for...
-

 229
229Windows DRM Files Used to Decloak Tor Browser Users
Downloading and trying to open Windows DRM-protected files can deanonymize Tor Browser users and reveal their real IP addresses, security researchers from...
-

 206
206Pentagon Servers Flawed, Easy to Hack
The Pentagon has known about the problem for 8 months. The U.S. Department of Defense could be at risk of being attacked...
-
 177
177LATEST UBUNTU UPDATE INCLUDES OPENSSL FIXES
Ubuntu users are being urged to update their operating systems to address a handful of recently patched OpenSSL vulnerabilities which affect Ubuntu and its...
-

 117
117Mobile Security Firm Wants to Buy Expired Zero-Days
Zimperium, the mobile security company that discovered the Stagefright bug in the summer of 2015, announced yesterday its intention to buy fully-working...
-
 100
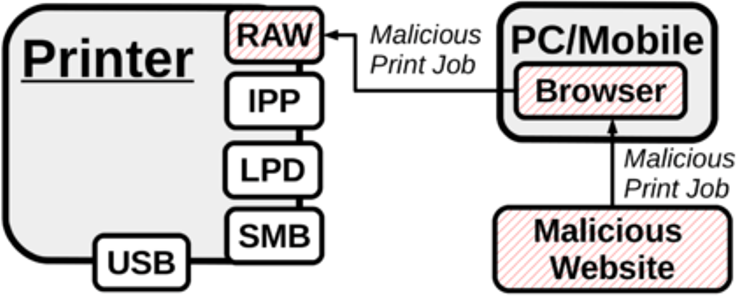
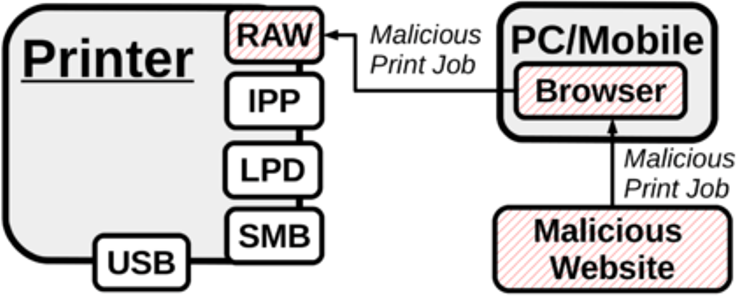
100Hacking printers exploiting Cross-site printing (XSP) attacks
A group of researchers from the University Alliance Ruhr has found a cross-site printing bug in the old PostScript language. Popular printer models...
-
 271
271Serious Linux vulnerabilities “Dirty COW” is a privilege escalation vulnerability in the Linux Kernel – Linux users urged to protect
Recently ,there have been some serious vulnerabilities found in various Linux systems. Whilst OS vulnerabilities are a common occurrence. The ‘Dirty Cow’...






