Vulnerabilities
-

 149
149Hackers demonstrate how to hack Samsung SmartCam
Researchers Exploitee.rs discovered a flaw in Samsung SmartCam IP cameras that could be exploited to execute commands and hijack vulnerable devices. Samsung...
-
 153
153This phishing email uses an unexpected trick to infect PCs with keylogger malware
Rather than using macros, this malware uses Visual Basic Script to avoid detection. Cybercriminals are targeting a US major financial services provider...
-
 120
120Insidious phishing attack leverages on fake attachments to steal Gmail credentials
Cybercriminals are adopting specially crafted URLs to trick users into entering their Gmail credentials in a new sophisticated phishing campaign. Security experts...
-

 142
142Stealing passwords from McDonald’s users
By abusing an insecure cryptographic storage vulnerability (link) and a reflected server cross-site-scripting vulnerability (link) it is possible to steal and decrypt...
-

 216
216Intelligence report claims the Kremlin has cracked Telegram service
A raw intelligence document published last week claims Russian cyber experts have cracked Telegram messaging service to spy on opponents. A raw intelligence...
-

 232
232Internet Archive Launches Chrome Extension That Replaces 404 Pages With Archived Copies
The Internet Archive has launched on Friday a Chrome extension that will detect “Page not found” and other web errors and replace...
-

 204
204WordPress 4.7.1 released, patches eight vulnerabilities and 62 bugs
According to the release notes the latest version of WordPress 4.7.1 addresses eight security vulnerabilities and other 62 bugs. Wednesday the latest...
-

 91
91Hacker Steals 900 GB of Cellebrite Data
The hackers have been hacked. Motherboard has obtained 900 GB of data related to Cellebrite, one of the most popular companies in...
-

 92
92Adobe, Microsoft Push Critical Security Fixes
Adobe and Microsoft on Tuesday each released security updates for software installed on hundreds of millions of devices. Adobe issued an update...
-

 223
223Juniper SRX firewalls open a root-level account due to a flaw
Experts at Juniper have discovered that an update for its Juniper SRX firewalls opens a root-level account on the network device. The company started...
-
 162
162New, Poorly-Made Terror Exploit Kit Drops Monero Cryptocurrency Miner
Security researchers from Trustwave and Malwarebytes have come across a new, poorly assembled exploit kit that appears to be the work of...
-

 212
212WordPress, Joomla, and Magento Continue to Be the Most Hacked CMSs
Based on statistical data gathered by Sucuri from 7,937 compromised websites, WordPress, Joomla, and Magento, in this order, continued to be the...
-

 160
160WordPress Plugin Stop User Enumeration does not stop user enumeration
User Enumeration is the capacity to automatically figure out if a given account is valid on a system. By enumerating client accounts, you are at...
-
 147
147This new Mac malware freezes your computer with email drafts
A new form of malware is targeting Macs and launching denial-of-service attacks on users by creating multiple email drafts that crash the...
-

 347
347FTC files lawsuit against D-Link for router and camera security flaws
The FTC has filed a lawsuit against D-Link for failing to protect its customers against ‘well known and easily preventable software security...
-

 88
88MM CORE IN-MEMORY BACKDOOR RETURNS AS “BIGBOSS” AND “SILLYGOOSE”
we will detail our discovery of the next two versions of MM Core, namely “BigBoss” (2.2-LNK) and “SillyGoose” (2.3-LNK). Attacks using “BigBoss” appear likely...
-

 86
86Critical RCE vulnerabilities affect SwiftMailer, PhpMailer and ZendMail
The security expert Dawid Golunski from Legal Hackers has reported critical RCE flaws in the popular PHP libraries SwiftMailer, PhpMailer and ZendMail....
-
 242
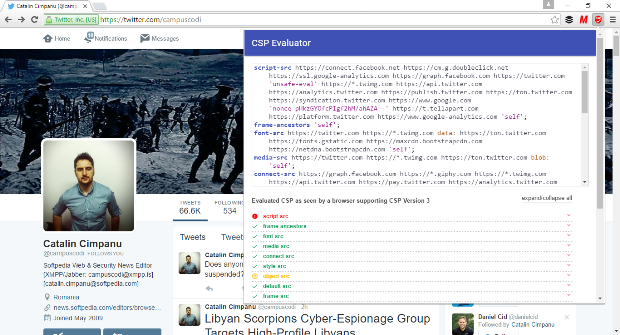
242Google Releases Two Chrome Extensions for XSS Discovery and Mitigation
Google says it paid over $1.2 million just for XSS bugs. Google released two new tools called CSP Evaluator and CSP Mitigator...
-
 82
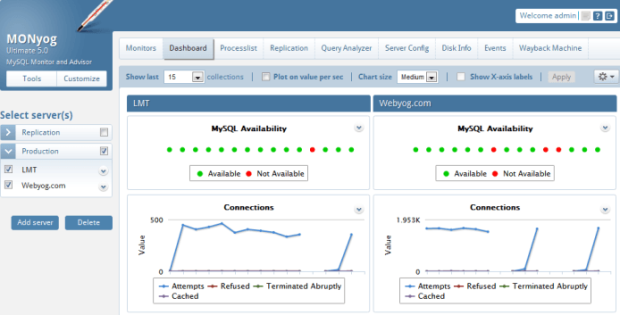
82Researcher found a severe flaw in the MONyog monitoring tool
A security expert discovered a vulnerability in the MONyog tool that could be exploited by a normal user to elevate his privilege...
-

 236
236Unpatched Vulnerability Affecting PHP 7 Servers
PHP 7 is affected by an unpatched vulnerability that opens servers running the latest branch of the PHP programming language to attacks....
-

 232
232SQL Attack (Constraint-based)
It is good to know that nowadays, developers have started paying attention to security while building websites. Almost everyone is aware of...






