Vulnerabilities
-

 164
164Cyanogen Inc. shuts down CyanogenMod in Christmas bloodbath
Open source Android ROM project dies, developers launch fork. Cyanogen Inc., the company built around the CyanogenMod open source Android OS ROM...
-
 87
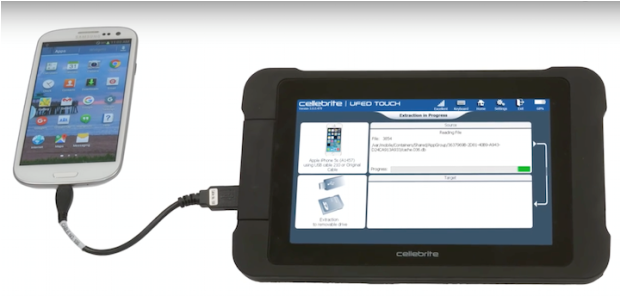
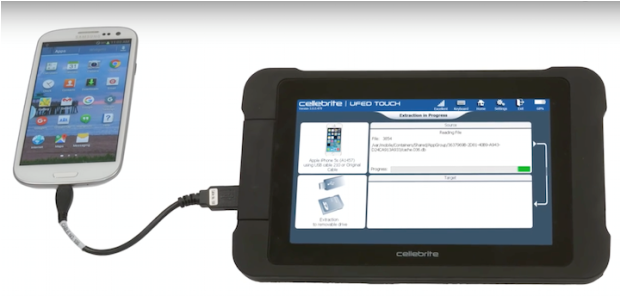
87US State Police Have Spent Millions on Israeli Phone Cracking Tech
When cops have a phone to break into, they just might pull a small, laptop-sized device out of a rugged briefcase. After...
-

 79
79ZyXEL and Netgear Fail to Patch Seven Security Flaws Affecting Their Routers
Router manufacturers such as Netgear and ZyXEL have failed to address seven security flaws reported by security researchers in the last three...
-

 232
232Top 10 famous computer bugs that cost millions of dollars
Top 10 Famous and Interesting Bugs in The Tech World Computer bugs or coding errors are a common phenomenon in the tech world...
-

 77
77Cryptolulz666 hacked the Dutch Chamber of Commerce in HK
@Cryptolulz666 and his colleague Kapustkiy broke into the systems of another website belonging to a HK corporation, the Dutch Chamber of Commerce....
-

 164
164Steam Down!!! Phantom Squad DDoS Steam servers and bring it down for Christmas!!
Steam servers DDoSed and taken down by Phantom Squad hacker group, gamers left in lurch during busy Christmas weekend If you are...
-
 147
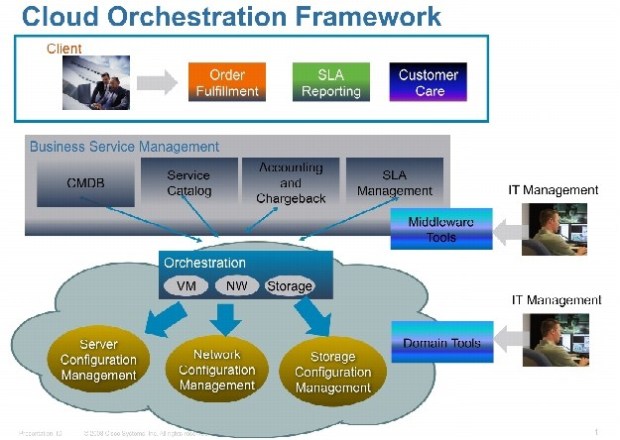
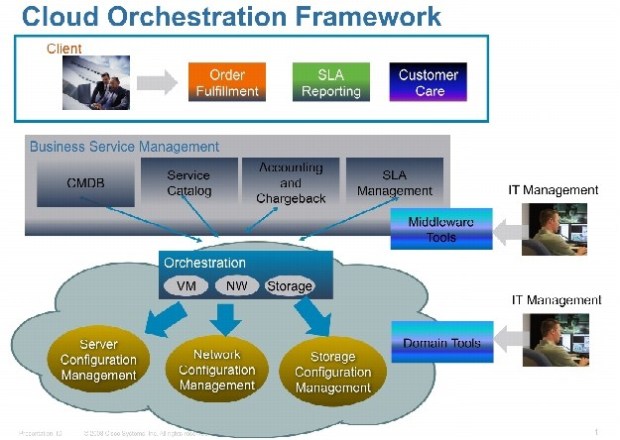
147A flaw in Cisco CloudCenter Orchestrator exploited by hackers in the wild
Cisco is warning customers about a critical privilege escalation flaw that has been exploited in attacks against the Cisco CloudCenter Orchestrator systems....
-

 244
244Rapid7 Named Common Vulnerability and Exposure Numbering Authority
Boston, MA — December 20, 2016 — Rapid7, Inc. (NASDAQ: RPD), a leading provider of IT and security analytics solutions, today announced that...
-

 76
76It’s Now Commonplace for Android Banking Trojans to Include Ransomware Features
The current generation of Android banking trojans are all equipped with ransomware-like features in order to lock the user’s device, and in...
-

 166
166Indian Institute of Technology Kharagpur hacked by Cryptolulz666
Cryptolulz666 announced another data breach, he hacked the database of the Indian Institute of Technology Kharagpur, the second of the country. Just...
-

 108
108MICROSOFT PATCHES PUBLICLY DISCLOSED IE, EDGE VULNERABILITIES
Microsoft today patched a half-dozen critical browser vulnerabilities that have been publicly disclosed, but apparently not used in attacks as of yet....
-
 119
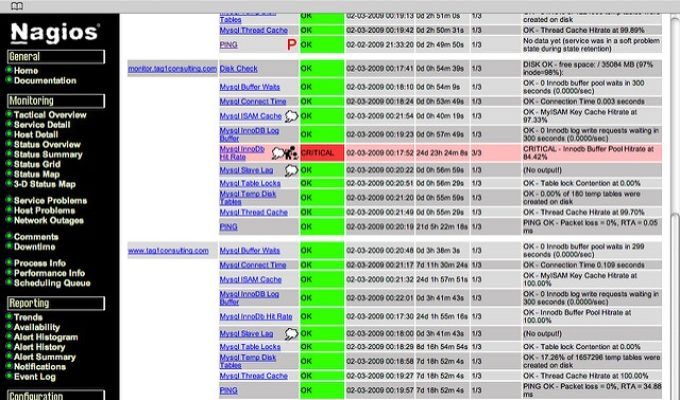
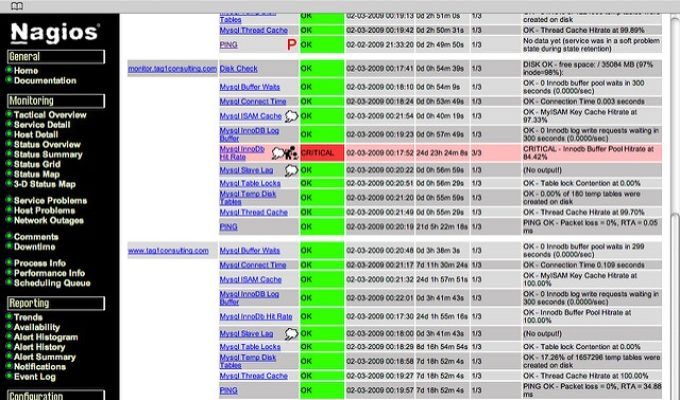
119NAGIOS CORE PATCHES ROOT, RCE VULNERABILITIES
Nagios Core has been updated to take care of two critical vulnerabilities that can be pinned together to attack servers hosting the...
-

 95
95$300 Device Can Steal Mac FileVault2 Passwords
Swedish hardware hacker Ulf Frisk has published today instructions on how to build and use a $300 device that can retrieve login...
-

 151
151A Backdoor Discover in Skype allows to hack everything that Skype can offer for Mac OS X
Trustwave recently reported a locally exploitable issue in the Skype Desktop API Mac OS-X which provides an API to local programs/plugins executing...
-

 187
187Newly Uncovered Site Suggests NSA Exploits for Direct Sale
The Shadow Brokers—a hacker or group of hackers that stole computer exploits from the National Security Agency—has been quiet for some time....
-

 161
161Vulnerability in Joomla Allows Attackers to Reset Passwords and Take Over Sites
The Joomla Project released version 3.6.5 of the Joomla CMS that addresses three security bugs, of which one can allow attackers to...
-

 164
164Old Skype for Mac API Doubles as a Backdoor
A soon-to-be-deprecated API included with Skype for Mac contains a vulnerability that allows an attacker to bypass authentication procedures and query for...
-

 158
158Samas Ransomware Group Made at Least $450,000
A criminal group has made at least $450,000 by infecting organizations with the Samas ransomware in the past year, according to an...
-

 182
182Lax Cybersecurity at Nuclear Facilities is a Recipe For Widespread Disaster
Experts at the Nuclear Industry Summit (NIT) explained how to reduce the risk of damaging cyberattacks at nuclear facilities. The threat of...
-

 139
139CERT Warns Users to Stop Using Two Netgear Router Models Due to Security Flaw
The United States Computer Emergency Readiness Team (US-CERT), an organization within the Department of Homeland Security (DHS), has published a security alert...
-

 201
201No, there’s no evidence (yet) the feds tried to hack Georgia’s voter database
State election official bungles the case that DHS tried to breach his office. Accusations that the US Department of Homeland security tried...






