Vulnerabilities
-

 225
225‘Android for Work’ Security Containers Bypassed with Relative Ease
Mobile security experts from Skycure have found two methods for bypassing the security containers put around “Android for Work,” allowing attackers to...
-

 184
184German parents told to destroy Cayla dolls over hacking fears
German watchdog classifies My Friend Cayla doll as ‘illegal espionage apparatus’ and says shops and owners could face fines An official watchdog...
-

 223
223Mobile apps and stealing a connected car
The concept of a connected car, or a car equipped with Internet access, has been gaining popularity for the last several years....
-
 235
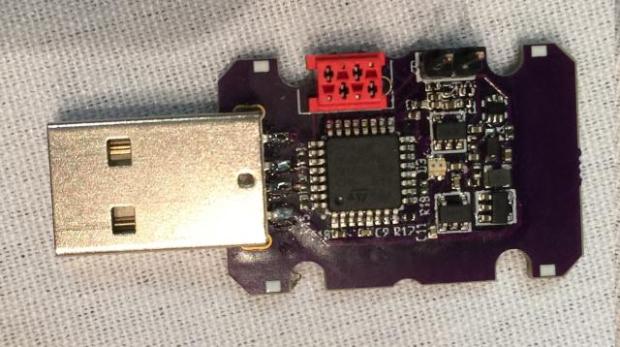
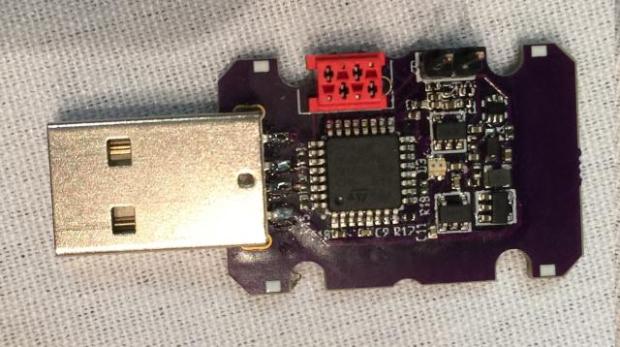
235USB Killer now lets you fry most Lightning and USB-C devices for $55
Plus a new, stealthy “anonymous” stick, because that’s what the world really needed. Remember the USB Killer stick that indiscriminately and immediately...
-

 107
107Researchers Create New System That Makes Bitcoin Transactions Harder to Track
Researchers from Boston University, North Carolina State University, and George Mason University have created a new protocol called TumbleBit that they say...
-

 123
123Unexpected Journey #2 – Taking Down Entire Domain Using Vulnerabilities of a SIEM Product
As I said on my previous article, being a penetration tester makes us feel like a group of traveler. Today, I would...
-

 73
73Phwning the boardroom: hacking an Android conference phone
At Context we’re always on the lookout for interesting devices to play with. Sat in a meeting room one day, we noticed...
-

 171
171Xen Project asks to limit security vulnerability advisories
The organization is requesting permission to limit disclosures to only the most severe bugs. The Xen Project has requested feedback from the...
-

 103
103Somebody Hacked Mexico’s Soda-Tax Advocates with Spyware
There’s a disturbing possibility that the Mexican government, the soda industry, or some combination of both used spyware to harass health advocates...
-

 172
172Researchers Discover Self-Healing Malware That Targets Magento Stores
Dutch malware experts have found a new malware strain that targets online shops running on the Magento platform, which can self-heal using...
-

 173
173ASLR-security-busting JavaScript hack demo’d by university boffins
Amster-damn, that’s a hell of a vulnerability to make browser bug exploitation easier. Researchers in Europe have developed a way to exploit...
-
 191
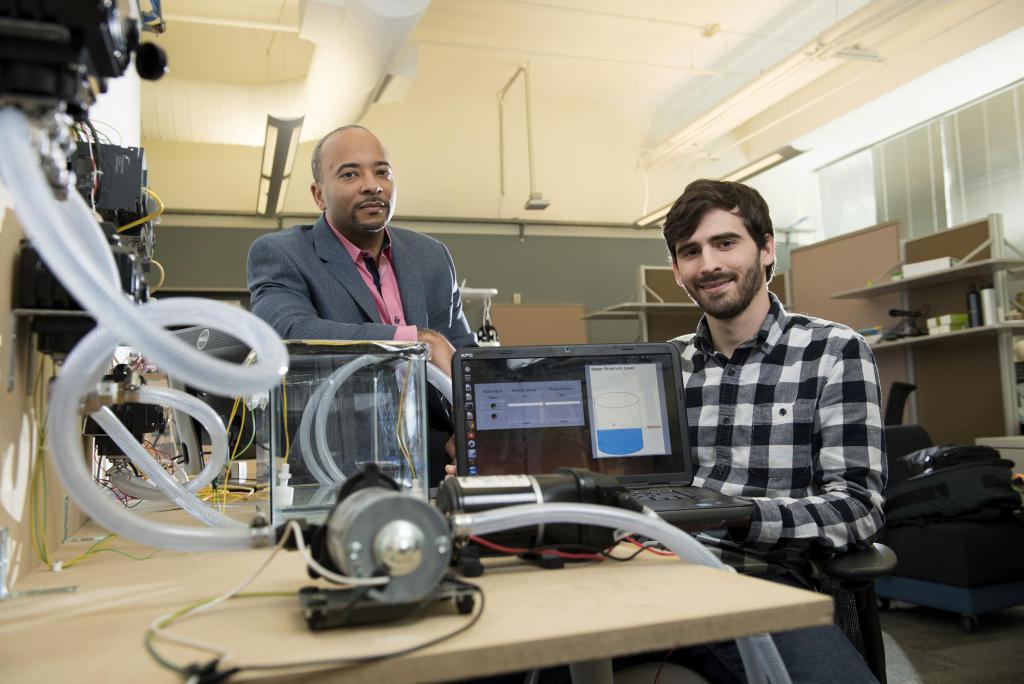
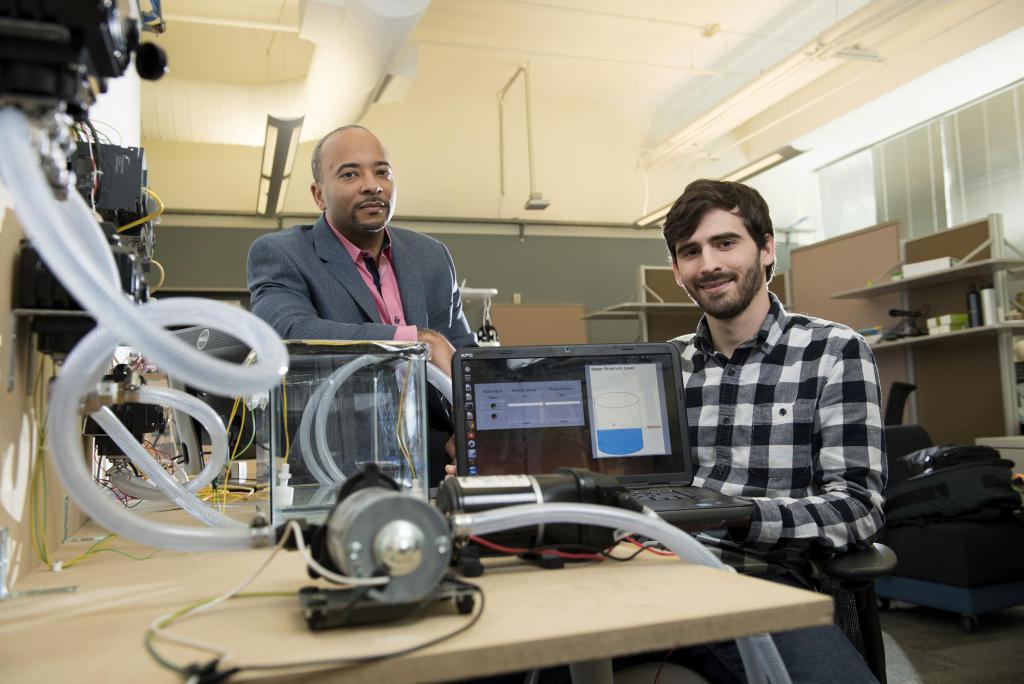
191A simulation shows how a ransomware could hack PLCs in a water treatment plant
The security researchers at the Georgia Institute of Technology have simulated a ransomware-based attack on PLCs in a water treatment plant. The...
-

 149
149UPDATED FIRMWARE DUE FOR SERIOUS TP-LINK ROUTER VULNERABILITIES
Chinese router maker TP-Link is wrestling with the disclosure of a handful of vulnerabilities in its C2 and C20i routers. The most...
-
 258
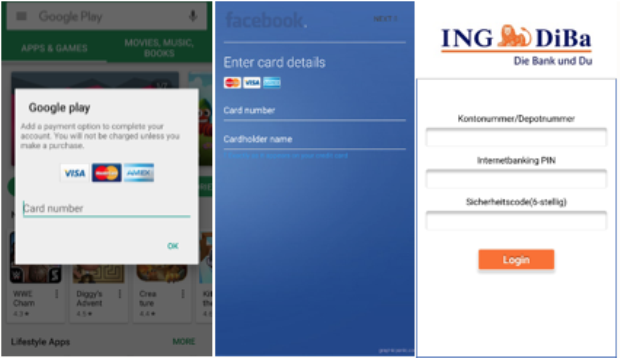
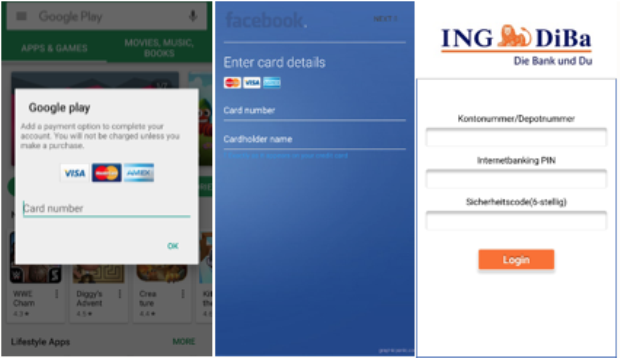
258Android Banking Trojan Marcher Targets Dozens of Apps, Bypasses Antivirus
It starts with a phishing attack over SMS, continues with a bad app and ends with your stolen bank account. Android-targeting banking...
-
 104
104New Tool Takes Mere Minutes to Create Dark Web Version of Any Site
Independent security researcher wants to make creating Tor hidden service versions of websites that much easier. More mainstream services and websites are...
-

 176
176Indian Ministry of Home Affairs website hacked, authorities take it down
Home Ministry’s website mha.nic.in hacked; Hackers exploited Drupal vulnerability Unknown hackers today used a Drupal exploit to hack mha.nic.in, which is Indian...
-

 160
160Ultranationalist Developer Behind SerbRansom Ransomware
An ultranationalist developer from Serbia is behind a series of malware strains, including a new ransomware family named SerbRansom, discovered yesterday by...
-

 197
197HIGH SEVERITY BIND VULNERABILITY CAN LEAD TO A CRASH
The Internet Systems Consortium patched the BIND domain name system this week, addressing a remotely exploitable vulnerability it considers high severity and...
-

 169
169Run this in April: UPDATE Azure SET SQLthreat_detection = ‘generally available’
Microsoft says it will fully power up its Azure SQL Database Threat Detection service this spring. This technology, which has been in...
-
 172
172Hacker hijacked more than 150,000 printers
For many of us hacking of printers seems to be next to impossible thing. But, a hacker has hacked more than 150,000...
-
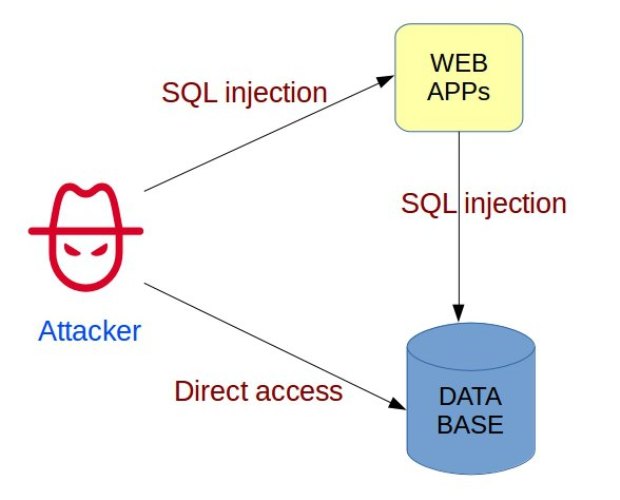
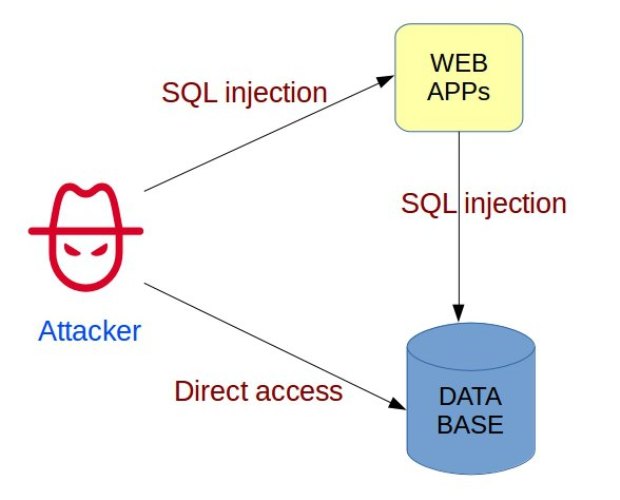 189
1892 thoughts on “Code Execution in SQL Server via Fileless CLR-based Custom Stored Procedures”
Recently I was given the task of performing command execution on a compromised MSSQL server with the following restrictions: No use of...






