Vulnerabilities
-
 184
184NSA’S DOUBLEPULSAR KERNEL EXPLOIT IN USE INTERNET-WIDE
If you’re on a red team or have been on the receiving end of a pen-test report from one, then you’ve almost...
-

 190
190Is ‘admin’ password leaving your IoT device vulnerable to cyberattacks?
Internet-connected devices in your home or office will be vulnerable to botnets and other attacks, if you don’t change the original login...
-
 110
110HipChat hacked, resets passwords for affected users
Group chat service HipChat made an announcement on its blog that their Security Intelligence Team detected a “vulnerability” in a third-party library...
-

 200
200Microsoft Edge Vulnerability Allows Cookie and Password Theft
A vulnerability in the Microsoft Edge browser can be exploited and allow an attacker to obtain a user’s password and cookie files...
-
 252
252Critical Microsoft Edge Vulnerability leads to Bypass the Password and Cookie Theft – Still Not Yet Patched
[jpshare]Critical Microsoft Edge Vulnerability Allows to steal the cookies and password revealed by Recent Research by PoC (Proof-of-Concepts) .This Vulnerability Discovered under...
-

 186
1862016’s Most Popular Exploit Was the Vulnerability Used for the Stuxnet Attacks
One of the vulnerabilities used to spread the Stuxnet virus was 2016’s most popular exploit, according to telemetry data gathered by Russia...
-
 169
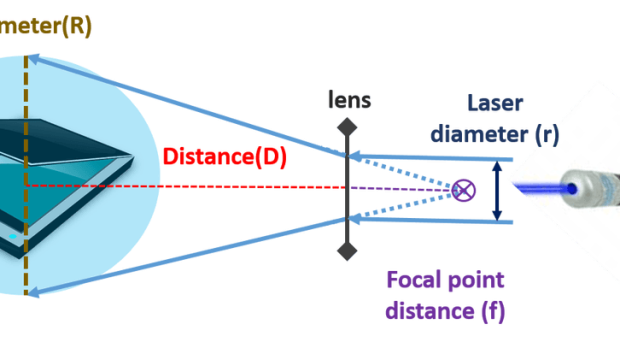
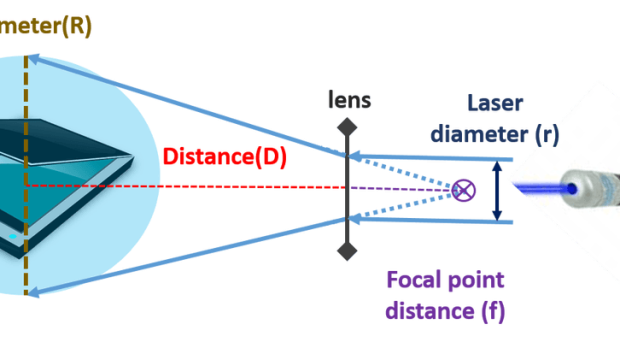
169Ops, hackers can exfiltrate data from air-gapped networks through a malware controlled via a scanner
A group of Israeli researchers has devised a new technique to exfiltrate data from a PC in an air-gapped network through malware controlled via scanners....
-

 185
185SKYPE FIXES ‘SPYKE’ CREDENTIAL PHISHING REMOTE EXECUTION BUG
Microsoft recently fixed a vulnerability in its video chat and messaging app Skype that could have allowed an attacker to execute code...
-
 138
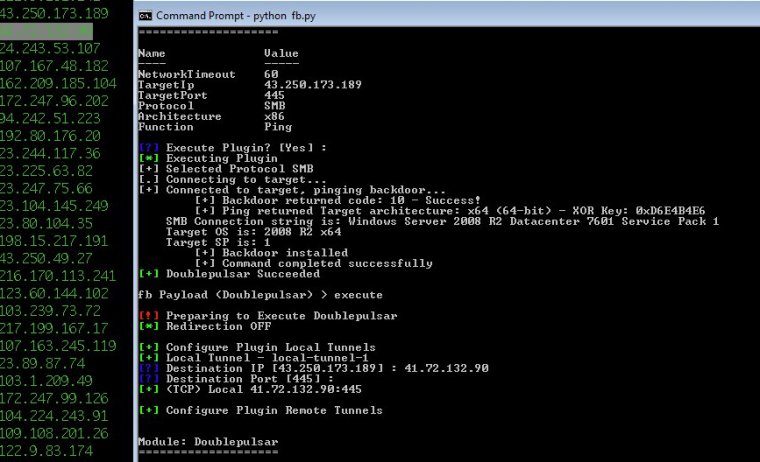
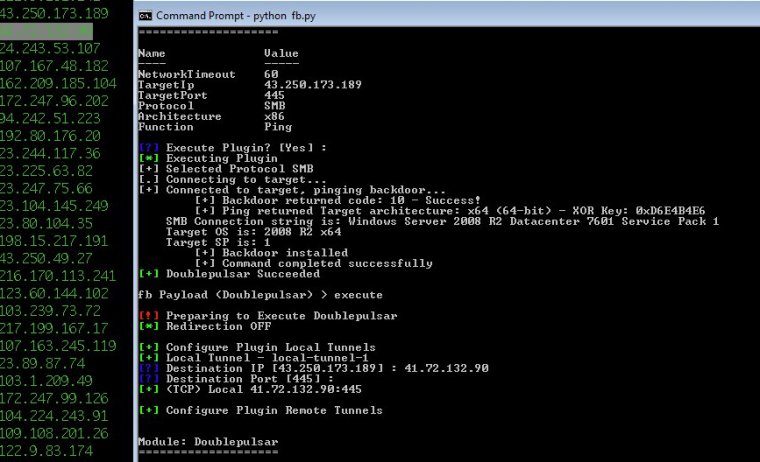
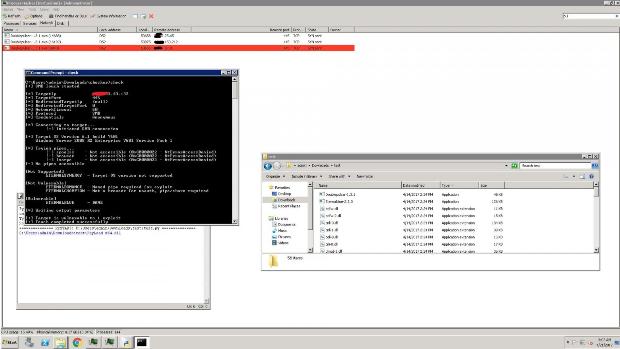
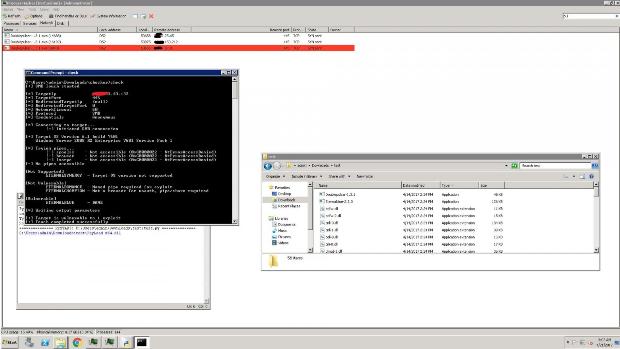
13810,000 Windows computers may be infected by advanced NSA backdoor
Did script kiddies use DoublePulsar code released by NSA-leaking Shadow Brokers? Security experts believe that tens of thousands of Windows computers may...
-
 165
165AES-NI Ransomware Dev Claims He’s Using Shadow Brokers Exploits
The developer of the AES-NI ransomware claims that the recent “success” he’s been enjoying is due to the NSA exploits leaked last...
-

 209
209Vulnerabilities in Linksys routers allow attackers to hijack dozens of models
Cyber security experts disclosed the existence of 10 unpatched security flaws in dozens of Linksys routers widely used today. The IOActive senior...
-
 349
349WordPress vulnerable to Cross-Site Request Forgery in Connection Information – Not yet fixed with last Update
[jpshare] Wordpress vulnerable to Cross-Site Request Forgery in Connection Information – Not yet fixed with the last Update. WordPress is a free online...
-

 106
106ANALYZING THE DOUBLEPULSAR KERNEL DLL INJECTION TECHNIQUE
Like many in the security industry, we’ve been busy investigating the implications of the Shadow Brokers leak, with the DOUBLEPULSAR payload in...
-

 218
218Windows bug used to spread Stuxnet remains world’s most exploited
Code-execution flaw is triggered by plugging a booby-trapped USB into vulnerable PCs. One of the Microsoft Windows vulnerabilities used to spread the...
-

 105
105Meet PINLogger, the drive-by exploit that steals smartphone PINs
Sensors in phones running both iOS and Android reveal all kinds of sensitive info. Smartphones know an awful lot about us. They...
-
 102
102WAVE OF JAVA-BASED RATS TARGET TAX FILERS
Spammers are spreading Java-based remote access Trojans, known as jRATs, targeting tax filers with attachments named “IRS Updates.jar” and “Important_PDF.jar” that, if executed, give...
-
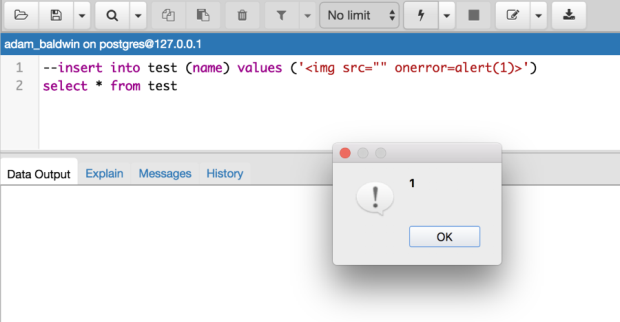
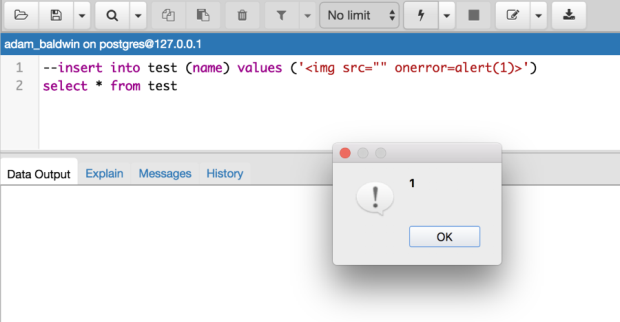 222
222SQL Injection & more via XSS in pgAdmin 4
This is the story of how I found and exploited XSS (content injection) in the pgAdmin4 1.3 desktop client. (Before I get...
-
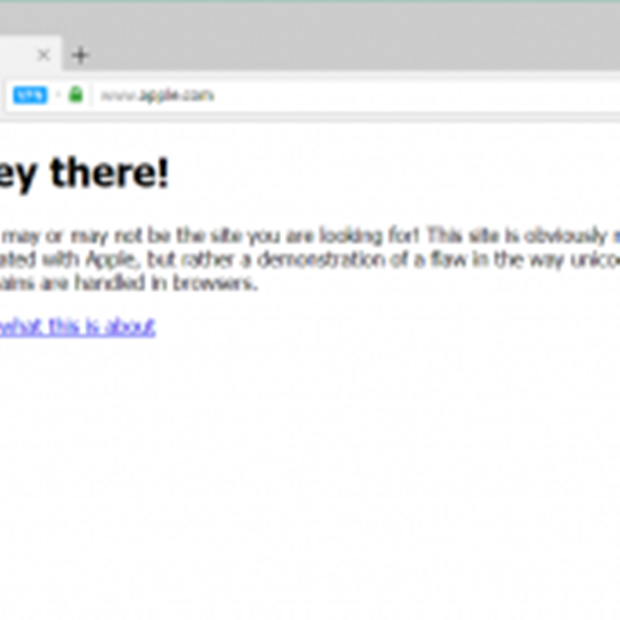
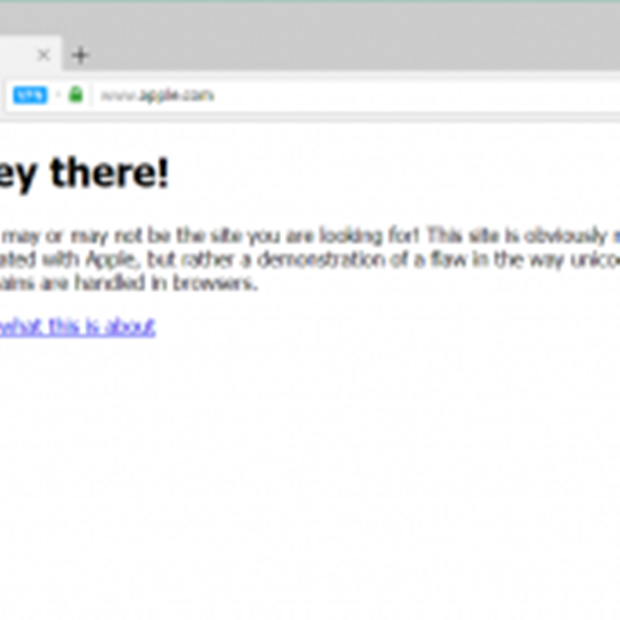 278
278Chrome, Firefox, and Opera Vulnerable to Undetectable Phishing Attack
Browsers such as Chrome, Firefox, and Opera are vulnerable to a new variation of an older attack that allows phishers to register...
-

 233
233Callisto APT Group exploited Hacking Team surveillance tools to hack Government targets
The Callisto APT Group borrowed the source code leaked by hackers that broke into Hacking Team network. According to F-Secure Labs, The Callisto APT...
-

 186
186EXPLOIT KIT ACTIVITY QUIETS, BUT IS FAR FROM SILENT
Over the past six months, the roar of exploit kits has quieted to a whimper. But that doesn’t mean exploit kit threats are...
-
 192
192Watch out, the Riddle vulnerability affects some Oracle MySQL versions. Update them now
A bug dubbed Riddle vulnerability affecting MySQL 5.5 and 5.6 clients exposed user credentials to MiTM attacks. Update to version 5.7. A coding...






