Vulnerabilities
-

 217
217Building Searchable Encrypted Databases with PHP and SQL
This question shows up from time to time in open source encryption libraries’ bug trackers. This was one of the “weird problems”...
-
 88
88Millions of Android devices potentially exposed to the Cloak and Dagger attack
Researchers at Georgia Institute of Technology have discovered a new attack against Android OS, dubbed ‘Cloak and Dagger,’ millions of devices at...
-
 200
200Security Firm Releases Windows XP Patch for NSA Exploit ESTEEMAUDIT
Cyber-security firm enSilo has released a patch for Windows XP and Windows Server 2003 that will protect against attacks via ESTEEMAUDIT, a...
-

 119
119Apple iCloud, Android Nvidia driver N-day exploit details revealed
Kernels can be exploited and iCloud account user information leaked due to the security flaws. Zimperium has released the public details of...
-
 257
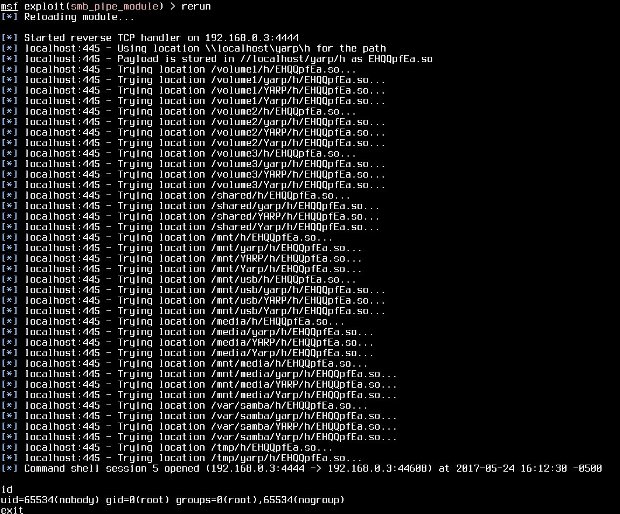
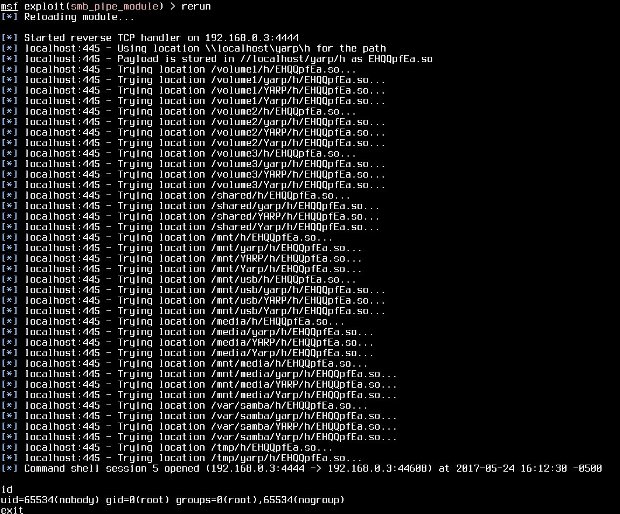
257A wormable code-execution bug has lurked in Samba for 7 years. Patch now!
Comparisons to the Windows flaw WCry exploited are exaggerated, but only a little. Maintainers of the Samba networking utility just patched a...
-

 232
232Trend Micro ServerProtect Contains Multiple Critical Arbitrary Code Execution Vunerabilities including XSS and CSRF
A Trend Micro product ServerProtect for Linux 3.0 Contain 6 Major and very critical vulnerabilities Discovered. ServerProtect Protecting against viruses, rootkits, and...
-

 177
177Canadian Teen Allegedly Behind Notorious Dark Web Hacking Forum
Ping, the administrator of the Hell hacking forum, is allegedly a young boy who supposedly tried to phish teachers. On the dark...
-
 243
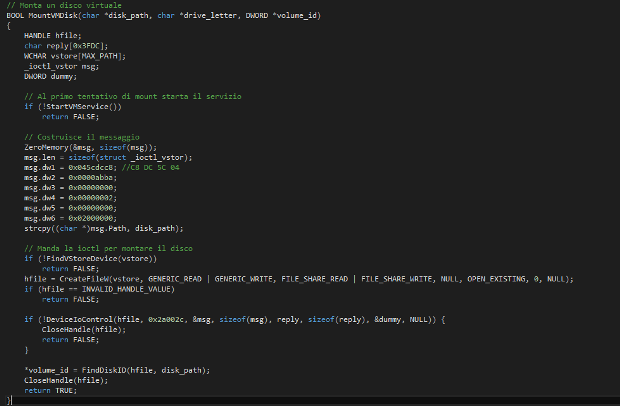
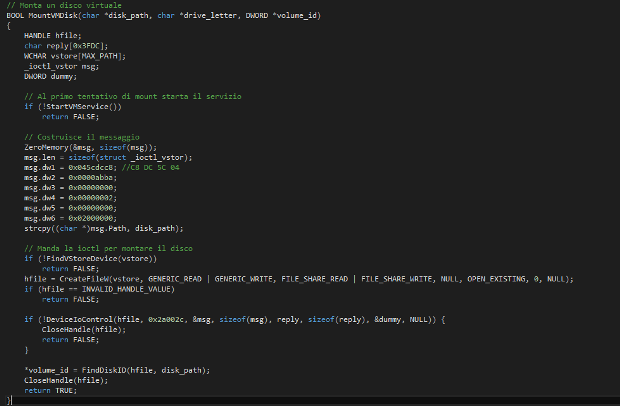
243Post-exploitation: Mounting vmdk files from Meterpreter
Whenever I get a shell on a Windows system with VMware installed I feel a certain frustration at not being able to...
-

 213
213Samsung Galaxy S8 Iris Scanner Fooled by a Photo
A photo of a person’s eye taken at a medium distance is more than enough to trick a Samsung Galaxy S8 smartphone,...
-

 317
317200 Million Downloaded video players including VLC Player are vulnerable to Malicious subtitles Attack -A Complete Takeover Attack
A new Cyber Attack Spreading through Vulnerable Subtitles which Downloaded by Victims Media Player and threatens more than 200 Millions of vulnerable...
-

 184
184New firmware for Netgear routers includes a data collection feature
A new firmware released for NightHawk R7000 Netgear routers includes a remote data collection feature, here’s how to turn off it. In...
-

 246
246Yahoo retires ImageMagick library after 18-byte exploit leaks user email content
The simple line of code made it possible for attackers to view private Yahoo Mail images. Yahoo has decided to retire the...
-

 114
114SSD Drives Vulnerable to Attacks That Corrupt User Data
NAND flash memory chips, the building blocks of solid-state drives (SSDs), include what could be called “programming vulnerabilities” that can be exploited...
-

 169
169The ultimate Linux Trojan horse: Windows Subsystem for Linux
Fedora, openSUSE and Ubuntu are now available in the Windows Store, making life easier for Windows-dominant organizations to run open source software....
-

 131
131DaFont Site Hacked, Almost 700K Accounts Exposed
Hackers got access to usernames, email addresses, and plaintext passwords thanks to improper hashing. DaFont.com was hacked earlier this month, the company...
-

 208
208More people infected by recent WCry worm can unlock PCs without paying ransom
A tool released on Friday decrypts PCs running a fuller suite of Windows versions. New hope glimmered on Friday for people hit...
-

 193
193Windows XP hit by WannaCry ransomware? This tool could decrypt your infected files
Windows XP wasn’t vulnerable to the WannaCry worm but still could be infected with the ransomware. Now there’s a tool to decrypt...
-
 112
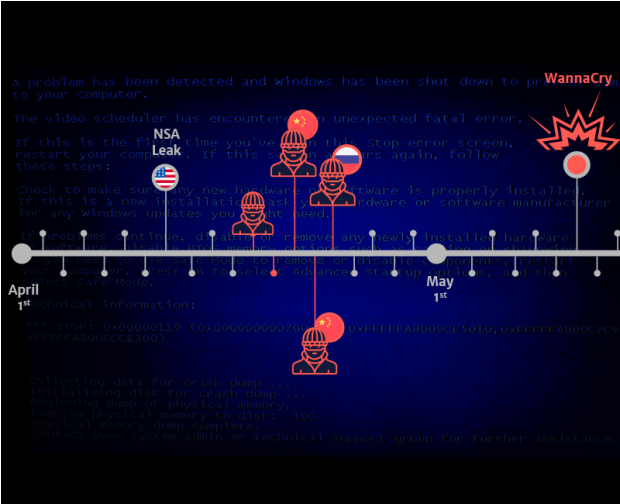
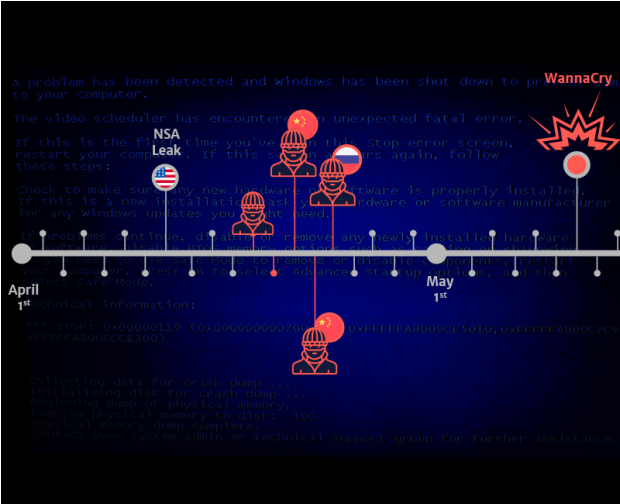
112Multiple Groups Have Been Exploiting ETERNALBLUE Weeks Before WannaCry
We have found evidence of much more sophisticated actors leveraging the NSA ETERNALBLUE exploit to infect, install backdoors and exfiltrate user credentials...
-

 213
213Hacker Demands Ransom After Stealing Source Code From Famous App Maker
Steven Frank, co-founder of Panic, a vendor of Mac and iOS apps, has admitted yesterday that a hacker stole some of his...
-
 117
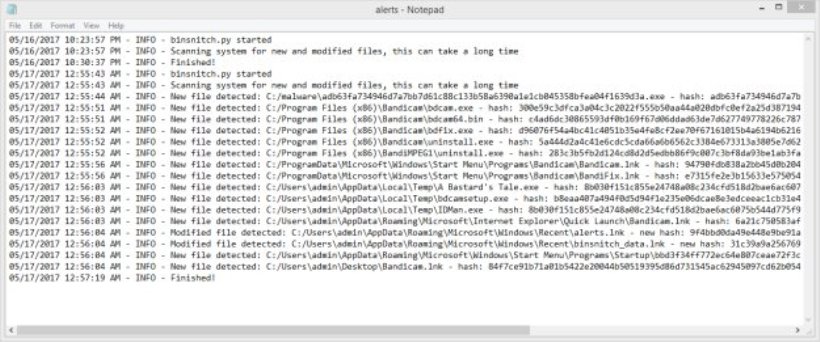
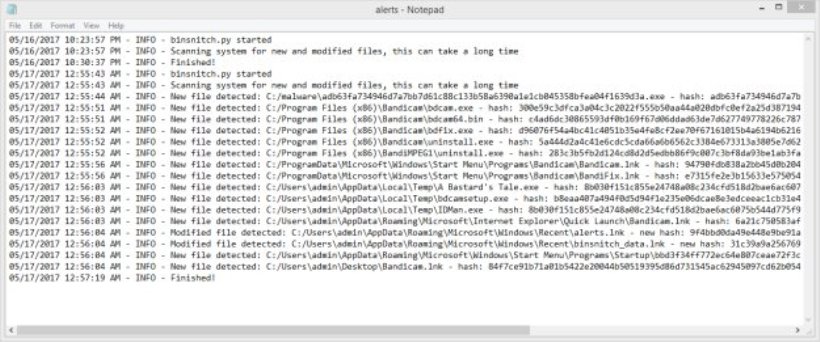
117Using binsnitch.py to detect files touched by malware
Yesterday, we released binsnitch.py – a tool you can use to detect unwanted changes to the file sytem. The tool and documentation is available...
-
 190
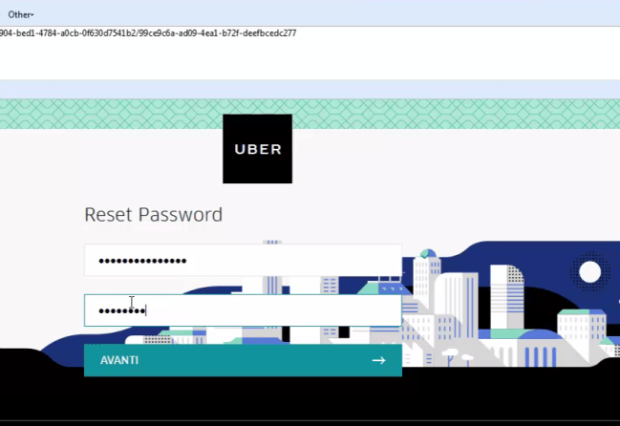
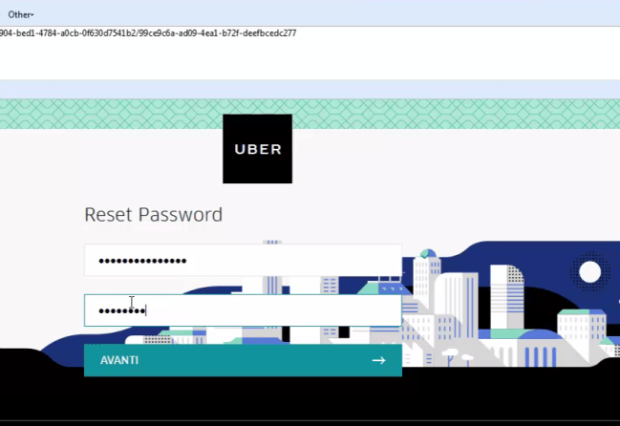
190A critical Improper Authentication vulnerability in Uber allowed password reset for any account
An Italian expert discovered a critical Improper Authentication vulnerability affecting the UBER platform that allowed password reset for any account. The Italian...






