Vulnerabilities
-

 310
310Security Expert Hacks ATM By Drilling A Hole
ATM can be hacked by just drilling a hole ATMs have always had a target painted on their backs. Just last year,...
-

 139
139Crooks Reused Passwords on the Dark Web, so Dutch Police Hijacked Their Accounts
Dutch Police are aggressively going after Dark Web vendors using data they collected from the recently seized Hansa Market. Currently, the infosec...
-
 238
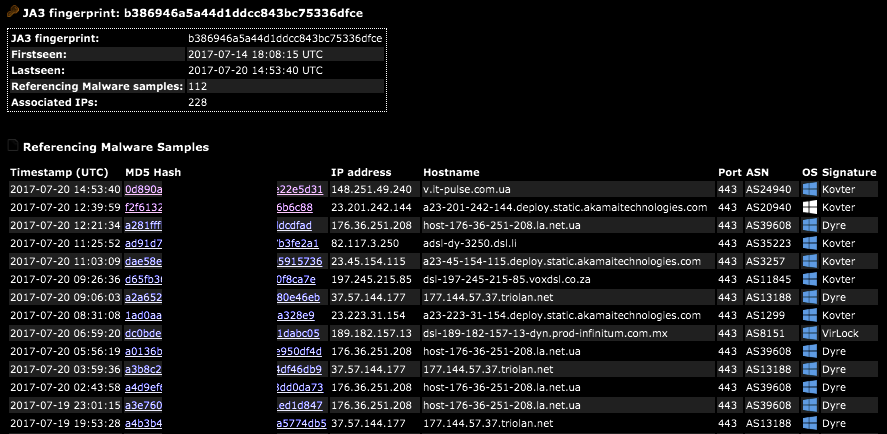
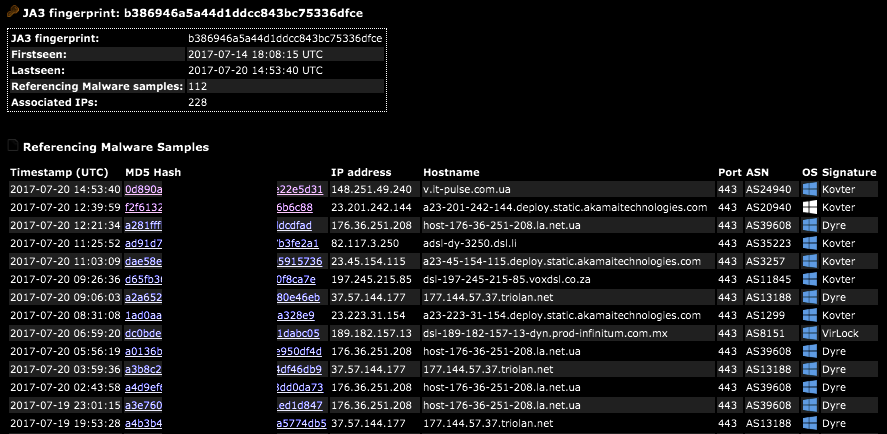
238SSL/TLS Client Fingerprinting for Malware Detection
A JA3 hash represents the fingerprint of an SSL/TLS client application as detected via a network sensor or device, such as Bro...
-

 92
92Experts detailed the new Operation Wilted Tulip campaign of the CopyKittens APT
Researchers from ClearSky and Trend Micro uncovered a new massive cyber espionage campaign conducted by CopyKittens dubbed ‘Operation Wilted Tulip’ A joint...
-

 107
107NOVEL ATTACK TRICKS SERVERS TO CACHE, EXPOSE PERSONAL DATA
LAS VEGAS—Researcher Omer Gil has devised a way to trick a web server into caching pages and exposing personal data. The so-called...
-
 245
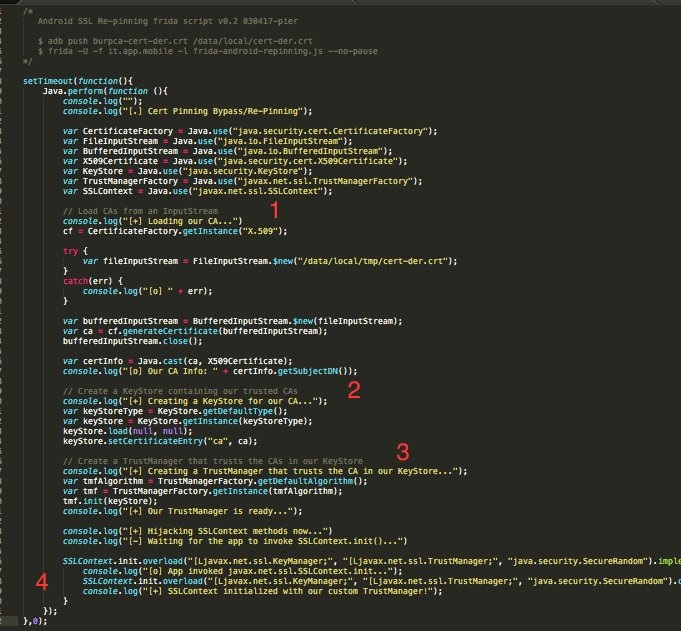
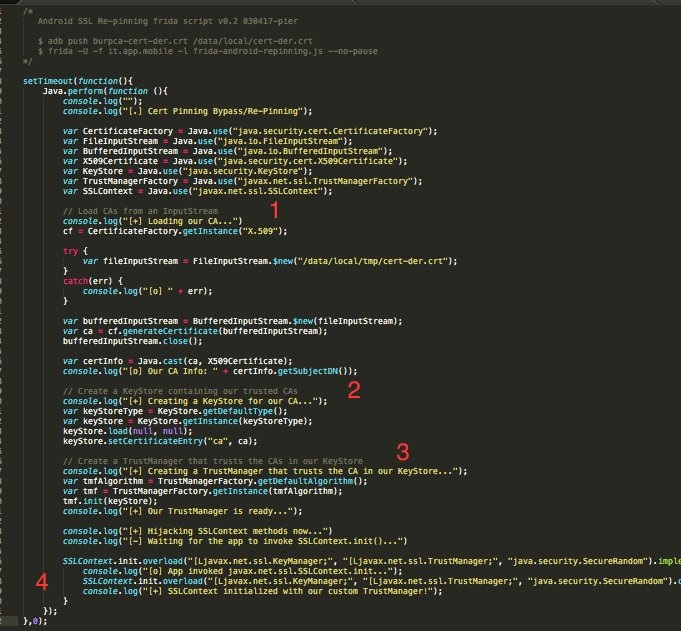
245Universal Android SSL Pinning bypass with Frida
Android SSL Re-Pinning Two kinds of SSL Pinning implementations can be found in Android apps: the home-made and the proper one. The...
-

 185
185Hacker Steals $8.4 Million Worth of Ethereum From Veritaseum Platform
Veritaseum has confirmed today that a hacker stole $8.4 million from the platform’s ICO on Sunday, July 23. This is the second...
-
 253
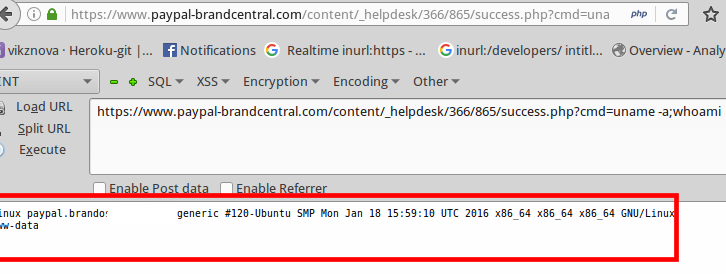
253Expert exploited an unrestricted File Upload flaw in a PayPal Server to remotely execute code
The security researcher Vikas Anil Sharma exploited an unrestricted File Upload vulnerability in a PayPal Server to remotely execute code. The security researcher...
-

 179
179Microsoft sued Fancy Bear to gain control of the domains used in the cyber espionage campaigns
Microsoft used the lawsuit to disrupt a large number of cyber espionage campaigns conducted by infamous Fancy Bear APT hacking group We...
-

 165
165Shut Up and Hack
I wrote most of the code of this small project, called ‘injectAllTheThings’, a while ago when I started developing custom tools for...
-
 102
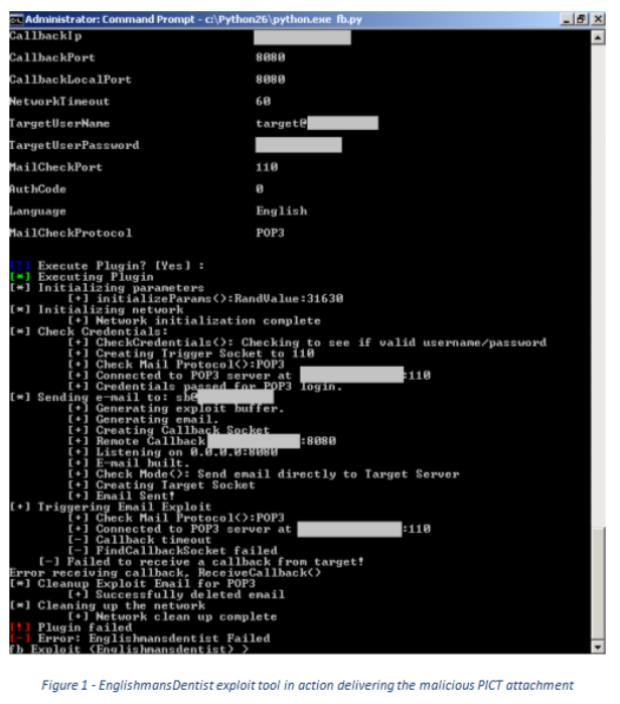
102EnglishmansDentist Exploit Analysis
Introduction We are continuing our series of blog posts dissecting the exploits released by ShadowBrokers in April 2017. After the first two...
-
 121
121Tor network will pay you to hack it through new bug bounty program
Tor wants to find bugs which could compromise the identity of its users. The Tor Project has joined with HackerOne to launch...
-

 205
205Chrome Extension Hijacks Search Results While Filtering Trump from the Web
While doing my normal scan through various sites that are known to push unwanted programs, I ran across a new version of...
-

 168
168A bug in Gnome pic parser can be exploited to run malicious VBScripts
A bug in your image thumbnailer could represent a new attack vector for hackers that can exploit it for script injection. Another day,...
-
 211
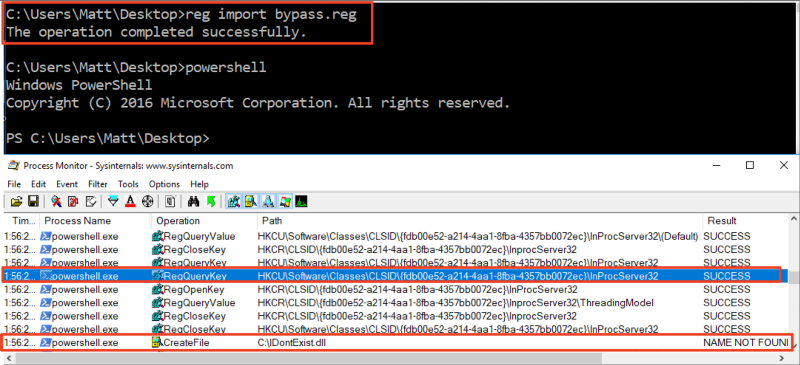
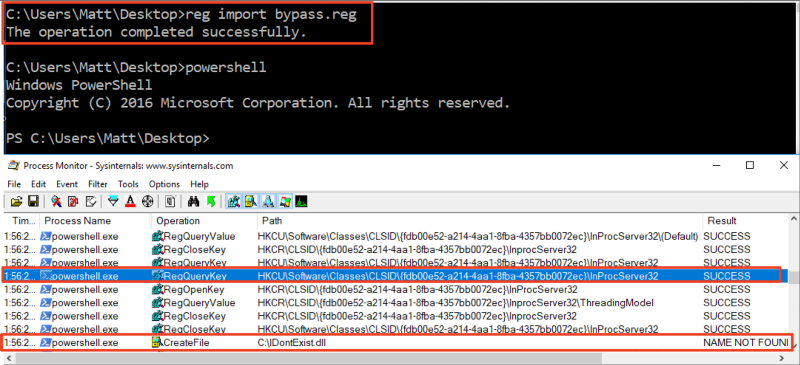
211Bypassing AMSI via COM Server Hijacking
Microsoft’s Antimalware Scan Interface (AMSI) was introduced in Windows 10 as a standard interface that provides the ability for AV engines to...
-

 230
230How to hack a Segway Ninebot miniPRO hoverboard in 20 seconds
Attackers could remotely hack and hijack Ninebot miniPRO hoverboard in just 20 seconds of continuous Bluetooth connection. Do you have an hoverboard?...
-

 116
116Hacker Uses Parity Wallet Vulnerability to Steal $30 Million Worth of Ethereum
An unknown hacker has used a vulnerability in an Ethereum wallet client to steal over 153,000 Ether, worth over $30 million dollars....
-
 248
248Wikileaks: CIA tasked Raytheon for analyzing TTPs used by threat actors in the wild
Wikileaks revealed that CIA contractor Raytheon Blackbird Technologies was tasked to analyze advanced malware and TTPs used by threat actors in the...
-

 280
280ORACLE RELEASES BIGGEST UPDATE EVER: 308 VULNERABILITIES PATCHED
Oracle admins are today staring down the barrel of the biggest quarterly Critical Patch Update ever. The numbers are gory: 308 vulnerabilities patched, 165...
-

 233
233SambaCry Vulnerability Used to Deploy Backdoors on NAS Devices
Someone is using the SambaCry vulnerability to install a backdoor trojan on Linux devices running older versions of the Samba file-sharing server....
-

 251
251Millions of IoT Devices Infected with “Devil’s Ivy” Remote Code Execution Vulnerability Including Internet Connected Cameras
A New Vulnerability called “Devil’s Ivy” Discovered that infected Tens of Millions of IoT Devices which leads to Remotely Execute the code...






