Vulnerabilities
-
 137
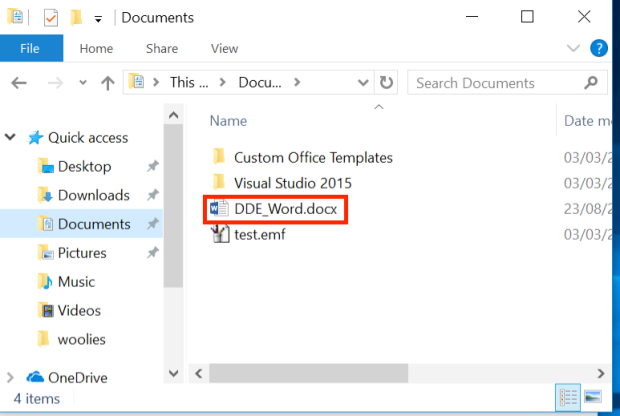
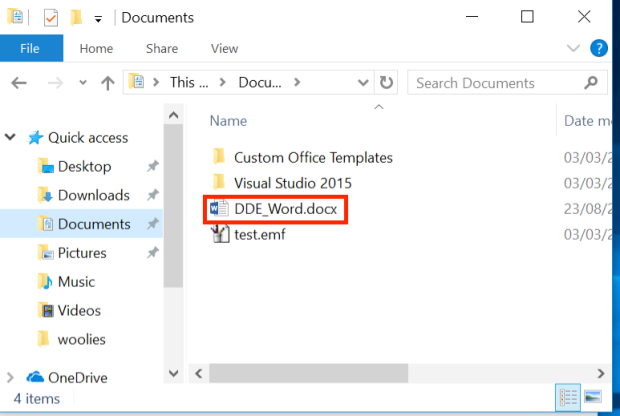
137Macro-less Code Exec in MSWord
In our context DDE works by executing an application, that will provide the data (data provider). In a previous post1 We discussed...
-
 266
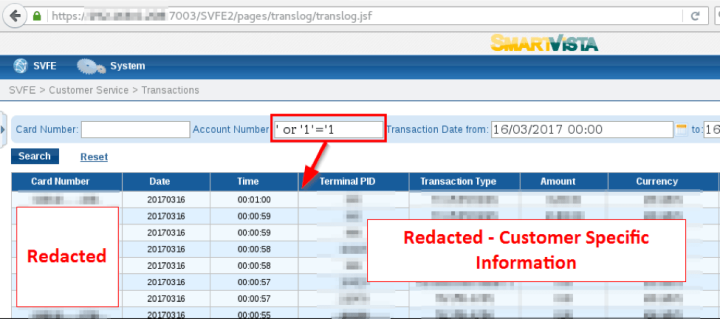
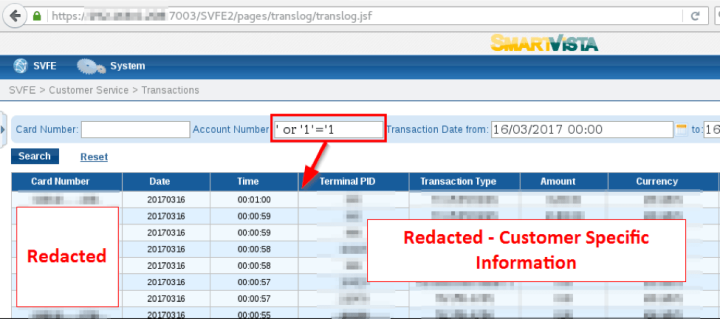
266Swiss BPC banking software SmartVista is vulnerable to SQL Injection attacks
The suite of payment infrastructure and management systems SmartVista created by the BPC Group is vulnerable to SQL Injection attacks. Researchers at...
-

 210
210A Bug Has No Name: Multiple Heap Buffer Overflows In the Windows DNS Client
CVE-2017-11779 fixed by Microsoft in October of 2017, covers multiple memory corruption vulnerabilities in the Windows DNS client. The issues affect computers running Windows...
-

 206
206T-Mobile Website Allowed Hackers to Access Your Account Data With Just Your Phone Number
The bug exposed customers’ email addresses, their billing account numbers, and the phone’s IMSI numbers. T-Mobile has patched the bug. Until last...
-
 343
343Microsoft addresses CVE-2017-11826 Office Zero-Day used to deliver malware
Microsoft October Patch Tuesday addresses the CVE-2017-11826 Office Zero-Day vulnerability that has been exploited in the wild in targeted attacks. Yesterday we...
-

 274
274WhatsApp Exploit Can Allow Hackers To Monitor Your Sleep And Other Things
Who knew there could be ways to analyze our sleep patterns other than the sleep tracking apps and fitness bands. Credits to...
-

 170
170Accenture left a huge trove of highly sensitive data on exposed servers
The four exposed servers had no password, but contained the “keys to the kingdom.” Technology and cloud giant Accenture has confirmed it...
-
 210
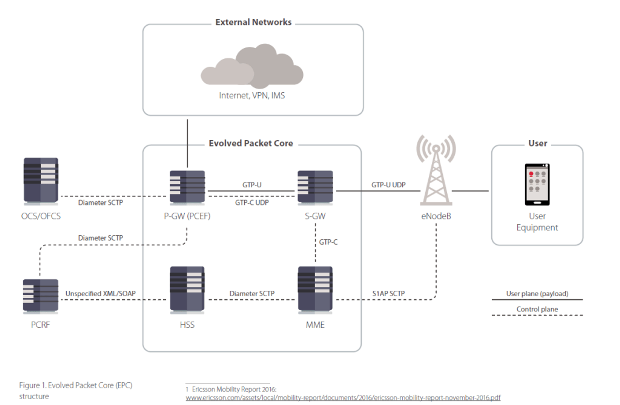
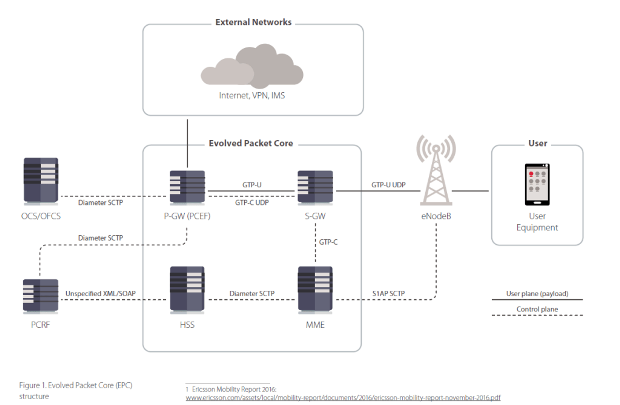
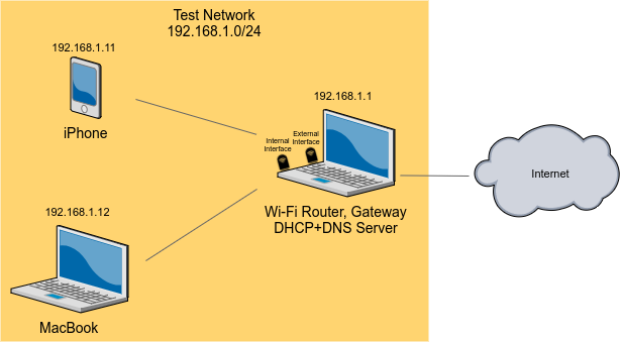
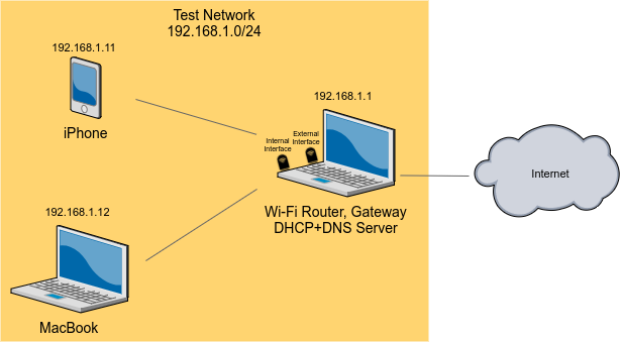
2104G/5G Wireless Networks as Vulnerable as WiFi and putting SmartCities at Risk
Researchers from security firm Positive Technologies warns of 4G/5G Wireless Networks as vulnerable as WiFi and putting smart-cities at risk The Internet of...
-

 89
89A man who goes by the nickname LiquidWorm released a FLIR Thermal Camera Exploit
On September 25, 2017, a man which goes by the nickname ‘LiquidWorm’ has released the exploit code for FLIR Thermal Cameras. On...
-
 132
132One of the Internet’s Gatekeepers Is Eyeing Sneaky Cryptocurrency Miners
Websites are hijacking computers to mine digital coins. Cloudflare, an internet security company founded in 2010, has quickly become an integral part...
-
 296
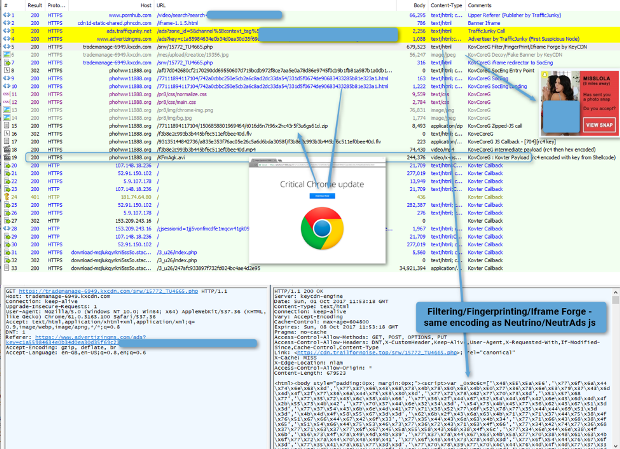
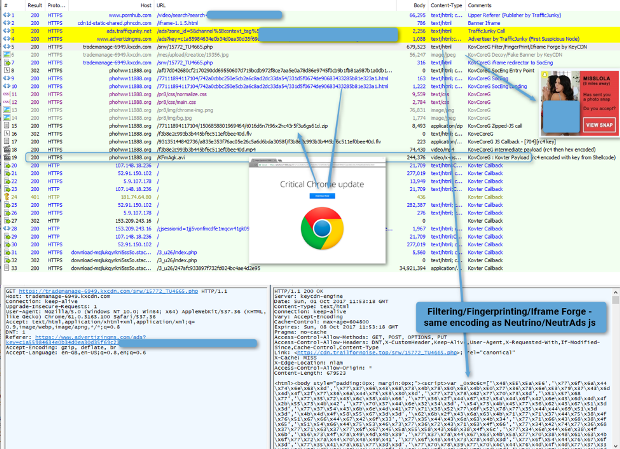
296Kovter Group malvertising campaign exposes millions to potential ad fraud malware infections
This attack chain exposed millions of potential victims in the US, Canada, the UK, and Australia, leveraging slight variations on a fake...
-

 134
134A critical vulnerability affects Siemens smart meters
Siemens has just released a firmware update for the 7KT PAC1200 Siemens smart meters that addresses a critical vulnerability. Siemens has just...
-
 191
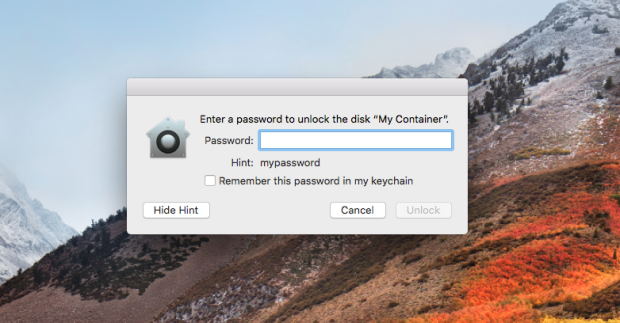
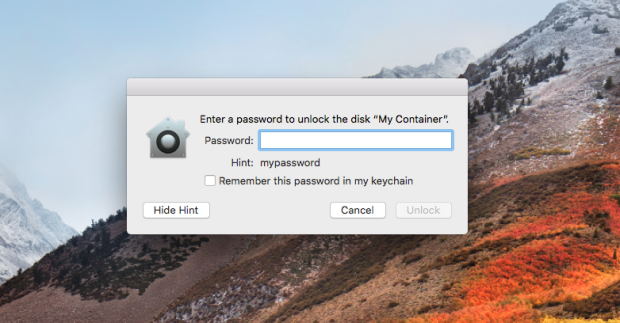
191Apple Issues Emergency Patch to Fix Password Leak in Disk Encryption Utility
Apple rushed out an emergency patch Thursday that fixed an incredulous bug in its shiny new High Sierra operating system that revealed APFS volume...
-
 246
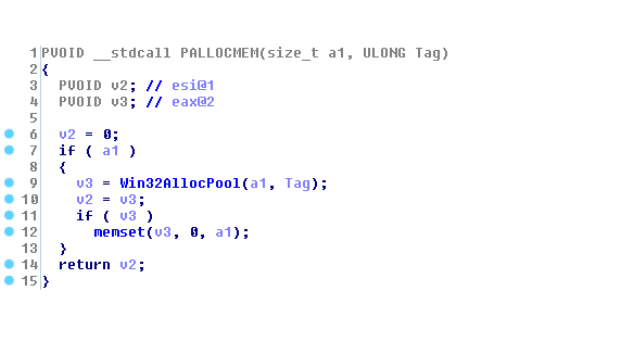
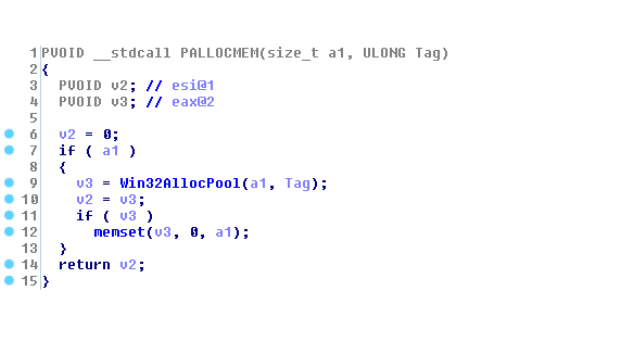
246Using Binary Diffing to Discover Windows Kernel Memory Disclosure Bugs
Patch diffing is a common technique of comparing two binary builds of the same code – a known-vulnerable one and one containing...
-
 151
151CVE-2017-12617 Code Execution flaw patched in Apache Tomcat
Several security vulnerabilities have been patched in recent weeks in Apache Tomcat, including the CVE-2017-12617 Code Execution vulnerability. Several security vulnerabilities have...
-
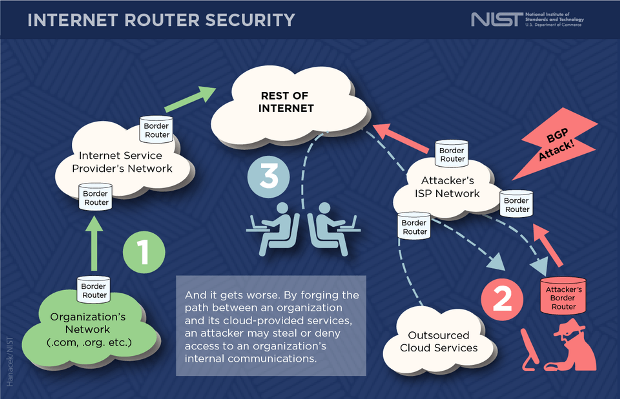
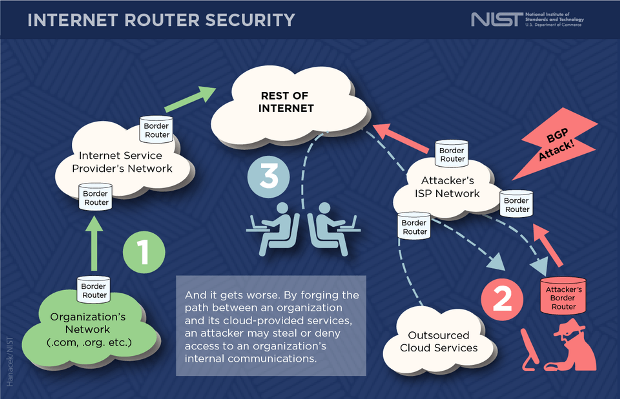 127
127New Network Security Standards Will Protect Internet’s Routing
Electronic messages traveling across the internet are under constant threat from data thieves, but new security standards created with the technical guidance...
-

 97
97Password leak puts online radio stations at risk of hijack
Leaked admin accounts and passwords for radio stations allowed anyone to log-in and hijack broadcasts. A password leak vulnerability in a popular...
-

 200
200MACS NOT RECEIVING EFI FIRMWARE SECURITY UPDATES AS EXPECTED
Since the Thunderstrike bootkit attacks targeting Apple firmware were disclosed in 2015, Apple has bundled subsequent EFI updates with its regular macOS security and software updates...
-
 215
215Exploiting The Wi-Fi Stack on Apple Devices
Earlier this year we performed research into Broadcom’s Wi-Fi stack. Due to the ubiquity of Broadcom’s stack, we chose to conduct our...
-

 102
102Amazon-owned grocery chain Whole Foods Market suffered payment card breach
News of the day is that another big company suffered a security breach, the victim is the Amazon-owned grocery chain Whole Foods...
-
 218
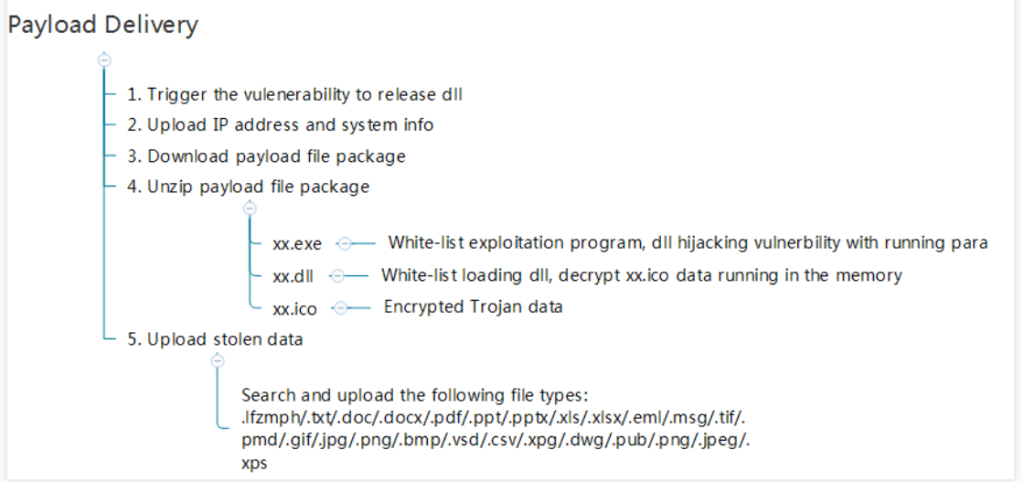
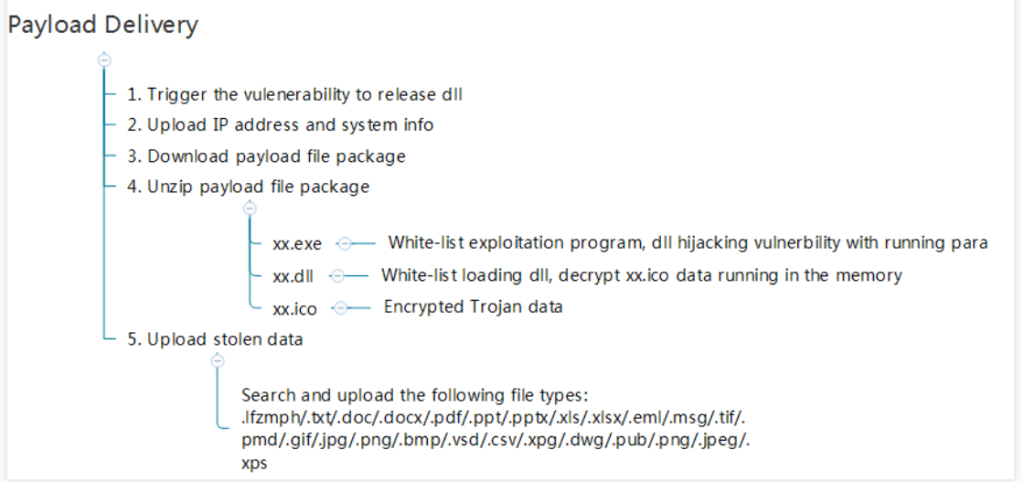
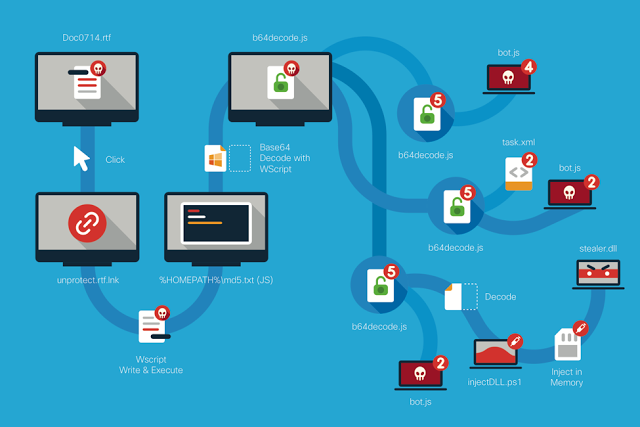
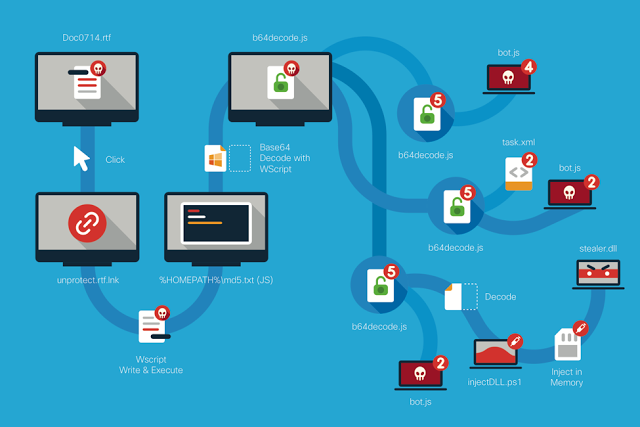
218FIN7 Group Uses JavaScript and Stealer DLL Variant in New Attacks
Throughout this blog post we will be detailing a newly discovered RTF document family that is being leveraged by the FIN7 group...






