Vulnerabilities
-

 159
159How one hacker stole thousands of dollars worth of cryptocurrency with a classic code injection hack on EtherDelta
learned about a malicious code injection that allowed a hacker to steal private keys from multiple victims’ wallets and then manually drain...
-

 158
158CISCO addressed several critical IOS flaws that expose devices to remote attacks
Cisco has released security updates for its IOS Operating System to fix more than a dozen critical and high severity vulnerabilities. Cisco...
-

 262
262Internet Explorer Bug Leaks What Users Type in the URL Address Bar
Microsoft’s Internet Explorer browser is affected by a serious bug that allows rogue sites to detect what the user is typing in...
-

 173
173Another Banking Trojan Adds Support for NSA’s EternalBlue Exploit
A third banking trojan has added support for EternalBlue, an exploit supposedly created by the NSA, leaked online by the Shadow Brokers,...
-

 179
179Experts spotted a login page flaw in Joomla that exposes admin credentials
Researchers at RIPS Technologies discovered a login page vulnerability affecting Joomla versions between 1.5 and 3.7.5 that exposes admin credentials. Experts at...
-
 173
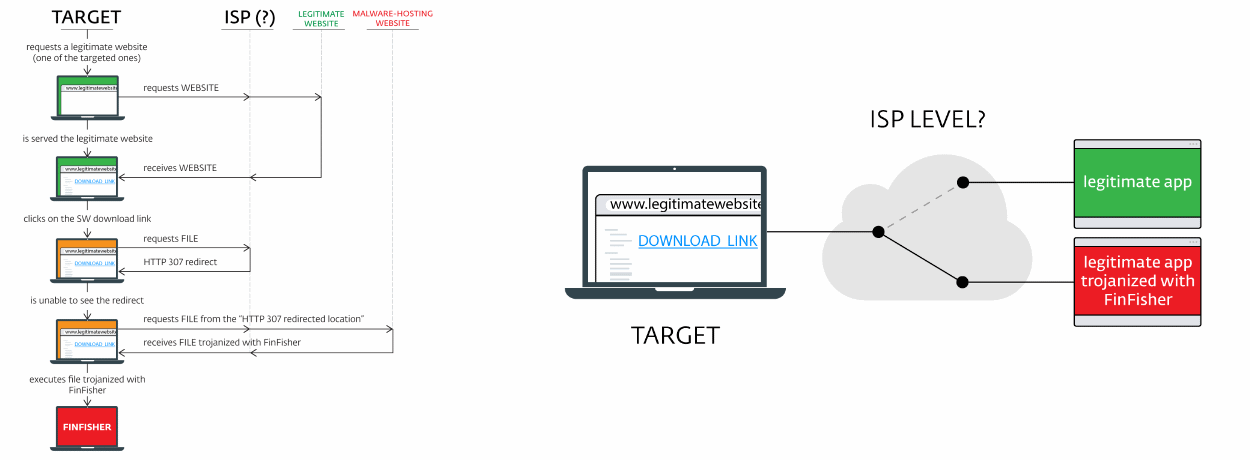
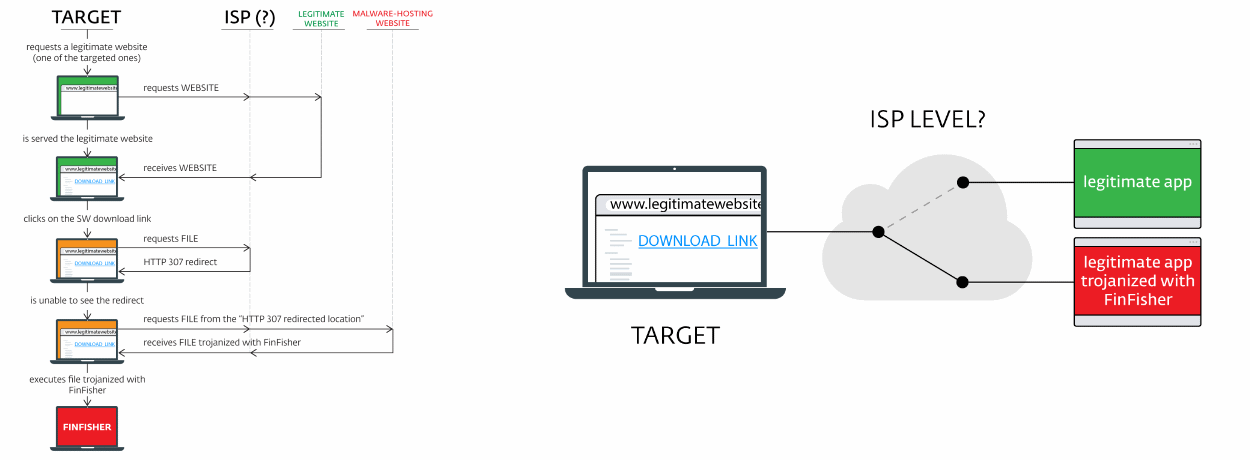
173ISP Involvement Suspected in the Distribution of FinFisher Spyware
Security researchers have tracked a malware distribution campaign spreading the FinFisher spyware — also known as FinSpy — to the infrastructure of ...
-

 180
180CLKSCREW Attack Can Hack Modern Chipsets via Their Power Management Features
A team of three scientists from Columbia University has discovered that by attacking the combo of hardware and software management utilities embedded...
-

 111
111Attackers Take Over WordPress, Joomla, JBoss Servers to Mine Monero
Attacks aimed at delivering cryptocurrency mining tools on enterprise networks have gone up as much as six times, according to telemetry data...
-

 265
265SEC Says Hackers Breached Its System, Might Have Used Stolen Data for Insider Trading
Yesterday, the US Securities and Exchange Commission (SEC) — the US government agency that regulates the financial sector — admitted in a...
-
 193
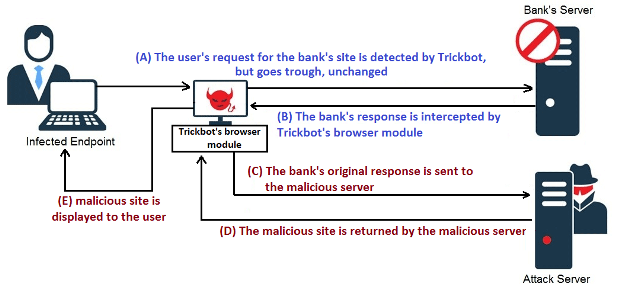
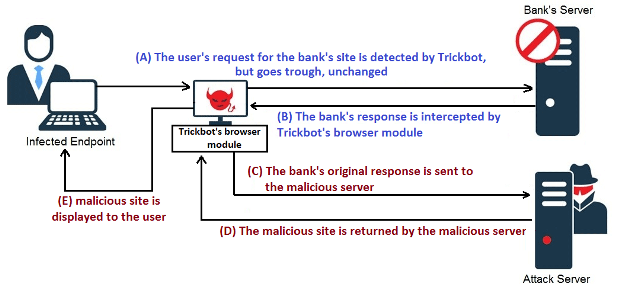
193How TrickBot tricks its victims with web injects (Server side injections) :
A lot has already been written about TrickBot, a banking trojan which is believed to be the successor of the Dyre banking malware....
-

 252
252Attackers Can Use HVAC Systems to Control Malware on Air-Gapped Networks
Heating, ventilation, and air conditioning (HVAC) systems can be used as a means to bridge air-gapped networks with the outside world, allowing...
-
 266
266Viacom left the keys of its digital kingdom on a publicly exposed AWS S3 bucket
The security researcher Chris Vickery discovered that Media giant Viacom left sensitive data and secret access key on unsecured Amazon AWS S3 bucket....
-

 196
196Researchers demonstrate how to steal Bitcoin by exploiting SS7 issues
Hackers have exploited security weaknesses in SS7 protocol to break into a GMail account, take control of a bitcoin wallet and steal...
-

 174
174Premium SMS malware EXPENSIVEWALL infected millions of Android handsets
Google removed 50 malicious apps from the official Play Store after experts discovered a new malware, dubbed ExpensiveWall, eluded Google Bouncer checks. Google...
-

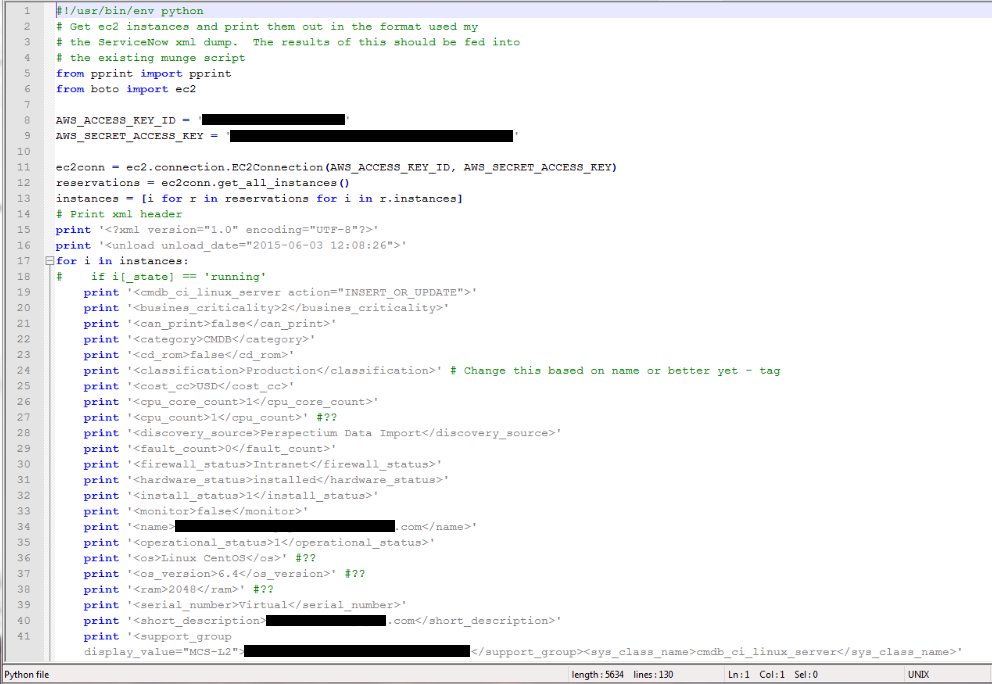
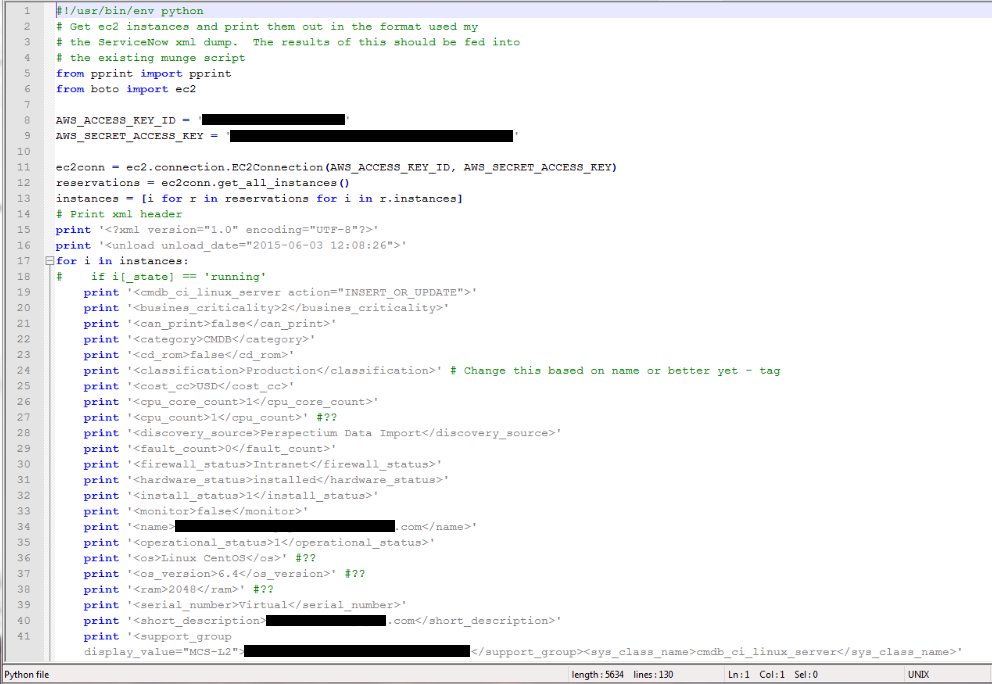
 216
216BlueBorne – 8 Zero Day Bugs Threaten 8.2 Billion Bluetooth-Enabled Devices
Asecurity firm Armis has identified a set of 8 zero-day bugs, collectively known as BlueBorne, which put Bluetooth-capable devices at the risk...
-

 196
196Second Researcher Drops Router Exploit Code After D-Link Mishandles Bug Reports
Embedi, a hardware security firm, has published details about two vulnerabilities that have yet to be patched in the firmware of D-Link...
-

 395
395RouteX Malware Uses Netgear Routers for Credential Stuffing Attacks
A Russian-speaking hacker has been infecting Netgear routers over the past months with a new strain of malware named RouteX that he...
-
 362
362Critical BlueBorne Vulnerability Puts More Than 5 Billion Bluetooth Enabled Devices Under Attack
Bluetooth is the leading and most widespread protocol for short-range communications.It is the backbone of short range connectivity in the vast majority...
-
 261
261Bashware: Malware Can Abuse Windows 10’s Linux Shell to Bypass Security Software
Bashware is the name of a new technique that allows malware to use a new Windows 10 feature called Subsystem for Linux...
-

 109
109Comodo Caught Breaking New CAA Standard One Day After It Went Into Effect
One day after the CAA (Certificate Authority Authorization) standard became obligatory on September 8, a German security researcher caught Comodo breaking the...
-

 189
189Hackers can remotely access Smiths Medical Syringe Infusion Pumps to kill patients
The US-CERT is warning of hackers can remotely access Smiths Medical Syringe Infusion Pumps to control them and kill patients. IoT devices...






