Vulnerabilities
-
 211
211Lenovo VIBE Mobile Phones Vulnerable to Local Root Privilege Escalation – Its Time to Update your Lenovo Smart Phones
A Critical Vulnerabilities Discovered in Lenovo Vibe Android Mobiles Phones which leads to Local Privilege Escalation to the Victims device that is...
-

 123
123SIEMENS PATCHES CRITICAL INTEL AMT FLAW IN INDUSTRIAL PRODUCTS
Siemens patched two critical vulnerabilities that affected its industrial products this week. One, tied to a recently disclosed flaw in Active Management...
-

 245
245SQL Injection flaw in WordPress Plugin WP Statistics potentially exposed 300,000+ Sites
Security experts at Sucuri have discovered a SQL Injection vulnerability in WP Statistics, one of the most popular WordPress plugins. Security experts at...
-

 103
103Management bug can crash Cisco IOS, IOS XE
Nine SNMP MIBs vulnerable. Cisco’s been caught out by the venerable Simple Network Management Protocol, turning up nine bugs in IOS and...
-
 197
197A critical flaw allows hacking Linux machines with just a malicious DNS Response
A remote attacker can trigger the buffer overflow vulnerability to execute malicious code on affected Linux systems with just a malicious DNS response....
-

 244
244Zero-day Skype flaw causes crashes, remote code execution
The critical flaw doesn’t require any user interaction, either. A critical flaw in Microsoft’s Skype web messaging and call service allows attackers...
-

 188
188This Windows Defender bug was so gaping its PoC exploit had to be encrypted
Microsoft recently patched a critical vulnerability in its ubiquitous built-in antivirus engine. The vulnerability could have allowed attackers to execute malicious code...
-
 175
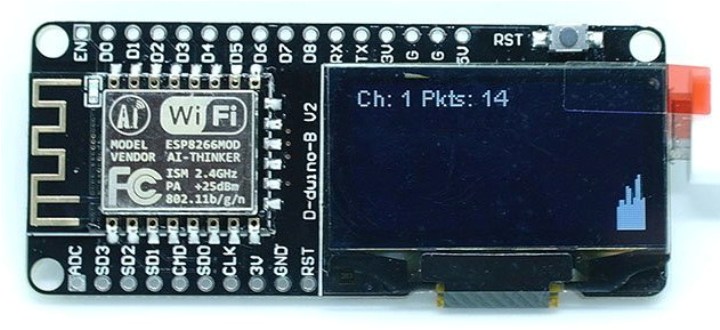
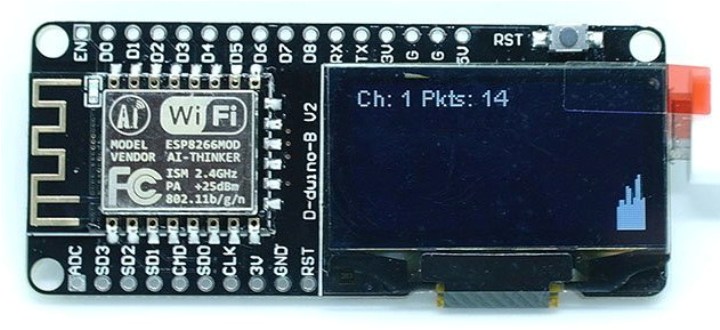
175Handheld WiFi Packet Monitor
Every day you wake up, perhaps check your phone or other Internet connected device, and head out the door or into your...
-

 211
211UK Govt Wants Encryption Backdoors but Can’t Even Protect Its Email Servers From a Brute-Force Attack
A “determined” attacker has breached the email system of the UK Parliament over the weekend, according to a statement put out by...
-

 216
216Drupal fixes the CVE-2017-6922 flaw exploited in spam campaigns in the wild
Drupal team released security updates to fix several vulnerabilities, including the critical access bypass flaw CVE-2017-6922 exploited in spam campaigns. The Drupal...
-

 214
214Symantec patches Messaging Gateway remote code execution bugs
The three vulnerabilities allow attackers to disarm the platform and execute code. Symantec has patched three vulnerabilities in the Symantec Messaging Gateway...
-

 131
131Netflix Hacker Stole “Orange Is the New Black” Season from Vulnerable Windows PC
Larson Studios paid $50,000 to the hacker group, but they decided to leak the season because of breach of contract. Season 5...
-

 235
235Stack Clash Vulnerability Grants Root Access on Linux and Other UNIX OSes
A vulnerability nicknamed “Stack Clash” allows an attacker to gain root privileges on a UNIX system and take over vulnerable machines. The...
-
 205
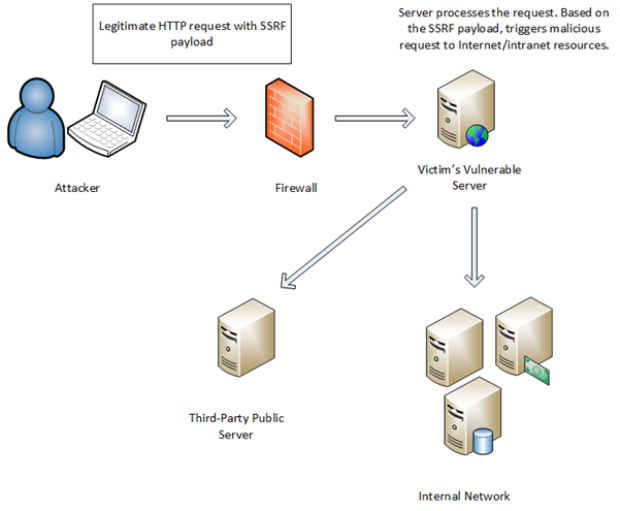
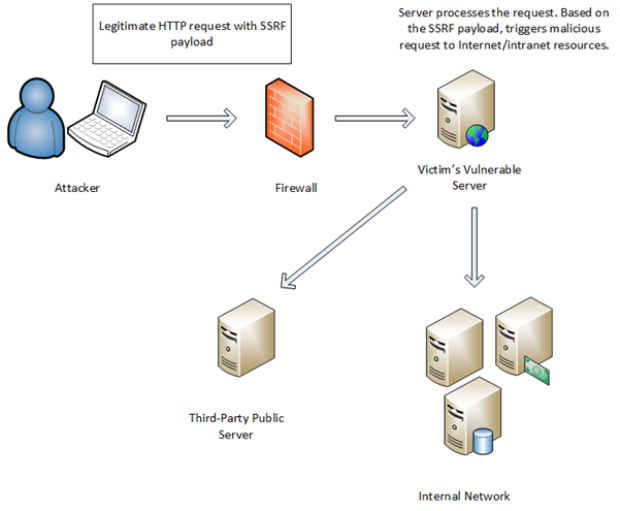
205Abusing the AWS metadata service using SSRF vulnerabilities
I recently worked on a small toy project to execute untrusted Python code in Docker containers. This lead me to test several...
-

 146
146Hacker “His Royal Gingerness” Jailed for Cyber-Attack on UK Hospital, Airport
Daniel Devereux, 30, a British man calling himself “His Royal Gingerness” has been sentenced to 32 weeks in prison for hacking the...
-

 208
208You Can Hack Some Mazda Cars with a USB Flash Drive
EXCLUSIVE — Mazda cars with next-gen Mazda MZD Connect infotainment systems can be hacked just by plugging in a USB flash drive...
-

 193
193New Code-injecting SOREBRECT Fileless Ransomware detected in the wild
The number of fileless malware continues to increase, recently security researchers spotted a new Fileless Ransomware dubbed Sorebrect. Sorebrect is able to inject malicious...
-
 184
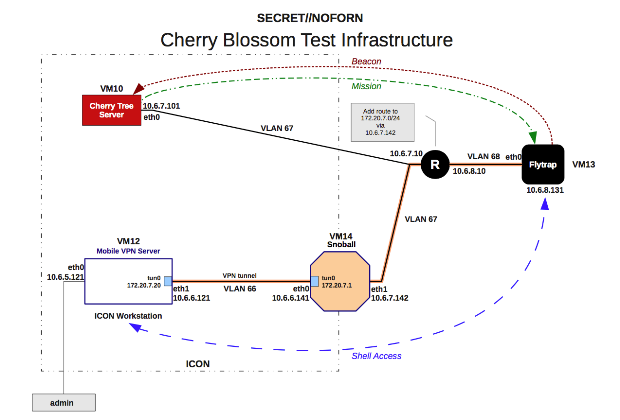
184Advanced CIA firmware has been infecting Wi-Fi routers for years
Latest Vault7 release exposes network-spying operation CIA kept secret since 2007. Home routers from 10 manufacturers, including Linksys, DLink, and Belkin, can...
-

 317
317Industroyer malware touted as ‘biggest cyber threat to critical infrastructure since Stuxnet’
SECURITY RESEARCHERS have uncovered Industroyer and have labelled it as the biggest threat to critical infrastructure since Stuxnet. Stuxnet was the malicious warm responsible...
-

 172
172OneLogin suffers breach—customer data said to be exposed, decrypted
Customer account-only support page warns of “ability to decrypt encrypted data.” OneLogin has admitted that the single sign-on (SSO) and identity management...
-

 195
195Linux Distros Patch Dangerous Vulnerability in Sudo Command
Several Linux distros have issued updates to fix a vulnerability in Sudo, a Linux app behind the “sudo” command, which can allow...






